Scan Website Vulnerability using Uniscan (Beginner Guide)
Through this article, we are trying to elaborate the word Enumeration using Kali Linux tool UNISCAN.
Uniscan is a simple Remote File Include, Local File Include, and Remote Command Execution vulnerability scanner as well as work as enumerating tool in order to gather information like open ports and protocol related to target and investigate it against any vulnerability.
Let’s start!!!
Open the terminal and type following command using –j option for server fingerprints
uniscan -u "http://testphp.vulnweb.com/listproducts.php?cat=1" -j
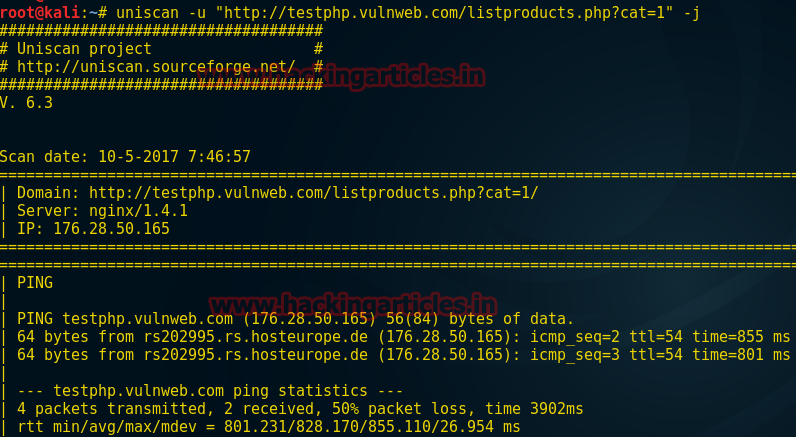
It will start enumeration from PING by sending ICMP packets to the targeted server and establish the connection.
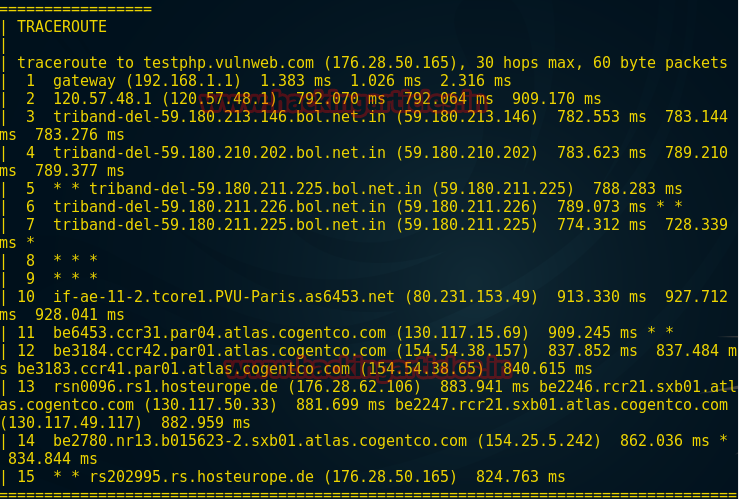
Further, it will use TRACEROUTE to show the path of a packet of information taken from source to destination and list all the routers it travels through or fails to and is discarded. In actually, it will inform you how long each ‘hop’ from the router to router takes.
NSLOOKUP is a program to query Internet domain name servers (DNS). NSLOOKUP or Reverse DNS (rDNS) is a method of resolving an IP address into a domain name
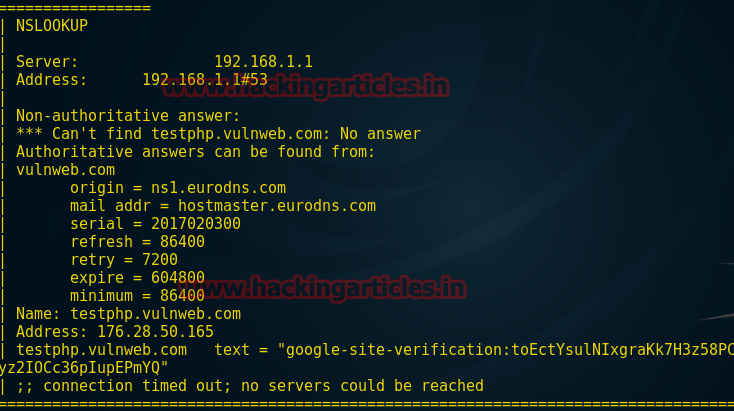
Uniscan made use of NMAP for aggressive scan against the targeted server to identify open ports and protocols services hence from the screenshot you can observe the result. It also enumerates the target using NMAP NSE script to identify the vulnerability and details of running services.

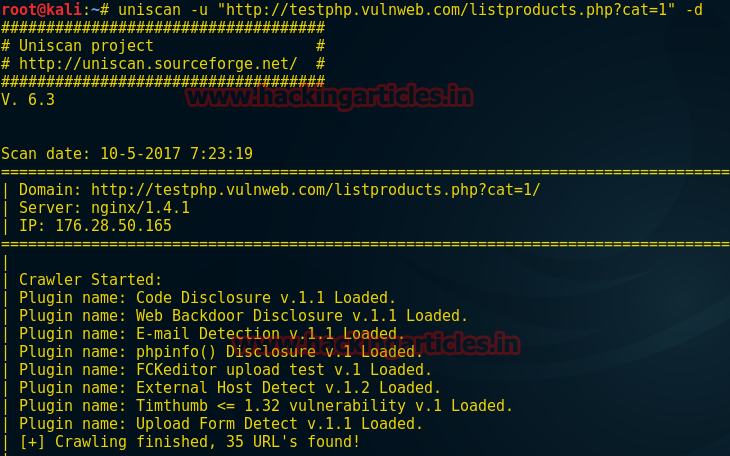
Now type the following command for dynamic scan against the targeted server using –d option.
uniscan -u "http://testphp.vulnweb.com/listproducts.php?cat=1" -d
Now it will load the selected plug-in for fetching more details related to the targeted server.
From given screenshot, you can observe the result where it came up with an email id moreover loaded further plug-in for scanning vulnerability like SQL injection, remote or local file inclusion and XSS.
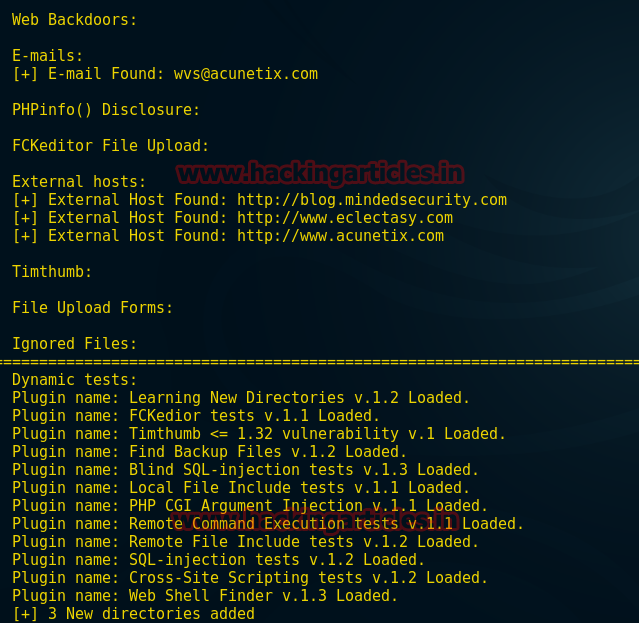
From given below screenshot you can see it has used blind SQL injection and return a link of the targeted web pages. Similarly, it will test for XSS and remote or local file inclusion vulnerability.

Now type next command using –q option to enable directory test in targeted server
uniscan –u http://192.168.1.107 –q
Form scanning result you can read the fetched directories.

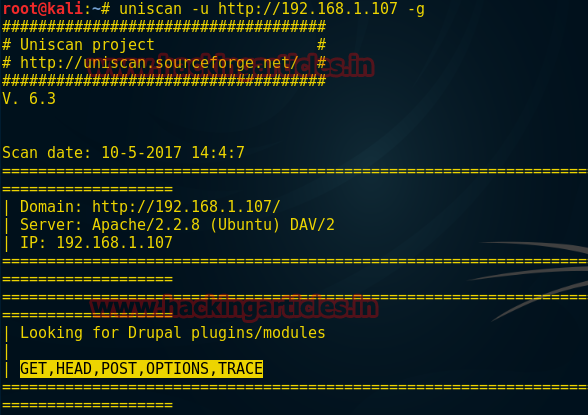
Last but not least use –g option for web fingerprints with the following command
uniscan –u http://192.168.1.107 –g
Here we have come across available http option GET, HEAD, POST, OPTION, and TRACE which might help in verb tampering.
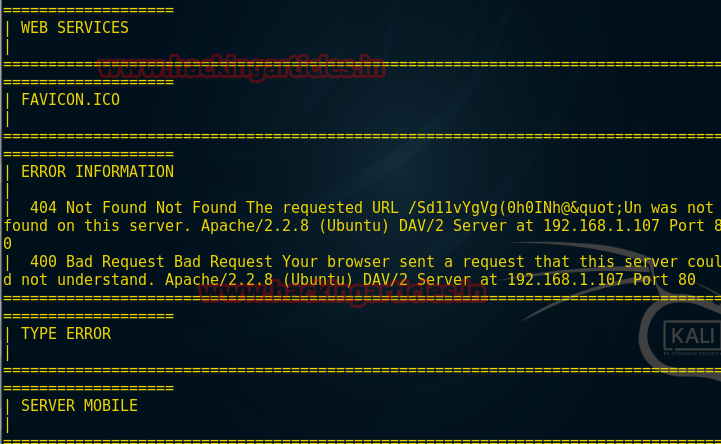
It will try to find out web service and error information and type of error as shown in the given image.
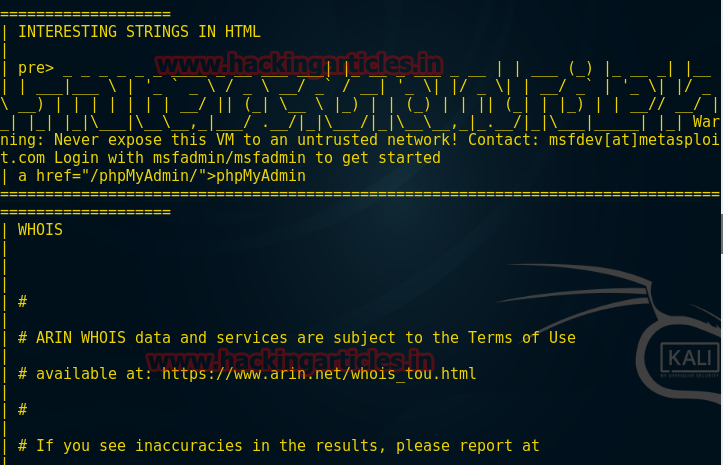
Here this tool inserts a string in html in order to grab banner moreover we have come across the credential of the web server and from the given screenshot you can read login msfadmin: msfadmin
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here