Comprehensive Guide on SearchSploit
Hello friends!! Several times you might have read our articles on CTF challenges and other, where we have used searchsploit to find out an exploit if available in its Database. Today in this article we are going to discuss searchsploit in detail.
Table of Content
- Introduction to searchsploit
- Title Searching
- Advance Title Searching
- Copy To Clipboard
- Copy To Directory
- Examine an Exploit
- Examining Nmap result
- Exploit-DB Online
- Eliminate Unwanted Results
- Case Sensitive
Introduction to SearchSploit
Included in the Exploit Database repository on GitHub is “searchsploit”, a command line search tool for Exploit-DB that also allows you to take a copy of Exploit Database with you, everywhere you go. SearchSploit gives you the power to perform detailed offline searches through your locally checked-out copy of the repository. This capability is particularly useful for security assessments on segregated or air-gapped networks without Internet access.
Since we are using GNOME build of Kali Linux, therefore, the “exploitdb” package is already included by default, all we need to do, open the terminal and just type “searchsploit” and press Enter. You will welcome by its help screen.
Source: https://www.exploit-db.com/searchsploit/

Title Searching
Using –t option enables “title” parameter to search an exploit with a specific title. Because by default, searchsploit will try both the title of the exploit as well as the path. Searching an exploit with a specific title gives quick and sorted results.
Syntax: searchsploit [option] <title>
searchsploit -t java
The above command will search exploit related to the Java platform and will show all exploit available in the exploit DB database.

Advance Title Searching
Even you can use –t option, to get the more fine result in finding the exploit of any particular platform. For example, if you want to find out java exploit for windows platform, then you can consider the following command.
searchsploit –t java windows
Now you can compare the current output result from the previous result.

Copy To Clipboard
Using –p options enable “copy to clipboard parameter” as this option provides more information related to the exploit, as well as copy the whole path to the exploit to the clipboard, all you need press Ctrl V to paste.
searchsploit 39166 searchsploit -p 39166
In the following image, we have shown the default result varies when we use –p option along with it.

Copy To Directory
using –m options enable “copy to directory/folder parameter” as this option provides the same information as above related to the exploit, as well as copy the exploit in your current working directory.
searchsploit 39166 searchsploit -m 39166
In the following image, we have shown the default result varies when we use –m option along with it.

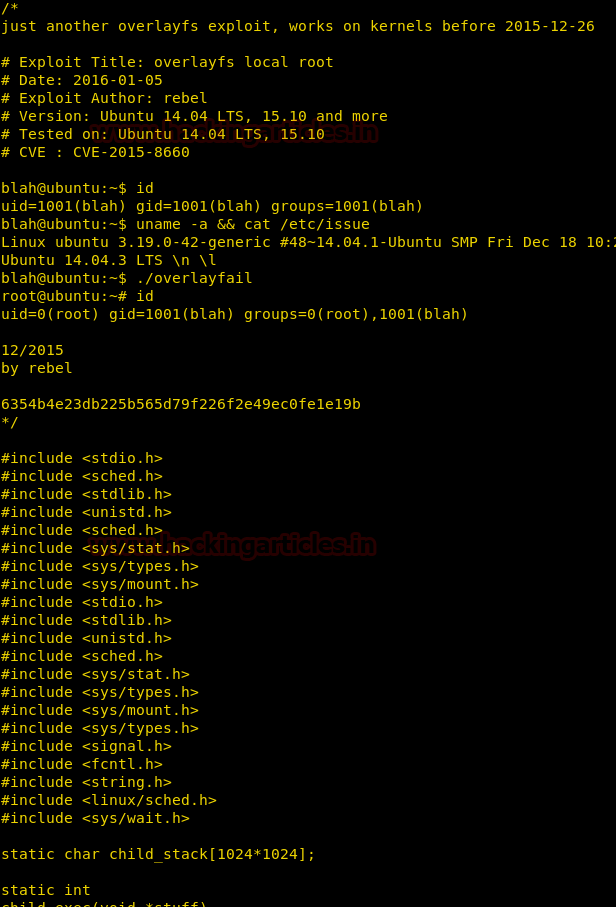
Examine an Exploit
Using —examine option, enables examine parameter to read the functionality of that exploit with the help of $PAGER.
searchsploit 39166 --examine

The above command will open the text file of the exploit to review its functionality, code, and other information.
Examining Nmap result
As we all know, Nmap has a very remarkable feature that let you save its output result in .xml format and we can identify each exploit associated with the nmap XML file.
nmap -sV 192.168.1.102 -oX result.xml
With the help of above command, we have saved the scanning result of nmap in an XML file, so that we can search the exploit related to scanned port/services.

Using –x option enables the examine parameter as well as –nmap option Checks all results in Nmap XML output with service version to find out related exploit with it.
searchsploit –x --nmap result.xml
Here you can observe that it is using verbose mode to examine XML file and had shown all possible exploit of running services.

Continue reading…

Exploit-DB Online
Using –w option enables website URL because on its website you will get more detailed information such as CVE-ID, setup files, tags, and vulnerability mappings which is not included in searchsploit.
searchsploit ubuntu 14.04 –w
The above command will show all available Exploit DB website links for the exploit related to Ubuntu 14.04.

Eliminate Unwanted Results
using –exclude option, it enables exclude parameter to remove the unwanted result from inside the list of exploit. You can also remove multiple terms by separating the terms with a “|” (pipe). This can be considered in the following:
searchsploit ubuntu 14.04 searchsploit --exclude="Privilege Escalation"
In the following image, we have shown the default result varies when we use –exclude option along with it. Even you can eliminate more terms with the help of “|” (pipe)
searchsploit --exclude="Privilege Escalation" | (Poc)

Moreover, we can use the universal Grep command to remove the unwanted result from its output result. This can be considered in the following:
searchploit ubuntu14.04 searchploit ubuntu 14.04 | grep "Buffer Overflow"
The above command will only look for all available exploit of ubuntu 14.04 on Buffer Overflow and dump the result.

Case Sensitive
Using –c option enables the “case-sensitive search” parameter to find out exploit related to specific character mention in the command, by default it makes the insensitive search. You can consider the following example:
searchsploit xss searchsploit –c XSS
As you can observe by default it has shown all available exploit related to xss/XSS but in the next command, it has shown the result only for XSS.

To learn more about Penteration Testing. Follow this Link.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
Need article for reference
Thanks great article, didn’t know it could do the nmap thing! It would be nice if it could also match against a list of installed packages on a remote system (dpkg -l)
Hello, how can I use an exploit found with Searchsploit with Metasploit? It’s hard for me to find the right exploit at Metasploit.
It gives the following error
searchsploit –x –nmap result.xml
root@kali:~# searchsploit -v –nmap result.xml
[i] Reading: ‘result.xml’
result.xml:1: parser error : Start tag expected, ‘<' not found
Starting Nmap 7.80 ( https://nmap.org ) at 2020-12-15 06:16 EST