Beginners Guide for John the Ripper (Part 1)
We know the importance of John the ripper in penetration testing, as it is quite popular among password cracking tool. In this article, we are introducing John the ripper and its various usage for beginners.
What is John the Ripper?
John the Ripper is a free password cracking software tool developed by Openwall. Originally developed for Unix Operating Systems but later on developed for other platforms as well. It is one of the most popular password testings and breaking programs as it combines a number of password crackers into one package, autodetects password hash types, and includes a customizable cracker. It can be run against various encrypted password formats including several crypt password hash types commonly found in Linux or Windows. It can also be to crack passwords of Compressed files like ZIP and also Documents files like PDF.
Where to get John the Ripper?
John the Ripper can be downloaded from Openwall’s Website here.
Or from the Official John the Ripper Repo here
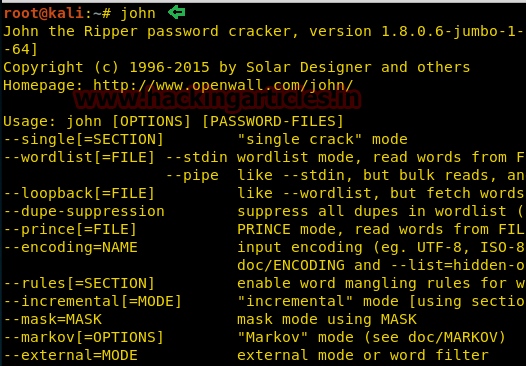
John the Ripper comes pre-installed in Linux Kali and can be run from the terminal as shown below:
John the Ripper works in 3 distinct modes to crack the passwords:
- Single Crack Mode
- Wordlist Crack Mode
- Incremental Mode
John the Ripper Single Crack Mode
In this mode John the ripper makes use of the information available to it in the form of a username and other information. This can be used to crack the password files with the format of
Username:Password
For Example: If the username is “Hacker” it would try the following passwords:
hacker
HACKER
hacker1
h-acker
hacker=
We can use john the ripper in Single Crack Mode as follows:
Here we have a text file named crack.txt containing the username and password, where the password is encrypted in SHA1 encryption so to crack this password we will use:
Syntax: john [mode/option] [password file]
john --single --format=raw-sha1 crack.txt
As you can see in the screenshot that we have successfully cracked the password.
Username: ignite
Password: IgNiTe

John the Ripper Wordlist Crack Mode
In this mode John the ripper uses a wordlist that can also be called a Dictionary and it compares the hashes of the words present in the Dictionary with the password hash. We can use any desired wordlist. John also comes in build with a password.lst which contains most of the common passwords.
Let’s see how John the Ripper cracks passwords in Wordlist Crack Mode:
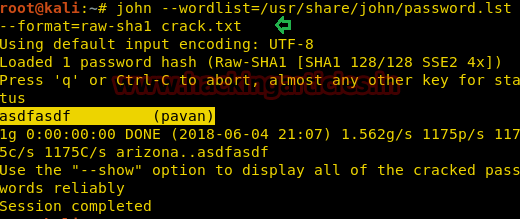
Here we have a text file named crack.txt containing the username and password, where the password is encrypted in SHA1 encryption so to crack this password we will use:
Syntax: john [wordlist] [options] [password file]
john --wordlist=/usr/share/john/password.lst --format=raw-sha1 crack.txt
As you can see in the screenshot, john the Ripper have cracked our password to be asdfasdf
Cracking the User Credentials
We are going to demonstrate two ways in which we will crack the user credentials of a Linux user.
Before that we will have to understand, what is a shadow file?
In the Linux operating system, a shadow password file is a system file in which encrypted user password is stored so that they are not available to the people who try to break into the system. It is located at /etc/shadow.
First Method
Now, for the first method, we will crack the credentials of a particular user “pavan”.
Now to do this First we will open the shadow file as shown in the image.
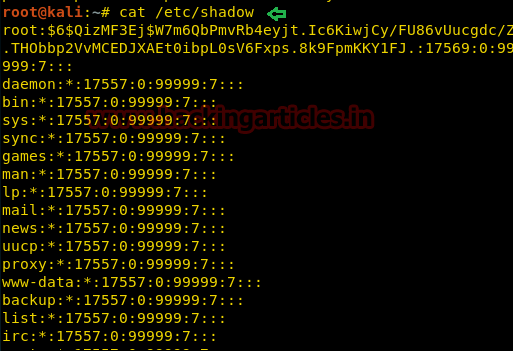
And we will find the credentials of the user pavan and copy it from here and paste it into a text file. Here we have the file named crack.txt.

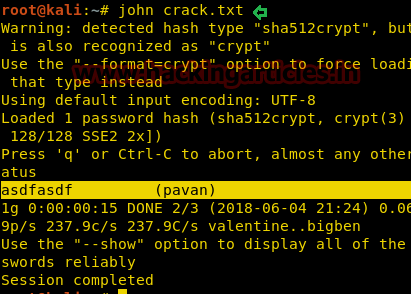
Now we will use john the ripper to crack it.
john crack.txt
As you can see in the image below that john the ripper has successfully cracked the password for the user pavan.
Second Method
Now, for the second method, we will collectively crack the credentials for all the users.
To do this we will have to use John the ripper utility called “unshadow”.
unshadow /etc/passwd /etc/shadow > crack.txt
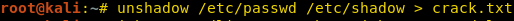
Here the unshadow command is combining the /etc/passwd and /etc/shadow files so that John can use them to crack them. We are using both files so that John can use the information provided to efficiently crack the credentials of all users.
Here is how the crack file looks after unshadow command.
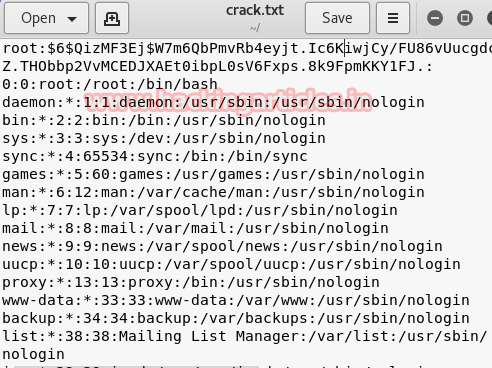
Now we will use john to crack the user credentials of all the users collectively.
john --wordlist=/usr/share/john/password.lst crack.txt
As you can see from the provided image that we have discovered the following credentials:
| User | Password |
| Raj | 123 |
| Pavan | Asdfasdf |
| Ignite | Yellow |
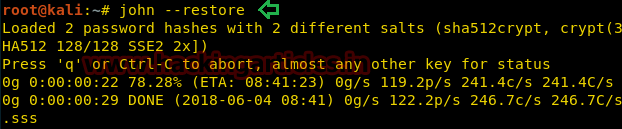
Stopping and Restoring Cracking
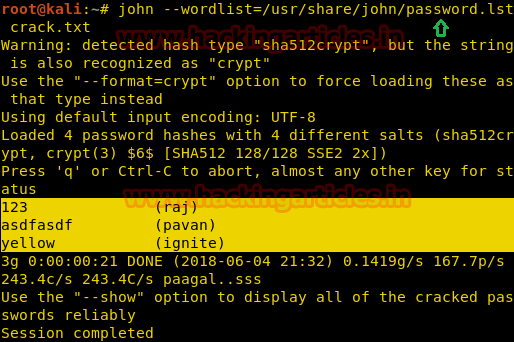
While John the ripper is working on cracking some passwords we can interrupt or pause the cracking and Restore or Resume the Cracking again at our convenience.
So while John the Ripper is running you can interrupt the cracking by Pressing “q” or Crtl+C as shown in the given image.
Now to resume or restore the cracking process we will use the –restore option of John the ripper as shown :
john --restore
Now we will decrypt various hashes using John the Ripper
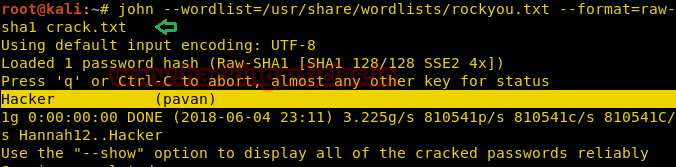
SHA1
To decrypt SHA1 encryption we will use RockYou as wordlist and crack the password as shown below:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=raw-sha1 crack.txt
As you can see in the given image that we have the username pavan and password as Hacker
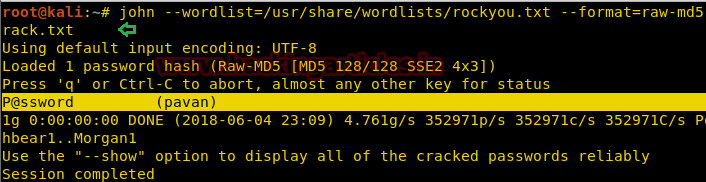
MD5
To decrypt MD5 encryption we will use RockYou as wordlist and crack the password as shown below:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=raw-md5 rack.txt
As you can see in the given screenshot that we have the username pavan and password as P@ssword.
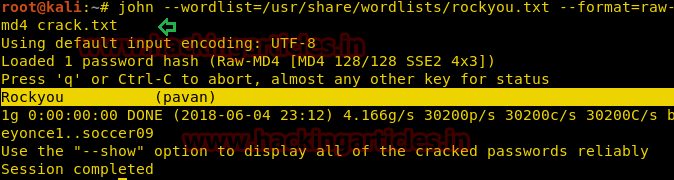
MD4
To decrypt MD4 encryption we will use RockYou as wordlist and crack the password as shown below:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=raw-md4 crack.txt
As you can see in the given screenshot that we have the username pavan and password as Rockyou
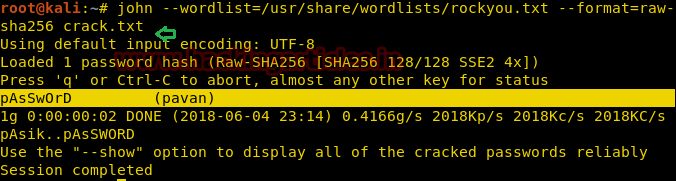
SHA256
To decrypt SHA256 encryption we will use RockYou as wordlist and crack the password as shown below:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=raw-sha256 crack.txt
As you can see in the given screenshot that we have the username pavan and password as pAsSwOrD
RIPEMD128
To decrypt RIPEMD128 encryption we will use RockYou as wordlist and crack the password as shown below:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=ripemd-128 crack.txt
As you can see in the given image that we have the username pavan and password as password123
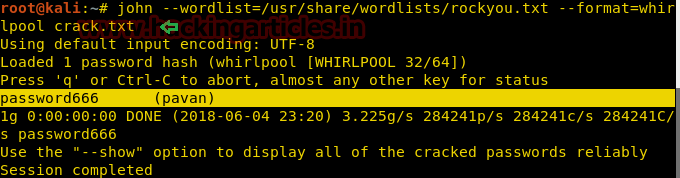
Whirlpool
To decrypt whirlpool encryption we will use RockYou as wordlist and crack the password as shown below:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=whirlpool crack.txt
As you can see in the given screenshot that we have the username pavan and password as password666
View All Formats
John the Ripper supports much encryption some of which we showed above. To view all the formats it supports:
john --list=formats
Hope, you can take reference of this article while using John the ripper, More on John the Ripper will be in the Next Part.

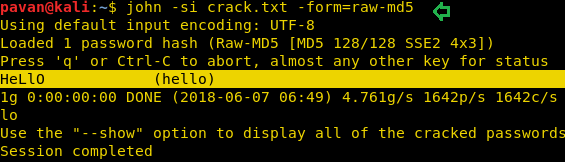
Abbreviating the Options
We don’t have to type complete option every time we use john the ripper, Developers have given users the option to abbreviate the options like
–single can be written as -si
–format can be written as -form
Shown below is an example of how to use these abbreviations.
john -si crack.txt -form=raw-md5
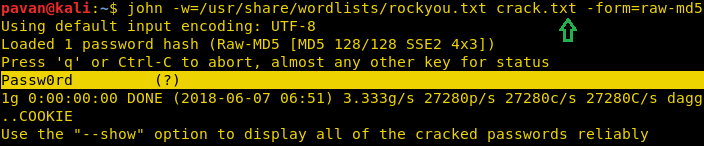
Another abbreviation we can use is:
–wordlist can be written as -w
john -w=/usr/share/wordlists/rockyou.txt crack.txt -form=raw-md5
Cracking Multiple Files
We can also crack multiple hash files if they have the same encryption. Let’s take an example, we have two files.
- crack.txt
- md5.txt
Both contain md5 hashes, so to crack both files in one session, we will run john as follows:
Syntax: john [file 1][file 2]
john -form=raw-md5 crack.txt md5.txt

Author: Pavandeep Singh is a Technical Writer, Researcher and Penetration Tester Contact here
sir how to make this crack.txt having username and password. please help by replying.
How to make crack.txt
sudo make –text=True –smart=0 crack.txt
Yàaah is a good and insipered Things to begginers
its excellent tutorial
Whenever I try to do single crack mode it says “Using default input encoding: UTF -8 No password hashes loaded (see FAQ)” please help me! I put the hashed password in the file.
Hi,
Is there a way to suggest to “john” a string that I believe is a part of the password? It should shorten the time of cracking (in theory).
Regards,
MR
i dont understand where you got the user name from? is that for pc login or pdf login or website or i dont know?/
now where will you use that username and password for?
I was trying to crack SAM file of a windows 10 virtual machine .. it shows password cracked but still passwords are not shown … it just shows back the content of the file similar like cat command does .
try “sudo” in front of john
What John rule would we use to add all capital letters to the end of the word?
crack.txt
Name1:gsaweroigalnkxxx..64letters: (i.e. sha256)
Name2:wqtgakl3r5lkbalak..64letters:
etc..
But how do we know what passwords we are cracking? There is nowhere MAC specified?
└─$ echo “IgNiTe” | sha1sum 130 ⨯
bda966e8b0f5c02d460951fd571349e272c2097f –
└─$ cat single.pass
ignite:bda966e8b0f5c02d460951fd571349e272c2097f
└─$ john –single single.pass
└─$ john –show single.pass
0 password hashes cracked, 1 left
what’s wrong?