Active Directory Enumeration: PowerView
In this guide, we will explore how to perform Active Directory enumeration using PowerView, a powerful tool within PowerShell. PowerView enables penetration testers and security professionals to gather crucial information about an Active Directory environment, aiding in post-exploitation and lateral movement. By leveraging PowerView for Active Directory enumeration, you can identify valuable targets and enhance your security assessment capabilities.
Active Directory Enumeration is a challenge for even some of the seasoned attackers and it is easy to miss some key components and lose the change to elevate that initial foothold that you might receive. In this article, we bring you methods that you can use to enumerate AD using PowerShell.
Table of Contents
- Introduction
- Get-NetUser
- Get-UserProperty
- Find-UserField
- Invoke-UserHunter
- Get-NetDomain
- Get-NetDomainController
- Get-NetComputer
- Get-UserProperty
- Get-NetForest
- Get-NetForestCatalog
- Get-NetForestDomain
- Get-NetLoggedon
- Get-DomainPolicy
- Get-NetOU
- Get-NetGroup
- Get-NetGroupMember
- Get-NetGPO
- Find-GPOLocation
- Invoke-EnumerateLocalAdmin
- Get-NetProcess
- Invoke-ShareFinder
- Invoke-FileFinder
- Invoke-ACLScanner
- Find-LocalAdminAccess
- Get-NetSession
- Conclusion
Introduction
We have configured an Active Directory Lab that mimics a Real-Life Environment with a bunch of Users, Machines, and Vulnerabilities. In this Article/Demonstration, we are focused on our ability to Enumerate Information that can be then further be used to elevate privileges or be able to help with Lateral Movement. A tool by the name of PowerView was developed and integrated by Will Schroeder (a.k.a harmj0y). It soon became an integral toolkit to perform Active Directory Attacks and Enumeration. For this demonstration, we will assume that we have gained the initial foothold. Now we will use PowerShell with PowerView to enumerate the machine and the Domain. In case you run into difficulties running any of the commands depicted use the Official GitHub for the Installation Process.
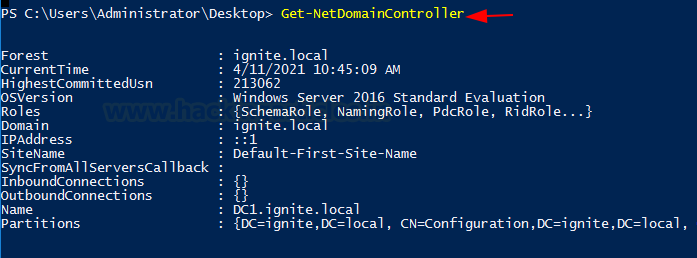
Get-NetUser
In our Active Directory Lab Setup, we created 7 users with different roles and privileges. We can confirm this by Viewing the Active Directory Users and Computers as shown in the image.

Running PowerView for Enumeration
This setup helps demonstrate and correlate the information we are about to enumerate using PowerShell. The attacker has transferred the PowerView to the Target System. To run the PowerShell Script on the System, the Execution Policy must be set to Bypass as shown in the image. Next, the attacker imports the Modules from the PowerView Script. This is a one-time process. After this, the attacker can directly use the Modules to perform Enumeration. To get the users that are active on the Network, the attacker runs the following command.
Get-NetUser

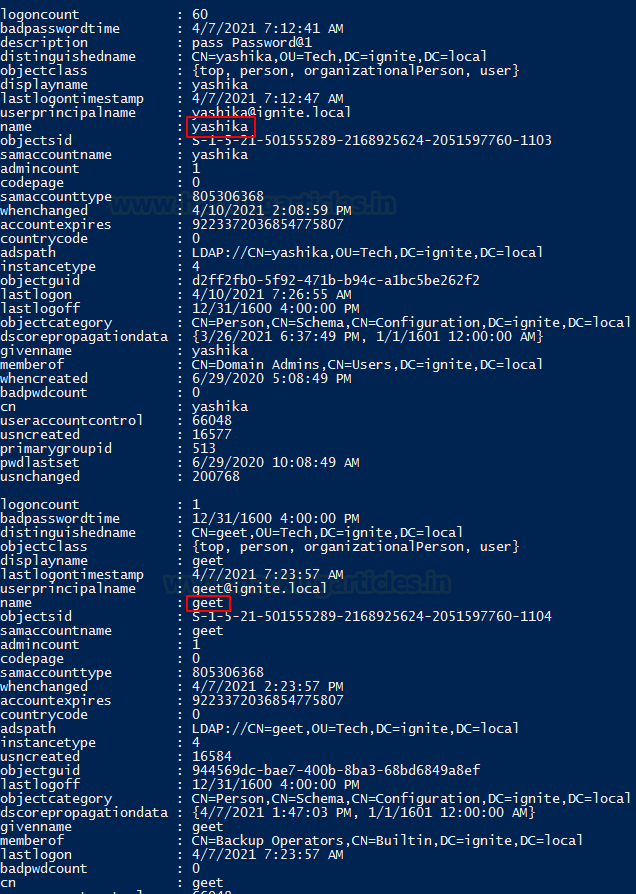
The users that are enumerated are not just restricted to usernames. The data collected also consists of logoncount. It gives an idea of an active or inactive user in the network. Next, there is a badpasswordtime. It tells the last time and date when an attempt to log on was made with an invalid password on this account. Then, there is a small description of the user. It includes the names of groups that this particular user is part of. At last, it shows the date and time since the last password change. This information is very important. It helps the attacker learn about the user Behavior.
Filtering and Targeting Specific Users
Similar Information is available for the users Yashika and Geet.
To get an abstract list of users created on the Network, the attacker grabs the Common Name. This is done by using the select command on the output of the Get-NetUser Module.
Get-NetUser | select cn
Administrator, Yashika, Geet, Aarti, Raj, Pavan, Jeenali, Japneet, etc. are the various users in this Network Environment.
Similarly, to gather information about a particular user, the attacker can target a specific account. For example, after the attacker extracts users in the previous section, they choose a particular user. Now, more information about that user is required. This can be done using a flag -Username with the username that the attacker wants to target. In this case, the attacker chooses the Yashika User.
Get-NetUser -UserName yashika

A streamlined but detailed output regarding the Yashika user is extracted by the attacker.
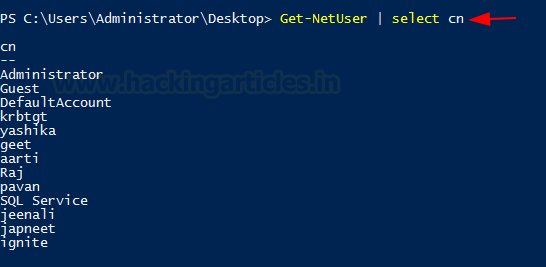
Get-UserProperty
When working with the Users and their properties, we see that there is a variable by the name pwdlastset. We can use this to check which user is reluctant to change their passwords. This can be configured to any of the property that was extracted in the previous. For this demonstration, we will be extracting the password last set property of all the users.
Get-UserProperty -Properties pwdlastset
Find-UserField
There are times when the network has so many users that it becomes difficult for the Domain Administrator to track all users and their credentials. In such cases, administrators sometimes resort to risky methods to save credential information. A common example I’ve encountered in real environments is saving credentials or important user details in the user description.
Using Find-UserField for Enumeration
This information can be extracted using the Find-UserField command with a specific search term. In this demonstration, we used the term “pass” to search for potential passwords. As seen, the user Yashika had their password written and saved in the description.
This technique is not limited to passwords. By using the right set of keywords, such as “built,” attackers can also identify built-in accounts. The following commands can help with this:
Find-UserField -SearchField Description -SearchTerm "pass" Find-UserField -SearchField Description -SearchTerm "built"

The information extracted using the Find-UserField command comes from the Properties of a user. On the server, you can view these properties by opening the user list, right-clicking on any user, and selecting Properties. This will display a window, similar to the one shown in the image below. In this example, the Administrator has stored their password in the Description Field.
It’s important to note that this is a major security risk. From the attacker’s perspective, always check for such descriptions, as they may contain valuable information that can help further the attack.

Invoke-UserHunter
The Invoke-UserHunter module in PowerView is used to locate where specific users are currently logged in within an Active Directory environment. This is especially useful for attackers or red teamers who want to identify systems where privileged users (like Domain Admins) are active, enabling targeted attacks like credential dumping or lateral movement.
Invoke-UserHunter
By default, this command searches for sessions of users who are members of high-privileged groups (e.g., Domain Admins).

Parameters
- -UserName <name> – Target a specific username.
- -CheckAccess – Filter systems that you have admin rights to (very useful for practical attacks).
- -Stealth – Uses fewer queries to evade detection, but may miss some results.
- -Delay <seconds> – Adds a delay between queries (helps avoid detection by monitoring systems).
Invoke-UserHunter -CheckAccess

Why It’s Useful:
Helps attackers focus efforts on machines with high-value targets.
Reduces noise by skipping irrelevant machines.
Assists Blue Teamers in understanding attacker behavior and improving defenses (e.g., limiting interactive logins for privileged users).
Get-NetDomain
When attackers need to extract domain-related information directly from the target server, they can rely on Get-NetDomain. This command extracts various Domain data, including the Forest Name and Domain Controllers with Children (which might be configured in a real environment server). It also retrieves the Name of the Parents, along with the RidRoleOwner—a Domain Controller (DC) Object that holds the Relative Identifier (RID) master role—and the PdcRoleOwner, which is another DC Object that holds the PDC emulator role for that specific Domain.
Get-NetDomain

In case the attacker wanted to go against a specific domain, they can use a domain option by providing the name of the exact domain that they are looking for and Get-NetDomain will extract the data for that particular domain.
Get-NetDomain -domain "ignite.local"

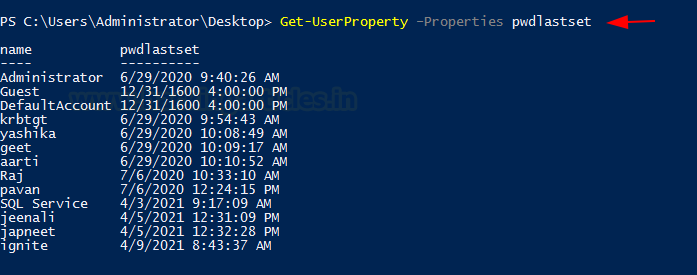
Get-NetDomainController
Next on the lineup, we have the Get-NetDomainController. This provides the information of the particular server device instead of the domain. When an attacker wants to extract the data about the Domain Controller Machine then this tool can be used. It extracts the Forest Information, with the Time and Date configured on the Server. IT tells the OS Version that can help constraint the search for Kernel Exploits for the attacker. Then the attacker has the IP Addressing data with the Inbound and Outbound connections.
Get-NetDomainController
Similar to the Get-NetDomain the attacker can configure Get-NetDomainController to be targeted to a specific domain. The scenario that the attacker might be looking at multiple domains set up with multiple server setup so the attacker can use the -Domain option to target that specific Domain Controller inside the Domain.
Get-NetDomainController -Domain ignite.local

Get-NetComputer
What seems to be a pretty simple option can turn out to be one of the most used tools to extract a huge amount of data from either the Domain Controller or even a single device. If the attacker runs the Get-NetComputer directly on the Domain Controller machine as demonstrated, it will reveal the Computer Names of all the devices connected in the Domain.
Get-NetComputer
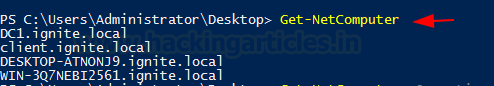
Moving on, if the attacker decides to use -Ping Option then they can get the list of all the devices that can be pinged from the machine they are running the Get-NetComputer from.
Get-NetComputer -Ping

If the attacker doesn’t want to extract the data one parameter at a time there is an option to extract all the data from the Machine. This can be done with the FullData option, but keep in mind that a large amount of data extraction leads to large chances of getting detected.
Get-NetComputer -FullData

Moreover, if the attacker decides to use the -OperatingSystem option with the Get-NetComputer and provide the Name of the OS as a parameter then they can extract all the machines that are running that specific Operating System.
Get-NetComputer -Operatingsystem "Windows Server 2016 Standard Evaluation"

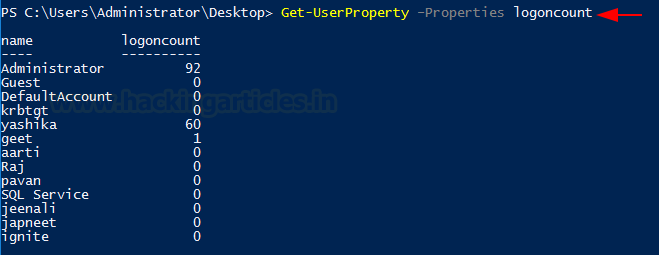
Get-UserProperty
Next on the list is the UserProperty. Up until now, the attacker can extract the users and very little information about them. This was limited but this problem is solved using UserProperty. With it, the attacker can aim to those niche details about any particular property. Some of the information extractable is check for Administrator Level Access, Password Time, Password Change Date, Description of the User, check what group the different users are a part of, and much more.
Get-UserProperty
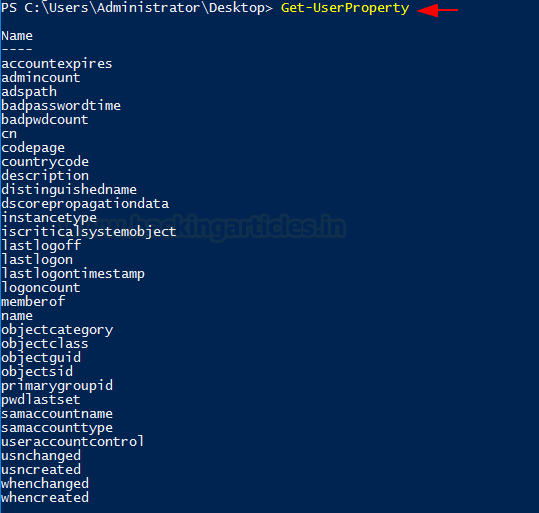
To target a specific Property, the attacker can use the Properties option and specify the property they want to inquire about. For the demonstration, the property that was inquired here was badpwdcount. This tells the attacker about the unsuccessful attempts that were made against all the users.
Get-UserProperty -Properties badpwdcount

The attacker can focus on the logoncount property to get an understanding as to which of the users are dormant and which among them are active. In a real-life scenario, inactive users might be the users in a network of ex-employees that have been overlooked by the Administrator. This can create a problem as firstly these accounts would not adhere to change their password also the attack mounted on these accounts won’t raise flags being these users are legit.
Get-UserProperty -Properties logoncount
Get-NetForest
Apart from the domain information and the user information, the attacker can also gain information about the forests and there can be multiple forests inside a domain. To procure information about the forest in the current user’s domain is to use Get-NetForest.
Get-NetForest

Get-NetForestCatalog
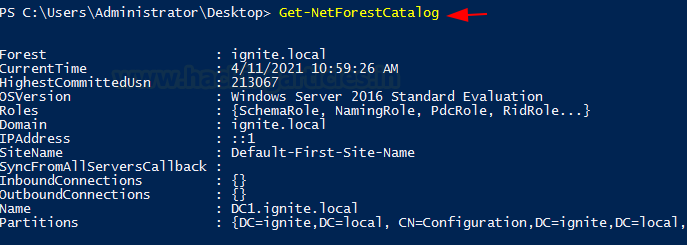
Forests typically have different global catalogs that can help the attacker to get some precarious information about the domain. This can be observed from the following demonstration of extracting all the global catalogs of the current forest using the Get-NetForestCatalog.
Get-NetForestCatalog
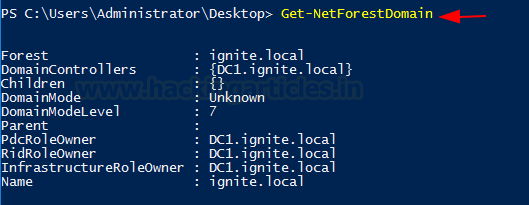
Get-NetForestDomain
Moving on from the catalogs, the attacker can also work on extracting the various domains of the forest the current user is located in. This can be done by running Get-NetForestDomain as shown in the demonstration.
Get-NetForestDomain
Get-NetLoggedon
That’s enough Forest, getting back to the users on the local or remote machine the attacker can take advantage of the NetLoggedon module. Administrative Rights are required to use this module. This module uses the NetWkstaUserEnum Win32API call to extract the users currently logged on. If the attacker is in a bit of a hurry, they can enumerate all the users logged on to all the machines in the domain by first running Get-DomainComputer and then using Get-NetLoggedon on that data. They can concatenate this using a pipe.
Get-DomainComputer | Get-NetLoggedon
In this demonstration, however, it is shown how to enumerate users that are loggedon on a particular machine with the help of the ComputerName option and providing the Name.
Get-NetLoggedon -ComputerName DC1

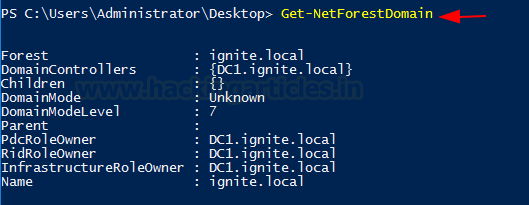
Get-DomainPolicy
The Get-DomainPolicy command in PowerView is used to retrieve the default domain policy and domain controller policy settings in an Active Directory (AD) environment. This includes password policies, lockout policies, and Kerberos settings—crucial for both attackers and defenders.
Get-DomainPolicy

To enumerate Kerberos details, the attacker can try and go after the Kerberos Policy which contains data such as the Max Ticket Age, Max Renew Age, and several Ticket Validation Client. This kind of information can come in handy if the attacker is trying to perform a ticket forging attack or similar attack.
(Get-DomainPolicy)."KerberosPolicy"

Parameters
- –Domain <domain> — Specify a different domain to query.
- -LDAPFilter — Apply custom LDAP filtering if needed.
- -Server <domain controller> — Target a specific domain controller.
Returns the password and lockout policy portion of the domain policy.
(Get-DomainPolicy)."SystemAccess"
Get-NetOU
Attackers use the Get-NetOU command in PowerView to enumerate Organizational Units (OUs) in an Active Directory (AD) environment. Organizational Units are containers within AD used to group users, computers, and other objects—often by department, location, or role.
To Enumerate, run the following command on PowerShell.
Get-NetOU
This lists all OUs in the current domain.

It can be observed that there are 4 OUs on the Target Server. Namely, Tech, VPN, Sales, and HR.
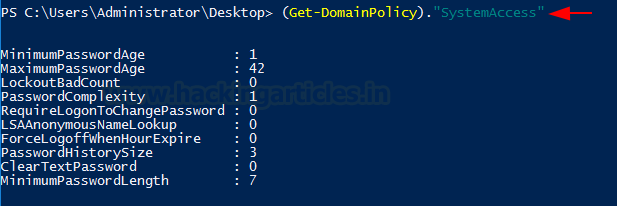
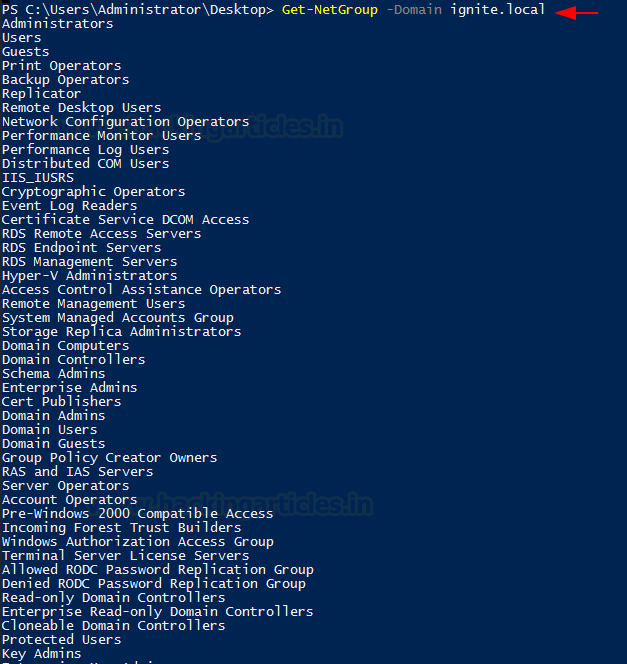
Get-NetGroup
The Get-NetGroup command in PowerView is used to enumerate groups in an Active Directory (AD) environment. It’s a key recon tool for both Red Teamers and Blue Teamers to discover group-based privileges and access controls.
Get-NetGroup
This retrieves a list of all groups in the current domain.

Parameters
- -GroupName <name> — Search for a specific group by name.
- -Domain <domain> — Query a different domain.
- -FullData — Get all LDAP attributes for each group.
- -SearchBase <OU DN> — Limit search to a specific Organizational Unit.
Extracting and Targeting Group Information
When the attacker wants to extract groups that include the keyword “admin,” they use it to find relevant administrator-related groups. These groups might be important or contain sensitive information.
Get-NetGroup *admin*

Suppose the attacker wants to check the group membership of a specific user. Then they can use the UserName option to do so, as shown in the example. The attacker extracts information for the Yashika user:
Get-NetGroup -UserName yashika

To target a specific domain, the attacker can use the Domain option along with the domain name provided:
Get-NetGroup -Domain ignite.local
Detailed Group Enumeration and Filters
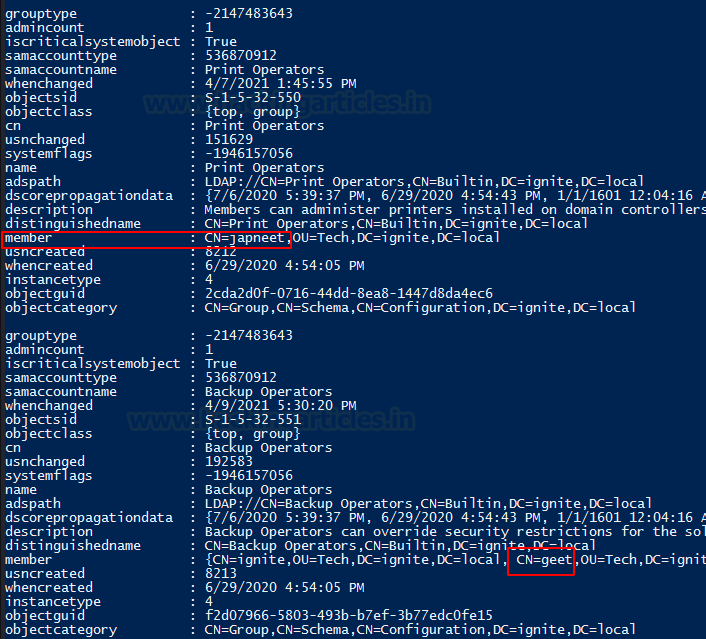
Furthermore, if the attacker wants to extract all data about groups in the domain, they use the FullData option. It helps extract all users with their group details. In the demonstration, it is observed that an Admin exists in the domain and is a member of the Administrator Group along with other User Groups.
Get-NetGroup -FullData

There is a member named Japneet who is part of the Tech Group. When the attacker looks for more information about group users, they observe that a user named Geet also belongs to the Tech Group.
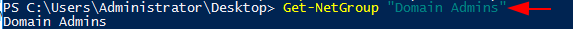
Next, the attacker moves from user-based group enumeration to group-based enumeration by providing a specific group name:
Get-NetGroup "Domain Admins"
They can also combine multiple options to enumerate detailed data about a group:
Get-NetGroup "Domain Admins" -FullData

Finally, the attacker can streamline enumeration by combining several options. This includes specifying a particular group name and domain.
Get-NetGroup -GroupName *admin* -Domain ignite.local
Get-NetGroupMember
In the enumeration, if the attacker gets to a stage where they have successfully enumerated the group names then they can use that in collaboration with the Get-NetGroupMember to extract the members of that group. In the demonstration, we extracted the members of the group Domain Admins.
Get-NetGroupMember -GroupName "Domain Admins"

As discussed earlier Get-NetGroupMember also supports some options to run along such as the Recurse. It helps the attacker extracts significant amounts of data about all the users of the group they provided. As it can be observed from the screenshots of running Get-NetGroupMember with and without Recurse there is some significant difference between them both.
Get-NetGroupMember -GroupName "Administrators" -Recurse

Get-NetGPO
Group Policy provides an interesting way to figure out how the Domain is set up and what set of rules and policies the Administrator has designed to govern the Domain. You can enumerate this using Get-NetGPO. This command extracts all the information regarding Group Policies configured on the Target System.
Get-NetGPO

As you can observe from the previous iteration of running Get-NetGPO, the amount of information can be overwhelming. Hence, to get a clean and easy-to-understand output, you can use selection to retrieve specific names of the policies.
Get-NetGPO | select displayname

Find-GPOLocation
Getting the GPO location is a good way to map the abilities of a specific user. It takes the username that is provided to it and checks for the permissions for that users. This means that it will return the locations that are accessible for that user. In this demonstration, we use the Yashika user and we choose the verbose option as well to elaborate the result to get the most out of it.
Find-GPOLocation -UserName yashika -verbose

Invoke-EnumerateLocalAdmin
Invoke-EnumerateLocalAdmin does exactly what the names say. It searched for the Local Administrators for the domain. In our demonstration, we see that we have extracted the Administrator, Enterprise Admins and Domain Admins for our domain ignite. local.
Invoke-EnumerateLocalAdmin

Get-NetProcess
The Get-NetProcess command in PowerView is used to enumerate running processes on remote systems in an Active Directory environment. It’s especially useful during post-exploitation when an attacker wants to identify processes like antivirus tools, command shells, or credential managers running on target machines.
Get-NetProcess

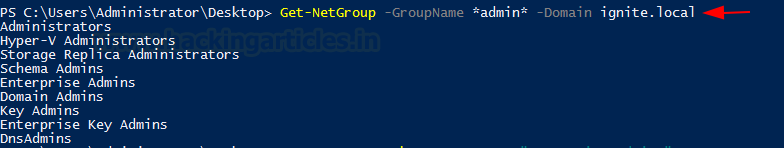
Invoke-ShareFinder
Any inexperienced attacker might wonder why there is a need to enumerate the shares when they can do that externally using SMB enumeration. But an experienced attacker knows that some shares are not visible to all users. The system can configure whether a particular share is visible and accessible to everyone or only to specific users. Therefore, to enumerate the shares in a domain, use Invoke-ShareFinder.
Invoke-ShareFinder
Invoke-FileFinder
Searching on the machine that the attacker has an initial foothold is not that difficult task. But to search a specific file across the network in the domain can be done using the Invoke FileFinder. It will search for sensitive files such as the Credentials files and other files that can lead to a serious compromise.
Invoke-FileFinder

Invoke-ACLScanner
ACL or Access Control Lists can be scanned on a domain that will return the weak permissions on the files. Bear in mind that Domain Permission can be a bit challenging to wrap your head around and the permission that you might find using Invoke-ACLScanner can be difficult to exploit. However, this does not mean that any attacker should not check for those. In simpler terms, Invoke-ACLScanner finds the permissions that the users and group have which are possible subject to exploitation. It determines this by separating the default permission and showing the list of permissions that do not default or new defined by the Administrator.
Invoke-ACLScanner -ResolveGUIDs

Find-LocalAdminAccess
Find-LocalAdminAccess also is pretty self-defined. It enumerated for machines on the local domain that have the users who have the local administrator access. It checks if the user has local administrator access using Test-AdminAccess. Then it checks for the Credential option. If passed, then it uses Invoke-UserImpersonation to impersonate the specified user before enumeration.
Find-LocalAdminAccess

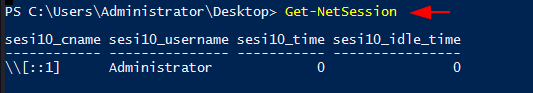
Get-NetSession
At last, it’s time to shine some light on the sessions generated inside a Domain. Attackers can enumerate these sessions with the help of the Get-NetSession tool. When they run this command, they extract session information for the local or a remote machine. This function executes the NetSessionEnum Win32API call to extract the session information. They can use it in its bare form, as demonstrated, or use it with the ComputerName option to target a specific host.
Get-NetSession
Conclusion
Active Directory is extensive and can be confusing for novice security professionals. In this guide, we will explore how to perform Active Directory enumeration using PowerView, a powerful tool within PowerShell. PowerView enables penetration testers and security professionals to gather crucial information about an Active Directory environment, aiding in post-exploitation and lateral movement. This resource will help you enumerate your Active Directory Deployment and understand the information that an attacker can extract.
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Contact on Twitter and LinkedIn
how can I set up the same or at least similar to your laboratory for testing?