IDS, IPS Penetration Testing Lab Setup with Snort (Manually)
Hello friends! As you people must be aware of various types of security issues facing by IT sector originations daily. There are so many types of firewall and IDS or third-party software available to shoot out major different types of security issues in the network.
In this article, you will learn how to configure the famous “SNORT as IDS” of IT sector originations which work as a real-time machine.
Snort is software created by Martin Roesch, which is widely used as Intrusion Prevention System [IPS] and Intrusion Detection System [IDS] in the network. It is separated into the five most important mechanisms for instance: Detection engine, Logging, and alerting system, a Packet decoder, Preprocessor, and Output modules.
The program is quite famous to carry out real-time traffic analysis, also used to detect query or attacks, packet logging on Internet Protocol networks, to detect malicious activity, denial of service attacks and port scans by monitoring network traffic, buffer overflows, server message block probes, and stealth port scans.
Snort can be configured in three main modes:
- Sniffer mode: it will observe network packets and present them on the console.
- Packet logger mode: it will record packets to the disk.
- Intrusion detection mode: the program will monitor network traffic and analyze it against a rule set defined by the user.
After that, the application will execute a precise action depend upon what has been identified.
Let’s Begin!!
Snort Installation
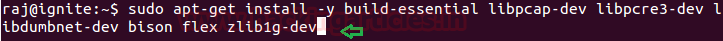
We had chosen the ubuntu 14.04 operating system for installation and configuration of snort. Earlier than installing snort in your machine, you should need to install the necessary dependencies of ubuntu. Therefore open the terminal and type given below command to install pre-requisites:
sudo apt-get install -y build-essential libpcap-dev libpcre3-dev libdumbnet-dev bison flex zlib1g-dev
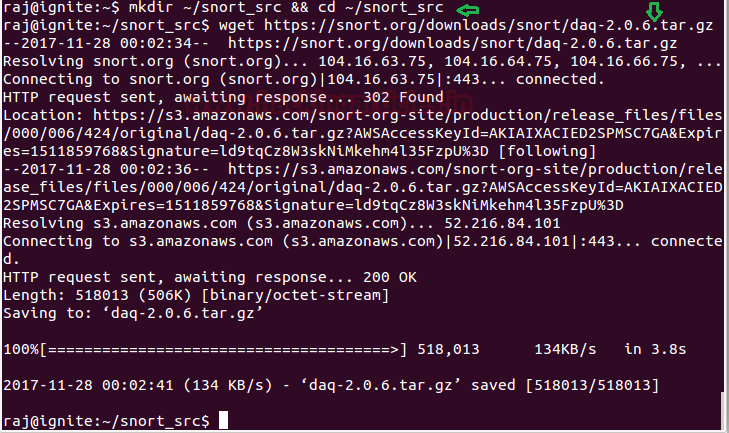
Now create a folder to download snort and its dependencies package inside. Type given below commands to create a folder “snort-src” and move inside it to download DAQ-2.0.6
mkdir ~/snort_src && cd ~/snort_src
wget https://snort.org/downloads/snort/daq-2.0.6.tar.gz
Snort need to set up the DAQ, or Data Acquisition library, for packet I/O. The DAQ change direct calls into lib pcap functions with an abstraction layer that facilitates operation on a variety of hardware and software interfaces without requiring changes to Snort. It is possible to select the DAQ type and mode when invoking Snort to perform pcap read back or inline operation, etc. The DAQ library may be useful for other packet processing applications and the modular nature allows you to build new modules for other platforms.
From given below image you can confirm that we had successfully downloaded daq-2.0.6 tar file.
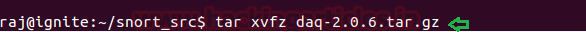
Now execute given below command to extract tar file.
tar xvfz daq-2.0.6.tar.gz
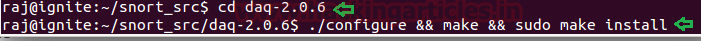
Move inside the daq-2.0.6 folder by executing given below the first command and then execute the second command for automatic installation and configuration.
cd daq-2.0.6 ./configure && make && sudo make install
Till here you had learned how to install daq-2.0.6 for snort.
Now again move into snort-src folder and type given below command to download the latest version of snort-2.9.11
wget https://snort.org/downloads/snort/snort-2.9.11.tar.gz
From given below image you can confirm that we had successfully downloaded snort-2.9.11 tar file.

Now execute given below command to extract tar file.
tar xvfz snort-2.9.11.tar.gz

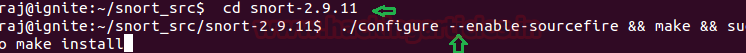
Move inside the snort-2.9.11 folder by executing given below the first command and then execute the second command for automatic installation and configuration.
cd snort-2.9.11 ./configure --enable-sourcefire && make && sudo make install
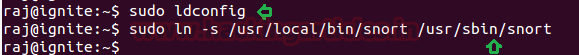
Run the following command to manage and install shared libraries
sudo ldconfig
Type given below command for generating a symbolic link
sudo ln -s /usr/local/bin/snort /usr/sbin/snort
A symbolic link also known as a soft link is a file system entry that points to the file name and location. Deleting the symbolic link does not remove the original file. If, on the other hand, the file to which the soft link point is removed, the soft link stops working, it is broken.
Now execute given below command that snort to verify itself by testing its installation and configuration.
snort -V
The first part of snort installation finished here

Configure Snort to in IDS Mode in Network
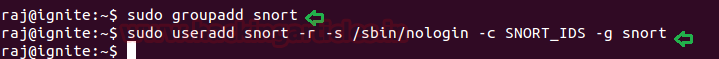
Execute given below command to create the snort user and group, where snort will run as an unprivileged user.
sudo groupadd snort sudo useradd snort -r -s /sbin/nologin -c SNORT_IDS -g snort
Above command will create a group as “snort” and add a member “snort” into it.
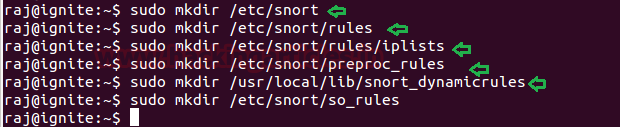
Now further we need to make some directories which Snort suppose at the timing of running in IDS mode in the network. Snort stores configuration files in /etc/snort; rules in /etc/snort/rules; store compile rules in /usr/local/lib/snort_dynamicrules, and stores its logs in /var/log/snort:
Type given below command to create the Snort directories:
sudo mkdir /etc/snort sudo mkdir /etc/snort/rules sudo mkdir /etc/snort/rules/iplists sudo mkdir /etc/snort/preproc_rules sudo mkdir /usr/local/lib/snort_dynamicrules sudo mkdir /etc/snort/so_rules
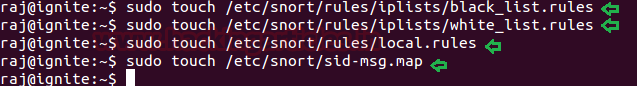
Type given below command to create some files that stores rules and ip lists
sudo touch /etc/snort/rules/iplists/black_list.rules sudo touch /etc/snort/rules/iplists/white_list.rules sudo touch /etc/snort/rules/local.rules sudo touch /etc/snort/sid-msg.map
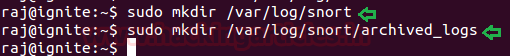
Type given below command to create our logging directories:
sudo mkdir /var/log/snort sudo mkdir /var/log/snort/archived_logs
Type given below command to adjust permissions:
sudo chmod -R 5775 /etc/snort sudo chmod -R 5775 /var/log/snort sudo chmod -R 5775 /var/log/snort/archived_logs sudo chmod -R 5775 /etc/snort/so_rules sudo chmod -R 5775 /usr/local/lib/snort_dynamicrules

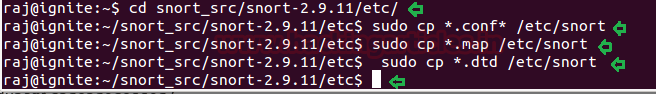
Snort required some configuration files and the dynamic preprocessors to be copied from the Snort source folder into the /etc/snort folder, therefore, execute given below command for that.
cd snort_src/snort-2.9.11/etc/ sudo cp *.conf* /etc/snort sudo cp *.map /etc/snort sudo cp *.dtd /etc/snort
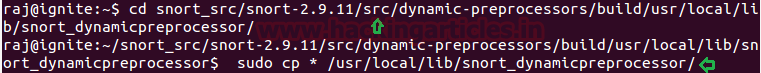
cd snort_src/snort-2.9.11/src/dynamic-preprocessors/build/usr/local/lib/snort_dynamicpreprocessor/ sudo cp * /usr/local/lib/snort_dynamicpreprocessor/
Editing snort configuration file
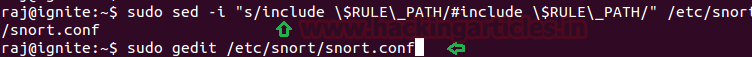
Now we need to comment out all rulesets with the following command:
sudo sed -i "s/include \$RULE\_PATH/#include \$RULE\_PATH/" /etc/snort/snort.conf
After then open the configuration file using gedit for making some changes inside.
sudo gedit /etc/snort/snort.conf
Scroll down the text file near line number 45 to specify your network for protection as shown in the given image.
#Setup the network addresses you are protecting
ipvar HOME_NET 192.168.1.1/24

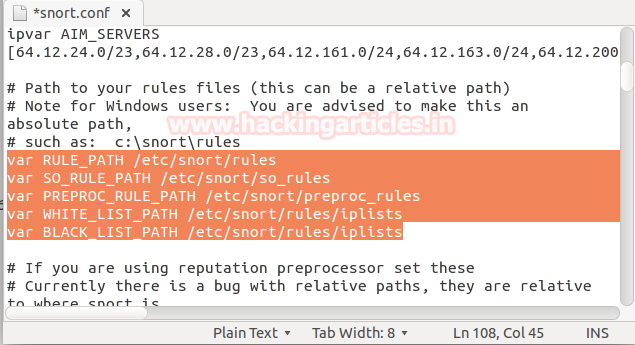
Now again scroll down near line number 108 to set the path of your rule file which you had created above for storing snort rules, as shown in given below image.
var RULE_PATH /etc/snort/rules var SO_RULE_PATH /etc/snort/so_rules var PREPROC_RULE_PATH /etc/snort/preproc_rules var WHITE_LIST_PATH /etc/snort/rules/iplists var BLACK_LIST_PATH /etc/snort/rules/iplists
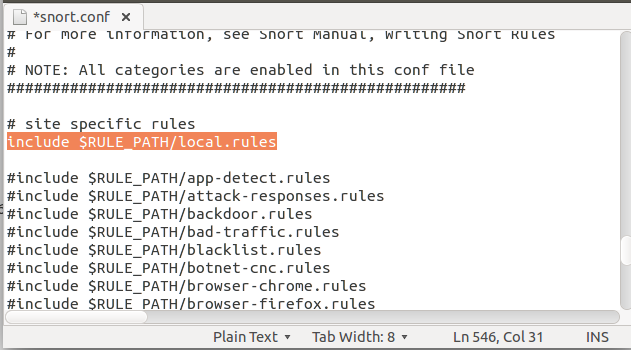
One more time scroll down the text near line number 546 to uncomment highlighted text.
include $RULE_PATH/local.rules
Save the file and close it once all the editing is done in the snort configuration file.
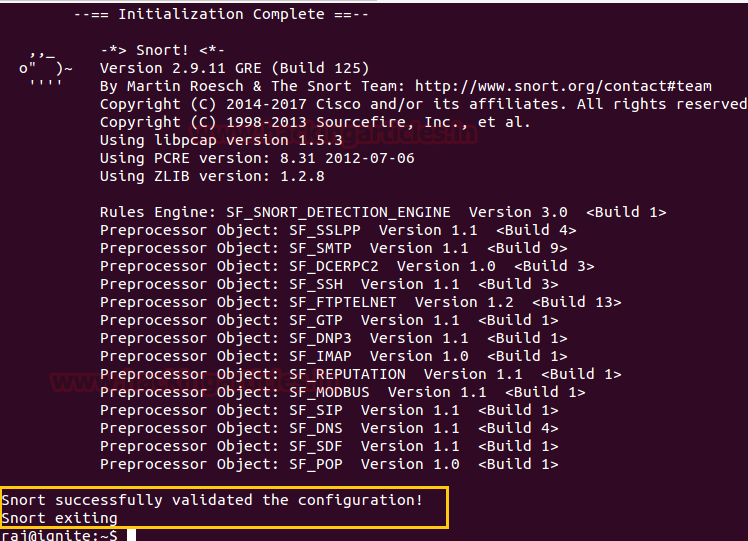
Now once again we need to verify its configuration setting, therefore, execute the following command to test it.
sudo snort -T -i eth0 -c /etc/snort/snort.conf
Now it will compile the complete file and test the configuration setting automatically as shown in given below image:

Great!! We had successfully configured snort as IDS for protecting our network.
Reference link
Author: AArti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here