Password Cracking:SMB
In this article, we will learn how to gain control over our victim’s PC through SMB Port. There are various ways to do it and let take time and learn all those because different circumstances call for a different measure.
Table of Content
- Hydra
- X-Hydra
- Medusa
- Ncrack
- Metasploit
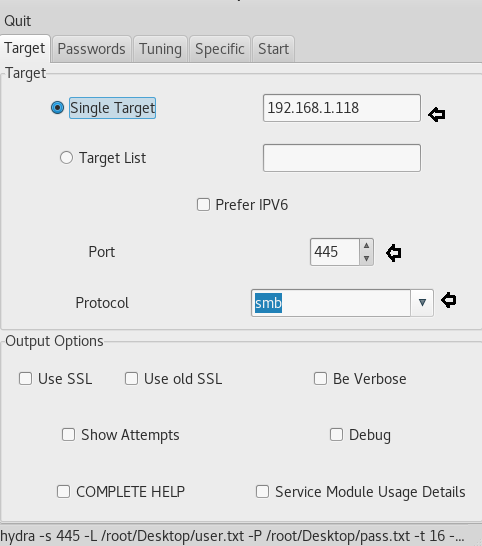
xHydra
This is the graphical version to apply dictionary attack via SMB port to hack a system. For this method to work:
Open xHydra in your Kali. And select Single Target option and there give the IP of your victim PC. And select smb in the box against Protocol option and give the port number 445 against the port option.
Now, go to Passwords tab and select Username List and give the path of your text file, which contains usernames, in the box adjacent to it. Then select Password List and give the path of your text file, which contains all the passwords, in the box adjacent to it.

After doing this, go to the Start tab and click on the Start button on the left. Now, the process of dictionary attack will start. Thus, you will attain the username as pc21 and password as 123 of your victim.

Hydra
This is one command method and works efficiently with not much work. This method works in the terminal of kali. Therefore, open the terminal in your kali and type:
hydra -L /root/Desktop/user.txt -P /root/Desktop/pass.txt 192.168.1.118 smb
Here,
-L –> denotes the path of username list
-P –> is to denote the path of the password
Once the commands are executed it will start applying the dictionary attack and so you will have the right username and password in no time. After a few minutes, Hydra cracks the credential, as you can observe that we had successfully grabbed the SMB username as pc21 and password as 123.

Ncrack
This too is a one command method which also works in the terminal of kali. Go to your terminal and type:
ncrack –U /root/Desktop/user.txt -P /root/Desktop/pass.txt 192.168.1.118 –p 445
Here,
-U –> denotes the path of username list
-P –> denotes password file’s path
445 –> is the port number
And so, with little work, we can attain the password and username of our victim’s PC. Hence, all the methods to hack a system through SMB port which is used for file sharing

Medusa
Medusa is a speedy, parallel, and modular, login brute-forcer. The goal is to support as many services which allow remote authentication as possible Run the following command
medusa -h 192.168.1.118 -U /root/Desktop/user.txt -P /root/Desktop/pass.txt -M smbnt
Now, the process of dictionary attack will start. Thus, you will attain the username and password of your victim.

Metasploit
This module will test an SMB login on a range of machines and report successful logins. If you have loaded a database plugin and connected to a database this module will record successful logins and hosts so you can track your access.
Once the Metasploit opens type:
use auxiliary/scanner/smb/smb_login msf exploit (smb_login)>set rhosts 192.168.1.118 msf exploit (smb_login)>set user_file /root/Desktop/user.txt msf exploit (smb_login)>set pass_file /root/Desktop/pass.txt msf exploit (smb_login)>set stop_on_success true msf exploit (smb_login)>exploit
Here,
auxiliary/scanner/smb/smb_login—> is a module we will use to attempt to login
/root/Desktop/user.txt –> is the path of a text file which is the resident of all the possible usernames.
/root/Desktop/pass.txt –> is the path of a text file in which all the possible passwords resides.
Now, the process of dictionary attack will start. Thus, you will attain the username and password of your victim.

Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
Does metaspolit care about the version of smb?
certainly not, it only trys a combinations of usernames and passwords. Note that we are not using eternalblue.
this article is great, i wish i can share the knowledge that i also have
where do you get the text file? Do you have to create it or download it?
in kali linux, you can get bunch of wordlist files on /usr/share/wordlist directory.