Beginners Guide for John the Ripper (Part 2)
We learned most of the basic information on John the Ripper in our Previous Article which can be found here. In this article, we will use John the Ripper to crack the password hashes of some of the file formats like zip, rar, pdf and much more.
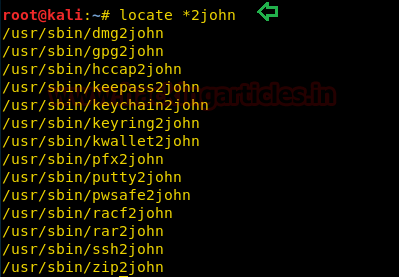
To crack these password hashes, we are going to use some of the inbuilt and some other utilities which extract the password hash from the locked file. There are some utilities that come inbuilt with John which can be found using the following command.
locate *2john
As you can see that we have the following utilities, we will demonstrate some of them here.
Cracking the SSH Password Hash
John the Ripper can crack the SSH private key which is created in RSA Encryption. To test the cracking of the private key, first, we will have to create a set of new private keys. To do this we will use a utility that comes with ssh, called “ssh-keygen”.
ssh-keygen

After opening, it asks for the location at which we want the public/private RSA key pair to store? You can use any location or you can leave it as default.
After that it asks for the passphrase, after entering the password again, we successfully generate the RSA private key. (Refer the image)
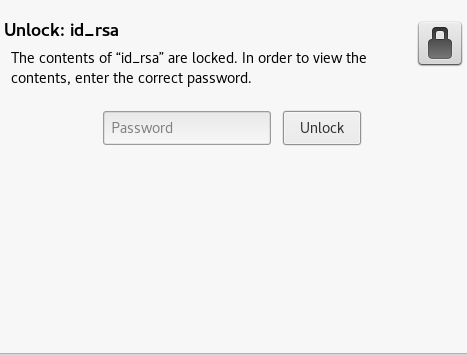
When you will try to open the file, you will be greeted by the following prompt.
Now John cannot directly crack this key, first, we will have to change its format, which can be done using a john utility called “ssh2john”.
Syntax: ssh2john [location of key]
ssh2john /home/pavan/.ssh/id_rsa > crack.txt
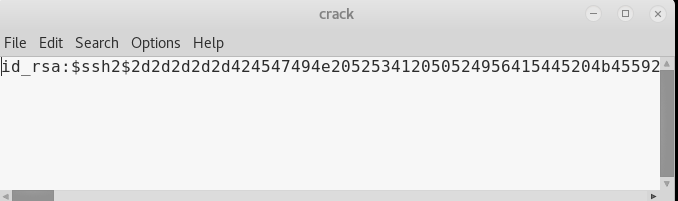
You can see that we converted the key to a crackable hash and then entered it into a text file named id_rsa.txt.
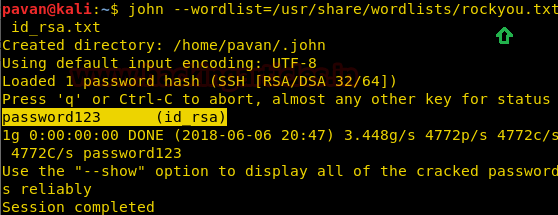
Now let’s use John the Ripper to crack this hash.
john --wordlist=/usr/share/wordlists/rockyou.txt id_rsa.txt
Great! We have successfully cracked the passphrase used to create the private ssh key to be “password123”
Cracking the KeepPass2 Password Hash
John the Ripper can crack the KeepPass2 key. To test the cracking of the key, first, we will have to create a set of new keys. To do this we will use a utility that is called “kpcli”.
kpcli
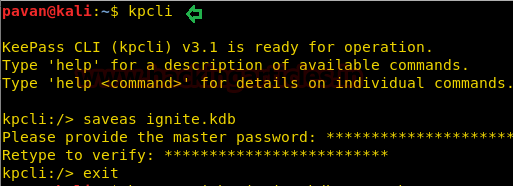
Now we will create a database file using the command “save as” and naming the database file as ignite.kdb and entering a passcode to secure it.
When you will try to open the file, you will be greeted by the following prompt.
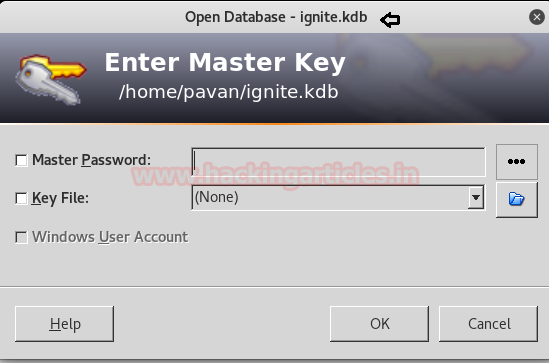
Now John cannot directly crack this key, first, we will have to change its format, which can be done using a john utility called “keepass2john”.
Syntax: keepass2john [location of key]
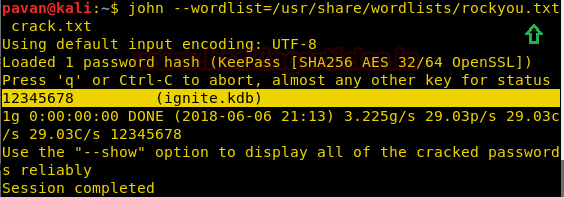
keepass2john ignite.kdb > crack.txt

Now let’s use John the Ripper to crack this hash.
john --wordlist=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the key to be “12345678”
Cracking the RAR Password Hash
Now we will crack some compressed files, to do that we will have to create a file to be compressed so let’s do that using echo command as shown in the given screenshot.
You can see that we created a file.txt which we will be using to create compressed files.
echo hackingarticles.in > file.txt

John the Ripper can crack the RAR file passwords. To test the cracking of the password, first, let’s create a compressed encrypted rar file.
rar a -hpabc123 file.rar file.txt

- a = Add files to archive
- hp[password] = Encrypt both file data and headers
This will compress and encrypt our file.txt into a file.rar. So, when you will try to open the file, you will be greeted by the following prompt.

Now John cannot directly crack this key, first, we will have to change it format, which can be done using a john utility called “rar2john”.
Syntax: rar2john [location of key]
rar2john file.rar > crack.txt

Now let’s use John the Ripper to crack this hash.
john --wordlist=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the key to be “abc123”

Cracking the ZIP Password Hash
John the Ripper can crack the ZIP file passwords. To test the cracking of the password, first, let’s create a compressed encrypted zip file.
zip -er file.zip file.txt

- e = Encrypt
- r = Recurse into directories
This will compress and encrypt our file.txt into a file.zip. So, when you will try to open the file, you will be greeted by the following prompt.
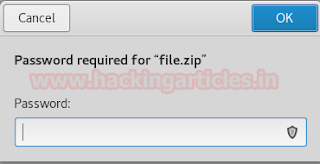
Now John cannot directly crack this key, first, we will have to change its format, which can be done using a john utility called “zip2john”.
Syntax: zip2john [location of key]
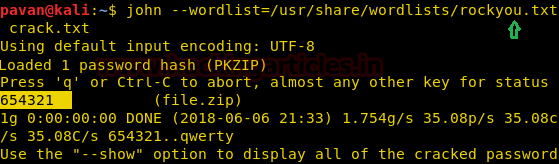
zip2john file.zip > crack.txt
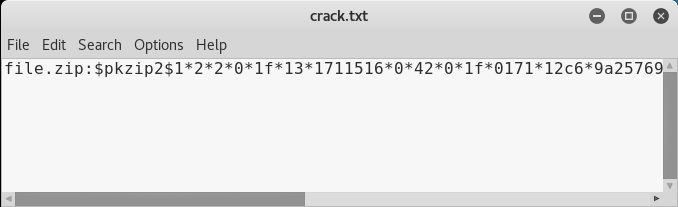
Now let’s use John the Ripper to crack this hash.
john --wordlist=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the key to be “654321”
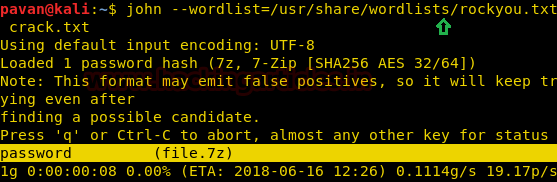
Cracking the 7-Zip Password Hash
John the Ripper can crack the 7-Zip file passwords. To test the cracking of the password, first, let’s create a compressed encrypted 7z file.
7z a -mhe file.7z file.txt -p"password"
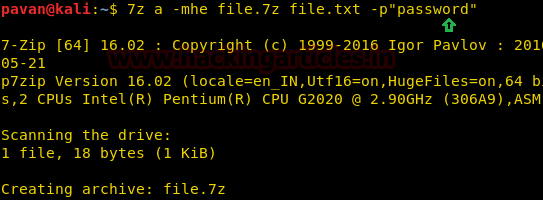
- a = Add files to archive
- m = Set compression Method
- h = Calculate hash values for files
- e = Encrypt file
- p = set Password
This will compress and encrypt our file.txt into a file.7z. So, when you will try to open the file, you will be greeted by the following prompt.

Now John cannot directly crack this key, first, we will change its format, which can be done using a john utility called “7z2john”. This is not inbuilt utility, It can be downloaded from here.
Syntax: zip2john [location of key]
python 7z2john.py file.7z > crack.txt
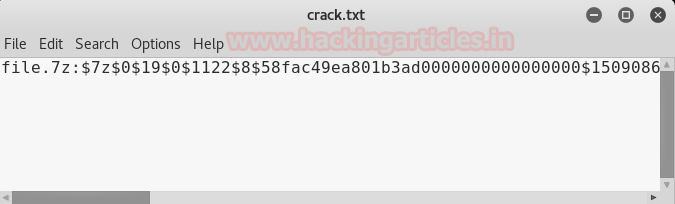
Now let’s use John the Ripper to crack this hash.
john –wordlist=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the key to be “password”
Cracking the PDF Password Hash
John the Ripper can crack the PDF file passwords. You can encrypt your pdf online by using this website. This will compress and encrypt our pdf into a password protected file.pdf. So, when you will try to open the file, you will be greeted by the following prompt.
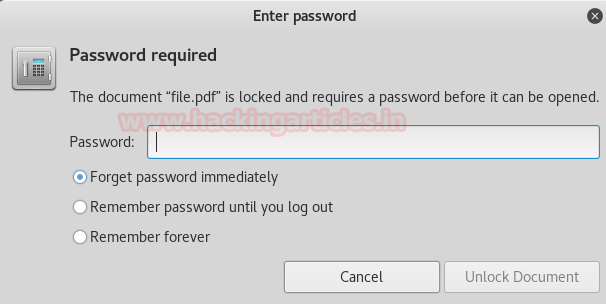
Now John cannot directly crack this key, first, we will have to change its format, which can be done using a john utility called “pdf2john”. This is not an inbuilt utility, it can be downloaded from here.
Syntax: pdf2john [location of key]
python pdf2john.py file.pdf > crack.txt

Now let’s use John the Ripper to crack this hash.
john –wordlist=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the key to be “password123”.

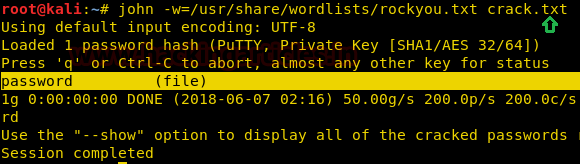
Cracking the PuTTY Password Hash
John the Ripper can crack the PuTTY private key which is created in RSA Encryption. To test the cracking of the private key, first, we will have to create a set of new private keys. To do this we will use a utility that comes with PuTTY, called “PuTTY Key Generator”.
Click on “Generate”. After Generating the key, we get a window where we will input the key passphrase as shown in the image.
After entering the passphrase, click on Save private key to get a private key in the form of a .ppk file
After generating transfer this .ppk file to Kali Linux.
Now John cannot directly crack this key, first, we will have to change its format, which can be done using a john utility called “putty2john”.
Syntax: putty2john [location of key]
putty2john file.ppk > crack.txt

You can see that we converted the key to a crackable hash and then entered it into a text file named crack.txt.
Now let’s use John the Ripper to crack this hash.
john –w=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the private PuTTY key to be “password”.
Cracking the “Password Safe” Password Hash
John the Ripper can crack the Password Safe Software’s key. To test the cracking of the key, first, we will have to create a set of new keys. To do this we will install the Password Safe Software on our Windows 10 System.
To get a new key, Click on “New”
In this prompt, check the Show Combination Box. After that Enter the passphrase you want to use to generate the key. This will generate a .psafe3 file.
After generating transfer this .safe3 file to Kali Linux.
Now John cannot directly crack this key, first, we will have to change its format, which can be done using a john utility called “pwsafe2john”.
Syntax: pwsafe2john [location of key]
pwsafe2john ignite.psafe3 > crack.txt

You can see that we converted the key to a crackable hash and then entered it into a text file named crack.txt.
Now let’s use John the Ripper to crack this hash.
john –w=/usr/share/wordlists/rockyou.txt crack.txt
Great! We have successfully cracked the passphrase used to create the private pwsafe key to be “password123”

Author: Pavandeep Singh is a Technical Writer, Researcher and Penetration Tester Contact here
Raj,
Great blog post and it helped me learn. However, the 7z to john hasn’t worked for me. it always errors out with something weird.
For example recently i was trying to do a ctf and that gave me a password encoded 7z. I ran into your article here and tried executing 7z2john.py, but it errored out saying “7-Zip files without header encryption are *not* supported yet!”
Well, i understood what it meant, but don’t know how to fix it.