Check Meltdown Vulnerability in CPU
Hello Friends!! You must be heard of the latest vulnerbility “Meltdown” which has been discovered almost in every CPU having intel processessor, from this link you can check list of vulnerable CPU discription. Today we are going to disccuss how to “Check Metltadown vulnerability in any CPU” by using a script.
From Wikipedia
Meltdown is a hardware vulnerability affecting Intel x86 microprocessors and some ARM-based microprocessors. It allows a rogue process to read any physical, kernel or other process’s mapped memory, regardless of whether or not it should be able to do so. It allows an unauthorized process to read data from any address that is mapped to the current process’s memory space, because instruction pipelining in the affected processors means that the data from the unauthorized address will almost always be temporarily loaded into the CPU’s cache during speculative execution, from which it can be recovered using other techniques, even if the original read instruction eventually fails due to privilege checking and never produces a readable result. Since many operating systems map physical memory, kernel processes, and other running user space processes into the address space of every process and rely on privilege checking to prevent unauthorized access, Meltdown effectively allows a rogue process to read any physical, kernel or other process’s mapped memory, regardless of whether or not it should be able to do so. Accordingly, many servers and cloud services were impacted, as well as a potential majority of smart devices and embedded devices using ARM based processors (mobile devices, smart TVs and others), including a wide range of networking equipment.
Let’s start!!
Open the terminal and type given below command to download the script form git hub. It can only dump linux_proc_banner which is work as an interface for internal data structures in the kernel and it is used to get information regarding the system and to change certain kernel Process.
git clone https://github.com/paboldin/meltdown-exploit.git
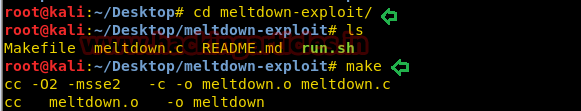
From given below image you can observe I had successfully download this script in my Linux machine.

Now explore the downloaded folder in terminal now run the command “make” for compiling the program file before running the script.
Now run the script by executing given below command which will identify the state of vulnerability by read its memory space.
./run.sh
From given below image you can observe where it is vulnerable ON has dumped the complete detail of CPU Processor. So here it has shown some details such as:
Vendor Id: Vendor ID or VID is unique number assign to a Hardware to identify it on which system it has been installed.
CPU family: Same functionality Processors are categories into same family, here CPU family 6 means indicate a model from Pentium Pro family.
Model: Indicates model number of CPU family.
Model name: Holds Model name of Processor
Stepping: It is used identify the version of microprocessor
Microcode: it is a lowest instruction set permanently to control the microprocessor
CPU MHz: Describe Usage of CPU.
Cache size: Define the size of cache memory.

You can also verify above result by executing given below command which is used for obtaining details of system information.

Source: https://github.com/paboldin/meltdown-exploit