Windows Privilege Escalation: Insecure GUI Application
In the series of Privilege escalation, till now we have learned that Microsoft Windows offers a wide range of fine-grained permissions and privileges for controlling access to Windows components including services, files, and registry entries. Today through applications we are going to exploit the privileges. Many GUI applications need higher privileges other than the current user to have, to access some of their particular services. Secondly, just due to misconfiguration of the application. Let’s deep dive into it.
Table of Content
- Introduction
- Prerequisites
- Lab setup of insecure GUI Application
- Abusing Insecure GUI Application
Prerequisites:
Machine A-Window 10 (Ignite as an admin user)
Notepad++ Installed application on window 10
Lab Setup of Insecure GUI Application
Machine A, has ignite as an admin user.
Now, by the whoami /priv command, we get to know that “Ignite “an admin user has only 5 privileges of shut down, change notification etc. with the enable and disable state which is displayed in the below screenshot
whoami /priv
We have to understand that if any user has admin access even though that user does not have full or higher privileges.
Now we will check the ignite admin user’s privileges by adding a new user “demo”. Unfortunately, access is denied. It means “ignite” user does not have full higher privileges.
Install Notepad++ on window 10 and misconfigure the application or insecure it by providing the run as administrator.
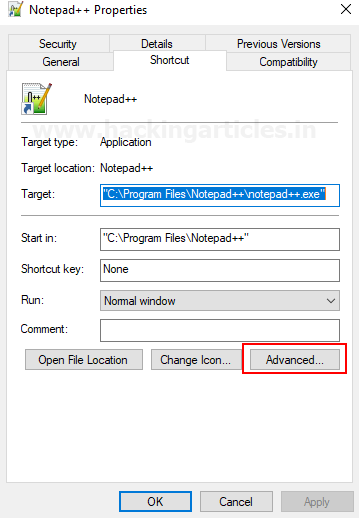
Right-click on the Notepad++ icon and click on the properties to edit advance settings.
Edit the Notepad++ properties just by click on advanced and then ok, by default it will display some of the information of Notepad++ properties as mentioned in the following screenshot.
In the next window of advanced properties, there is an option to run the application as an administrator. Just tick the option and click on OK. Now whenever we will execute the Notepad++ automatically it will run as administrator.
Abusing Insecure GUI Application
After enumerate some time on windows applications, we found that the Notepad++ application has a feature that allows us to open the file, the short key to open the file is CTRL+O or by navigating to the option File then go to open.
Note: In lab set up we had already granted permission to run as administrator, whenever we execute the Notepad++.
The next open prompt will allow us to run a binary with the same privilege escalation same as the Notepad++ process.
Just by entering the cmd exe in the navigating bar, it will open a command prompt.
Now, the Command prompt will open with the Notepad++‘s administrator privileges. The following command will display all the privileges names, descriptions and enabled and disabled features
whoami /priv
If it will allow operations like to open a command prompt or to run executable with the high privileges then it will allow escalating the privileges.
This demonstrates that admin user “ignite” does not have the same privileges as the Notepad++ application that runs as an administrator. Just compare the first and last screenshots for a better understanding. We will characterize this as privilege escalation even though we can now add any new user through the command line. Finally, demo user is successfully added and take the advantage of insecure GUI application to exploit the privileges.
Author: Nisha Sharma is an Experienced and Certified Security Consultant.Highly skilled in Infrastructure, web pentesting along SIEM and other security devices. Connect with her here





Yes this works, but you still need to enter Admin Creds at UAC to “enable” runas admin in ‘advanced’ settings, otherwise this will not work. but good to see how things can be abused…