5 Ways to Directory Bruteforcing on Web Server
In this article, we have a focus towards directory brute force attack using Kali Linux tool and try to find hidden files and directories inside a web server for penetration testing.
Table of Content
- What is Path Traversal or Directory Traversal?
- DIRB
- Dirbuster
- Wfuzz
- Metasploit
- Dirserach
What is Path Traversal or Directory Traversal?
A path traversal attack is also known as directory traversal aims to access files and directories that are stored outside the web root folder. By manipulating variables that reference files with “dot-dot-slash (…/)” sequences and its variations or by using absolute file paths, it may be possible to access arbitrary files and directories stored on file system including application source code or configuration and critical system files. For more information visit owasp.org
Let’s Start!!!
DIRB
DIRB is a Web Content Scanner. It looks for existing (and/or hidden) Web Objects. It basically works by launching a dictionary-based attack against a web server and analyzing the response. DIRB main purpose is to help in professional web application auditing.
The tool “Dirb” is in-built in Kali Linux, therefore, Open the terminal and type following command to start brute force directory attack.
dirb http://192.168.1.5/dvwa
Hence you can see read the fetched directories and file in the given screenshot.
To know more, read the full article from here: https://www.hackingarticles.in/comprehensive-guide-to-dirb-tool/

DirBuster
DirBuster is a multi threaded java application designed to brute force directories and files names on web/application servers. DirBuster comes with a total of 9 different lists; this makes DirBuster extremely effective at finding those hidden files and directories.
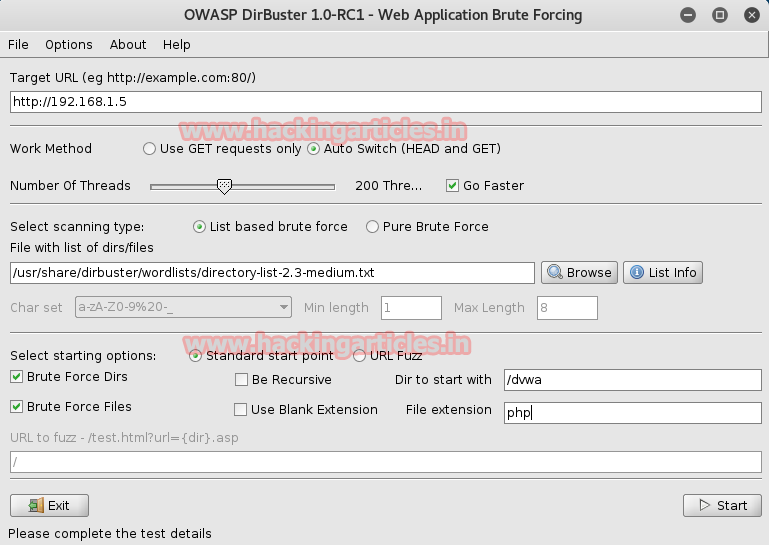
Similarly, open the terminal and type Dirbuster, then enter the target URL as shown in below image and browse /usr/share/dirbuster/wordlis/ directory-list-2-3-medium.txt for brute force attack.
Select option dir to start with /dvwa, once you have configured the tool for attack click on start.
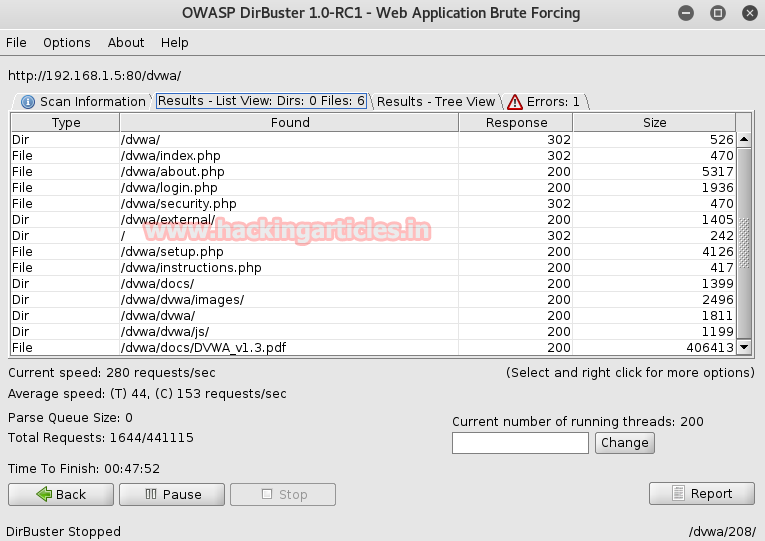
This will start the brute force attack and dumps all file and directory present inside web server as shown in the given screenshot.
To know more, read the full article from here: https://www.hackingarticles.in/comprehensive-guide-on-dirbuster-tool/
Wfuzz
Wfuzz is a tool designed for bruteforcing Web Applications, it can be used for finding resources not linked (directories, servlets, scripts, etc), bruteforce GET and POST parameters for checking different kind of injections (SQL, XSS, LDAP, etc), bruteforce Forms parameters (User/Password), Fuzzing, etc.
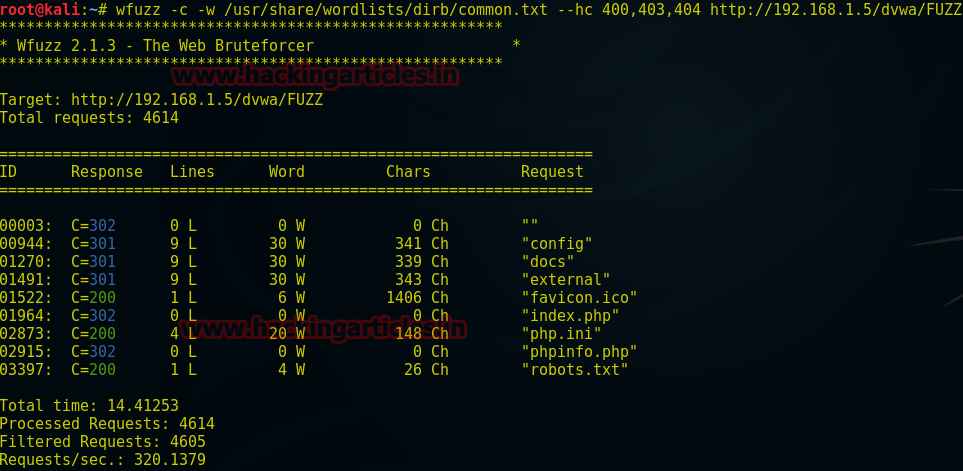
wfuzz -c -W /usr/share/wfuzz/wordlist/dir/common.txt --hc 400,404,403 http://192.168.1.5/dvwa/FUZZ
Here option –c is used for output with color; -W for wordlist; –hc for hiding responses with the specified code/lines/words/chars. It is also in-built in your Kali Linux.
Metasploit
HTTP Directory Scanner
This module identifies the existence of interesting directories in a given directory path.
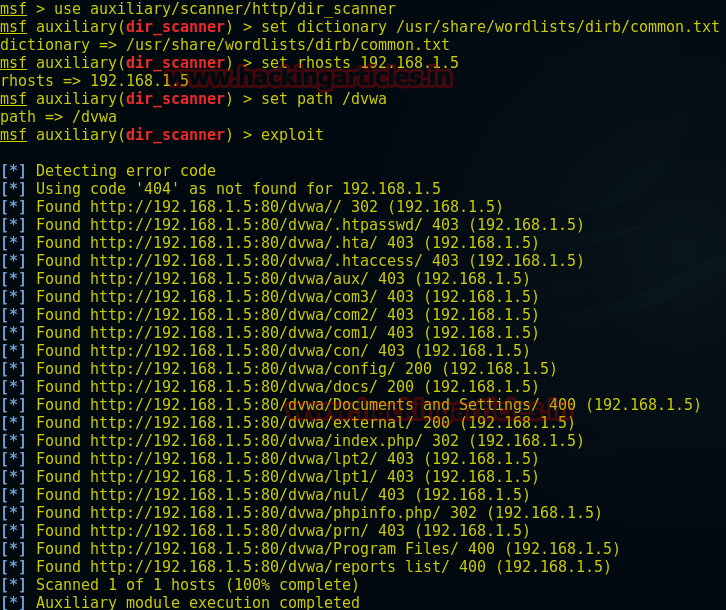
use auxiliary/scanner/http/dir_scanner msf auxiliary(dir_scanner) >set dictionary /usr/share/wordlists/dirb/common.txt msf auxiliary(dir_scanner) >set rhosts 192.168.1.5 msf auxiliary(dir_scanner) > set path /dvwa msf auxiliary(dir_scanner) >exploit
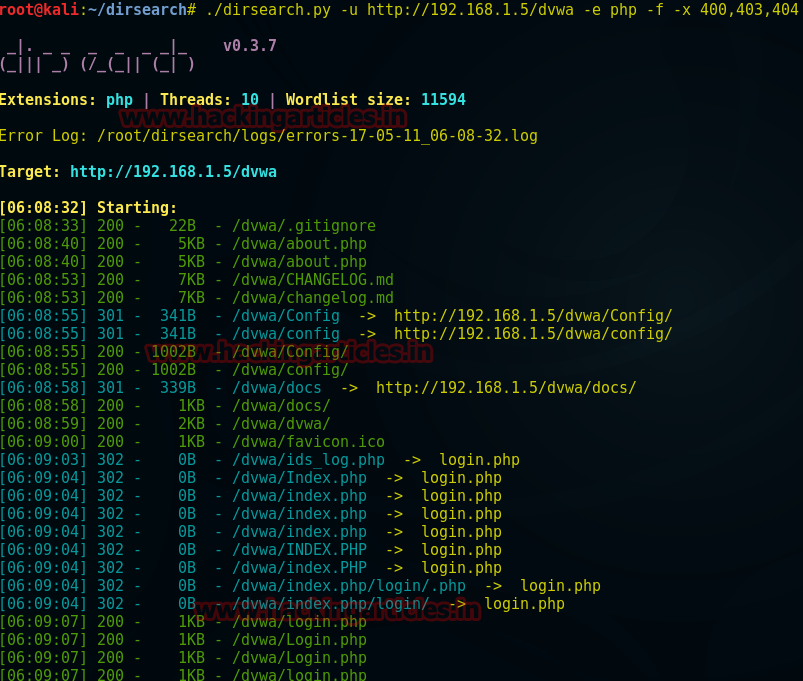
Dirsearch
Dirsearch is a simple command line tool designed to brute force directories and files in websites. This tool is available at GitHub you can download it from here and after installation in your Kali Linux type following to start dirsearch.
./dirsearch.py –u http://192.18.1.5/dvwa -e php -f -x 400,403,404
Here option –e is use for generating one entry for php extension; -x hide responses with the specified code/lines/words/chars.
From the given screenshot, you can read php file of the targeted web server.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here