Forensic Investigation : Prefetch File
In this article, we are going to study an important artifact of Windows, i.e. prefetch files. Every time you do anything on your Windows system, a file is created. These files are called Prefetch files. Through this article, we will learn how these are important and why do we need them.
Table of Content
- Introduction
- Forensic Analysis of Prefetch Files
- WinPrefetch View
- OS Forensic
- PECmd
- FTK Imager
Introduction
A Prefetch file is a file that you create when you open an application on your Windows system. Windows creates a prefetch record when you run an application from a specific area for the absolute first time.
Windows introduced prefetch files in Windows XP. Developers designed prefetch files to accelerate the Windows boot process and applications’ start-up process. In Windows XP, Vista, and 7, the system limits the number of prefetch files to 128, whereas in Windows 8 and above, it allows up to 1024.
Program execution proof can significantly aid a forensic investigator, as they can demonstrate that a certain executable ran on the system to cover up the tracks. As a forensic examiner, check whether the prefetching process is enabled before you initiate the forensic analysis of the prefetch record.
To check the status of prefetching, open the following location in Registry editor:
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management\PrefetchParameters
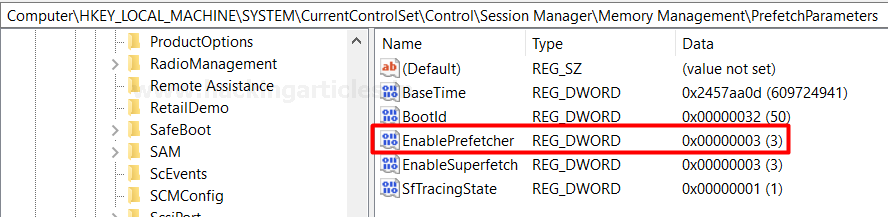
The system sets the value as 3 by default, as shown in the image above. You can change the following values according to your prefetching needs.
Windows Prefetching Options
We explain all the options that Windows provides to customize prefetching below:
- 0:Prefetching Disabled
- 1:Application Prefetching Enabled
- 2: Boot Prefetching Enabled
- 3:Application and Boot both Enabled
Metadata Found in a Prefetch File
The following metadata can be found in a single prefetch file:
- Executable’s name
- Eight character hash of the executable path.
- The path of the executable file
- Creation, modified, and accessed timestamp of executable
- Run count (Number of time the application has been executed)
- Last run time
- The timestamp for the last 8 run time (1 last run time and other 7 other last run times)
- Volume information
- File Referenced by the executable
- Directories referenced by the executable
Save the prefetch files under %SystemRoot%\Prefetch (C:\Windows\Prefetch).

You can open the prefetch files location you can directly search for “prefetch “in the run command.

It can also be opened as a directory from the command prompt, which is a good news for all the command-line lovers.

Forensic Analysis of Prefetch Files
WinPrefetch View
WinPrefetch View is a tool to read and examine the prefetch files stored in your system. The tool was developed by Nirsoft. This utility deals with any variant of Windows, beginning from Windows XP to Windows 10.
You can download the tool from here.

You can easily open the details of a particular prefetch file by simply clicking on it. Here, I have opened HFS.EXE-D3CAF0BF.pf for a detailed view. It shows details such as created time, modified time, file size, the path of process run count, last run time, missing process.

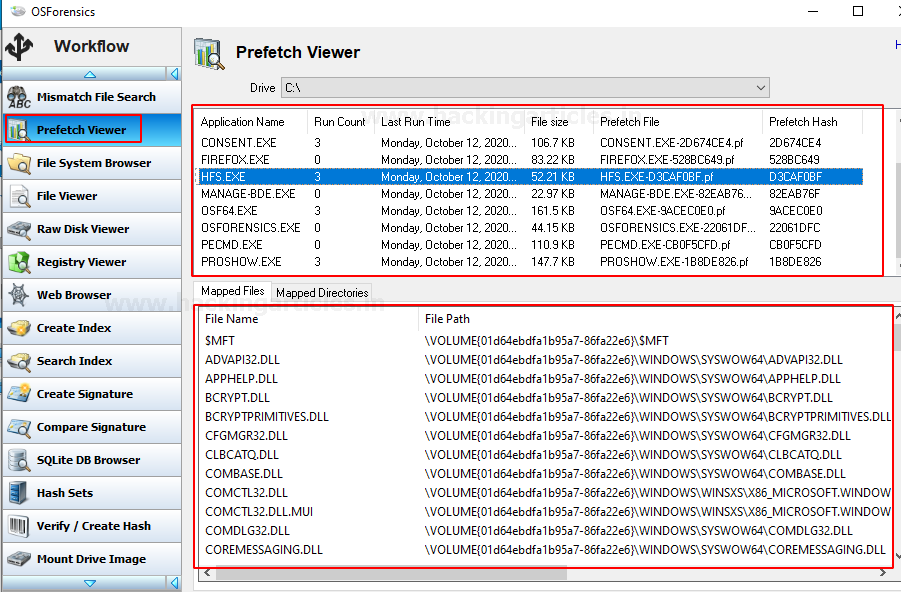
OS Forensics
OS Forensic is a digital forensic tool, a complete package for forensic investigation by Passmark software. Users extract, analyze data, search files, recover deleted passwords, and recover deleted evidence, much more.
Download the tool from here.
Prefetch Explorer Command Line (PECmd)
PECmd is a command-line tool by Eric Zimmerman, used for bulk analysis of prefetch files.This tool can also export your prefetch artifacts to .csv and .css.
You can download the tool from here.
To begin with run the executable file. Let’s parse the prefetch file using this tool we will use the –d parameter to parse all the prefetch file.
PECmd.exe –d "C:\Windows\Prefetch"

In the image below, the prefetch file for firefox.exe is visible. The tool has parsed all the metadata as the introduction explains.

Similarly, through the following image, you can observe the prefetch file for HFS.exe. Such files will be created for every application you access.

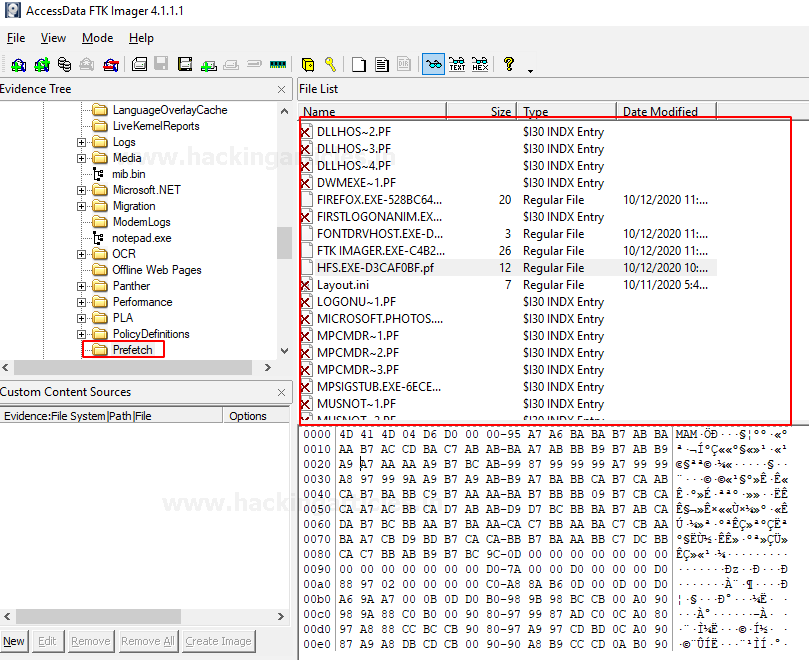
FTK Imager
As a Forensic Investigator, you can always access the prefetch files to understand the case given to you. Because through these files, you can determine what users frequently used on the system that you are investigating. You can easily do this with FTK Imager. FTK imager allows one to view and analyze the prefetch file present in the drive. To access the prefetch file through FTK, just open the said tool and look for the Prefetch folder in the left panel as highlighted in the image below:
This is all on prefetch files. Now that we understand these files properly, we can customize it, access it, and use it as we need. The most important thing to know about prefetch files is that they are a boon for retracing malware as they log any .exe file that runs on the system. Therefore, if someone executes a malicious file, you can track it through this.
To learn more about Cyber Forensics. Follow this Link
Author: Vishva Vaghela is a Digital Forensics enthusiast and enjoys technical content writing. You can reach her on Here
Hi, great article. it is mentioned ‘Windows makes a prefetch record when an application is run from a specific area for the absolute first time. Do you mean the first time after booting of windows? Then also, how cum it shows the counter when it creates the record when executed just for the first time
Great in-depth article, had the information I was looking for plus more.
This article just made my day and my next class a success.